Phoenix Security was honoured to host a sharp and honest conversation with Rick Doten, VP of Information Security and CISO at Centene Corporation’s North Carolina health plan, on Vulnerabilities, maturity model, and the NVD/CVE near death / Collapse
Rick Doten – VP, Information Security, Centene Corporation & CISO, North Carolina Medicaid Healthplan
With over 27 years of experience in cybersecurity and a deep background as both a Fractional CISO and strategist, Rick Doten brings a grounded, risk-based lens to today’s most pressing AppSec challenges. This session is about cutting through the noise, prioritizing what matters, and rethinking how we approach risk, remediation, and resilience in modern security.
Contents
Toggle1. Two Distinct Journeys, One Goal – Rick Doten View
| Stage | Typical Profile | Immediate Security Priority | ASPM Focus |
| Launching a programme | Fast-growing SaaS, scale-ups, or business units with <10 security staff | Visibility of software assets and quick wins that satisfy auditors | Auto-baseline every repo, map exposures to business context, push targeted remediation tickets |
| Chasing higher maturity | Enterprises with formal AppSec, threat-intel, and SOC teams | Shrinking mean-time-to-remediate (MTTR) and aligning fixes with threat activity | Continuous threat modelling, risk-based prioritisation, attack-path analytics, workflow automation |
