In what could be the biggest DDoS ever registered and in a month already full of advisories like LIBCURL Vulnerability HTTP/2 has been affected by a vulnerability CVE-2023-44487 aka Rapid Reset that could impact basically every web server and has been exploited in the wild. This blog aims to shed light on various aspects of HTTP/2, answering key questions that many have about this web protocol’s vulnerabilities and mitigations. The attackers leveraged this vulnerability to deploy a massive DDoS attack: Amazon mitigated attacks at a rate of 155 million requests per second, Cloudflare at 201 million rps, and Google endured a record-breaking 398 million rps. This vulnerability was under active attack in August.
Contents
ToggleWhat is HTTP/2?
HTTP/2 is the second major version of the HTTP network protocol, used by the World Wide Web. It brings key improvements over HTTP 1.1, such as smaller header sizes and multiplexing—the ability to send multiple requests for data in parallel over a single TCP connection. Unlike HTTP 1.1, which is text-based, HTTP/2 is binary-based, making it more compact and more efficient in terms of parsing.
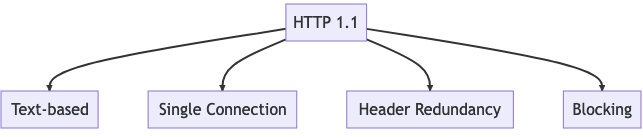
for each element of that page (CSS, images etc) HTTP 2 is a binary protocol that utilises multiplexing, which allows multiple requests and responses to be sent simultaneously over a single connection
Daniel Cuthbert has done a fantastic analysis on HTTP 1 vs 2 and Rapid Reset vulnerability
Bugs happen but it's rare you see a bug that grabs you so hard and makes you nod like a little dog..
— Daniel Cuthbert (@dcuthbert) October 11, 2023
CVE-2023-44487 did that for me
good god what a bug and here's why
Is HTTP/2 Vulnerable?
The short answer is yes. Like any technology, HTTP/2 is not immune to vulnerabilities. A notable example is CVE-2023-44487, a bug that exploits the HTTP/2 protocol’s feature called “streams.” Streams are multiplexed requests and responses with unique identifiers. The vulnerability lies in the RST_STREAM frame, which allows for immediate termination of a stream. Malicious actors have found ways to abuse this feature for DDoS attacks, making it a significant security concern.
Vendor Advisories and Statements for CVE-2023-44487 Rapid Reset
Several vendors have issued advisories and fixes for this vulnerability:
- Apache Tomcat: Fixed in 8.5.94
- AWS: No statement as of yet
- F5: No statement as of yet
- Microsoft IIS: No statement as of yet
- Microsoft MsQuic: Fixed in 2.2.3
- Nginx: Full details in their blog
- nghttp2 library: Fixed in 1.57.0
CISA Advisory CVE-2023-44487 Rapid Reset
The Cybersecurity and Infrastructure Security Agency (CISA) has also advised on this vulnerability. For more details, you can refer to CISA’s advisory on CVE-2023-44487.
Why is HTTP/2 Not Widely Used?
Despite its advantages, HTTP/2 has not seen universal adoption. Several factors contribute to this:
- Compatibility Issues: Older systems and browsers may not support HTTP/2, making it less appealing for websites that cater to a broad audience.
- Lack of Awareness: Many website owners are not fully aware of the benefits that HTTP/2 can bring, leading to slower adoption rates.
- Server Updates: Transitioning to HTTP/2 often requires updates to web servers, which some organizations may find cumbersome or risky.
How to Change from HTTP 1.1 to HTTP 2?
Transitioning from HTTP 1.1 to HTTP/2 is generally straightforward but requires careful planning:
- Server Software: Ensure your web server software supports HTTP/2. Popular web servers like Apache and Nginx have HTTP/2 support.
- SSL/TLS: HTTP/2 requires SSL/TLS for secure connections, so make sure you have an SSL certificate installed.
- Configuration: Update your web server’s configuration files to enable HTTP/2.
- Testing: Before fully transitioning, test the HTTP/2 settings on a staging server to identify any issues.
- Monitoring: After the transition, monitor performance and error logs to ensure everything is running smoothly.
Is HTTP 1.1 Still Being Used?
Yes, HTTP 1.1 is far from obsolete. Many older systems and websites still use HTTP 1.1 due to compatibility reasons, lack of resources, or simply because they don’t require the performance improvements that HTTP/2 offers.
