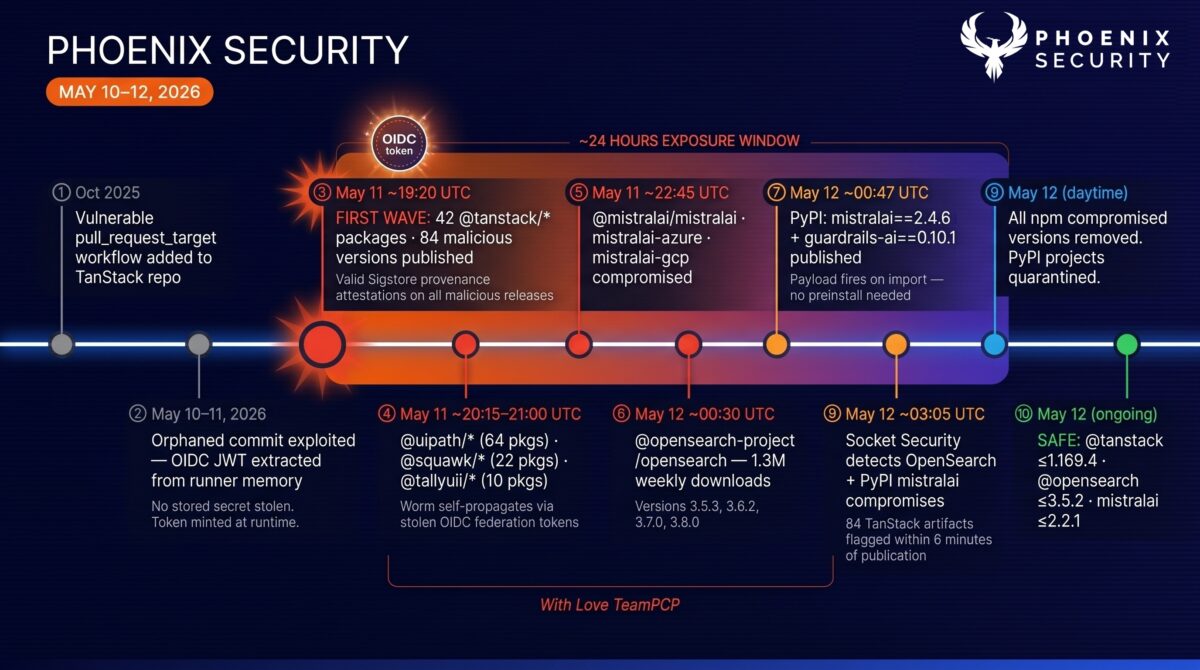
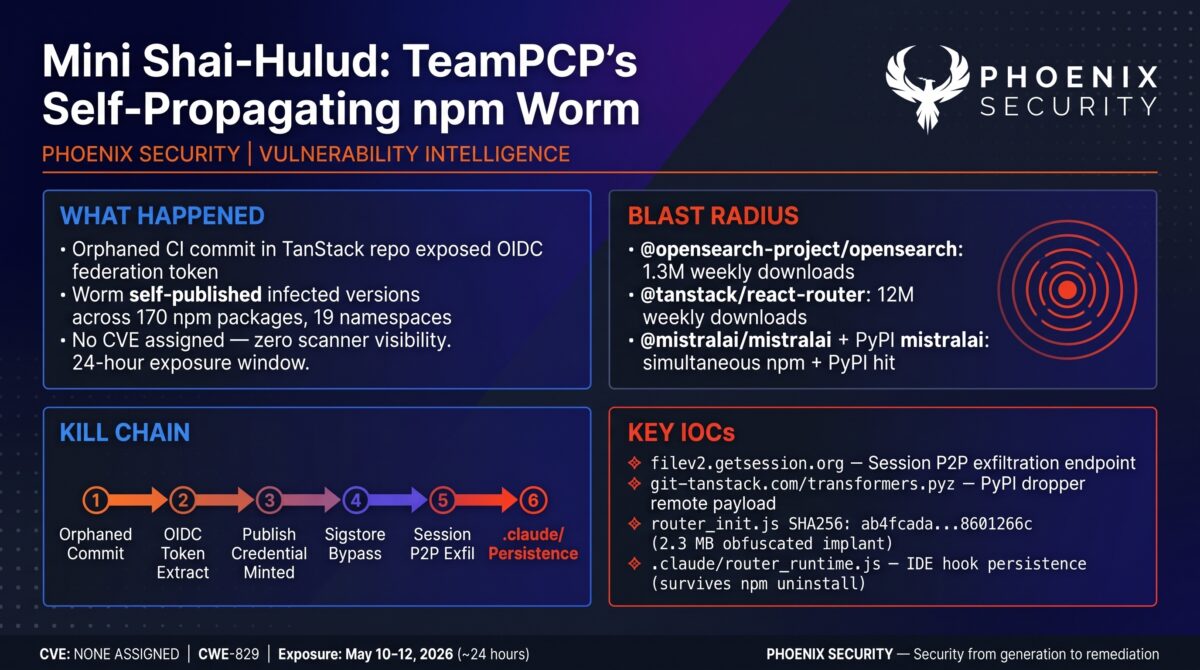
Between May 10 and May 12, 2026, TeamPCP — the group behind the Trivy, Checkmarx, and LiteLLM supply chain compromises — ran a self-propagating worm campaign across the npm and PyPI ecosystems. They named it Mini Shai-Hulud. The entry point was an orphaned commit in a TanStack CI workflow that still had OIDC trust federation configured with npm. No phished maintainer. No stored secret. The attacker extracted an OIDC token from the runner process and exchanged it for authenticated publish access to the entire TanStack namespace.
From there, the worm drove its own expansion: every infected CI run became a new publisher. Each compromised package version carried a preinstall hook that downloaded the Bun JavaScript runtime as a living-off-the-land binary, then launched a 2.3 MB obfuscated payload (router_init.js) that swept CI secrets, cloud credentials, Kubernetes tokens, and Vault secrets. On runners with active OIDC federation, the worm minted fresh npm tokens and republished infected versions under stolen maintainer identities — with valid Sigstore provenance attestations attached. By the time npm quarantine started, 170 packages across 19 namespaces were gone, including the AWS-maintained OpenSearch JavaScript client at 1.3 million weekly downloads and the official Mistral AI SDK family on both npm and PyPI.

Exfiltration ran through the Session P2P messaging network, not HTTP C2. The traffic is encrypted IM protocol — indistinguishable from legitimate messaging at the network layer. Persistence landed in Claude Code hook directories (.claude/) and VS Code task runners (.vscode/tasks.json). npm uninstall does not remove those. The worm fires again on every developer tool invocation until you explicitly clean the hook files. No CVE has been assigned. Traditional CVE-based vulnerability management had no visibility into any of this.
TL;DR for Engineering Teams – TeamPCP – Mini Shai Hulud
What it is: Self-propagating npm worm (Mini Shai-Hulud) attributed to TeamPCP. Entry via OIDC token extraction from a TanStack CI workflow orphaned commit. Worm republishes infected versions autonomously across maintainer namespaces using stolen OIDC federation tokens. Crosses into PyPI. No CVE assigned.
