As the guys at LunaSec have already mentioned (https://www.lunasec.io/docs/blog/spring-rce-vulnerabilities/ ), there’s been a bit of confusion around “Spring4Shell” and similar vulnerabilities that have been reported almost at the same time.
On March 29th, 2022, two RCE vulnerabilities were being discussed on the internet. Most of the people talking about them believe they’re talking about “Spring4Shell” (CVE Added: CVE-2022-22965), but in reality they’re swapping notes about CVE-2022-22963.
LunaSec
We’d like to focus on this specific aspect in this post to keep things simple and clear.
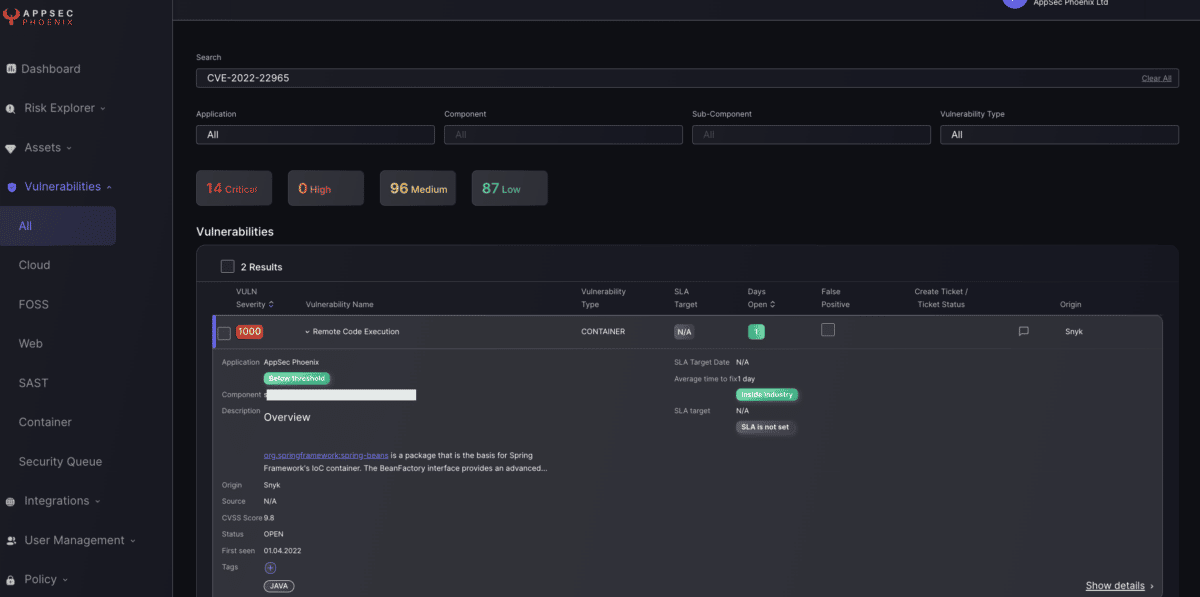
- Spring4Shell (CVE-2022-22965) is a Very Severe RCE vulnerability affecting Spring Core and its derivatives.
- CVE-2022-22963 (no known name) is a less severe vulnerability that affects Spring Cloud Function.
To make matters a bit more confusing, there seems to have been reports of a third vulnerability affecting Spring’s deserialisation logic, but this turned out not to be exploitable.
So we have two vulnerabilities affecting related, but distinct, Spring libraries and both represent a serious weakness for any system using the affected versions under the required conditions.
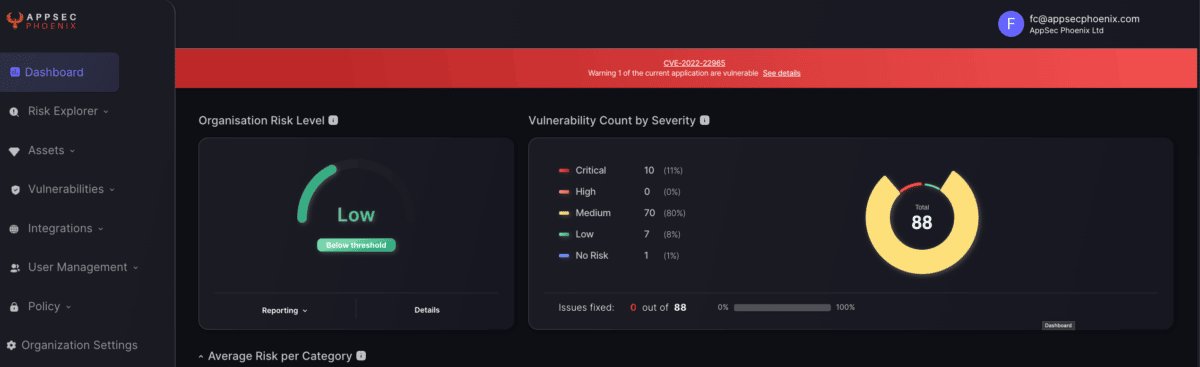
The threat intel team at AppSec Phoenix has triggered the corresponding alerts in our platform so that anybody with applications potentially affected by the vulnerability gets the corresponding notifications.