The Common Weakness Enumeration (CWE), a community-developed list of software and hardware weakness types, has released its annual “Top 25 Most Dangerous Software Weaknesses” for 2024 for application security and vulnerability management teams; we discover in this blog the patterns and the main categories of the new CWE top 25.
Note this page makes use of embedded diagrams. If you can’t see the interactive diagrams, please disable frames blocking.
We will cover in detail a comparison of the CWE top 25 across the years and across datasets. One of the new objectives is to simplify the classification in macro categories (e.g. Memory corruption and Auth bypass). We will mix AI mapping technique, vector description, and already existing analysis (CWE 1400 and CWE 1000 views)

- Check our analysis of the Top 25 Most Dangerous Software Weaknesses” for 2023 article from last year
- Check our analysis of CISA KEV and patterns of attacks in CISA KEV
- Check out our data explorers to dig into more vulnerability data
Contents
ToggleWhy CWE is important in Application Security and Vulnerability management and how ASPM can help
In application security, defenders face the ongoing challenge of identifying more dangerous patterns. The Common Weakness Enumeration (CWE) provides a structured way to catalog these weaknesses, culminating each year in the CWE Top 25—a snapshot of the most frequently occurring and highly severe vulnerabilities. Yet real-world exploit data (e.g., CISA KEV, VulnCheck, Ransomware usage) can diverge from the overall CWE list, leaving security and vulnerability management teams struggling to prioritize effectively.
Below, we explore the 2024 Top 25, where it aligns with external datasets, and how modern techniques—like AI mapping and ASPM (Application Security Posture Management)—bridge the gap to classify more vulnerabilities accurately.
Get an Assessment of the common root cause and patterns in your vulnerabilities
Why CWE and the Top 25 Matter
1. What are CWEs?
• CWEs are categories of software (and sometimes hardware) weaknesses. They go beyond symptoms (e.g., “RCE” or “DoS”) and drill into the root cause—like OS Command Injection (78) or Improper Privilege Management (269).
2. What is the CWE Top 25?
• Each year, the MITRE Team aggregates thousands of CVE records, scoring them by frequency (how many times a weakness appears) and severity (average CVSS score). The highest “danger scores” earn a spot in the Top 25.
3. Why is it sometimes misleading?
• Different attackers have different goals. For instance, Ransomware operators love Path Traversal (22) or privilege escalation flaws (269) to spread faster and encrypt critical data, while typical bug bounty data is riddled with XSS (79). So your prioritisation might differ depending on your environment or threat model.
2. AI-Driven Mapping and Closing the “Unclassified” Gap
Historically, many CVEs were left at broad, high-level CWEs (like CWE-200: Information Exposure) or simply “NVD-CWE-Other.” By tapping AI-driven keyword extraction and classification, the CWE project re-examined CVE descriptions for more precise matches (Base or Variant CWEs). This year, that approach reduced the number of “unclassified” vulnerabilities by an estimated 48%—a substantial improvement that helps focus application security teams on the actual root cause.
3. Biggest Movers in CWE Top 25 for 2024
Upward Trends:
•400 (Uncontrolled Resource Consumption) soared 13 places; resource exhaustion attacks have become more prominent, including DoS scenarios.
•200 (Exposure of Sensitive Information) also jumped 13 ranks, highlighting persistent data-leak issues.
• 269 (Improper Privilege Management) leapt by 7, consistent with deeper access-control misconfigurations discovered this year.
Downward Trends:
•20 (Improper Input Validation) slipped 6, partly because chain analysis was underused, leading those flaws to be mapped more specifically (e.g., directly to SQL Injection or XSS).
•190 (Integer Overflow) also dropped 9, overshadowed by more impactful memory-corruption entries like Out-of-Bounds Write (787).
4. Top Vulnerability Categories—and Where They Diverge
1. Access Control
• The largest chunk of the 2024 list covers access control issues: Improper Authentication (CWE-287), Missing Authorization (CWE-862), and Incorrect Authorization (CWE-863). These weaknesses top certain bug bounty lists but may rank differently in ransomware contexts.
2. Memory Safety
• Nation-state attackers and advanced groups frequently exploit memory-corruption CWEs (CWE-119, CWE-787, CWE-125, etc.). CISA KEV references highlight these as actively exploited. Yet bug bounty data rarely sees them at the top—researchers typically focus on web-facing vulnerabilities.
3. Injection
• Includes SQL Injection (CWE-89), OS Command Injection (CWE-78), and Code Injection (CWE-94). In bug bounties, injection flaws remain top earners (especially XSS, CWE-79). Meanwhile, ransomware operators lean more towards direct file or auth bypass vectors, occasionally leveraging OS Command Injection for quick RCE.
4. Resource & Lifecycle Management
• Refers to issues like Unrestricted File Upload (CWE-434) or Uncontrolled Resource Consumption (CWE-400). Ransomware groups find some success here, too—especially when file uploads allow them to drop malicious binaries.
Divergence Example:
• CWE-22 (Path Traversal) ranks #5 overall in the Top 25, but it’s #1 among ransomware actors because it helps them locate and encrypt valuable files. Conversely, CWE-79 (XSS) is #1 in the overall list but doesn’t crack the top 10 for ransomware usage.
5. Leveraging ASPM for Unified Vulnerability Management
Application Security Posture Management (ASPM) ties all these insights together in a single pane of glass. It looks at your entire environment—source code, CI/CD pipelines, production apps—and correlates data from:
• CISA KEV for in-the-wild exploited vulnerabilities.
• VulnCheck for publicly available proof-of-concept (PoC) exploits.
• Bug Bounty reports and internal scanners.
By tracking categories (e.g., Access Control, Memory Safety) and CWEs simultaneously, ASPM clarifies your highest-risk flaws. For instance, if an Insecure Deserialization (CWE-502) ranks mid-table in the Top 25 but also appears in CISA KEV or is known to be popular with ransomware operators, ASPM can prioritise those issues higher.
Key ASPM Benefits for CWE top 25 and OWASP top 25:
1. Automated Classification: AI-powered correlation ensures fewer “NVD-CWE-Other” placeholders.
2. Threat Context: Identifies whether a given CWE is highly exploited (e.g., from real KEV data).
3. Actionable Remediation: Integrates with your DevOps or ticketing systems to fix vulnerabilities faster.
Conclusion: Combining CWE Top 25 with Real-World Intelligence
• Comparative Data: Cross-referencing the 2024 CWE Top 25 against CISA KEV, VulnCheck, and ransomware usage reveals meaningful divergences—particularly around memory safety vs. web injection or path traversal vs. XSS.
• AI-Assisted Mapping: Thanks to improved classification methods, the list is more precise than ever—reducing “noise” and clarifying truly relevant root causes.
• ASPM Integration: By pairing the CWE framework with unified vulnerability management tools, you gain a complete picture of exploit potential, business impact, and actual attacker behavior.
Ultimately, the CWE Top 25 is no silver bullet—it’s a foundation. When layered with intelligence feeds and next-gen ASPM, it helps security teams shrink the “unclassified” gap and confidently tackle the vulnerabilities that matter most to their specific threat landscape—be it ransomware, nation-state exploits, or everyday bug bounty findings.
Pro Tip: Focus on the categories—Access Control still dominates the list, while Memory Safety leads advanced exploitation. Then overlay your environment’s data (e.g., is OS code a prime target? Are you mostly web-based?) to shape your 2024 security roadmap.
How can Phoenix Security Help
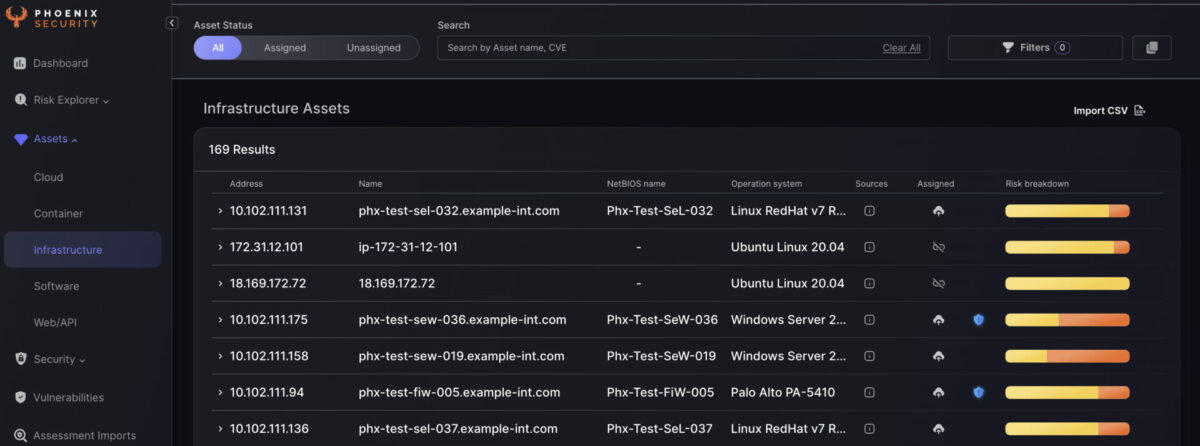
Phoenix traces CVE and CWE dynamically, offering you an overview of the top CWE in your organization.