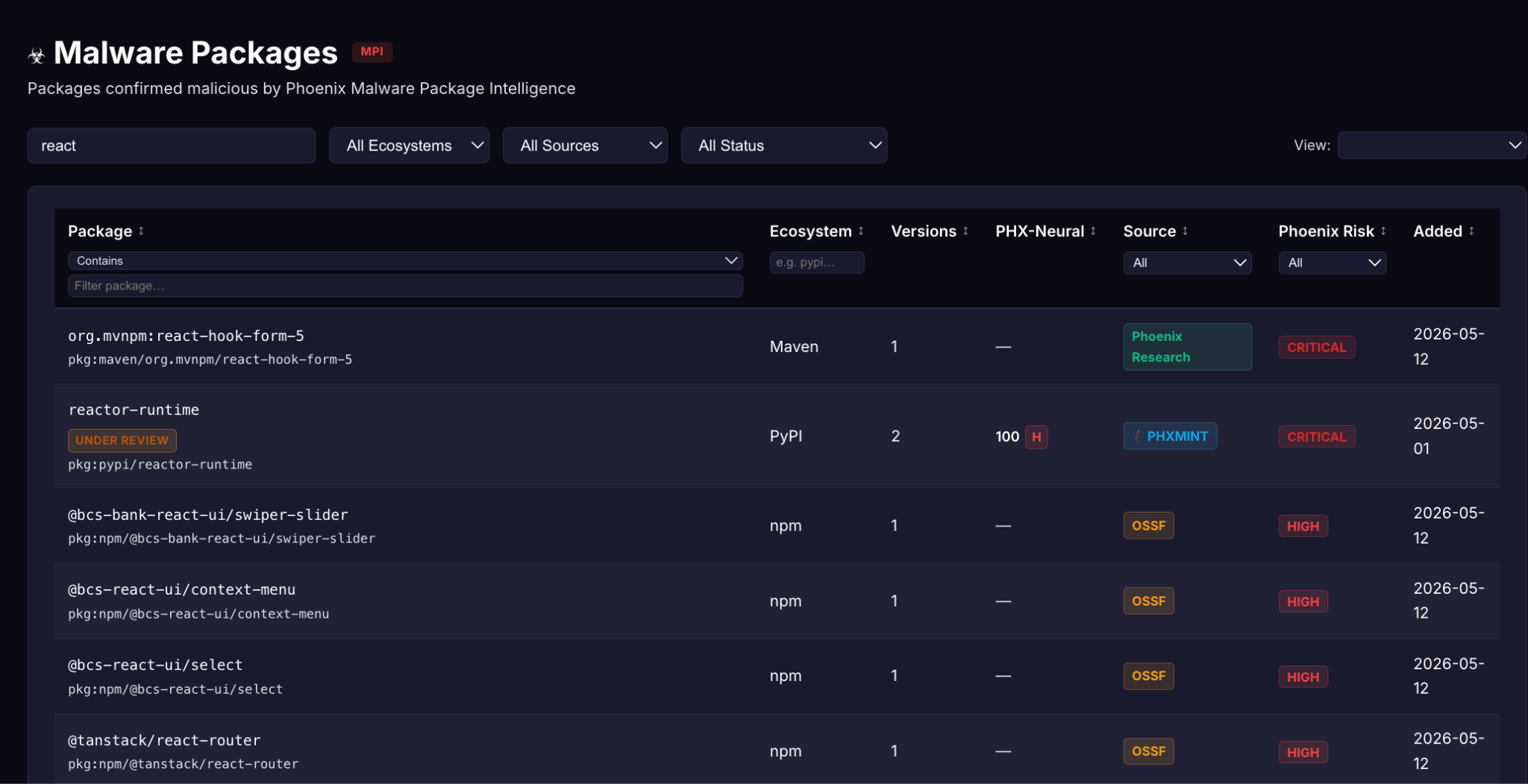
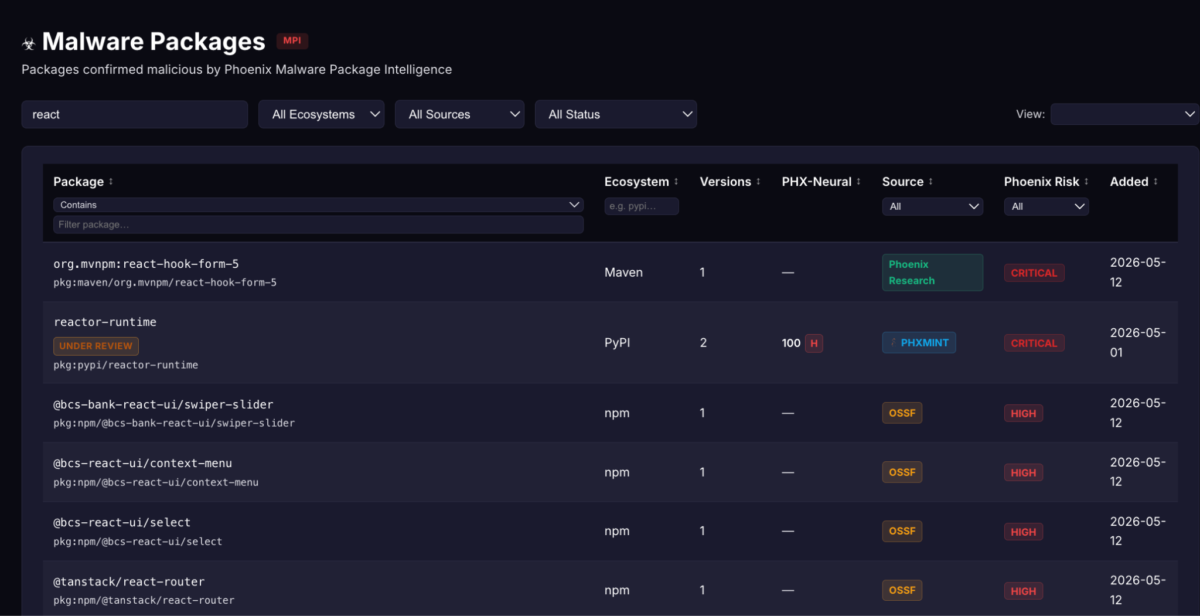
Phoenix Security Blue Malware Analysis – https://phxintel.security/malware.html
Where it bites: Any environment that installed a compromised version from 170 npm packages across 19 namespaces, or PyPI mistralai==2.4.6 / guardrails-ai==0.10.1. The preinstall hook fires on npm install — the package does not need to be imported. Highest blast radius: @opensearch-project/opensearch (versions 3.5.3, 3.6.2, 3.7.0, 3.8.0) at 1.3M weekly downloads; @mistralai/mistralai (2.2.2-2.2.4); @tanstack/react-router (1.169.5, 1.169.8).
Why it matters: OIDC federation — designed to eliminate long-lived tokens — was weaponized to mint fresh publish credentials. Infected packages carry valid Sigstore provenance attestations, which defeats provenance-based trust checks. Exfiltration through Session P2P is indistinguishable from normal IM traffic. Persistence in .claude/ hooks survives npm uninstall.
Patch status: Compromised versions removed from npm. PyPI mistralai and guardrails-ai quarantined. Safe versions: @opensearch-project/opensearch <=3.5.2 (or confirmed-clean post-quarantine release); @mistralai/mistralai <=2.2.1; mistralai PyPI <=2.4.5; guardrails-ai <=0.10.0.