Early-stage teams thrive on simplicity. A lightweight ASPM platform delivers unified dashboards, enables policy-as-code, and triggers developer-friendly tickets that close the riskiest gaps first. Mature programmes lean on the same visibility yet extend it with attack-graph context, kill-switch playbooks, and KPIs that prove value to the board.
2. The Code-Factory Challenge
Rick Doten and Francesco Cipollone discuss on Generative AI now ships code at a velocity few review cycles can match. Recent research shows that AI-assisted developers are more likely to insert exploitable flaws than peers writing by hand . Another survey of security teams links the spike in defects to limited manpower and governance .
Implication: every organisation—whether bootstrapping or operating at scale—must assume that freshly merged code carries latent risk. ASPM delivers guardrails by:
- auto-scanning pull requests before merge,
- enriching findings with exploit-maturity signals,
- looping results straight into sprint planning for near-real-time remediation.
3. CVE / NVD Gridlock: Why Your Backlog Grew Overnight Rick Doten View
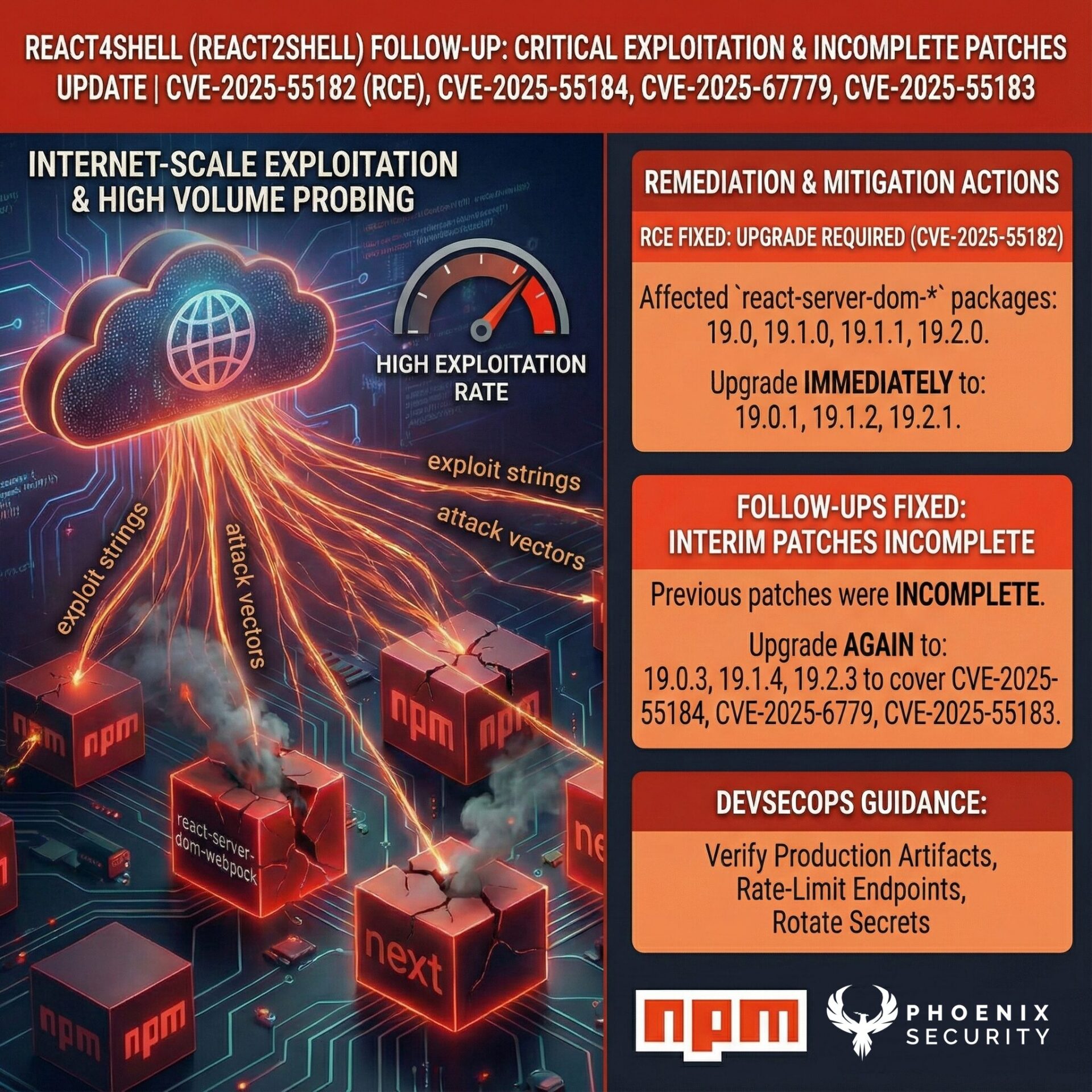
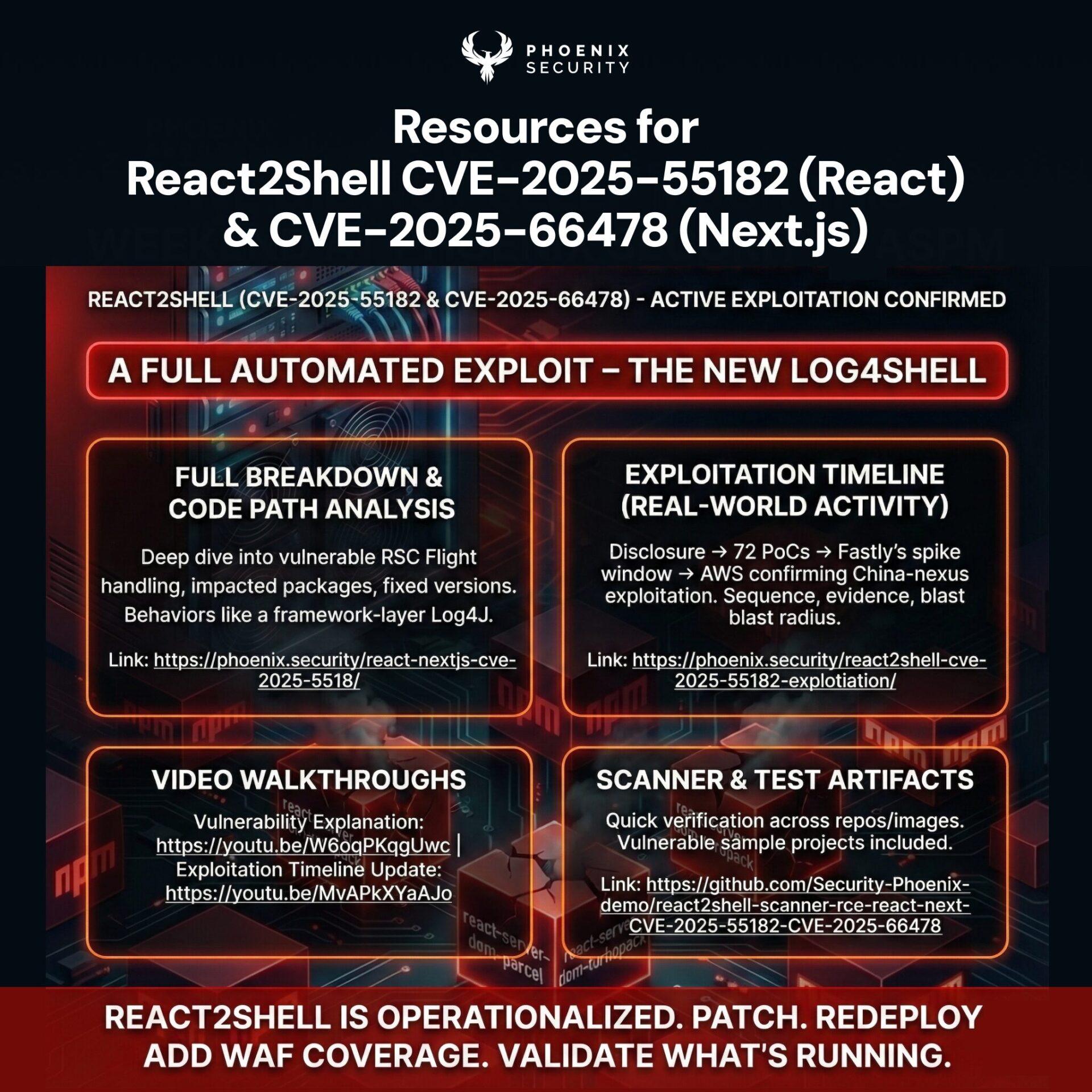
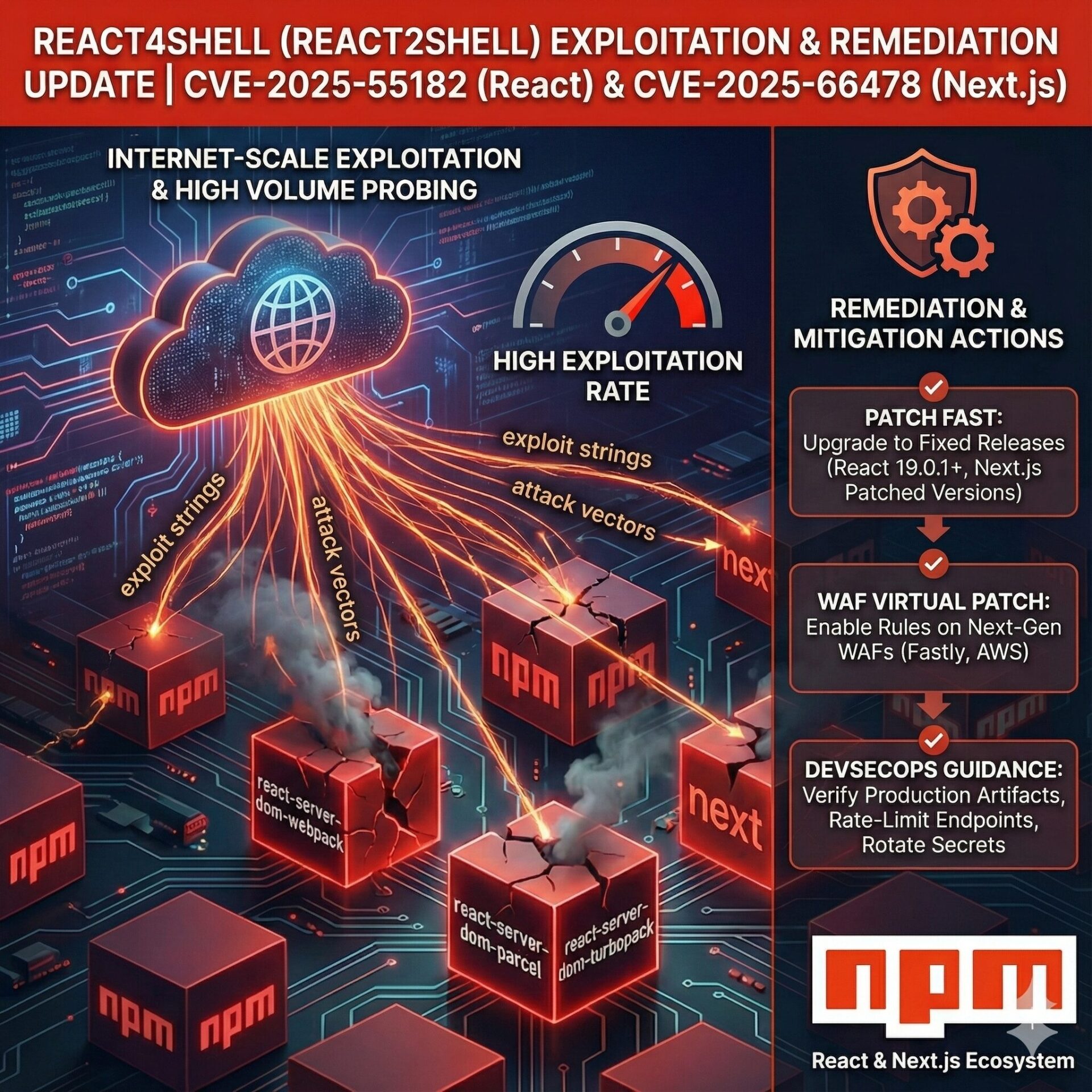
The National Vulnerability Database Rick Doten and Francesco Cipollone debate the crisis and mention that the NVD still faces a six-figure queue of unanalyzed CVEs, despite CISA’s “Vulnrichment” partnership and new vendor contracts. Delays create blind spots for scanners that depend on fully enriched records, pushing false assurance into dashboards.
Phoenix Security tracks NVD processing metrics daily and overlays them with exploit status to keep risk scores honest . When NVD metadata lags, the platform:
- Cross-references CISA’s Known Exploited Vulnerabilities list.
- Flags “backlog CVEs” that already appear in public proof-of-concept code.
- Boosts their priority—even if CVSS data is missing—so teams patch before headlines hit.
4. Action Plan
If you’re just starting
- Establish an inventory fast (repos, containers, cloud functions).
- Deploy policy templates that block default credentials and weak TLS ciphers.
- Integrate ASPM tickets with Jira or Azure DevOps; measure fixes in days, not quarters.
If you’re raising the bar
- Combine vulnerability data with threat-intel feeds to surface attack paths relevant to your stack.
- Automate “change-fail-safe” tasks—such as rollout guards or one-click container rebuilds—so remediation scales beyond human bandwidth.
- Track MTTR, exposure-hours, and exploit-path elimination as primary KPIs.
5. Why Phoenix Security
Phoenix Security’s ASPM engine unifies library, SBOM, runtime signals, and business context, turning noisy scan results into a ranked to-do list that developers actually accept. Teams cut remediation effort by up to 70 % while staying ahead of the NVD backlog and maintaining an index of 18+ sources to prevent NVD interruption and the boom in AI-generated code defects. Ready to run application security at the speed your business demands? Start your Phoenix Security trial today and turn backlog into burn-down.
How Phoenix Security Can Help

Organizations often face an overwhelming volume of security alerts, including false positives and duplicate vulnerabilities, which can distract from real threats. Traditional tools may overwhelm engineers with lengthy, misaligned lists that fail to reflect business objectives or the risk tolerance of product owners.

Phoenix Security offers a transformative solution through its Actionable Application Security Posture Management (ASPM), powered by AI-based Contextual Quantitative analysis and an innovative Threat Centric approach. This innovative approach correlates runtime data with code analysis and leverages the threats that are more likely to lead to zero day attacks and ransomware to deliver a single, prioritized list of vulnerabilities. This list is tailored to the specific needs of engineering teams and aligns with executive goals, reducing noise and focusing efforts on the most critical issues. Why do people talk about Phoenix

• Automated Triage: Phoenix streamlines the triage process using a customizable 4D risk formula, ensuring critical vulnerabilities are addressed promptly by the right teams.
• Contextual Deduplication: Utilizing canary token-based traceability, Phoenix accurately deduplicates and tracks vulnerabilities within application code and deployment environments, allowing teams to concentrate on genuine threats.
• Actionable Threat Intelligence: Phoenix provides real-time insights into vulnerability’ exploitability, combining runtime threat intelligence with application security data for precise risk mitigation.

By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.