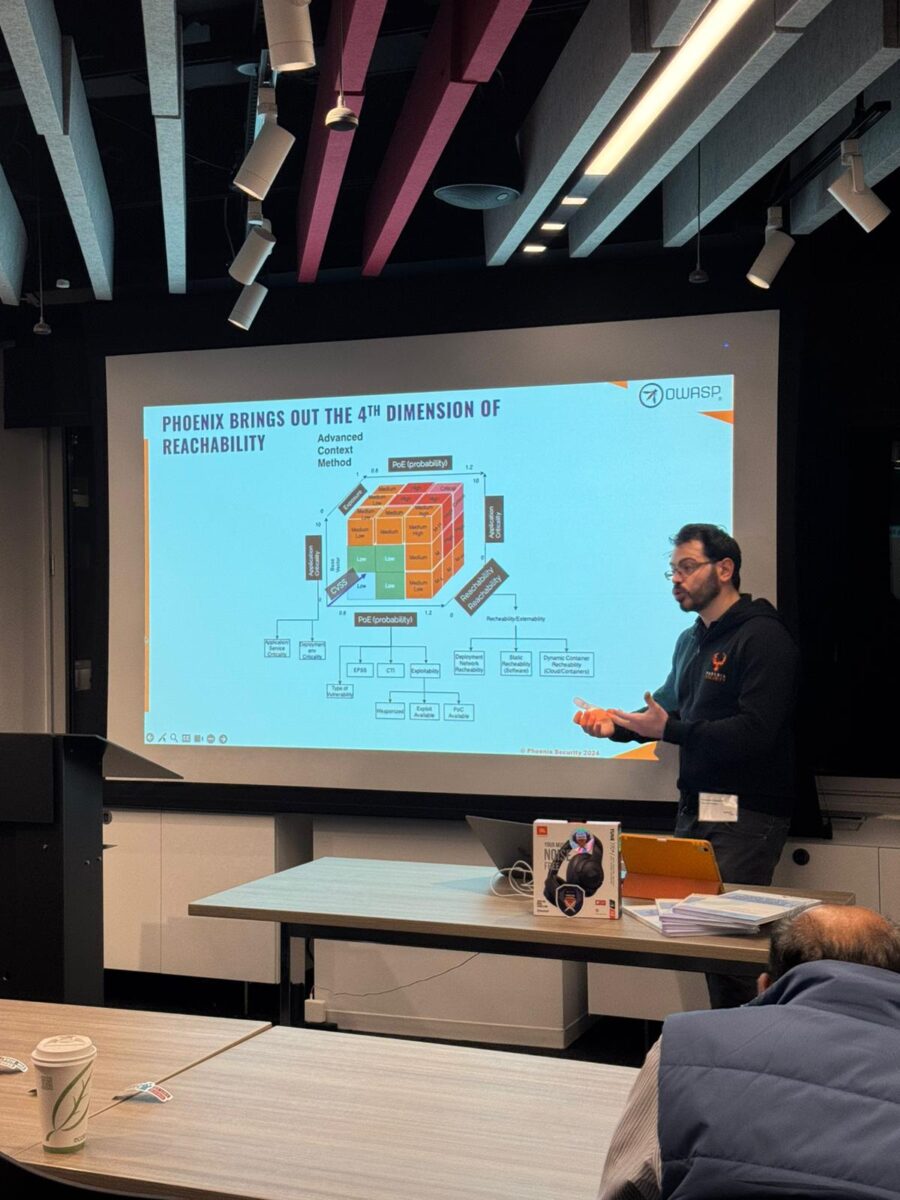
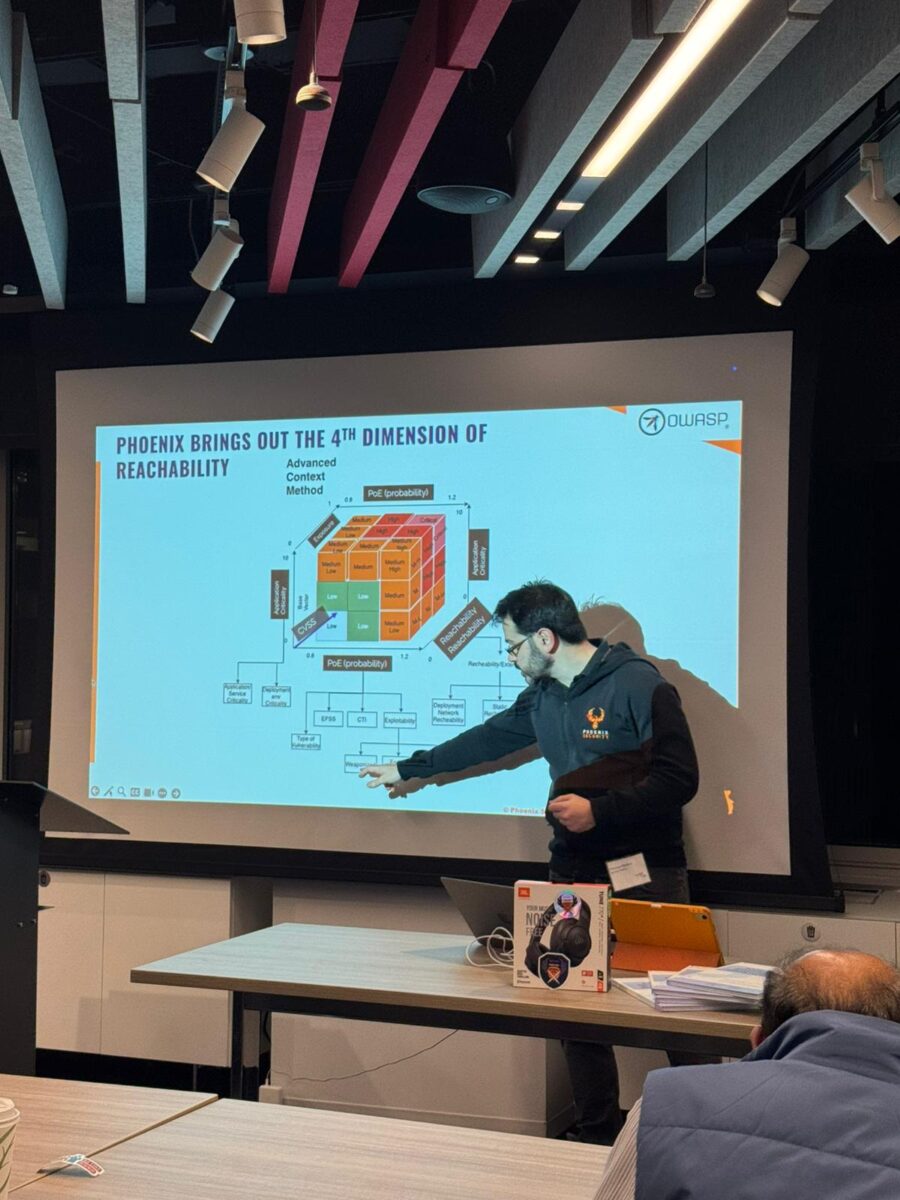
I recently had the pleasure of presenting at the OWASP NYC Chapter, where I delved into the all-too-common struggle with massive vulnerability backlogs and showase how ASPM technologies can help. My focus rested on reachability analysis, a method that pinpoints flaws likely to be exploited rather than forcing teams to chase every potential threat. This perspective aligns with Application Security Posture Management (ASPM) and promises a welcome reprieve from the usual avalanche of alerts.

During the session, I highlighted the reality that traditional scanning can’t keep up with modern container-based and cloud-centric architectures. By revealing how code, library, container, static, and runtime reachability each play a role in exploitability, I aimed to steer everyone away from perpetual patching marathons. One moment that got a hearty laugh: “Patching every reported flaw is a fool’s errand—like shoveling snow in a blizzard.” Behind the humor lurked an undeniable truth: context-driven prioritization stands far above any scattershot approach.
Contents
ToggleASPM is the heart of unifying code and cloud – Check out the snippet below:
at the end of the post there are additional resources, videos, books, and slides:
I also showcased how ASPM tools streamline remediation by clarifying which container image or application module triggered exposure. I’ve seen whole backlogs shrink when code-to-cloud traceability takes center stage. People at the webinar shared stories of Legacy software hurdles and never-ending demands from management. Several experts confirmed that concentrating on the likelihood of exploitation and genuine impact transforms how security activities unfold.
I wrapped up the talk by reminding everyone that these concepts aren’t theoretical. Attendees could download the presentation, explore a comprehensive recording, and chat one-on-one about implementation strategies. The raffle and the book signing also were a nice plus.
Check out the recent release of the Reachability analysis
We closed the event with pizza, not the NYC one, nothing like hearty food after digging into serious security topics. Those keen to dive deeper are encouraged to watch the recording, check the slides, and experiment with reachability analysis in their own environments. The difference between tackling real threats and drowning in alerts is huge, and I’m delighted to share how this approach can lighten the workload while boosting overall security.
Get a Free Posture assessment today
Some highlights of the evening:









Download the full presentation here:
Those eager to delve deeper are encouraged to watch the recording and examine the slides. Both illustrate how application security can reach new heights by understanding which flaws pose a threat. This method often slashes the workload while enhancing a team’s ability to fix what matters. Blending real data, dynamic reachability checks, and a healthy dose of humor may well be the ultimate recipe for fending off risks and keeping the dreaded vulnerability queue short.
Links and Resources:
• OWASP NYC Chapter Details:
















