Gartner’s recent Innovation Insight report on Application Security Posture Management (ASPM) predicts that ASPM and solutions like Phoenix Security will be crucial in modern application development, empowering organizations to take a risk-based approach to application security. Phoenix Security’s ASPM tools will enable organizations to gain visibility into their applications’ overall security posture, including vulnerabilities, policy violations, and other security risks, giving them control over their security risk management.
The report notes that modern application environments are becoming increasingly complex, with cloud-native architectures and microservices requiring more sophisticated security measures. ASPM solutions will be critical to help organizations secure their applications proactively. With Phoenix Security’s ASPM solutions, security teams can identify and remediate vulnerabilities and other security issues before attackers can exploit them, giving organizations greater control over their security posture.
The report also predicts that ASPM, like Phoenix Security and Phoenix Security, will continue to evolve, incorporating new technologies like machine learning and artificial intelligence to improve accuracy and automate certain security tasks. Moreover, ASPM solutions will enable organizations to take a risk-based approach to security, allowing them to prioritize security issues based on the severity of the risk, ensuring that they focus their resources where they are most needed.
Finally, the article emphasizes that giving control to organizations over their security risk management is essential.
Phoenix Security’s ASPM solutions will provide security and development teams with a holistic view of their applications’ security posture, promoting greater collaboration and enabling organizations to integrate ASPM solutions into their broader DevOps toolchain.
Contents
ToggleKey Hot Takes from Gartner Innovation Insight on ASPM

With Phoenix, we have been pioneering the ASPM approach since our inception in 2020 and enabling organizations to set risk-based targets that translate into actions for engineers.
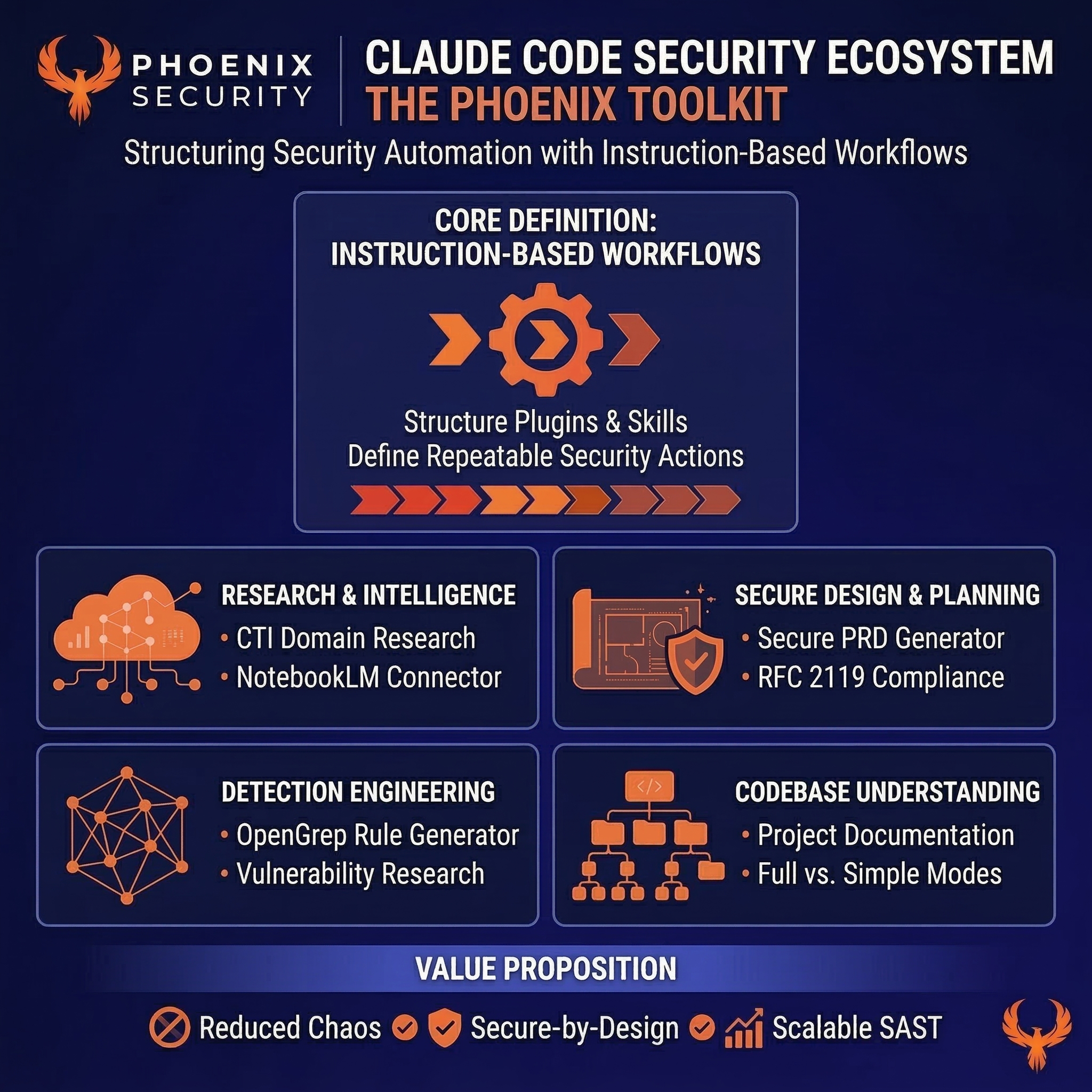
We did not stop there and brought ASPM and cloud contextualization together, unifying the risk-based and contextualized approaches under one single automated workflow.
