- 19th January 2025
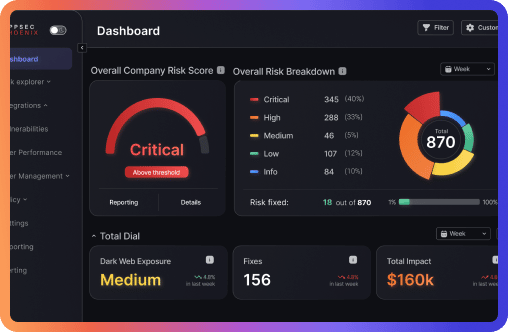
The 2024 CWE Top 25 list highlights the most dangerous software weaknesses. This article explores the methodology behind the list and how AI is improving threat detection. Discover how Application Security Posture Management (ASPM) and unified vulnerability management can help organizations address these critical threats.
Francesco Cipollone