Immediate action: Grep lockfiles for affected namespaces. Check for /tmp/transformers.pyz, .claude/router_runtime.js, pgmon.service. Rotate every secret on any CI runner that installed a compromised version. Block filev2.getsession.org, git-tanstack.com, api.masscan.cloud at egress DNS. Set npm config set ignore-scripts true on all CI runners.
Contents
ToggleVulnerability Overview – TeamPCP – Mini Shai Hulud
| Field | Value |
|---|---|
| Threat Group | TeamPCP (self-attributed: “With Love TeamPCP”) |
| Campaign Name | Mini Shai-Hulud |
| Affected Ecosystems | npm (170 packages, 19 namespaces), PyPI (2 packages) |
| Vulnerability Type | Supply chain compromise / OIDC federation abuse / self-propagating worm |
| CWE | CWE-829 (Inclusion of Functionality from Untrusted Control Sphere) |
| CVE | None assigned |
| Operational Severity | CRITICAL |
| Attack Vector | Network (npm install preinstall hook; PyPI import) |
| Active Exploitation | Confirmed — self-propagated across 170 packages in under 24 hours |
| Exposure Window | May 10–12, 2026 |
| Sigstore Bypass | Yes — malicious releases carry valid provenance attestations |
| KEV Status | Not listed |
Campaign
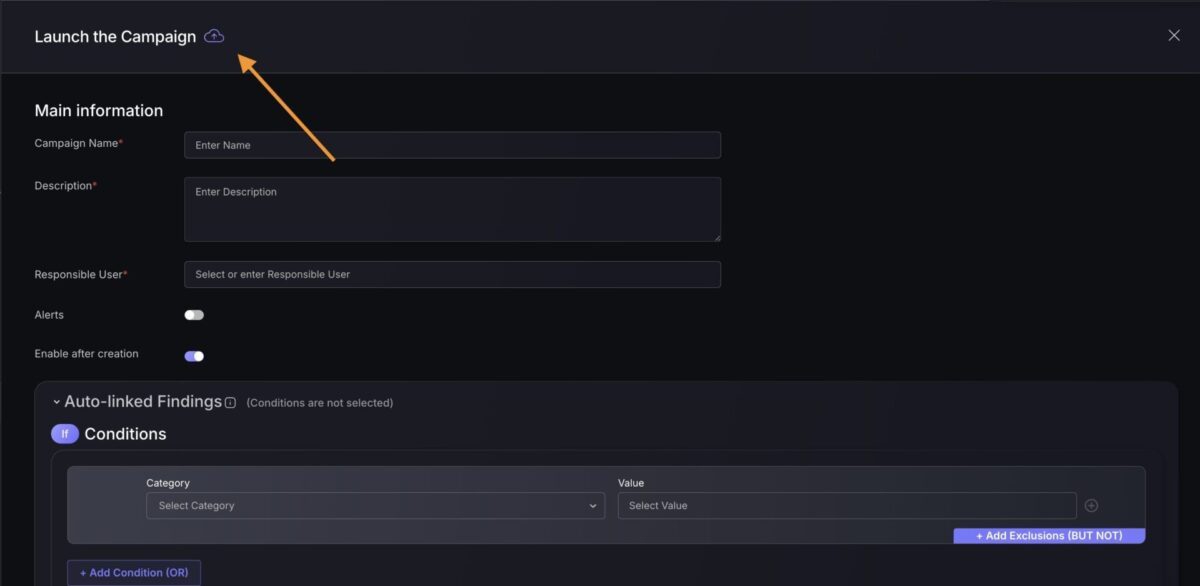
Campaign to identify if your libraries are affected by the react2shell CVE-2025-55182, CVE-2025-66478 in Phoenix security ASPM
Leverage the Phoenix Security SCA Scanner to identify the vulnerability blast radius
Scan with the Git automatic scanner or pull the repo individually (finding can be synced to Phoenix using –enable-phoenix and modifying the config: https://github.com/Security-Phoenix-demo/Shai-Hulud-Sha1-Hulud-V2-npm-compromise-scanner
Download the campaign:
Leverage Phoenix Security Filters and the campaign method to update/ retrieve the new vulnerabilities, or import those two files

Technical Anatomy
Root Cause: OIDC Federation Abuse via Orphaned CI Commit
The attack did not start with a phished password or a stolen API key. It started with an orphaned commit.
On May 10–11, 2026, TeamPCP identified an orphaned commit in a TanStack repository that was still reachable via a GitHub Actions workflow. The workflow had OIDC trust federation configured with npm — the standard mechanism for passwordless publishing, where CI can mint short-lived npm tokens on behalf of a registered publisher. By triggering a workflow run against the attacker-controlled commit, TeamPCP extracted the runner’s OIDC token and exchanged it with npm’s federation endpoint for a full publish credential on the TanStack namespace. Two-factor authentication was bypassed entirely: OIDC federation authenticates the CI workflow identity, not the human maintainer.
The TanStack postmortem attributes this to a chained attack — pull_request_target “Pwn Request” pattern, GitHub Actions cache poisoning across the fork-to-base trust boundary, and runtime memory extraction of an OIDC token from the runner process. No stored npm tokens were stolen.

Exploit Path
Step 1 — Entry via orphaned commit: An attacker-controlled commit in a fork runs inside a privileged workflow context because of a pull_request_target misconfiguration. The runner process holds an active OIDC JWT. The attacker reads it from runner memory during the test/cleanup phase.
Step 2 — OIDC token exchange for npm publish credential: The extracted OIDC JWT goes to npm’s trusted publisher federation endpoint. npm validates the token against the registered OIDC trust binding for the TanStack namespace and issues a publish token. The attacker now has authenticated publish access to every package in the namespace without any stored credentials.
Step 3 — Infected version publication with Sigstore provenance, then worm propagation: The malicious payload is packaged and published. Because the publish authenticates as the legitimate CI workflow identity, npm’s provenance system generates a valid Sigstore attestation. Consumers who inspect provenance records see a clean CI build. The worm then replicates: on any infected CI runner with OIDC federation, tanstack_runner.js repeats the token extraction and republishes under every accessible namespace.
The Three-Stage Payload (router_init.js, ~2.3 MB)
The payload is a single-line, 2.3 MB file obfuscated with javascript-obfuscator: string-array rotation, hex-encoded identifier lookups (_0x dispatcher called 2,864 times), control-flow flattening inside while(![]){} state machines, and a secondary XOR/AES decode layer (beautify()) that encodes 148 environment variable name accesses to defeat grep-based string extraction.
Stage 1 — Credential Harvest: The payload forks a detached child with all stdio suppressed (stdio: [‘ignore’,‘ignore’,‘ignore’]), then exits the parent cleanly. The child sweeps every major secrets plane:
- GitHub Actions: reads GITHUB_TOKEN, ACTIONS_ID_TOKEN_REQUEST_TOKEN; calls GET /repos/{repo}/actions/secrets?per_page=100 to enumerate all repository secrets
- AWS: reads AWS_ACCESS_KEY_ID, AWS_SECRET_ACCESS_KEY, AWS_ROLE_ARN; calls EC2 IMDSv2 (PUT /latest/api/token then role credential fetch); queries Secrets Manager and SSM Parameter Store across all regions via SigV4-signed API calls
- Kubernetes: reads /var/run/secrets/kubernetes.io/serviceaccount/token and ca.crt
- HashiCorp Vault: reads VAULT_TOKEN, VAULT_AUTH_TOKEN; connects to vault.svc.cluster.local:8200 (in-cluster Vault API)
- ECS: reads ECS task metadata endpoint at 169.254.170.2
Stage 2 — OIDC-Powered Worm Propagation: On runners with active OIDC federation, the payload calls ACTIONS_ID_TOKEN_REQUEST_URL to mint a fresh npm OIDC JWT, exchanges it for a publish token, queries npms.io to enumerate maintainer packages, and republishes infected versions under the latest dist-tag with valid Sigstore provenance attestations.
