According to CVEDetails, over 13% of exposed vulnerabilities possess a critical score which simply means that these exploitable vulnerabilities can do the most damage to the assets of a company.
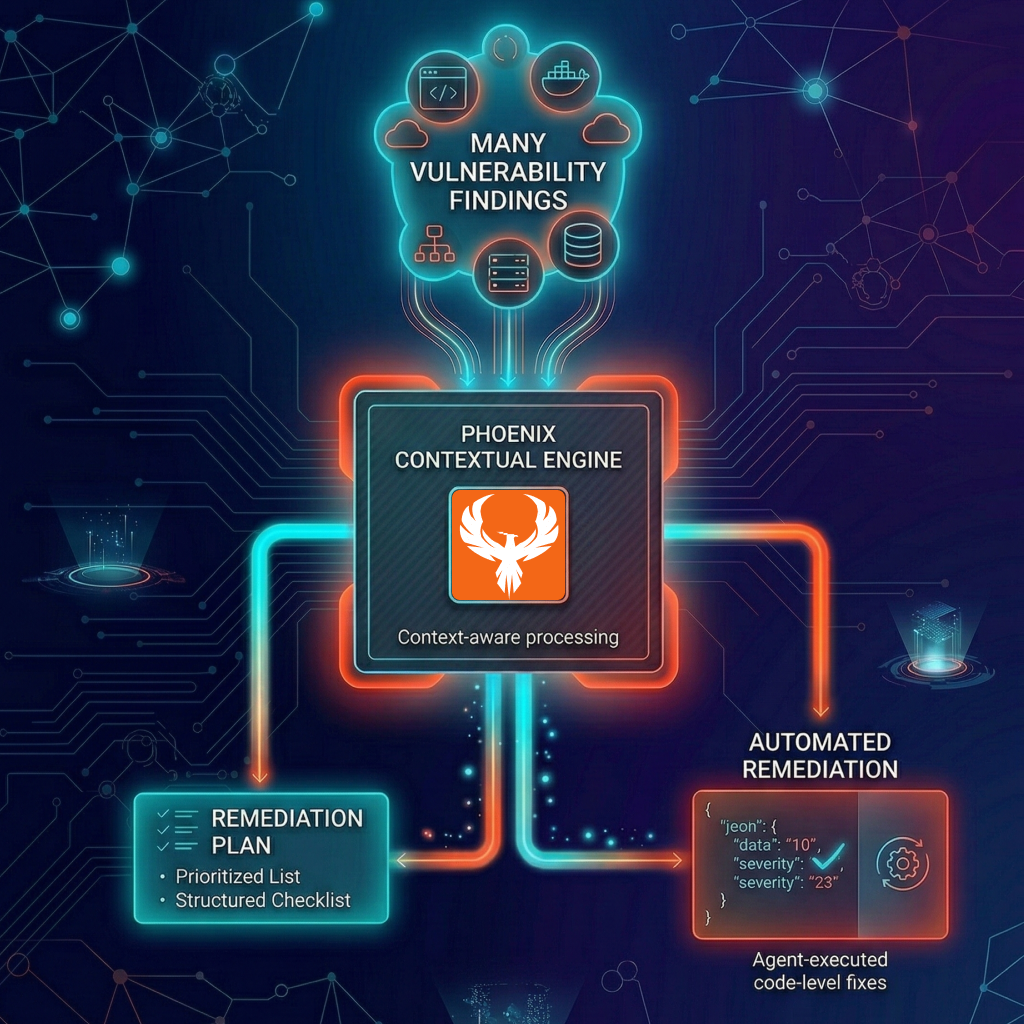
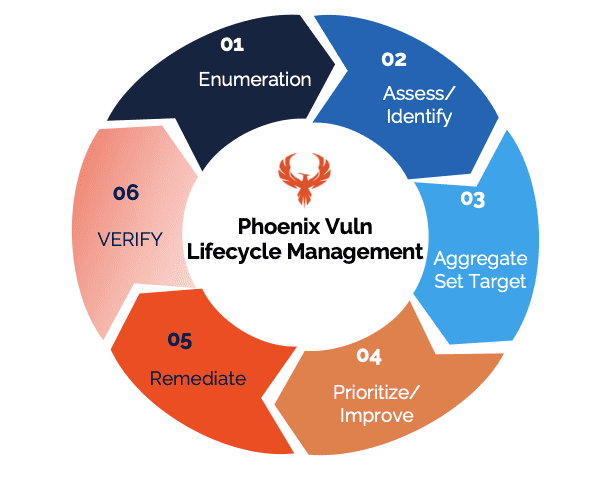
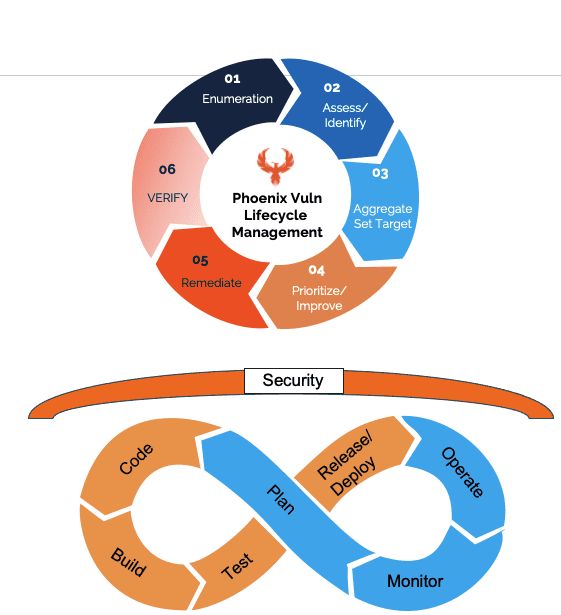
Companies often make mistakes while managing vulnerabilities according to their risk level. Vulnerability scanners may show thousands of vulnerabilities in a company’s infrastructure, but it is unrealistic to solve each of them. Typically, the vulnerability management process is divided into four sections, as described in the figure.
However, some flaws and loopholes are more urgent and important to fix than others. That’s why most security experts always first prioritize the most critical vulnerabilities before they apply any fixes. Still, there is a lot more to vulnerability management, and we will go through it step-by-step.
Vulnerability Management: Step-by-Step