The Scale of the Attack: A New Benchmark in Cyber Threats
On August 25, 2023, the cybersecurity community was put on high alert. Automated DDoS systems began detecting and mitigating unusually large HTTP attacks against numerous targets. While DDoS attacks are not new, the scale of this particular attack was unprecedented. The attack eventually peaked at an astonishing 201 million requests per second, nearly tripling the size of the previous largest attack on record.
The Botnet Factor
What makes this attack even more alarming is the relatively small size of the botnet used to execute it. The attacker generated this massive attack using a botnet of just 20,000 machines. To put this in perspective, botnets today consist of hundreds of thousands or even millions of machines.
The Potential for Widespread Impact
The implications are staggering because the entire web typically sees only between 1–3 billion requests per second. Using this method, it’s conceivable that an attacker could focus an entire web’s worth of requests on a small number of targets, effectively crippling them. This raises serious questions about the preparedness of current cybersecurity measures to handle attacks of this scale.
Mitigation Strategies for CVE-2023-44487 Rapid Reset
One way to mitigate the vulnerabilities in HTTP/2 is to disable it on your web server. Microsoft provides a guide on how to do this using the Registry Editor. However, it’s crucial to exercise caution when using the Registry Editor, as incorrect usage can lead to severe system issues.
Here’s a step-by-step guide based on Microsoft’s recommendations:
- Open Registry Editor: Click Start, click Run, type