Stage 3 — Repository Poisoning via GitHub GraphQL: Using stolen GITHUB_TOKEN values, the implant calls the createCommitOnBranch GraphQL mutation to write payload files directly to repository branches. Target paths: .claude/router_runtime.js, .claude/settings.json, .claude/setup.mjs, .vscode/setup.mjs, .vscode/tasks.json, and arbitrary .github/workflows/ files. All commits are authored as claude@users.noreply.github.com, impersonating the Anthropic Claude Code GitHub App.
The .claude/ Persistence Mechanism
Claude Code supports a hooks configuration in .claude/settings.json that executes shell commands in response to tool events. By writing a copy of the worm into .claude/router_runtime.js and registering it in .claude/settings.json, the worm re-executes every time a developer uses Claude Code in the affected project directory. This persistence survives npm uninstall and package cache clearing. Package removal is not sufficient remediation.
Protect yourself with the latest threat intelligence, get access to PHOENIX BLUE Today
Exfiltration via Session P2P Protocol – TeamPCP – Mini Shai Hulud
Harvested credentials are not POSTed to a conventional HTTPS C2 server. The payload routes exfiltration through the Session decentralized P2P messaging network using the full embedded signalservice Protocol Buffers stack (Envelope, Content, DataMessage, WebSocketMessage, SharedConfigMessage). Traffic uploads to https://filev2.getsession.org/file/ over plain HTTP with tls.rejectUnauthorized: false, honoring any CI runner outbound proxy. To a network observer, this is regular encrypted P2P messaging traffic. No CDN provider or domain registrar can take down Session’s distributed snode network — DNS-level blocking of .getsession.org is the only practical perimeter control.
The PyPI Dropper: Simpler, Same Infrastructure
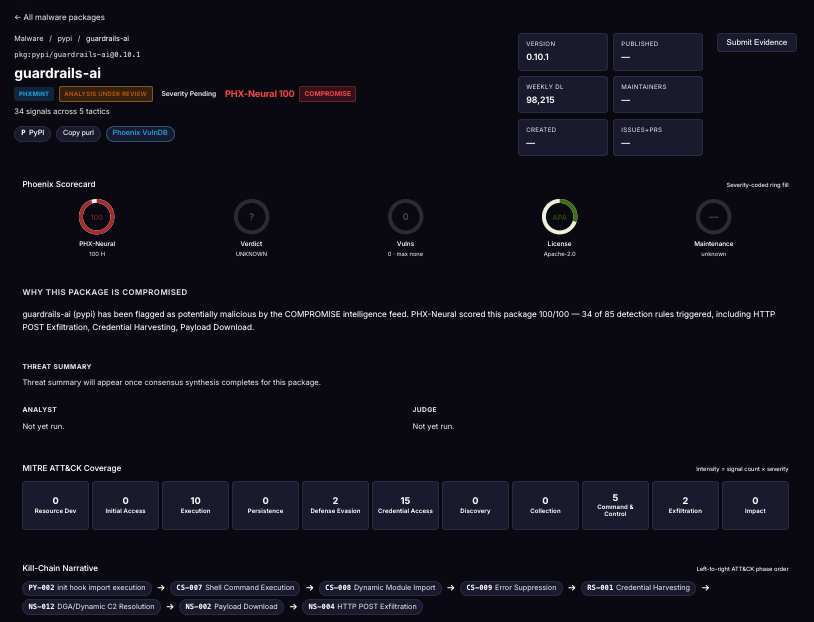
The guardrails-ai==0.10.1 PyPI compromise uses a different mechanism. On import (not install) on Linux, the package fetches https://git-tanstack.com/transformers.pyz, writes it to /tmp/transformers.pyz, and runs it with python3. No hash check. No signature verification. The same git-tanstack.com domain used as the attacker self-attribution page serves this payload. TeamPCP made no attempt to separate infrastructure between the npm and PyPI sides of the campaign.
Sandbox Detection – TeamPCP – Mini Shai Hulud
The payload checks two environment variables — TESTING_TAR_FAKE_PLATFORM and FAKE_PLATFORM — as sandbox-detection canaries. If either is set, the payload runs cleanly, producing a benign execution trace in sandboxes that fake platform metadata.
Affected Versions
npm — Highest Impact Packages
| Package | Compromised Versions | Safe Versions | Weekly Downloads |
|---|---|---|---|
| @opensearch-project/opensearch | 3.5.3, 3.6.2, 3.7.0, 3.8.0 | <=3.5.2 | ~1.3M |
| @mistralai/mistralai | 2.2.2, 2.2.3, 2.2.4 | <=2.2.1 | — |
| @mistralai/mistralai-azure | 1.7.1, 1.7.2, 1.7.3 | <=1.7.0 | — |
| @mistralai/mistralai-gcp | 1.7.1, 1.7.2, 1.7.3 | <=1.7.0 | — |
| @tanstack/react-router | 1.169.5, 1.169.8 | <=1.169.4 | ~12M |
| @tanstack/router-core | 1.169.5, 1.169.8 | <=1.169.4 | — |
| @tanstack/solid-router | 1.169.5, 1.169.8 | <=1.169.4 | — |
| @tanstack/vue-router | 1.169.5, 1.169.8 | <=1.169.4 | — |
| @uipath/* (64 packages) | Various | Verify per OSM CSV | — |
| @squawk/* (22 packages) | Various | Verify per OSM CSV | — |
| @tallyui/* (10 packages) | Various | Verify per OSM CSV | — |
| @beproduct/nestjs-auth | 0.1.2 through 0.1.19 | <=0.1.1 | — |
PyPI
| Package | Compromised Version | Safe Version | Notes |
|---|---|---|---|
| mistralai | 2.4.6 | <=2.4.5 | PyPI quarantined |
| guardrails-ai | 0.10.1 | <=0.10.0 | Executes on import; no hash check; fetches from git-tanstack.com |
Full 170-package inventory available at OpenSourceMalware.com under tag #mini-shai-hulud and Socket’s Mini Shai-Hulud campaign tracker at socket.dev/supply-chain-attacks/mini-shai-hulud.