We can take the vulnerability management and prioritization process step-by-step to simply form a rigid strategy that is capable of securing our system from unwanted attacks. Here are a few steps to follow.
- IT & Asset Inventory Information
It’s important to perform a detailed analysis of the company’s assets to see which parts can be most affected and which parts will stay the least affected if certain vulnerabilities are exploited. Also, security analysts should know where the company’s data is being stored because these sections are generally most sensitive to attacks and data breaches.
Once security pentesters are aware of all the ins and outs including IT assets such as hardware, operating systems, then they can move towards the next step.
- Vulnerability Severity
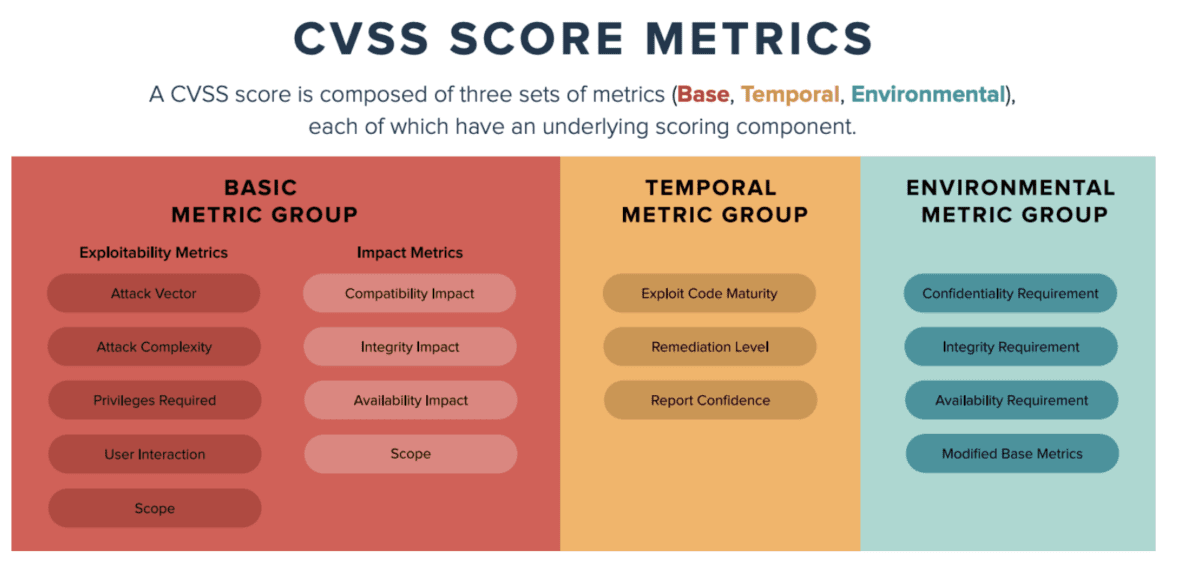
In order to prioritize vulnerabilities, we need to analyze their severity levels. These severity levels are often judged using CVSS scores. The higher scores point to more severe vulnerabilities that are easily exploitable and can also do the most damage to your assets.
