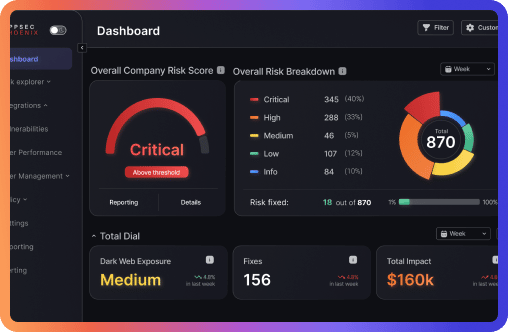
Between 21:57 and 23:30 UTC on April 22, 2026, a malicious @bitwarden/cli@2026.4.0 was live on npm for 93 minutes — long enough to reach CI/CD pipelines, developer workstations, and cloud automation hosts. The payload steals credentials across GitHub, AWS, GCP, and Azure, propagates as a self-replicating npm worm, injects GitHub Actions workflow stealers, and poisons AI coding assistants by injecting an invisible manifesto into shell configuration files. This is the first documented npm supply chain attack executed through Trusted Publishing.









![Phoenix Security infographic: Claude Code Critical Vulnerability — CI/CD Nightmare, 3 Command Injection Flaws. Dark navy and orange background with circuit-board pattern. Center: terminal window showing attack chain [config] | [shell] | [exfil] with three red arrows pointing to attack targets — CI/CD Pipeline Compromise (top right), Cloud Key Exfiltration via AWS (middle right), and Developer Workstation Compromise leading to Server-to-Server lateral movement (bottom right). Phoenix Security logo at top. Bottom text: "CLAUDE CODE / CRITICAL VULNERABILITY / CI/CD NIGHTMARE / 3 COMMAND INJECTION FLAWS / Credential Exfiltration · CWE-78 · Confirmed / Shell Injection in CLI, Editor, and Auth Helpers."](https://phoenix.security/media/Gemini_Generated_Image_abcn46abcn46abcn.jpeg)