Campaign Scope and Timeline
| Date / Time (UTC) | Event |
|---|---|
| May 10–11, 2026 | Orphaned TanStack CI commit exploited via pull_request_target; OIDC token extracted from runner memory |
| May 11, ~19:20 UTC | First wave: @tanstack/* — 42 packages, 84 malicious version pairs published |
| May 11, ~20:15–21:00 UTC | Wave expands to @uipath/* (64 packages), @squawk/* (22), @tallyui/* (10) |
| May 11, ~22:45 UTC | @mistralai/mistralai, @mistralai/mistralai-azure, @mistralai/mistralai-gcp compromised |
| May 12, ~00:30 UTC | @opensearch-project/opensearch compromised — versions 3.5.3, 3.6.2, 3.7.0, 3.8.0 |
| May 12, ~00:47 UTC | PyPI: mistralai==2.4.6 and guardrails-ai==0.10.1 published |
| May 12, ~03:05 UTC | OpenSearch and PyPI mistralai compromises; all-clear alert triggered |
| May 12 (during campaign) | TeamPCP serves “With Love TeamPCP” message from git-tanstack.com while campaign is live |
| May 12 | All npm compromised versions removed; PyPI projects quarantined |
Exposure Analysis
| Environment | Risk Level | Reason |
|---|---|---|
| CI/CD pipelines (affected packages installed) | CRITICAL | preinstall hook fires on install; OIDC token extraction; all runner secrets compromised |
| Kubernetes clusters | CRITICAL | Service account token harvest; in-cluster Vault API access; lateral movement capability |
| Cloud workloads (AWS EC2/ECS/GCE/Azure) | CRITICAL | IMDSv2 credential extraction; Secrets Manager and SSM queried across all regions |
| Developer machines | HIGH | SSH keys, .env files, shell history, Git creds swept; .claude/ persistence survives package removal |
| CI with OIDC-federated npm publishing | CRITICAL | Worm self-propagates under stolen maintainer identity with valid Sigstore provenance |
| guardrails-ai==0.10.1 environments | HIGH | Payload fires on import; remote code execution with no integrity check |
| Pipelines with ignore-scripts=true | Not affected (npm) | Blocks preinstall hook chain at first hop |
Real-World Impact of TeamPCP – Mini Shai Hulud
Automated tooling detected 84 compromised TanStack artifacts within six minutes of publication — meaning detection exists and fires quickly. Six minutes is fast. It is not fast enough: CI pipelines that run on push will have installed compromised versions before any detection fires.
OpenSearch is the single highest blast-radius package in this campaign. At 1.3 million weekly npm downloads, it lands in observability stacks, search-backed services, and OpenSearch/Elasticsearch ingestion pipelines across thousands of organizations. Any application or pipeline that resolved versions 3.5.3, 3.6.2, 3.7.0, or 3.8.0 between May 12 00:29 UTC and quarantine time is in scope.
The Mistral AI SDK compromise hit npm and PyPI simultaneously. For organizations running LLM applications on the Mistral SDK, both the JavaScript and Python clients were poisoned in the same campaign wave.
The Sigstore provenance bypass is a structural problem with how provenance works. Organizations that implemented provenance verification as a supply chain control would have seen “verified provenance” badges on the malicious TanStack releases. The provenance record accurately shows that the package was published from a GitHub Actions run in the TanStack repository. It cannot indicate that the run evaluated attacker-controlled code. Provenance tells you where a package was built; it does not tell you whether that build environment was clean.
The Session P2P exfiltration channel is the hardest part to address at the network layer. No CDN provider, domain registrar, or certificate authority can take down Session’s snode swarm. Organizations that rely on domain reputation scoring for C2 detection have no visibility into this channel.
Detection Guidance
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| C2 / exfil | filev2.getsession.org | Session P2P file upload — npm-side exfiltration |
| C2 bootstrap | seed1.getsession.org | Session P2P service node bootstrap |
| Attacker API | api.masscan.cloud | Attacker-controlled infrastructure |
| PyPI dropper domain | git-tanstack.com | Serves transformers.pyz and self-attribution page |
| PyPI dropper URL | git-tanstack.com/transformers.pyz | Remote payload fetched by guardrails-ai 0.10.1 on import |
| Persistence path | .claude/router_runtime.js | Claude Code hook worm persistence — survives npm uninstall |
| Persistence path | .claude/settings.json | Registers worm as Claude Code tool event handler |
| Persistence path | .claude/setup.mjs | ESM loader shim |
| Persistence path | .vscode/setup.mjs | VS Code ESM loader |
| Persistence path | .vscode/tasks.json | VS Code workspace task auto-run |
| PyPI dropper write | /tmp/transformers.pyz | Written by guardrails-ai 0.10.1 on import |
| Commit author spoof | claude@users.noreply.github.com | Injected commits masquerading as Claude Code agent |
| Attacker GitHub | github.com/voicproducoes | Repo: “A Mini Shai-Hulud has Appeared”; ID 269549300 |
File Hashes (SHA-256)
| SHA-256 Hash | Artifact |
|---|---|
| ab4fcadaec49c03278063dd269ea5eef82d24f2124a8e15d7b90f2fa8601266c | router_init.js / router_runtime.js (~2.3 MB obfuscated implant) |
| 2ec78d556d696e208927cc503d48e4b5eb56b31abc2870c2ed2e98d6be27fc96 | tanstack_runner.js (worm propagation loader) |
Detection Queries
Lockfile scan:
grep -E “(@tanstack|@uipath|@squawk|@mistralai|@opensearch-project)/” \
package-lock.json pnpm-lock.yaml yarn.lock 2>/dev/null
Filesystem persistence check:
ls -la ~/.claude/router_runtime.js ~/.claude/setup.mjs \
~/.vscode/setup.mjs /tmp/transformers.pyz /tmp/pglog 2>/dev/null
Git history check (run per repo):
git log –all –author=’claude@users.noreply.github.com’ –since=’2026-05-10′
router_init.js hash check:
find . -path ‘*/node_modules/*/router_init.js’ -exec sha256sum {} \; 2>/dev/null
MITRE ATT&CK Mapping
| Technique | Description | Campaign Application |
|---|---|---|
| T1195.002 | Supply Chain Compromise: Software Supply Chain | 170 npm packages, 2 PyPI packages poisoned |
| T1552.005 | Cloud Instance Metadata API | IMDSv2 credential extraction from EC2/ECS |
| T1552.004 | Unsecured Credentials: Private Keys | SSH keys, TLS certs, cloud service principal files |
| T1543.002 | Create/Modify System Process: Systemd Service | pgmon.service persistence (consistent with prior TeamPCP waves) |
| T1048.002 | Exfiltration Over Alternative Protocol | Session P2P network instead of HTTP C2 |
| T1036 | Masquerading | Commits spoofed as claude@users.noreply.github.com; pgmon service name |
| T1059.007 | Command and Scripting Interpreter: JavaScript | Bun runtime used as LOLBin for payload execution |
| T1176 | Browser Extensions / IDE Persistence | Persistence via .vscode/tasks.json and .claude/settings.json |
Remediation Guidance
Immediate Actions
- Pin away from compromised versions. Update all lockfiles to exclude compromised version ranges. For @tanstack/* packages, pin to versions prior to 1.169.5 or the latest verified clean release post-quarantine.
- Block C2 infrastructure at DNS egress: filev2.getsession.org, seed1.getsession.org, git-tanstack.com, api.masscan.cloud. IP-based blocking is impractical for the Session snode swarm — DNS-level blocking is required.
- Rotate all secrets on any affected CI runner. Any workflow that ran npm install during May 10–12, 2026 and resolved a compromised version should treat all runner secrets as compromised: GitHub PATs, OIDC federation bindings, AWS access keys, Kubernetes service account tokens, HashiCorp Vault tokens, Docker registry credentials, npm publish tokens.