Regeditin the Open box, and click OK. - Locate Subkey: Navigate to
HKLM\SYSTEM\CurrentControlSet\Services\HTTP\Parameters. - Edit DWORD Values: Set DWORD type values
EnableHttp2TIsandEnableHttp2Cleartextto 0 to disable HTTP/2 or 1 to enable it. - Restart: Exit the Registry Editor and restart your computer.
For more details, you can refer to Microsoft’s update guide on CVE-2023-44487.
Disabling HTTP/2 in NGINX is not necessary. Simply ensure you have configured:
- keepalive_requests should be kept at the default setting of 1000 requests
- http2_max_concurrent_streams should be kept at the default setting of 128 streams
Testing and Scanning Tools for CVE-2023-44487
For those interested in testing their web servers for HTTP/2 support or vulnerability to CVE-2023-44487, you can use this HTTP/2 scanner Python script. Credit to Daniel Cuthbert
Alternatively, you can use this Python script, please use at your own risk, and review the code before running it
Bugs happen but it's rare you see a bug that grabs you so hard and makes you nod like a little dog..
— Daniel Cuthbert (@dcuthbert) October 11, 2023
CVE-2023-44487 did that for me
good god what a bug and here's why
How Phoenix Security Can Help Identify HTTP/2 Vulnerability CVE-2023-44487 in Your Products
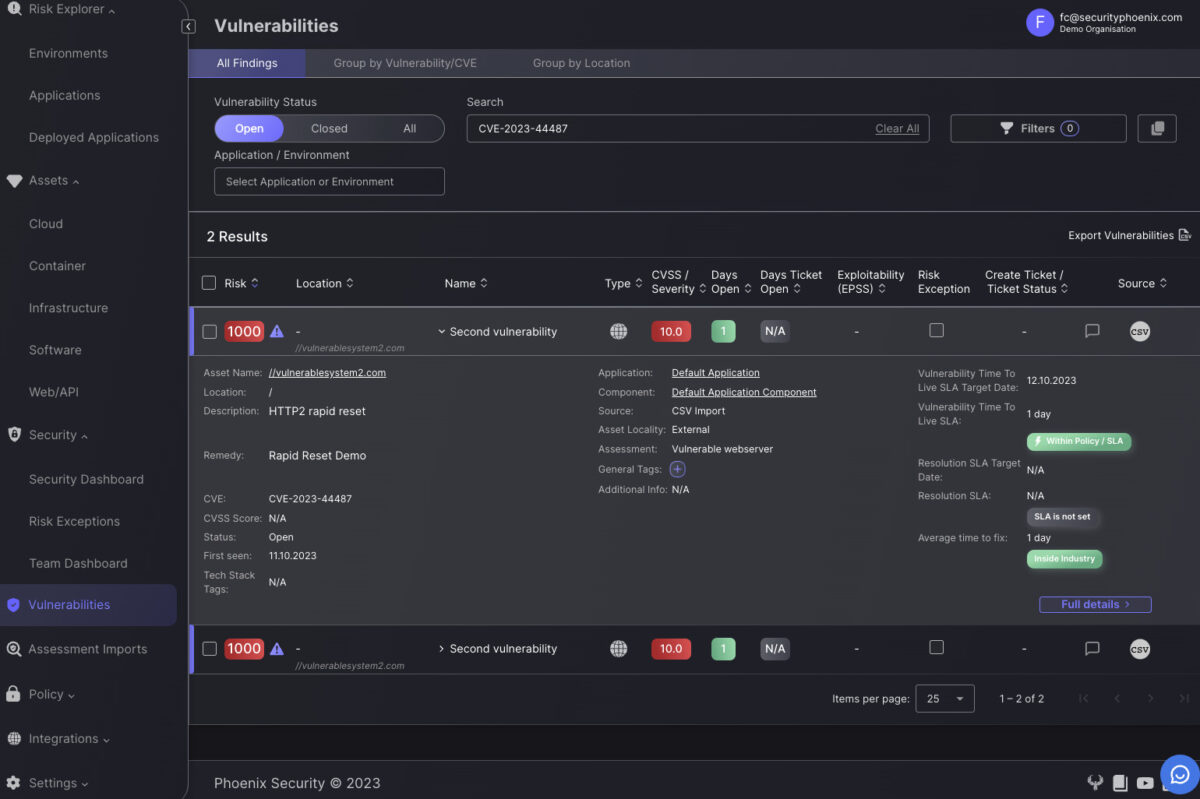
Phoenix Security serves as a beacon for security professionals aiming to pinpoint the vulnerabilities at scale, while CVE-2023-44487 is fairly new you should be able to identify the vulnerabilities in the vulnerability screen and asset screen vulnerability within their systems.
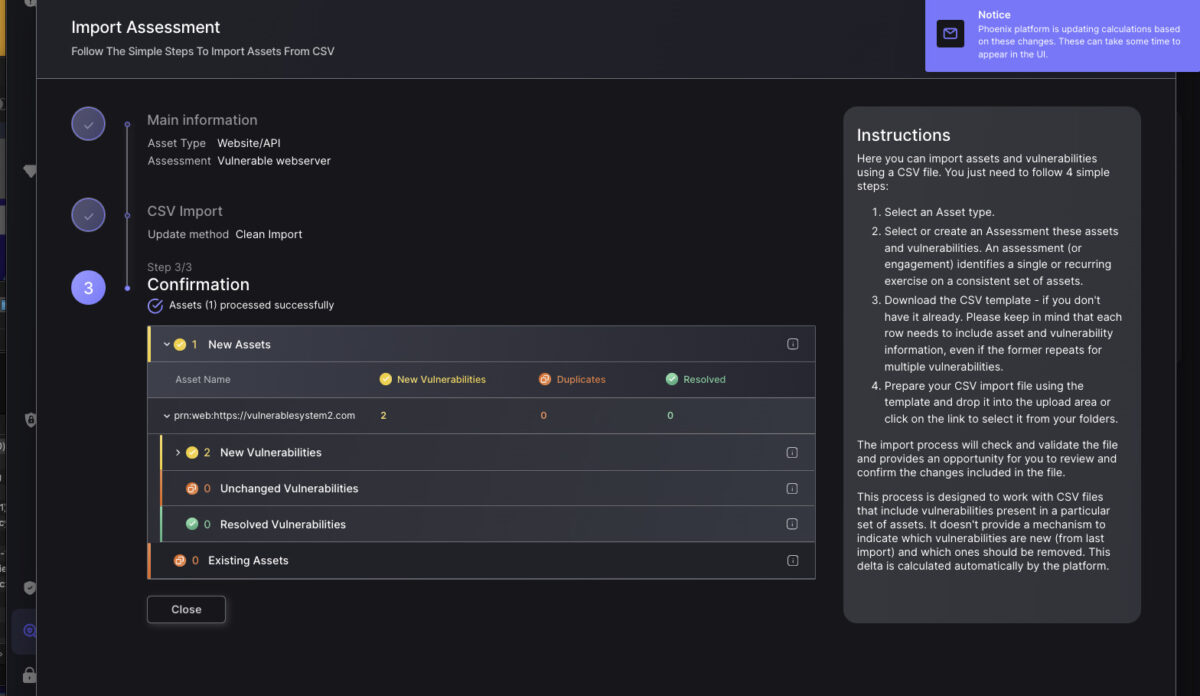
You can also scan with the above scripts and import the results into phoenix to have an asset inventory