Once we have CVSS scores for each scanned vulnerability, then prioritization becomes much easier, and we can finally focus on major threats while ignoring all the false positives and less severe flaws.
- Verify Scan’s Authenticity
The most severe vulnerabilities might be a false positive. Hence, it is important to verify that whether the scanned vulnerability is actually inside the system or your vulnerability scanner mixed it up with some other vulnerability.
This step is important because it allows us to filter any unnecessary false positives that may waste our time.
- Impact on your Assets
Some vulnerabilities impact the whole infrastructure, while others might be limited to a few systems. Therefore, security pentesters should check the impact of severe vulnerabilities on all applied assets inside a company.
At this stage, we can again filter out and prioritize our vulnerabilities because if a vulnerability is impacting over 80% of all the assets, then it should be our top priority. However, if it is only impacting a few systems, then we can re-prioritize it to a lower bracket.
- Affected Assets Nature
All the assets that are easily accessible through the cloud are more vulnerable than any offline or on-site assets. Also, if your company’s revenue generating systems are impacted by a severe vulnerability, then it should be prioritized to the top.
Offline systems with protection from unauthorized access can be given low priority, but all systems that are exploitable and accessible through the internet should be fixed as soon as possible before a hacker gets remote access and damages other important assets of a company.
- Assess Exposure Time
If certain exploitable vulnerabilities are residing in a company’s system for a long time then hackers are more likely to attack because they now have time to scan, build scripts and then exploit that vulnerability to damage your company.
Along with exposure time, if the vulnerability resides in the most common systems inside your organization such as Windows OS, then hackers are more likely to exploit it.
- Enlist Mitigation Techniques
Companies mostly apply patches or send upgrades to their systems, but these mitigation methods can possibly break the key functionalities of your system. Some vulnerabilities can also be fixed by making changes in system configuration, and it will the least affect your business operations.
Also, some vulnerabilities also link to other third-party providers that you are using within your company. In this case, you might need to uninstall third-party software to apply a fix. No matter how you mitigate the risk but always focus on severe shortlisted vulnerabilities.