- Remove .claude/ and .vscode/ persistence artifacts. npm uninstall is not sufficient. Check all developer home directories and project roots for: .claude/router_runtime.js, .claude/settings.json (inspect for unknown hooks), .vscode/tasks.json (inspect for unknown tasks), .claude/setup.mjs, .vscode/setup.mjs.
- Audit recent commits for spoofed claude@ authorship. Run git log –all –author=‘claude@users.noreply.github.com’ –since=‘2026-05-10’ across every repository your CI has write access to. Commits with this identity not initiated through the legitimate Claude Code GitHub App are attacker-injected.
- Uninstall affected PyPI packages. Remove mistralai==2.4.6 and guardrails-ai==0.10.1 immediately. Delete /tmp/transformers.pyz if present.
- Revoke and re-establish npm Trusted Publisher OIDC bindings for any package published from affected repositories. Confirm the publishing workflow is clean before re-establishing federation.
- Audit npm publish logs for unexpected version bumps from your organization’s packages, particularly versions published from GitHub Actions runners not initiated by a team member.
Long-Term Hardening
Disable npm install scripts on all CI runners: npm config set ignore-scripts true (or pnpm config set ignore-scripts true). This single line blocks the entire preinstall chain at the first hop. Most CI environments do not legitimately need lifecycle hooks from dependencies.
Restrict OIDC token scopes in GitHub Actions. Set permissions: id-token: none in all workflows that do not publish. Restrict id-token: write to only the specific job that publishes. Never grant OIDC token permissions to jobs that run attacker-influenced code.
Do not treat Sigstore provenance as a security gate on its own. Provenance verifies that a package was published from a specific CI workflow — not that the workflow ran trusted code. An attacker who can execute in GitHub Actions can generate valid Sigstore attestations for malicious packages.
Audit all pull_request_target workflows for PWN request patterns. If any step checks out PR head code, it is exploitable. Use poutine (Boost Security) or Zizmor for automated scanning.
Implement a version adoption delay policy. Community detection of supply chain attacks typically happens within minutes to hours. A 24–48 hour hold on new patch versions for non-critical CI dependencies provides a meaningful window for community detection to surface before your pipelines install.
Phoenix Security Recommendations
Mini Shai-Hulud had no CVE, no CVSS score, and no NVD entry. It compromised developer tooling and AI SDK infrastructure running with elevated trust in CI environments. For organizations with any of the 170 affected packages across their repository estate, the remediation surface is large and ownership is fragmented across multiple teams.
Attack surface management: Phoenix identifies which CI/CD pipelines and container images reference compromised package versions and maps whether those pipelines run in environments with OIDC federation enabled. For organizations with hundreds of repositories consuming @tanstack/, @mistralai/, or @opensearch-project/* packages, Phoenix provides a single view of which pipelines resolved compromised versions during the exposure window.
Contextual deduplication: The same compromised @opensearch-project/opensearch version appearing across 50 repositories does not generate 50 separate tickets. Phoenix correlates findings across all environments into a single prioritized backlog, surfacing the highest-risk instances — those with active cloud credentials or Kubernetes service account access — first.
Reachability analysis: Phoenix distinguishes between repositories where a compromised package version was declared in a lockfile versus those where the preinstall hook actually ran during a CI job. An environment with the package in its lockfile but no recent CI run has a materially different risk profile than one that ran npm install in the exposure window. That distinction drives remediation prioritization: secret rotation is urgent only where the hook executed.
Remediation campaigns: Create a Phoenix campaign to track lockfile remediation across all affected repositories, secret rotation completion per CI runner, .claude/ and .vscode/ persistence cleanup, OIDC federation rebuild, and Kubernetes pod cleanup for environments with the lateral movement variant. Assign owners per repository and track fix verification through to confirmed clean state.
Ownership attribution: Mini Shai-Hulud hit 19 namespaces across packages likely owned by multiple teams in any large organization. Phoenix maps vulnerable package references to responsible engineering teams automatically, making cross-team coordination tractable at scale.
If you are running Phoenix Security, the campaign configuration for Mini Shai-Hulud is ready to import. It includes all 170 compromised package versions across 19 namespaces — @tanstack/, @opensearch-project/, @mistralai/, @uipath/, @squawk/, @tallyui/ and more — pre-loaded as library filters. Importing the config creates an instant remediation campaign scoped to your estate, with ownership attribution per team and fix verification tracking.
Phoenix Security open-sourced a dedicated scanner for Sha1-Hulud / Shai-Hulud indicators across npm and PyPI → github.com/Security-Phoenix-demo/Shai-Hulud-Sha1-Hulud-V2-npm-compromise-scanner
Run it against your dependency tree to identify affected package versions, lifecycle script changes, and known IOCs across all five TeamPCP waves.
The results are clear:
- Bazaarvoice saved $6.3M in developer time and for teams removed critical in the first weeks of adoption
- ClearBank cut critical container vulnerabilities by 96–99% and reclaimed 4 hours per engineer per week.
- A global AdTech company saved an equivalent of 1.5M in development hours and reduced SCA-to-container noise by 82.4%
- Optimizely has been able to act on vulnerabilities sitting on the backlog.
Or learn how Phoenix Security slashed millions in wasted dev time for fintech, retail, and adtech leaders.
Fix with remediation. Don’t chase ghost vulnerabilities
Phoenix Security correlates vulnerable components with runtime workloads, identifies exposed pipelines via attack surface management, and assigns remediation ownership. A 170-package supply chain compromise becomes a trackable backlog with clear team accountability.
