At the beginning of the year, we had a flood of DDoS due to HTTP/2 failure, a series of vulnerabilities like CVE-2024-27316, CVE-2024-24549, and others can cause DDoS, in systems like software components like AMPHP, Apache HTTP Server, Apache Tomcat, Apache Traffic Server, Envoy, Golang, Node.js, Nghttp2, and Tempesta FW calling for ASPM and urgent attention for upgrading. This article delves into two significant vulnerabilities—Rapid Reset and the HTTP/2 Continuation Flood—highlighting their impact and the urgent call for mitigation efforts, particularly concerning software components like AMPHP, Apache HTTP Server, Apache Tomcat, Apache Traffic Server, Envoy, Golang, Node.js, Nghttp2, and Tempesta FW.
Understanding the HTTP/2 Protocol
HTTP/2 was designed to enhance web performance and efficiency. However, like any technological advancement, it introduced new vulnerabilities that malicious actors could exploit. The discovery of the ASPM vulnerability, along with others, has brought to light the ongoing vulnerability campaign aimed at exploiting these weaknesses, particularly through DDoS (Distributed Denial of Service) attacks.
The main difference between HTTP/1.1 and HTTP/2 is that the later is a binary protocol and client and server exchange frames instead of text lines. There are many frame types, including some control frames that does not transmit data but rather allow configuration of an HTTP/2 session (like SETTINGS or WINDOW_UPDATE). To make this vulnerability easy to understand I need to present two frames: HEADERS frame and CONTINUATION frame. For those who would like to catch up, the best way to learn it is by reading RFC9204.
The Emergence of Rapid Reset and HTTP/2 Continuation Flood
CONTINUATION frames are very similar to HEADER frames but they have just one flag: END_HEADERS which has the same function: when set the counterparty knows that more headers are coming in the following CONTINUATION frames.
Rapid Reset emerged as a formidable exploit, leveraging the HTTP/2 protocol’s stream cancellation feature to launch significant DDoS attacks. This vulnerability demonstrated the potential for even small botnets to cause substantial disruptions, making it a wake-up call for the cybersecurity community.
However, the HTTP/2 Continuation Flood has since been identified as an even more severe threat. Discovered by security researchers, this vulnerability exploits the protocol’s handling of CONTINUATION frames, leading to server instability, crashes, or memory exhaustion. Its stealthy nature—leaving no trace in HTTP access logs—compounds the challenge of detection and mitigation.
The attack uses an infinite chain of continuation

Reference https://nowotarski.info/http2-continuation-flood-technical-details
Exploitability
Despite not having evidence of exploit at scale, due to the DDoS nature and simplicity of attack is recommended high attention
Also, due to the nature of the embedded device and HTTP service, several 3rd party software will be affected:e.g. arista
- AMPHP (CVE-2024-2653) NO FIX –
- Apache HTTP Server (CVE-2024-27316) – Fixed in Apache HTTP Server 2.4.59
- Apache Tomcat (CVE-2024-24549) – No Fix
- Apache Traffic Server (CVE-2024-31309)
- Envoy (CVE-2024-27919 and CVE-2024-30255) – FIX
- Golang (CVE-2023-45288) – FIX
- Node.js (CVE-2024-27983) – N/A
- Nghttp2 (CVE-2024-28182) – patched version 1.61.0
- Tempesta FW (CVE-2024-2758) – patched version 0.7.1
more of those will come as the vulnerability evolves
Affected Software and the Call for Action
The HTTP/2 Continuation Flood affects a wide range of software, highlighting the vulnerability’s extensive reach. Notably, the following components have been identified as vulnerable, each assigned specific CVE identifiers indicating the need for immediate attention:
- AMPHP (CVE-2024-2653)
- Apache HTTP Server (CVE-2024-27316)
- Apache Tomcat (CVE-2024-24549)
- Apache Traffic Server (CVE-2024-31309)
- Envoy (CVE-2024-27919 and CVE-2024-30255)
- Golang (CVE-2023-45288)
- Node.js (CVE-2024-27983)
- Nghttp2 (CVE-2024-28182)
- Tempesta FW (CVE-2024-2758)
Mitigation and Forward Steps
The disclosure of these vulnerabilities has spurred a coordinated effort among developers, businesses, and cybersecurity professionals to patch affected systems and fortify their defenses against potential attacks. Upgrading to the latest versions of impacted software is crucial to mitigating the threats posed by the HTTP/2 Continuation Flood and other related vulnerabilities.
