Contents
ToggleVulnerabilities and the problem of scale for cloud and application security
Vulnerability management is identifying, evaluating, treating, and reporting on security vulnerabilities in systems and the software that runs on them.
This process, together with the vulnerability assessment, forms the lifecycle of vulnerability.
Security vulnerabilities refer to a technological weakness of a system, software, infrastructure, cloud taht a threat actor. could exploit
Why is vulnerability management becoming so vital today?
Vulnerability management is becoming ever so vital due to the increased complexity of the technology stack and more alerts from various vulnerability assessment tools.
The usual step at the lower maturity level of a vulnerability assessment and analysis is to assess all the vulnerabilities individually. With an average vulnerability assessment report containing 2000 individual vulnerabilities, this effort becomes quickly overwhelming.
Security professionals triage vulnerabilities daily and face the challenge of too many alerts coming from all parts of the organization and technology stacks.
According to the Verizon Data Breach investigation report, Vulnerabilities mismanagement is one of the four factors that leads to vulnerabilities.
According to research from the Ponemon Institute, 53% of companies spend more time navigating manual processes than actually responding to vulnerabilities.
Due to recent changes in vulnerability declaration, and related time to fix vulnerabilities under CISA BOD 22-01, time to fix vulnerabilities is becoming shorter and more critical.
With the current trend of 35% more CVE declared yearly and security teams being unable to cope with the stress and quitting, 54% of security professionals are considering a career change, it is ever more important to focus on the vulnerabilities that matter most.
Steps of the vulnerability lifecycle
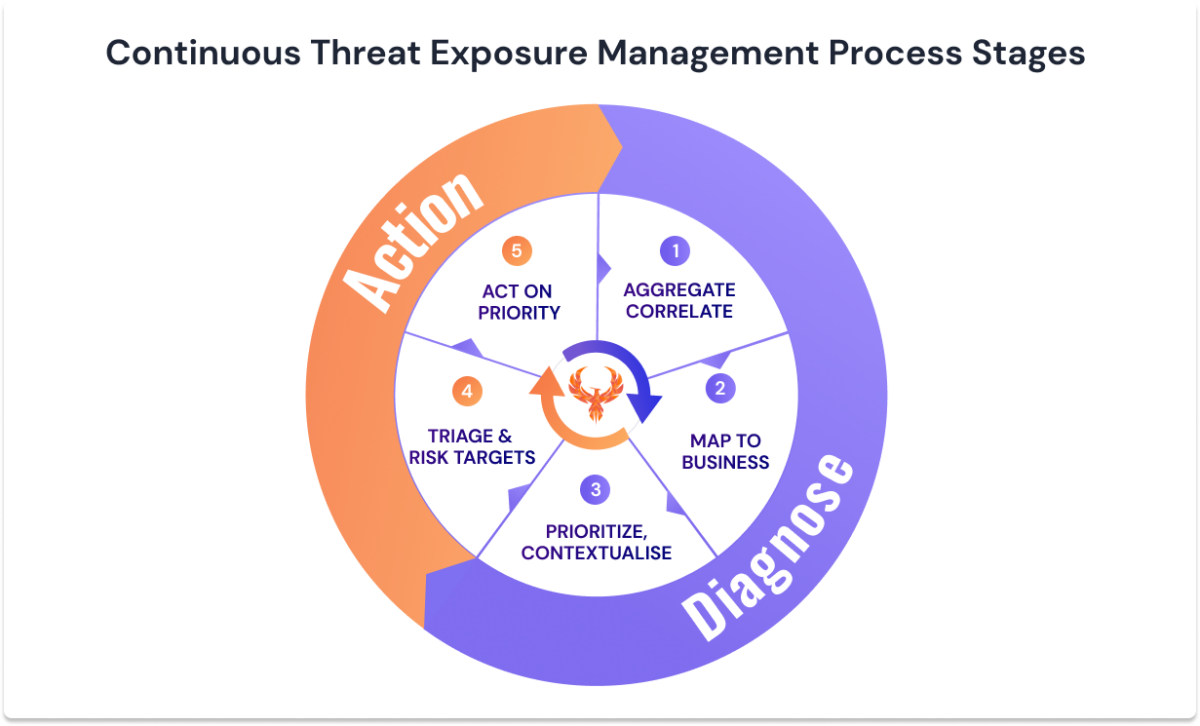
According to a recent Gartner research on vulnerability management is now evolving in Continous Threat and Exposure Management (CTEM) and becoming a new de facto standard for the vulnerability lifecycle.
The steps of the process start with
1 – Scoping, Aggregate and consolidate –
- Scope the part of the organization that will be subject to the vulnerability management process, Caveat, a lot of organizations start this process too wide and get frustrated quickly. Start small, iterate, and expand
- Aggregate & Correlate the vulnerability – this part of the process will be iterative and enable cleaning up, deduplicate and prioritising based on the relationship between assets
2 – Map to business – Correlate business application and environment (cloud, endpoint, containers …) to different parts of the business. This enables the traceability of who owns what and who is responsible for fixing the vulnerabilities.