Full list of packages
| Mini Shai-Hulud — TeamPCP IOC Package List | |||
| Campaign: Mini Shai-Hulud | Group: TeamPCP | Date: May 12, 2026 | Severity: CRITICAL | CVE: None Assigned | |||
| Ecosystem | Package | Compromised Versions | Malware Report |
| NPM | agentwork-cli | 0.1.4, 0.1.5 | Open report |
| NPM | @beproduct/nestjs-auth | 0.1.2–0.1.19 | Open report |
| NPM | cmux-agent-mcp | 0.1.3–0.1.8 | Open report |
| NPM | cross-stitch | 1.1.3–1.1.6 | Open report |
| NPM | @dirigible-ai/sdk | 0.6.2, 0.6.3 | Open report |
| NPM | @draftauth/client | 0.2.1, 0.2.2 | Open report |
| NPM | @draftauth/core | 0.13.1, 0.13.2 | Open report |
| NPM | @draftlab/auth | 0.24.1, 0.24.2 | Open report |
| NPM | @draftlab/auth-router | 0.5.1, 0.5.2 | Open report |
| NPM | @draftlab/db | 0.16.1, 0.16.2 | Open report |
| NPM | git-branch-selector | 1.3.3–1.3.7 | Open report |
| NPM | git-git-git | 1.0.8–1.0.12 | Open report |
| NPM | @mesadev/rest | 0.28.3 | Open report |
| NPM | @mesadev/saguaro | 0.4.22 | Open report |
| NPM | @mesadev/sdk | 0.28.3 | Open report |
| NPM | @mistralai/mistralai | 2.2.2–2.2.4 | Open report |
| NPM | @mistralai/mistralai-azure | 1.7.1–1.7.3 | Open report |
| NPM | @mistralai/mistralai-gcp | 1.7.1–1.7.3 | Open report |
| NPM | ml-toolkit-ts | 1.0.4, 1.0.5 | Open report |
| NPM | @ml-toolkit-ts/preprocessing | 1.0.2, 1.0.3 | Open report |
| NPM | @ml-toolkit-ts/xgboost | 1.0.3, 1.0.4 | Open report |
| NPM | nextmove-mcp | 0.1.3–0.1.7 | Open report |
| NPM | @opensearch-project/opensearch | 3.5.3, 3.6.2, 3.7.0, 3.8.0 | Open report |
| NPM | safe-action | 0.8.3, 0.8.4 | Open report |
| NPM | @squawk/airport-data | 0.7.4–0.7.7 | Open report |
| NPM | @squawk/airports | 0.6.2–0.6.5 | Open report |
| NPM | @squawk/airspace | 0.8.1–0.8.4 | Open report |
| NPM | @squawk/airspace-data | 0.5.3–0.5.6 | Open report |
| NPM | @squawk/airway-data | 0.5.4–0.5.7 | Open report |
| NPM | @squawk/airways | 0.4.2–0.4.5 | Open report |
| NPM | @squawk/fix-data | 0.6.4–0.6.7 | Open report |
| NPM | @squawk/fixes | 0.3.2–0.3.5 | Open report |
| NPM | @squawk/flight-math | 0.5.4–0.5.7 | Open report |
| NPM | @squawk/flightplan | 0.5.2–0.5.5 | Open report |
| NPM | @squawk/geo | 0.4.4–0.4.7 | Open report |
| NPM | @squawk/icao-registry | 0.5.2–0.5.5 | Open report |
| NPM | @squawk/icao-registry-data | 0.8.4–0.8.7 | Open report |
| NPM | @squawk/mcp | 0.9.1–0.9.4 | Open report |
| NPM | @squawk/navaid-data | 0.6.4–0.6.7 | Open report |
| NPM | @squawk/navaids | 0.4.2–0.4.5 | Open report |
| NPM | @squawk/notams | 0.3.6–0.3.9 | Open report |
| NPM | @squawk/procedure-data | 0.7.3–0.7.6 | Open report |
| NPM | @squawk/procedures | 0.5.2–0.5.5 | Open report |
| NPM | @squawk/types | 0.8.1–0.8.4 | Open report |
| NPM | @squawk/units | 0.4.3–0.4.6 | Open report |
| NPM | @squawk/weather | 0.5.6–0.5.9 | Open report |
| NPM | @supersurkhet/cli | 0.0.2–0.0.7 | Open report |
| NPM | @supersurkhet/sdk | 0.0.2–0.0.7 | Open report |
| NPM | @tallyui/components | 1.0.1–1.0.3 | Open report |
| NPM | @tallyui/connector-medusa | 1.0.1–1.0.3 | Open report |
| NPM | @tallyui/connector-shopify | 1.0.1–1.0.3 | Open report |
| NPM | @tallyui/connector-vendure | 1.0.1–1.0.3 | Open report |
| NPM | @tallyui/connector-woocommerce | 1.0.1–1.0.3 | Open report |
| NPM | @tallyui/core | 0.2.1–0.2.3 | Open report |
| NPM | @tallyui/database | 1.0.1–1.0.3 | Open report |
| NPM | @tallyui/pos | 0.1.1–0.1.3 | Open report |
| NPM | @tallyui/storage-sqlite | 0.2.1–0.2.3 | Open report |
| NPM | @tallyui/theme | 0.2.1–0.2.3 | Open report |
| NPM | @tanstack/arktype-adapter | 1.166.12, 1.166.15 | Open report |
| NPM | @tanstack/eslint-plugin-router | 1.161.9, 1.161.12 | Open report |
| NPM | @tanstack/eslint-plugin-start | 0.0.4, 0.0.7 | Open report |
| NPM | @tanstack/history | 1.161.9, 1.161.12 | Open report |
| NPM | @tanstack/nitro-v2-vite-plugin | 1.154.12, 1.154.15 | Open report |
| NPM | @tanstack/react-router | 1.169.5, 1.169.8 | Open report |
| NPM | @tanstack/react-router-devtools | 1.166.16, 1.166.19 | Open report |
| NPM | @tanstack/react-router-ssr-query | 1.166.15, 1.166.18 | Open report |
| NPM | @tanstack/react-start | 1.167.68, 1.167.71 | Open report |
| NPM | @tanstack/react-start-client | 1.166.51, 1.166.54 | Open report |
| NPM | @tanstack/react-start-rsc | 0.0.47, 0.0.50 | Open report |
| NPM | @tanstack/react-start-server | 1.166.55, 1.166.58 | Open report |
| NPM | @tanstack/router-cli | 1.166.46, 1.166.49 | Open report |
| NPM | @tanstack/router-core | 1.169.5, 1.169.8 | Open report |
| NPM | @tanstack/router-devtools | 1.166.16, 1.166.19 | Open report |
| NPM | @tanstack/router-devtools-core | 1.167.6, 1.167.9 | Open report |
| NPM | @tanstack/router-generator | 1.166.45, 1.166.48 | Open report |
| NPM | @tanstack/router-plugin | 1.167.38, 1.167.41 | Open report |
| NPM | @tanstack/router-ssr-query-core | 1.168.3, 1.168.6 | Open report |
| NPM | @tanstack/router-utils | 1.161.11, 1.161.14 | Open report |
| NPM | @tanstack/router-vite-plugin | 1.166.53, 1.166.56 | Open report |
| NPM | @tanstack/solid-router | 1.169.5, 1.169.8 | Open report |
| NPM | @tanstack/solid-router-devtools | 1.166.16, 1.166.19 | Open report |
| NPM | @tanstack/solid-router-ssr-query | 1.166.15, 1.166.18 | Open report |
| NPM | @tanstack/solid-start | 1.167.65, 1.167.68 | Open report |
| NPM | @tanstack/solid-start-client | 1.166.50, 1.166.53 | Open report |
| NPM | @tanstack/solid-start-server | 1.166.54, 1.166.57 | Open report |
| NPM | @tanstack/start-client-core | 1.168.5, 1.168.8 | Open report |
| NPM | @tanstack/start-fn-stubs | 1.161.9, 1.161.12 | Open report |
| NPM | @tanstack/start-plugin-core | 1.169.23, 1.169.26 | Open report |
| NPM | @tanstack/start-server-core | 1.167.33, 1.167.36 | Open report |
| NPM | @tanstack/start-static-server-functions | 1.166.44, 1.166.47 | Open report |
| NPM | @tanstack/start-storage-context | 1.166.38, 1.166.41 | Open report |