Moreover, organizations are advised to conduct regular vulnerability assessments and embrace a proactive stance towards cybersecurity. Understanding the intricacies of the HTTP/2 protocol and the nature of these vulnerabilities is essential in developing robust defense mechanisms against evolving cyber threats.
Conclusion
The discovery of vulnerabilities like Rapid Reset and the HTTP/2 Continuation Flood within the HTTP/2 protocol serves as a stark reminder of the dynamic landscape of cybersecurity threats. As technology continues to advance, so too do the opportunities for exploitation. It’s imperative that the cybersecurity community remains vigilant, collaborative, and proactive in its efforts to protect digital infrastructure from such vulnerabilities. By staying informed and prepared, we can navigate the complexities of the digital age with confidence and resilience.
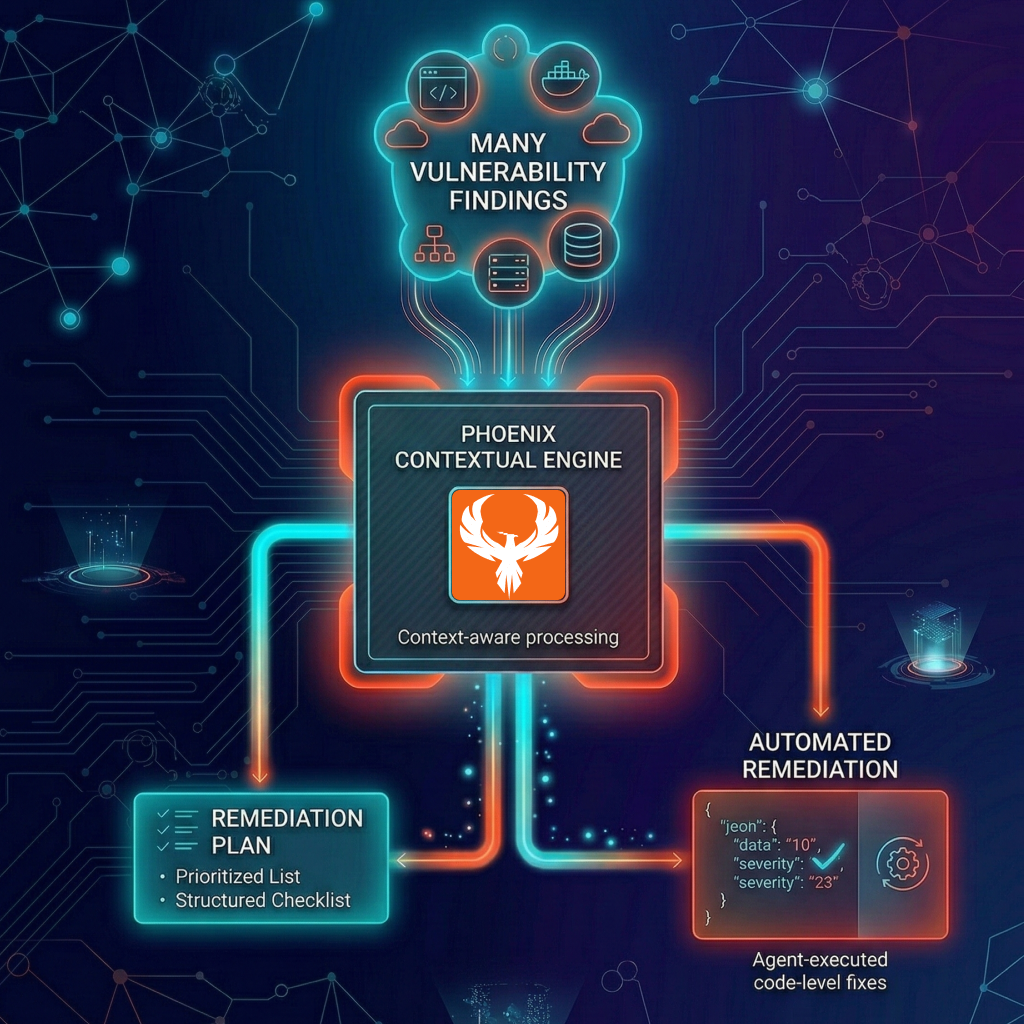
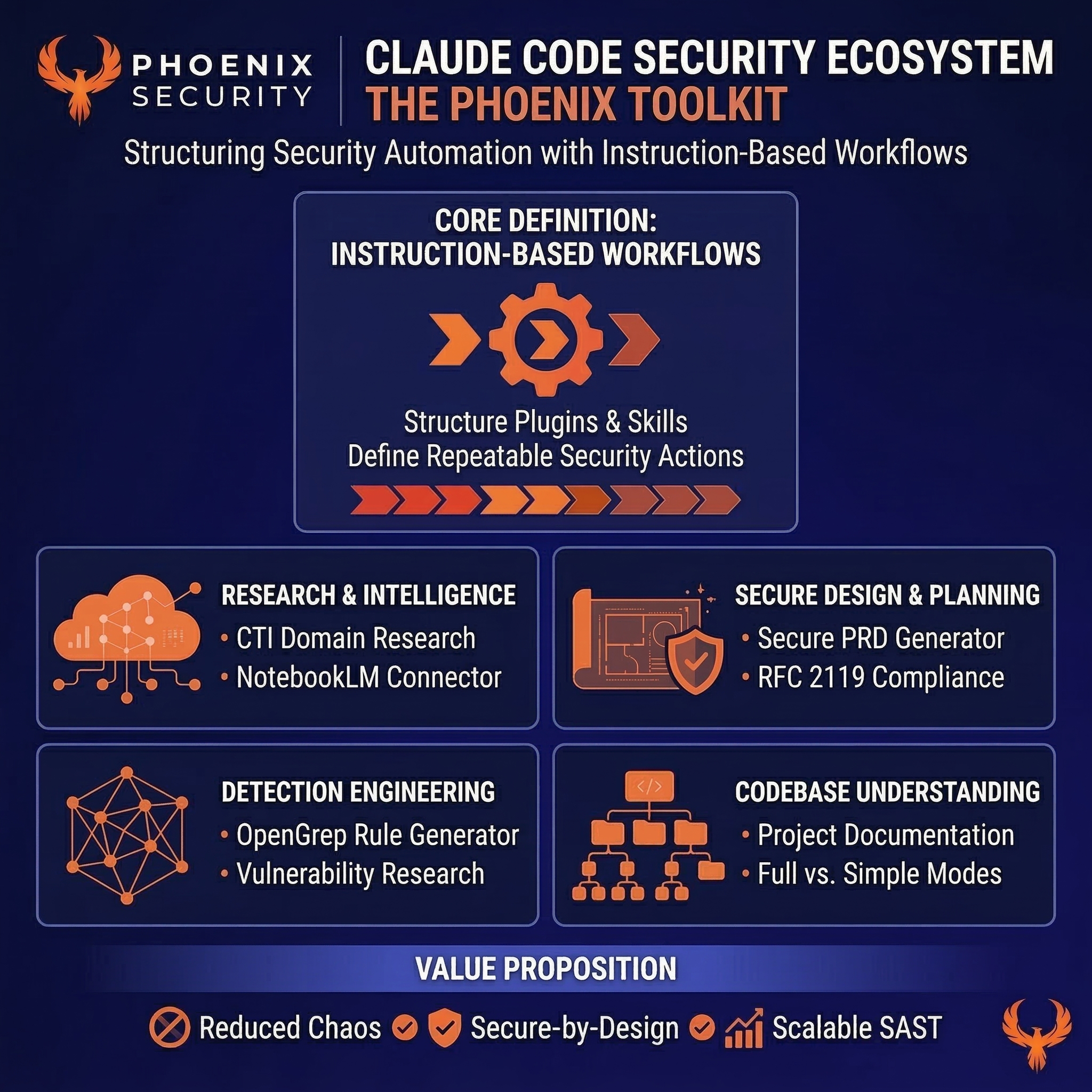
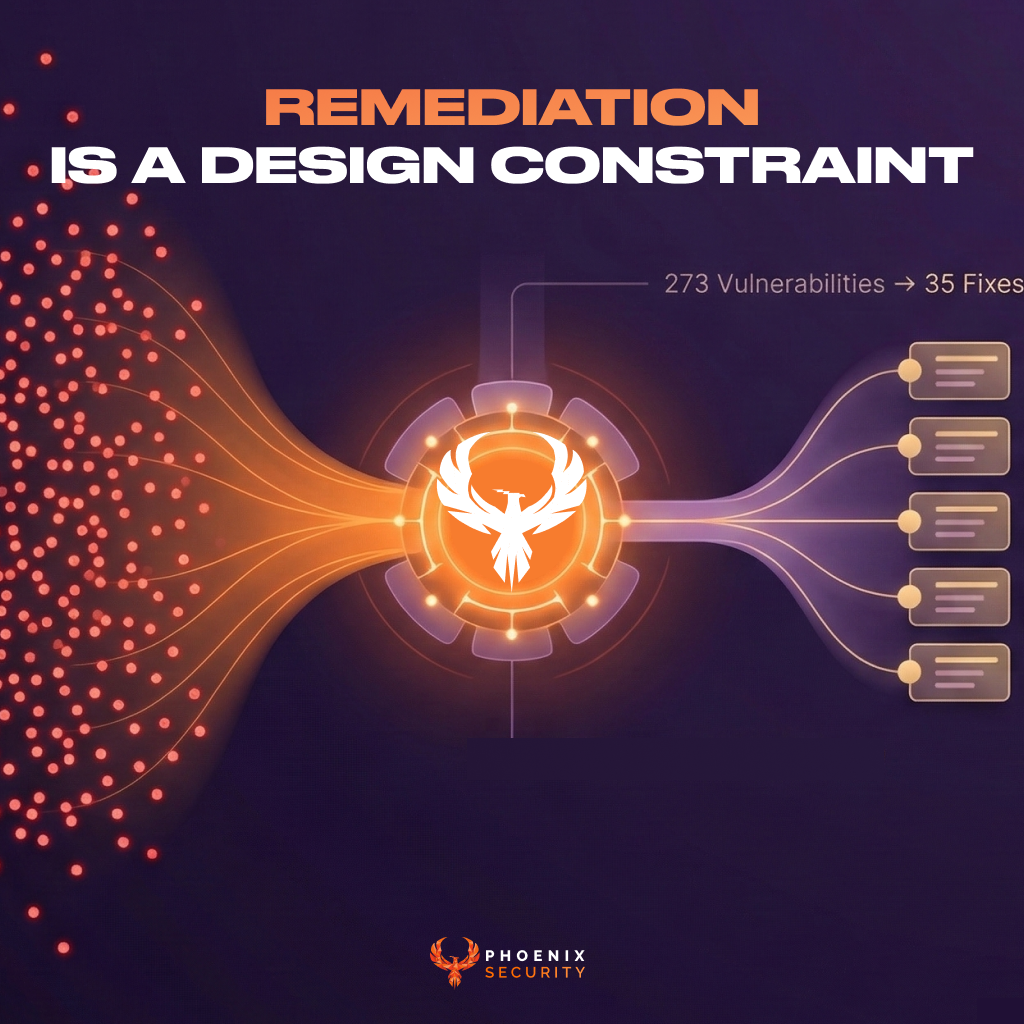