3 – Prioritization – Correlation, Contextualization and risk assessment of the vulnerabilities evaluating the impact and likelihood of exploitability
4 – Triage and Risk assessment – Assessment of the vulnerabilities in their context to determine which one is a true positive or a false positive. This process also includes risk acceptance/assessment and vulnerability exceptions. At this stage, you can start setting a risk tolerance level, and how risky / non-risky you want to be
5 – ACT – this stage is the execution phase. Plan with teams on what to fix and when, and identify the vulnerabilities that are more at risk (from the prioritization)
As the CTEM or CEM process depends much on collaboration, the remediation is a collaborative effort between the team assessing and implementing the vulnerability, the rest of the business
What are the areas in scope for vulnerability management
During vulnerability assessment, the areas that can benefit from vulnerability management are:
Software supply chain security
- SAST – Static Code Analysis
- DAST – Dynamic code analysis assessing
- SCA – vulnerability assessment of libraries
- CI/CD Security – vulnerability assessment of pipelines used to build software
- SBOM – list of artefacts in a software (with possible vulnerabilities attached to it)
- Purchased/Built Software – Software being purchased and used as is (usually subject to patches)
Environmental Security
- Cloud Security – vulnerability assessment of cloud environments ( like AWS, Azure, GCP), their misconfiguration and vulnerabilities
- Network Security
- Infrastructure Security / Endpoint Security – vulnerability assessment of servers and endpoints
Vulnerability Maturity Model Levels
The levels of maturity measure from very immature (L0) to highly mature (L5). The methodologies considered vary from an absent process (L0) to a more data-driven measured, and controlled process (L5).
We look at several maturity models from NIST to NCSC guidance and SANS. Despite being good guidance, they are disjointed and look at the problem, not from a risk perspective.
In an effort to improve vulnerability management maturity calculation and move towards a more risk-based approach, we created a model that encompasses application security, patching, vulnerability management, and cloud security.
Every organisation should go through different maturity levels and SLA/SLO exercises. The following is a good indication of maturity level.
Maturity 0 (mapped to SANS VMM Level 1) – Non Existent No Asset Register No Scanning Capabilities No Vulnerability Management Process No-Risk assessment of vulnerabilitiesOccasional pentest or manual assessment No scanning capabilities Measurement:No measurement or basic pentest results/fixed Maturity 1 (mapped to SANS VMM Level 1) – Scanning – Some scanning capabilities (early stage)No Asset RegisterOne or two scanners (infrastructure, code) Some Pentesting activity (internal/external)No Vulnerability management processJust Fix vulnerabilities when there is time.Vulnerabilities are fixed when and if discoveredMeasurement:Number of vulnerabilities fixed by severity from the output of each scanner |
When organisations are at maturity 1-2, the best and most efficient way is to start with a smaller team, scan and document assets, and demonstrate good control on those projects.
After this it is easier to replicate the model at scale with a systematic approach while teams get gradually more mature.
Maturity 2 (mapped to SANS VMM Level 2)Scanning Code, Assessing software with DAST or some dynamic application testing capabilitiesExternal attack surface tested Critical assets pentested regularlyManual triage or some Basic SLA (for a whitepaper on SLA see here) Vulnerabilities fixed when and if discoveredNo asset management or some basic levelSome non formalised vulnerability management processNo risk acceptance or assessment processMeasurement:Number of vulnerabilities fixed by severity from the output of each scanner Maturity 3 (mapped to SANS VMM Level 3) Start Using SLA for the whole (for a whitepaper on SLA see here) Policy & mandate when SLA fix Some basic level of the vulnerability management process, Some basic level of asset managementNo major measurement of vulnerabilities Not a consistent measurement of resolutionMeasurement:Number of vulnerabilities fixed by severity from the output of each scannerSLA Based vulnerability resolution time: Critical, High Medium low resolved at different time |
Maturity 4 (mapped to SANS VMM Level 4)Start Using SLA for the whole organisation. Consistent use of Severity Based SLAMove to Exposure Based SLA or Risk based SLAConsistent Pipeline approach for vulnerabilities scanning Scheduled/Regular Pentest, assessmentVulnerabilities fixed when and if discovered No asset managementMasurements SLA Based vulnerability resolution time: Critical, High Medium low resolved at different timeRisk based resolution times Team Security OKr (or beginning of)Risk based vulnerability measurement and resolution | |
Maturity 5 (mapped to SANS VMM Level 4)Creating Customised SLA/ SLO for different teams/complexity. Implementing SLA Levels based on Type of asset and risk Consistent use of Severity Based SLAMove to Exposure Based SLA or Risk based SLAEmbedded in Feedback LoopsCreating feedback loops to Customise SLA / SLO for systems in different categories. Confidently breaking pipeline Using team’s OKR to: Burning down regularly the Backlog of vulnerabilitiesSlack and ticketing system used actively to deliver vulnerabilities resolution to teamsMeasuring team performance & feeding it to higher managementProduct owner report on vulnerability resolution and riskRisk-based approach to vulnerability burndownScheduled/Regular Pentest, assessmentVulnerabilities fixed when and if discoveredAutomatic asset management driven by either the vulnerability scanners, CI/CD, cloud services Measurements:Measured Vulnerability management processStart measuring and feedback the Mean Time To Resolution (MTTR) and Mean Time Open (MTO). Measuring Vulnerability timelinesTeam Security OKr: Self imposed and agreed objectives with Security teamsRisk based vulnerability measurement and resolution |
For a more comprehensive view of Maturity Models in DevSecOps refer to the modern application security and DevSecOps Book
For a more comprehensive list of Maturity in vulnerability management, refer to the SANS Maturity Model
How can Phoenix Security Platform help?

Technology is not the holy grail or answer to all the problems. Vulnerability management remains a people & culture, process, and technology problem.
Phoenix security cloud platform can help automate, correlate and track maturity at scale and facilitate the enforcement of measurements.
Phoenix offers a way to scale triaging and prioritising vulnerabilities, removing the manual part of security analysis and enabling the security team to scale better, from a 1:10 to 1:40 ratio, react faster (from 290 days average resolution time to 30) and be more efficient in the time spent on each vulnerability.
With a proven methodology adopted by more than 1000 Security professionals, Phoenix enables security engineers to communicate more effectively with the business in terms of risk and loss as well as automatically prioritise vulnerabilities for developers