| NPM | @tanstack/valibot-adapter | 1.166.12, 1.166.15 | Open report |
| NPM | @tanstack/virtual-file-routes | 1.161.10, 1.161.13 | Open report |
| NPM | @tanstack/vue-router | 1.169.5, 1.169.8 | Open report |
| NPM | @tanstack/vue-router-devtools | 1.166.16, 1.166.19 | Open report |
| NPM | @tanstack/vue-router-ssr-query | 1.166.15, 1.166.18 | Open report |
| NPM | @tanstack/vue-start | 1.167.61, 1.167.64 | Open report |
| NPM | @tanstack/vue-start-client | 1.166.46, 1.166.49 | Open report |
| NPM | @tanstack/vue-start-server | 1.166.50, 1.166.53 | Open report |
| NPM | @tanstack/zod-adapter | 1.166.12, 1.166.15 | Open report |
| NPM | @taskflow-corp/cli | 0.1.24–0.1.29 | Open report |
| NPM | @tolka/cli | 1.0.2–1.0.6 | Open report |
| NPM | ts-dna | 3.0.1–3.0.4 | Open report |
| NPM | @uipath/access-policy-sdk | 0.3.1 | Open report |
| NPM | @uipath/access-policy-tool | 0.3.1 | Open report |
| NPM | @uipath/admin-tool | 0.1.1 | Open report |
| NPM | @uipath/agent-sdk | 1.0.2 | Open report |
| NPM | @uipath/agent-tool | 1.0.1 | Open report |
| NPM | @uipath/agent.sdk | 0.0.18 | Open report |
| NPM | @uipath/aops-policy-tool | 0.3.1 | Open report |
| NPM | @uipath/ap-chat | 1.5.7 | Open report |
| NPM | @uipath/api-workflow-tool | 1.0.1 | Open report |
| NPM | @uipath/apollo-core | 5.9.2 | Open report |
| NPM | @uipath/apollo-react | 4.24.5 | Open report |
| NPM | @uipath/apollo-wind | 2.16.2 | Open report |
| NPM | @uipath/auth | 1.0.1 | Open report |
| NPM | @uipath/case-tool | 1.0.1 | Open report |
| NPM | @uipath/cli | 1.0.1 | Open report |
| NPM | @uipath/codedagent-tool | 1.0.1 | Open report |
| NPM | @uipath/codedagents-tool | 0.1.12 | Open report |
| NPM | @uipath/codedapp-tool | 1.0.1 | Open report |
| NPM | @uipath/common | 1.0.1 | Open report |
| NPM | @uipath/context-grounding-tool | 0.1.1 | Open report |
| NPM | @uipath/data-fabric-tool | 1.0.2 | Open report |
| NPM | @uipath/docsai-tool | 1.0.1 | Open report |
| NPM | @uipath/filesystem | 1.0.1 | Open report |
| NPM | @uipath/flow-tool | 1.0.2 | Open report |
| NPM | @uipath/functions-tool | 1.0.1 | Open report |
| NPM | @uipath/gov-tool | 0.3.1 | Open report |
| NPM | @uipath/identity-tool | 0.1.1 | Open report |
| NPM | @uipath/insights-sdk | 1.0.1 | Open report |
| NPM | @uipath/insights-tool | 1.0.1 | Open report |
| NPM | @uipath/integrationservice-sdk | 1.0.2 | Open report |
| NPM | @uipath/integrationservice-tool | 1.0.2 | Open report |
| NPM | @uipath/llmgw-tool | 1.0.1 | Open report |
| NPM | @uipath/maestro-sdk | 1.0.1 | Open report |
| NPM | @uipath/maestro-tool | 1.0.1 | Open report |
| NPM | @uipath/orchestrator-tool | 1.0.1 | Open report |
| NPM | @uipath/packager-tool-apiworkflow | 0.0.19 | Open report |
| NPM | @uipath/packager-tool-bpmn | 0.0.9 | Open report |
| NPM | @uipath/packager-tool-case | 0.0.9 | Open report |
| NPM | @uipath/packager-tool-connector | 0.0.19 | Open report |
| NPM | @uipath/packager-tool-flow | 0.0.19 | Open report |
| NPM | @uipath/packager-tool-functions | 0.1.1 | Open report |
| NPM | @uipath/packager-tool-webapp | 1.0.6 | Open report |
| NPM | @uipath/packager-tool-workflowcompiler | 0.0.16 | Open report |
| NPM | @uipath/packager-tool-workflowcompiler-browser | 0.0.34 | Open report |
| NPM | @uipath/platform-tool | 1.0.1 | Open report |
| NPM | @uipath/project-packager | 1.1.16 | Open report |
| NPM | @uipath/resource-tool | 1.0.1 | Open report |
| NPM | @uipath/resourcecatalog-tool | 0.1.1 | Open report |
| NPM | @uipath/resources-tool | 0.1.11 | Open report |
| NPM | @uipath/robot | 1.3.4 | Open report |
| NPM | @uipath/rpa-legacy-tool | 1.0.1 | Open report |
| NPM | @uipath/rpa-tool | 0.9.5 | Open report |
| NPM | @uipath/solution-packager | 0.0.35 | Open report |
| NPM | @uipath/solution-tool | 1.0.1 | Open report |
| NPM | @uipath/solutionpackager-sdk | 1.0.11 | Open report |
| NPM | @uipath/solutionpackager-tool-core | 0.0.34 | Open report |
| NPM | @uipath/tasks-tool | 1.0.1 | Open report |
| NPM | @uipath/telemetry | 0.0.7 | Open report |
| NPM | @uipath/test-manager-tool | 1.0.2 | Open report |
| NPM | @uipath/tool-workflowcompiler | 0.0.12 | Open report |
| NPM | @uipath/traces-tool | 1.0.1 | Open report |
| NPM | @uipath/ui-widgets-multi-file-upload | 1.0.1 | Open report |
| NPM | @uipath/uipath-python-bridge | 1.0.1 | Open report |
| NPM | @uipath/vertical-solutions-tool | 1.0.1 | Open report |
| NPM | @uipath/vss | 0.1.6 | Open report |
| NPM | @uipath/widget.sdk | 1.2.3 | Open report |
| NPM | wot-api | 0.8.1–0.8.4 | Open report |
| PYPI | guardrails-ai | 0.10.1 | Open report |
| PYPI | mistralai | 2.4.6 | Open report |
| GITHUB | voicproducoes | n/a | attacker account |
References
- OpenSourceMalware.com — Mini Shai-Hulud Campaign Tracker (tag: #mini-shai-hulud): https://opensourcemalware.com
- Socket Security Research — TanStack npm Packages Compromised in Ongoing Mini Shai-Hulud Supply-Chain Attack: https://socket.dev/blog/tanstack-npm-packages-compromised-mini-shai-hulud
- Socket Security — Mini Shai-Hulud Campaign Tracker (live): https://socket.dev/supply-chain-attacks/mini-shai-hulud
- TanStack — Postmortem: OIDC Token Extraction via pull_request_target (GitHub repository)
- OpenSourceMalware.com — 6mile: TeamPCP Hits 160+ Packages Including OpenSearch and Mistral AI
- Wiz Research — Trivy Compromised by TeamPCP: https://wiz.io/blog/trivy-compromised-teampcp-supply-chain-attack
- Endor Labs — TeamPCP Isn’t Done: LiteLLM PyPI Compromise (upstream campaign context)
- Socket Security — CanisterWorm: npm Publisher Compromise Deploys Backdoor Across 29 Packages
- Aikido Security — TeamPCP Deploys CanisterWorm on NPM Following Trivy Compromise
- GitHub Advisory Database — GHSA-69fq-xp46-6×23 (Trivy ecosystem, upstream TeamPCP attribution)
- MITRE ATT&CK — T1195.002 Supply Chain Compromise: Software Supply Chain

