Phoenix also trace the top CVE and CWE that teams introduce
Phoenix security cutting-edge contextual risk-based algorithms enable organizations to prioritize application security vulnerabilities based on context and probability of exploitation and present a unified impact analysis.
The cutting-edge vulnerability selection engine enables organizations to set risk-based targets that translate into specific actions for engineers.
Get in control of your Application Security posture and Vulnerability management
Moreover, Phoenix Security’s correlation capabilities can help organizations link the activities in the code with the context in the shift-right part, ensuring that issues are identified and addressed proactively. Using Phoenix Security’s scorecard, organizations can create a common language between the security, development, and business teams, ensuring everyone is aligned and focused on achieving the same goals.
Finally, Phoenix Security’s ability to create risk-based profiles can help organizations translate their security goals into dynamic and smart targets for engineers. By using risk-based profiles, engineers can prioritize their work and focus on the most critical issues, ensuring they effectively use their time and resources.
Overall, by leveraging Phoenix Security’s powerful capabilities, organizations can implement a smart, risk-based approach to software development that ensures the success of their initiatives while minimizing risk and improving overall efficiency. With Phoenix Security as their partner, organizations can feel confident they are taking a proactive approach to software development aligned with their business objectives and goals.








![Phoenix Security infographic: Claude Code Critical Vulnerability — CI/CD Nightmare, 3 Command Injection Flaws. Dark navy and orange background with circuit-board pattern. Center: terminal window showing attack chain [config] | [shell] | [exfil] with three red arrows pointing to attack targets — CI/CD Pipeline Compromise (top right), Cloud Key Exfiltration via AWS (middle right), and Developer Workstation Compromise leading to Server-to-Server lateral movement (bottom right). Phoenix Security logo at top. Bottom text: "CLAUDE CODE / CRITICAL VULNERABILITY / CI/CD NIGHTMARE / 3 COMMAND INJECTION FLAWS / Credential Exfiltration · CWE-78 · Confirmed / Shell Injection in CLI, Editor, and Auth Helpers."](https://phoenix.security/media/Gemini_Generated_Image_abcn46abcn46abcn.jpeg)








