
Although companies prioritize their vulnerabilities based on affected assets, severity and exposure time, there are a few other root things to consider other than these obvious actions.
On a bigger picture, vulnerability prioritization consists of four components. These components include:
- Assets Exposure
- Business Impact
- Threat Context
- Vulnerability Severity
If we keep these vulnerability assessment and prioritization factors aside, then there are a few other underlying components that are important to study before we conclude our prioritization.
Contents
ToggleConsiderable Vulnerability Prioritization Factors
The vulnerability scanners present us with a lot of data about internal and external vulnerabilities, but businesses tend to ignore the identity of such flaws. Also, they rarely study their technology stack when it comes to prioritizing potential vulnerabilities. Here, we have defined the importance of these factors:
- Internal & External Vulnerabilities
Before, we compare internal and external vulnerabilities for prioritization purposes. We need to differentiate both types:
External Vulnerabilities
Many popular scanners tend to scan our networks both internally and externally. The external scan is focused on finding loopholes in your network’s firewall. The hackers can use external vulnerabilities to get inside your network by bypassing your firewall and security.
These external vulnerabilities are often more dangerous because they are externally exposed to the internet. Hence, any attacker can exploit them using a range of methods and techniques. The most common external threats are DDoS attacks, Session Hijacking, Malware attacks or password attacks.
Internal Vulnerabilities
According to IBM’s 2016 Cyber Security Intelligence Index, 60 percent of all attacks are carried out by insiders. Some employees often become a threat to their own company when they become malicious actors to fulfill their own purposes inside an organization.
Many data breaches are also caused by internal vulnerabilities that tend to be more dangerous. The malicious actor is already inside the network, and he can do more harm than anyone present outside the network.
Internal vs External Scans: Which Vulnerabilities to Prioritize
Both externally and internally scanned vulnerabilities are equally damaging for a company, but this impact also relies on the industry. Insider threat is more prevalent in some industries, where internal vulnerabilities can potentially leak the secrets of a company.
On the other hand, external attacks are often carried out by malicious actors who tend to sell a company’s data. They penetrate your network to find and exploit vulnerabilities to steal data and demand ransom.
In conclusion, companies should prioritize those types of threats that are more damaging to their IT assets across the organization. If external vulnerabilities can do more harm and are easily exploitable, then it should be set on high priority.
However, if internal security infrastructure is weak enough that any normal employee can potentially compromise secret data by exploiting rules or small vulnerabilities then internally found vulnerabilities should be prioritized.
- Technology Stack
The CyberSecurityWorks conducted a detailed research on vulnerabilities residing in various Technology Stacks. According to CSW’s findings, there are 4849 vulnerabilities in tech stacks. Majority of these vulnerabilities resided in VPN, Access Service, Database, Web Proxy, Web Gateway, CRM, Business Intelligence, Backup & Storage, Online conference.
