No matter the size or nature of your business, having a comprehensive security risk management strategy in place is essential. Without one, your business is vulnerable to various threats, from cyber-attacks to physical security breaches.
However, knowing how to create an application security strategy that works for your organization can be a challenging process. This article will cover the steps necessary to create a risk mitigation strategy tailored to your organization’s needs.
We will also discuss the importance of training, testing, and monitoring the procedure to ensure its effectiveness.
Purpose of Creating a Security Risk Management Strategy
The purpose of creating a security plan is to identify, analyze and mitigate security risks and reduce the potential for a data breach. This system will also provide the organization with a framework to evaluate security risks and develop a plan of action to reduce those risks.
Additionally, a comprehensive strategy will allow the organization to be proactive in its cloud security vulnerability management approach by regularly assessing, monitoring, and revisiting any security threats or vulnerabilities.
Steps for Creating a Comprehensive Security Risk Management Strategy
1. Identify risks: The first step in creating a security threat management strategy is identifying potential risks to the system or organization. This includes understanding the threats, vulnerabilities, and associated risks to the system or organization.
2. Assess risks: Once they have been identified, the next step is assessing them. This involves evaluating the likelihood that the risk will occur and the potential impact on the system or organization if it does.
3. Develop risk response strategies: Once risks have been identified and assessed, strategies must be developed. It is essential to either reduce, accept, or transfer the risk. This often involves implementing security controls to reduce the likelihood of a risk occurring or transferring the risk to a third-party vendor.
4. Monitor risks: After strategies have been developed, it is crucial to monitor the risks on an ongoing basis. This can involve regularly reviewing security logs and other reports to identify any new or changed risks.
5. Re-evaluate risks: It is vital to re-evaluate the risks regularly to ensure that the implemented strategies are still effective. This may involve updating or replacing existing security controls or strategies as needed.
Advantages of Having a Security Risk Management Strategy
Here are a few significant advantages of a robust security system:
- One of the main advantages of having a comprehensive security risk management strategy is enhanced security. With a system in place, organizations can more readily identify and address security threats and vulnerabilities and develop a plan to mitigate them. This improved security posture will allow the organization to protect its data and networks from potential threats or attacks.
- By constantly assessing and monitoring potential security threats and vulnerabilities, organizations can be more confident that their data and networks are secure. This will also allow organizations to respond more quickly and effectively to any security threats that may arise.
- Having a comprehensive security arrangement can help to improve risk awareness. By regularly assessing and revisiting security risks, organizations can be better informed on the types of threats they face, as well as the measures they can take to mitigate them. This improved awareness of security risks can help to ensure that the organization’s security posture remains strong.
Challenges of Implementing a Security Risk Management Strategy
While there are many advantages to having a comprehensive security structure, there are also some challenges that must be addressed in order to implement the system successfully.
- One of the main challenges is the cost of implementation. Developing and maintaining a comprehensive system can be costly and time-consuming, and organizations must ensure that they have the resources and budget necessary to implement the system successfully.
- Another challenge is the difficulty of establishing processes. Developing and implementing a system requires the organization to establish processes and procedures for identifying and assessing security threats and vulnerabilities and develop and implement a security risk management plan. This can be a difficult and time-consuming process, and organizations must ensure that they have the necessary resources and expertise to develop and implement the system successfully.
- Finally, implementing a strategy also requires a significant amount of time. Organizations must devote the necessary time and resources to developing, implementing, and monitoring the system to ensure its effectiveness.
How can AppSec Phoenix Help?

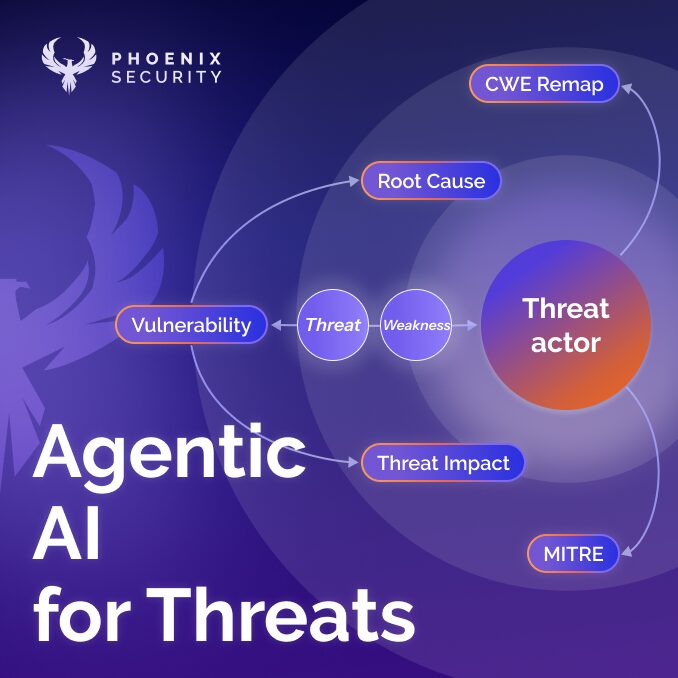
Phoenix Security is a software company that specializes in helping companies prioritize and manage their cybersecurity threats and exposure. We offer a comprehensive software solution that gives organisations a single view of the risk, visibility, and quantification of their cybersecurity exposure. the Phoenix Security Platform can help businesses quickly identify and prioritize threats, contextualize vulnerabilities and deliver prioritized tasks to engineers with just one risk strategy click. Get your risk strategy implemented with one click
With Phoenix Security, you can focus on what matters most and make contextual-based decisions based on the probability of exploitation and exposure to attacks. At Phoenix, we believe in walking the path with our customers and providing them with frameworks, tools and strategies to take vulnerability management into Cyber Exposure management. These strategies defend against cyber threats, and better understand the financial implications of their cybersecurity investments.
Conclusion
A comprehensive security strategy can be a powerful tool for organizations to protect their data and networks from cyber threats. By regularly assessing and monitoring security threats and vulnerabilities, organizations can be better prepared to mitigate those risks and reduce the potential for a data breach.
Additionally, having a comprehensive system in place can help organizations to be proactive in their approach to security plan and ensure that their security posture remains strong. Despite the challenges that may arise when implementing such a system, the long-term benefits of having a comprehensive security risk management system far outweigh the costs. See how Phoenix security can help