- ASPM is an increasingly essential tool for managing application security risks, with its adoption still in its infancy. The report predicts that over 40% of organizations that develop proprietary applications will adopt ASPM by 2026. It emphasizes that when selecting an ASPM vendor, organizations must ensure that the tool meets their specific use cases.
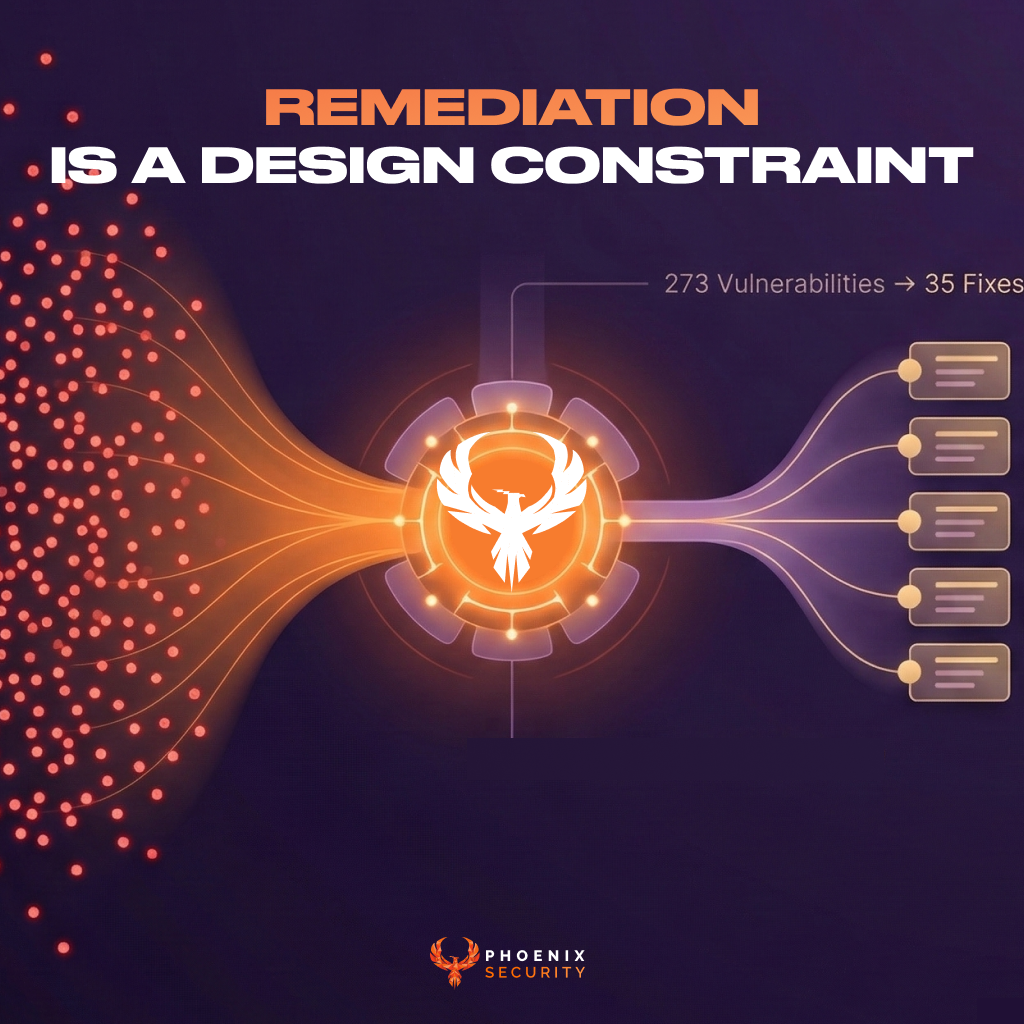
- For ASPM solutions to be successful, they must integrate seamlessly with other security tools and processes, replacing the traditional silos of visibility and responsibility with a consolidated view of security-related information. ASPM solutions must provide actionable insights and prioritize remediation efforts to enable teams to focus on issues that will provide the greatest return in overall risk reduction.