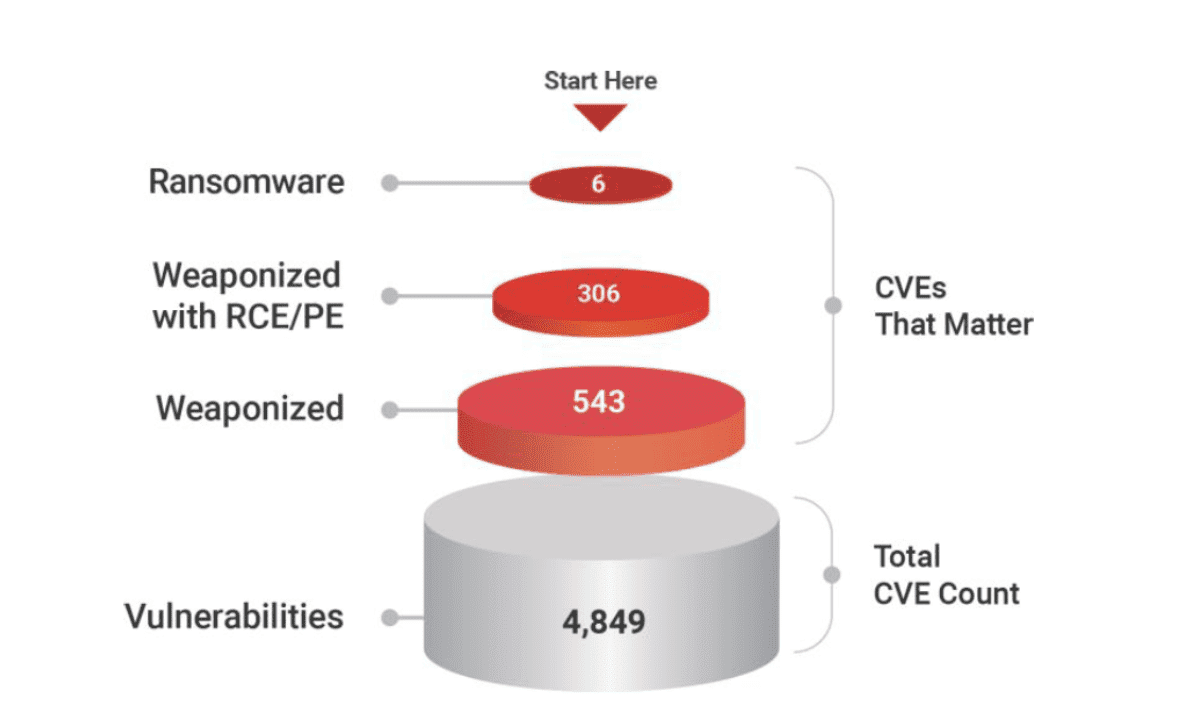
Out of all these vulnerabilities, 543 are said to be weaponized while 306 were prone to Remote Code Execution (RCE). These vulnerabilities in Tech Stacks were checked through various popular vulnerability scanners but the results were rather disappointing because these scanners potentially missed 100+ vulnerabilities. Some popular scanners like Nessus, Nexpose, and Qualys missed the following CVEs:
This is a clear explanation of how threat actors can easily find vulnerabilities that remain undetectable in Technology Stacks of various companies. Therefore, we probably need to use multiple scanners that always catch all potential threats according to their own parameters.
That’s exactly where AppSec Phoenix’s Ultimate Tool comes into play. This tool integrates with all popular scanners to find and report all vulnerabilities interactively on your dashboard. The tool offers various view windows for developers, app owners and pentesters to find and prioritize vulnerabilities using a range of integrated scanners.
3. CVE Numbers
Many scanning tools first find vulnerabilities against CVEs (Common Vulnerabilities and Exposures). The information is easily accessible on various CVE numbers. This information can be used to study the impact, extent, severity and exploitation possibilities of a vulnerability.
There are a range of CVE detail finders available to extract all the information about a particular vulnerability and how to remediate it. You can find information on many CVEs at CVEDetails, Mitre and NIST.
The vulnerabilities that have a CVE number are often easily exploited because they are common among hackers and malicious actors. Such vulnerabilities are easy to exploit because malicious scripts are readily available to attack the vulnerability. Therefore, CVEs should be fixed on top priority.
Mitre is the organization that acts as the editor body for these CVEs. They also published the list of most common CVEs of 2021. After running all vulnerability scans, you can scroll through this list to find all potential threats that might be found in your system.
AppSec Phoenix’s All-In-One Solution
It is always challenging for companies to pass their applications through all the scanners to collect data and then process it to generate reports to prioritize their risks. This approach is prone to errors, and many potential threats can be missed without a proper controlling system.
AppSec offers a single aggregation point to scan, find, prioritize and fix potential threats across all your assets. It comes with a range of indicators to tell you all potential pain points and vulnerabilities residing in your system, along with their severity level. Also, it provides an interactive dashboard for different parties to view vulnerabilities. Have a look at Detailed Features of AppSec Phoenix Solution.
Bottom Line
Vulnerability prioritization is an important step once all potential threats have been recognized. We can prioritize vulnerabilities based on their severity levels, exposure time and affected assets but there is a lot more to fix exploitable and most dangerous threats first. That’s exactly why everybody needs a rigid solution to perform all these tasks on automation so that hackers neve get enough time to exploit the actual flaw.
