How Phoenix Security Can Help Identify and schedule campaign for HTTP/2 continuation flood

Phoenix Security helps organizations identify and trace which systems have vulnerabilities, understanding the relation between code and the cloud. One of the significant challenges in securing applications is knowing where and where HTTP/2 library is used. ASPM tools can scan the application portfolio to identify instances of vulnerable Linux and which version is exploitable, mapping out where it is deployed across the organization. This information is crucial for targeted security measures and efficient patch management. Phoenix Security’s robust Application Security Posture Management (ASPM) system is adept at not just managing, but preempting the exploitation of vulnerabilities through its automated identification system. This system prioritises critical vulnerabilities, ensuring that teams can first address the most pressing threats and then optimise resource allocation and remediation efforts.
CVE-2024-27316 and campaign Phoenix allow to address CVE-2024-27316 in bulk with others, following an example of the most recent liblzma campaign CVE-2024-3094

The Role of Application Security Posture Management (ASPM):

ASPM plays a vital role in managing and securing applications like those built with HTTP/2. It involves continuous assessment, monitoring, and improvement of the security posture of applications. ASPM tools can:
- Identify and Track Vulnerable Versions/ Components: Locate where HTTP/2 is implemented within the software package.
- Vulnerability Management: Detect known vulnerabilities in HTTP/2 and prioritize them for remediation.
- Configuration Monitoring: Ensure HTTP/2 configurations adhere to best security practices.
- Compliance: Check if the usage of HTTP/2 aligns with relevant cybersecurity regulations and standards.
- Raise Exceptions where specific versions are not affected

By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.