- The report also notes that ASPM solutions need to support multiple deployment models, including on-premise, cloud, and hybrid environments. As such, organizations must ensure that the chosen ASPM vendor can support all legacy applications in their portfolio.
- Automation is also key to effective ASPM. The report recommends that ASPM tools automate the testing and remediation process as much as possible to reduce the burden on security teams. This includes automating the testing and remediation process and providing continuous testing and monitoring to promptly identify and remediate new vulnerabilities.
In summary, ASPM is a critical tool for managing application security risks, and its adoption is expected to increase significantly in the coming years. For organizations to benefit from ASPM solutions, they must integrate seamlessly with existing security tools and processes, provide actionable insights, prioritize remediation efforts, support multiple deployment models, and automate testing and remediation processes as much as possible.
In conclusion, ASPM tools and solutions like Phoenix security will be increasingly vital as organizations seek to secure their applications in a complex and ever-changing threat landscape. By taking a risk-based approach to application security and empowering organizations to gain control over their security risk management, Phoenix Security’s ASPM solutions will help organizations mitigate security risks and strengthen their overall security posture.
Next steps for Application Security
ASOC + Risk + Automated actions + ASPM = This is the SMART ACT Platform that phoenix security brings and has been pioneering since 2020
Get in control of your Application Security posture and Vulnerability management
ASPM vs ASOC
ASOC, or Application Security Orchestration and Correlation, is a security solution that provides centralized visibility and control over an organization’s application security posture. ASOC solutions typically incorporate multiple security tools, including static analysis, dynamic analysis, and Software Composition Analysis (SCA) tools, into a single platform, allowing security teams to manage their application security posture more effectively.
ASPM, or Application Security Posture Management, is a security solution that provides insight into an organization’s application security posture, including vulnerabilities, policy violations, and other security risks. ASPM tools typically provide a holistic view of an organization’s application security posture, enabling security teams to proactively identify and remediate vulnerabilities and other security issues.
The main difference between ASOC and ASPM is the age of the term. ASOC tools were the first centralizing tools to bring vulnerabilities from application security tools together. ASPM tools bring the concept of ASOC a step forward, adding risk and sometimes context in tools like Phoenix security.
| Features | ASOC | ASPM |
| Purpose | Centralize Vulnerabilities from Application Security Testing tools | Centralize Vulnerabilities from Application Security Testing tools. Bring Cloud and Risk view into a central posture |
| Functionality | Incorporates multiple security tools, including static analysis, dynamic analysis, and SCA tools, into a single platform | Provides a holistic view of an organization’s application security posture with application security in contextualized view |
| Approach | Focuses on providing centralized visibility and control | Focuses on providing insight into an organization’s application security postureFocus on risk-based reduction and business control |
| Key Benefits | Enables security teams to manage their application security efficiently | Enables security teams to identify and prioritize in contextualized fashion Enables organization to select the risk that matters most |
| Key Features | Centralized management and orchestration of multiple security tools, real-time risk scoring, and automated remediation workflows | A holistic view of an organization’s application security posture, risk prioritization, and vulnerability remediation recommendations |
How can Phoenix Security help to assess your posture?
In conclusion, ASPM tools and solutions like Phoenix security will be increasingly vital as organizations seek to secure their applications in a complex and ever-changing threat landscape. By taking a risk-based approach to application security and empowering organizations to gain control over their security risk management, Phoenix Security’s ASPM solutions will help organizations mitigate security risks and strengthen their overall security posture.
With Phoenix Security’s Appsec Solution and ASPM solution, security teams can focus on more strategic actions as our solution takes care of tedious and time-consuming tasks, such as data aggregation, issue prioritization, and tracking. By automating these tasks, our solution reduces the workload of security teams, allowing them to focus on more critical tasks such as incident response, threat hunting, and vulnerability management.