Deciphering Vulnerability Exploits: Beyond the Code
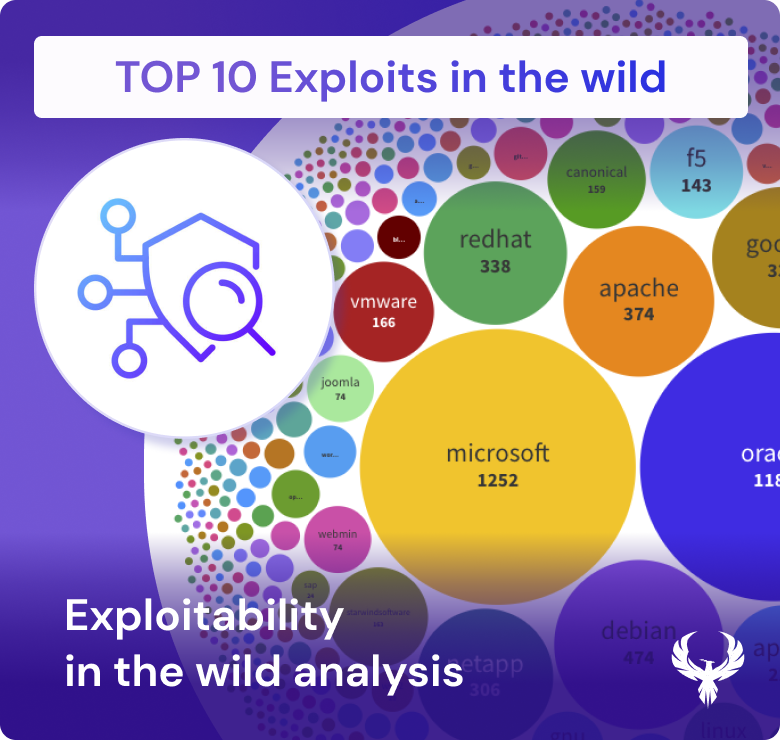
Exploit code isn’t synonymous with exploitability – not in the realm of cybersecurity where realism matters. While it undeniably contributes to the likelihood of a vulnerability being exploited, it’s only part of the equation. That’s where the Exploit Prediction Scoring System (EPSS) comes into play, assessing various facets to gauge the true exploit potential.
PUBLICLY AVAILABLE EXPLOIT CODE
In addition to collecting live exploitation data, the EPSS casts a wide net across sources like MetaSploit, Exploit-DB, and GitHub. Its mission? To determine if there’s published exploit code for the CVE at hand. While the presence of code correlates with the likelihood of exploitation, it’s no guarantee – a lesson we’ve learned through years of cybersecurity diligence.
OPEN SOURCE SECURITY TOOLS
Enter the world of open source security tools, the double-edged swords of ethical and unethical hackers alike. Tools like Intrigue, Sn1per, Jaeles, and Nuclei are in the EPSS spotlight. Why? Because understanding their capability to exploit a given CVE is essential. It’s a reminder that the same tools wielded by defenders can also be leveraged by attackers.
BOTTOM LINE
Just because exploit code surfaces online doesn’t mean you can realistically attack a vulnerability in your network. Real-world scenarios demand more than just code availability. Reachability analysis is key, and the EPSS knows it.
So, if you’re ready to unravel the intricacies of vulnerability exploits, CWE, and leverage the insights from our extensive threat intelligence sources, join us on this journey. In a world where the digital battleground is ever-evolving, understanding the true exploit potential of vulnerabilities is your best defense.