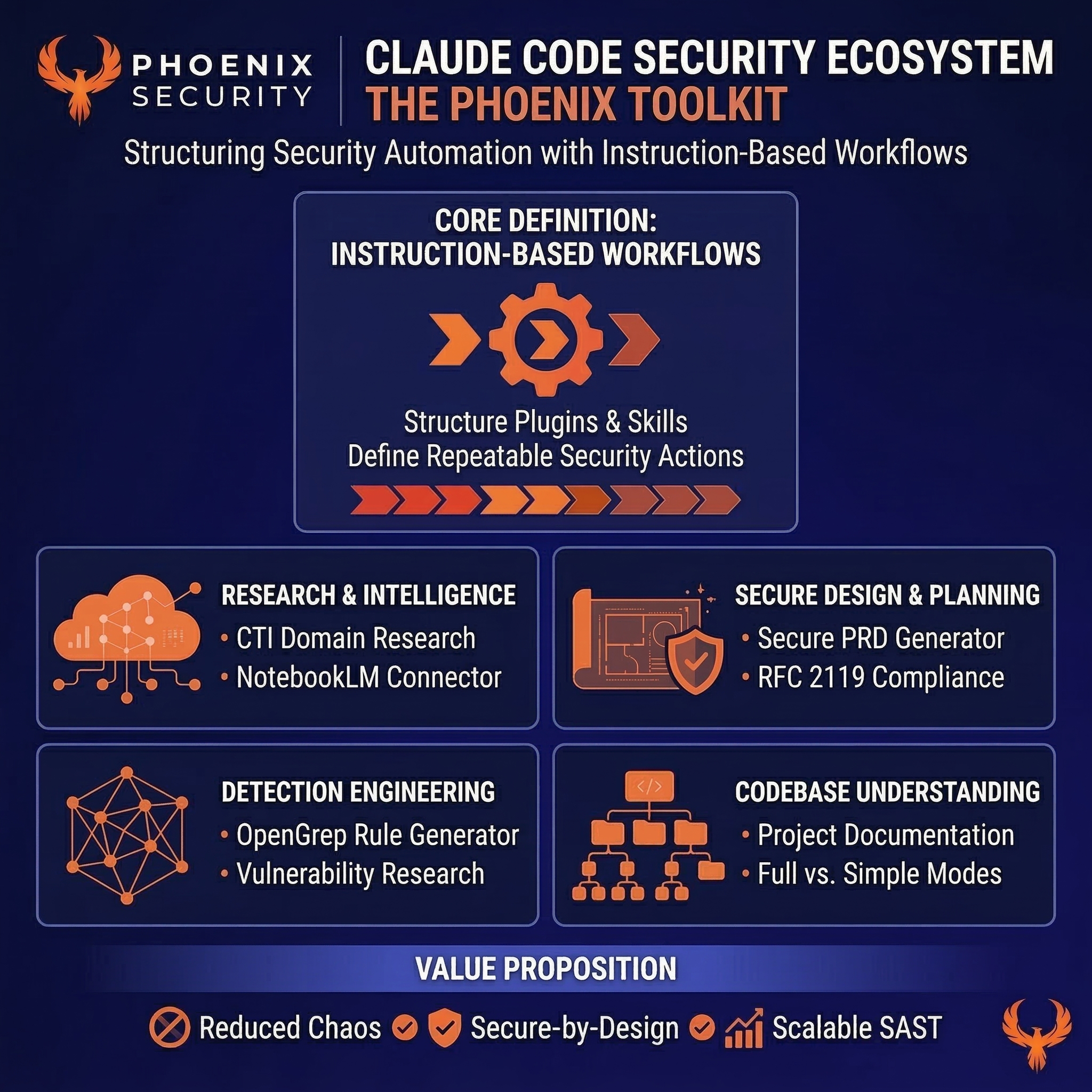
AppSec Phoenix’s All-In-One Solution – Find, Prioritize & Fix
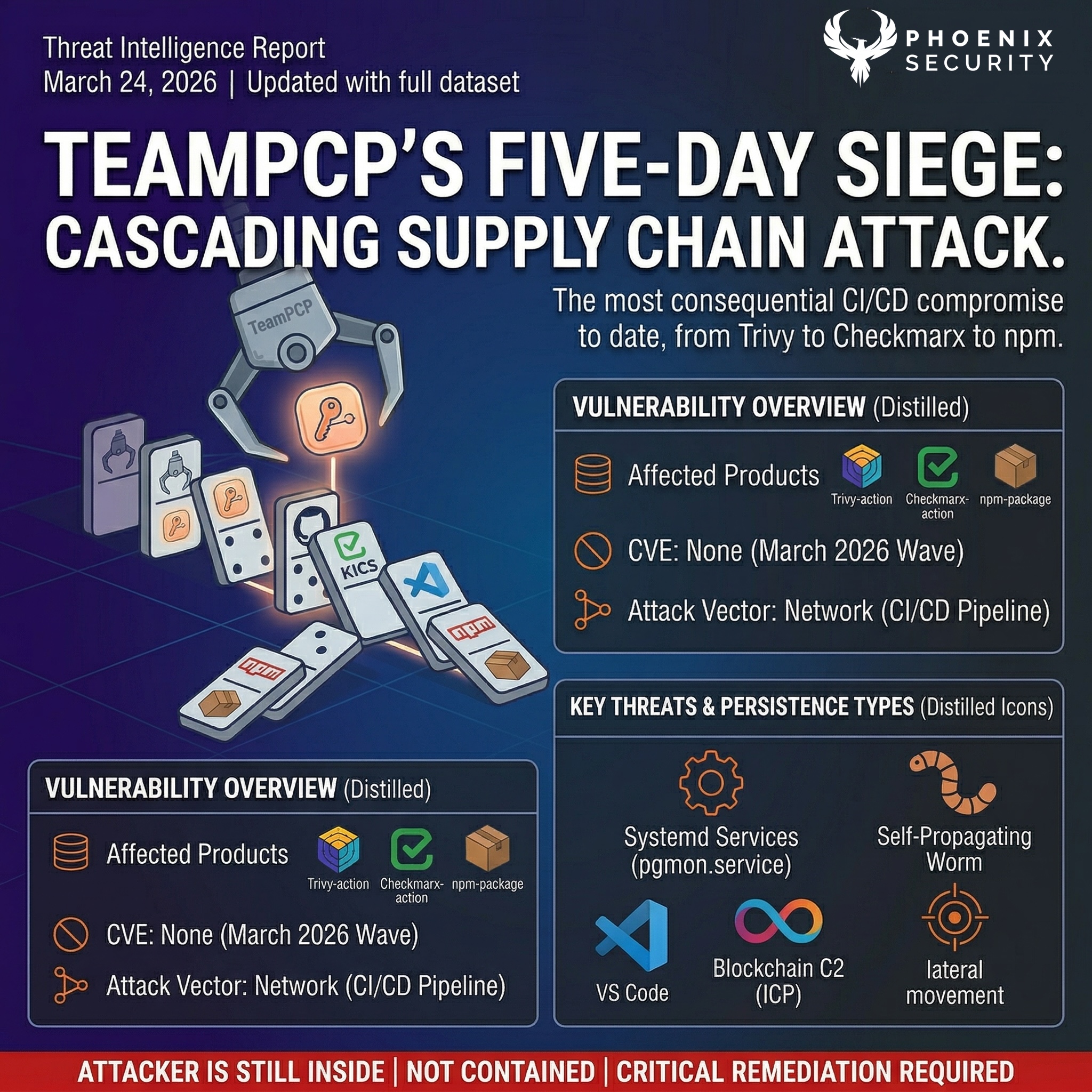
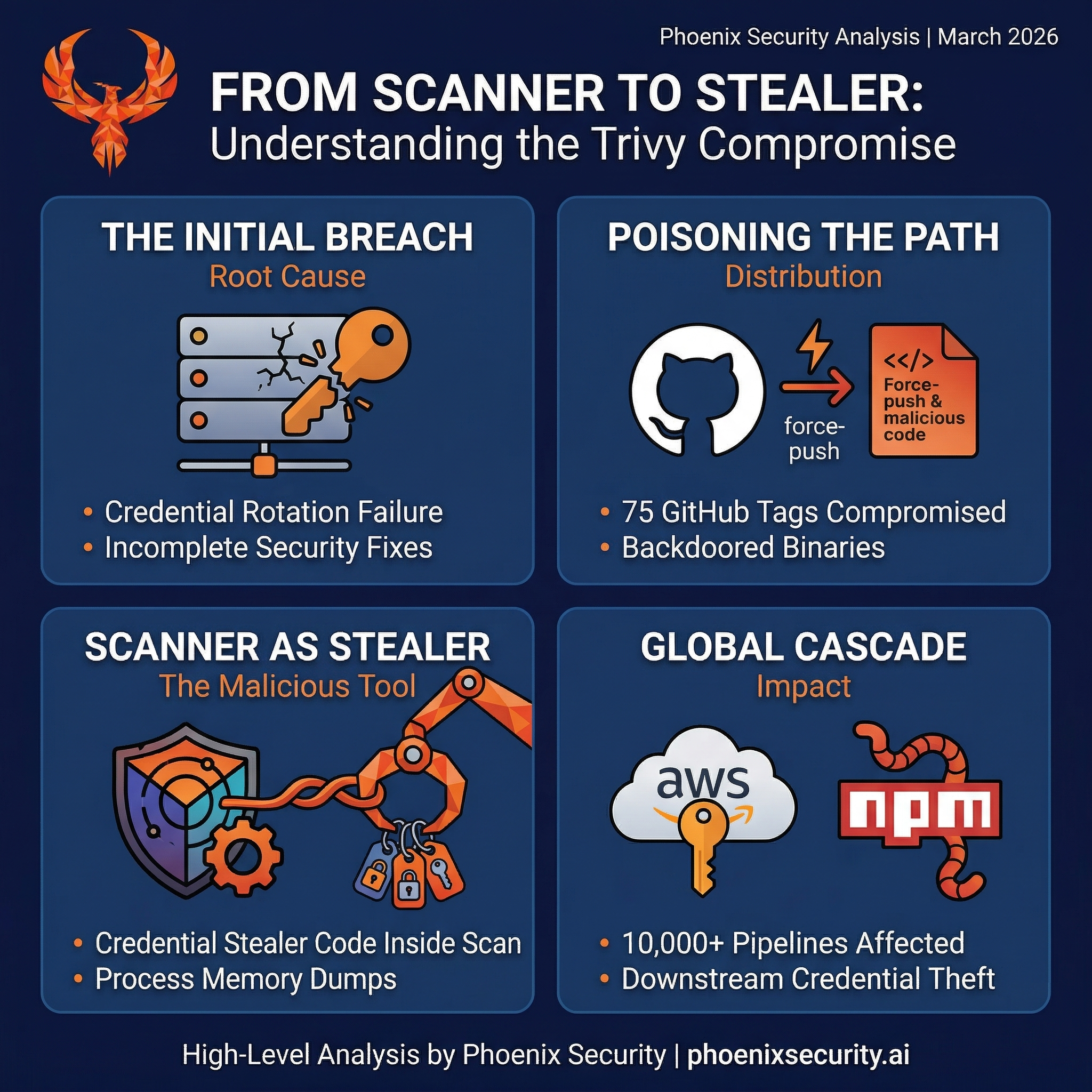
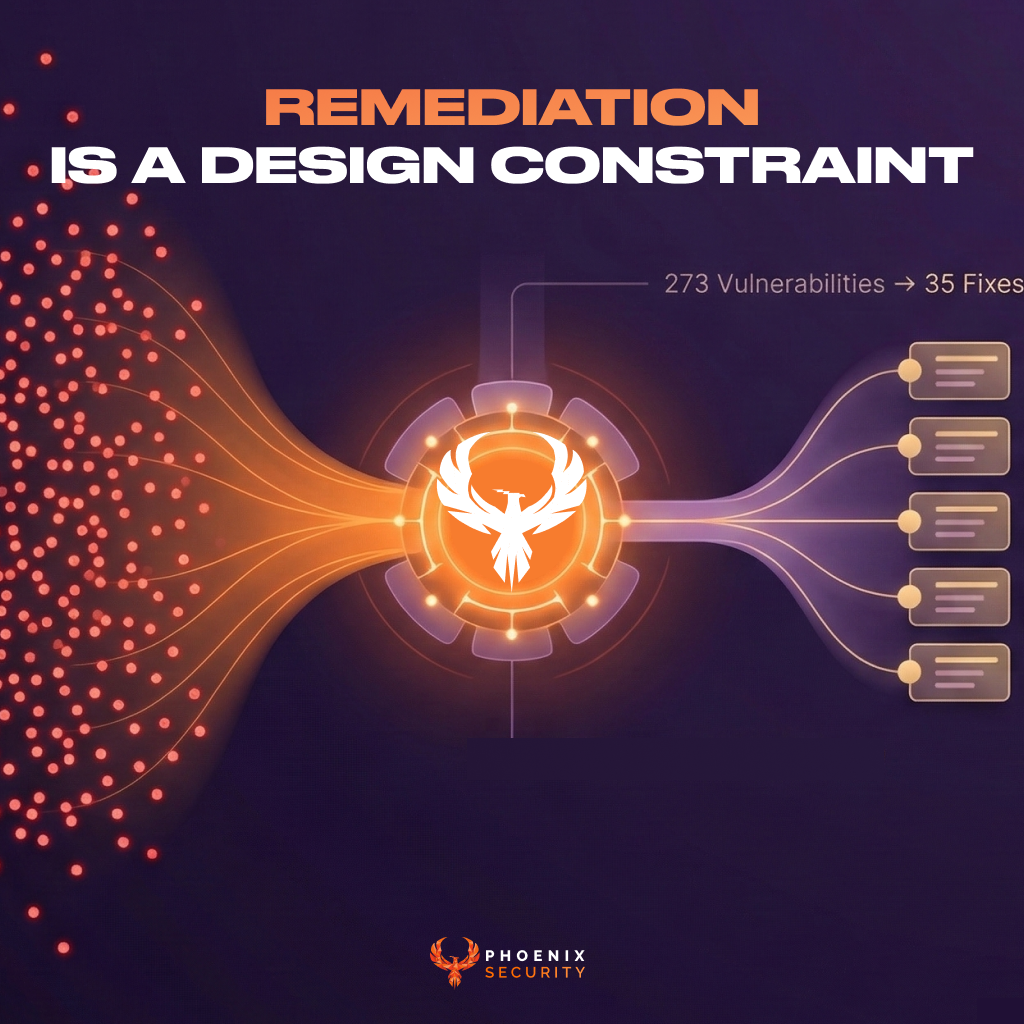
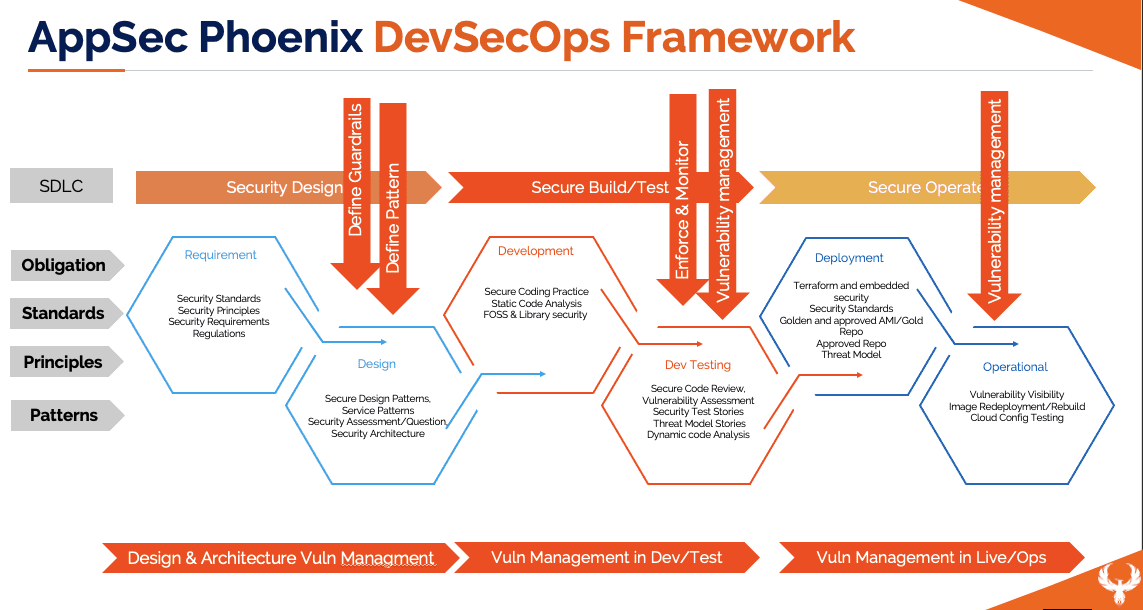
A significant challenge faced by companies is passing their applications through all of the scanners to collect data and then processing it to generate reports for risk prioritization. This approach is susceptible to errors, and many potential threats can be missed if a proper control system is not in place.
AppSec offers a single aggregation point to scan, find, prioritize and fix potential threats across all your assets. It comes with a range of indicators to tell you all potential pain points and vulnerabilities residing in your system, along with their severity level. Also, it provides an interactive dashboard for different parties to view vulnerabilities. Have a look at Detailed Features of AppSec Phoenix Solution.
Bottom Line
Prioritization brings clarity, and it allows focusing on the important flaws that are most impacting for your company. We have our 7-step approach to help you analyze, prioritize and mitigate vulnerabilities in a much better and professional way.