From Chaos to Code Fixes: The Remediator Agent Redefines ASPM Application Security Vulnerability Management
Application and Cloud security today is defined by volume — endless alerts, duplicated findings, and disconnected tools, disconnected alerts from pentests, to on-prem vulnerabilities, unclear ownership, and divergent directives from leadership. Phoenix Security brings clarity to this chaos with the release of the new Remeditaor, now with autofix, pushing code and SCA changes directly into the source code once agreed. Phoenix pushes the new approach to SPM (Surface Posture Management) and ASM (Attack Surface Management), expanding vulnerability management, combining discovery and attribution, leveraging AI-driven context, Enabling Automated and programmatic attribution, and aligning and collaborating across code, cloud, and runtime. Instead of chasing every alert, teams gain a unified system that prioritizes what matters, enabling faster, smarter remediation within existing DevSecOps workflows.

Phoenix Security’s AI Agents were built to solve exactly that. To enhance engineers’ and developers’ workflows 10X, aligning the executive risk objective, driving down vulnerability, turning data into context, context into risk, and building a business narrative rooted in action.

The philosophy is simple:
- Scan or get the data in — scan, aggregate, and normalize vulnerabilities from every scanner, repository, and runtime source.
- Attribute accurately — assign ownership automatically to the right teams, services, and applications.
- Remediate intelligently — provide contextual fixes, flexible enough to adapt to your workflow — from autofix in GitHub, to remediation campaigns, to guided fixes for Dev and SecOps teams.
Contents
ToggleAI Agents That Work With You, Not Instead of You
Phoenix Security’s agentic architecture includes three intelligent components that work together to drive actionable security:
1. The Researcher — Context From the Outside In
The Researcher Agent, now GA, continuously monitors open and closed threat intelligence sources.
It researches advisories and any other sources of vulnerability to scale analyst capacity and leverage the power of threat intel and Gemini to identify which vulnerabilities are more likely to be exploited. The Researcher creates a detailed machine-generated vulnerability vector from research articles and advisories, tapping directly at the source and overcoming the shortcomings of NVD. The researcher rewrites CWE, fills gaps, correlates them with threat actors and known ransomware campaigns using MITRE ATT&CK techniques, and predicts exploitation likelihood using proprietary AI models developed with Google. It doesn’t just summarize CVEs — it tells you which ones are likely to be used by a threat actor to target your organization in your current context.
2. The Analyzer — Context From the Inside Out
The Analyzer Agent connects the dots between code, cloud, and runtime.
Using reachability analysis and STRIDE threat modeling, it identifies which vulnerabilities are reachable and exploitable in your environment. This ensures your team focuses only on the issues that could actually impact your business — not theoretical noise.
3. The Remediator — From Knowledge to Action
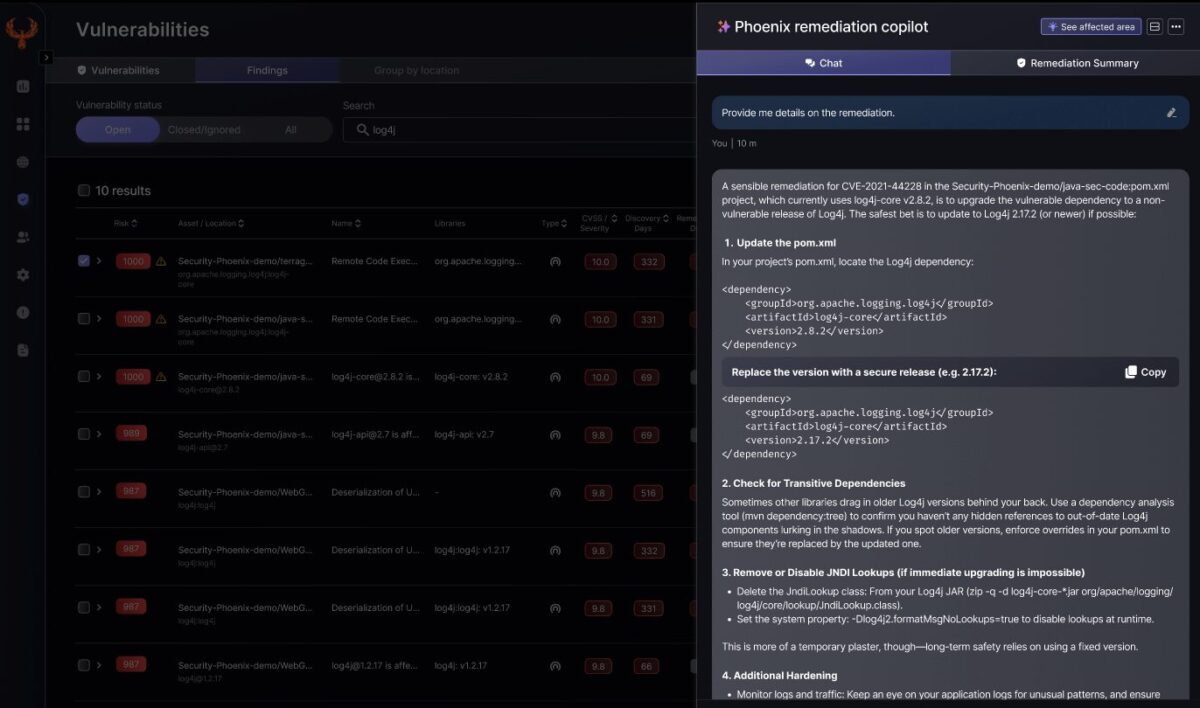
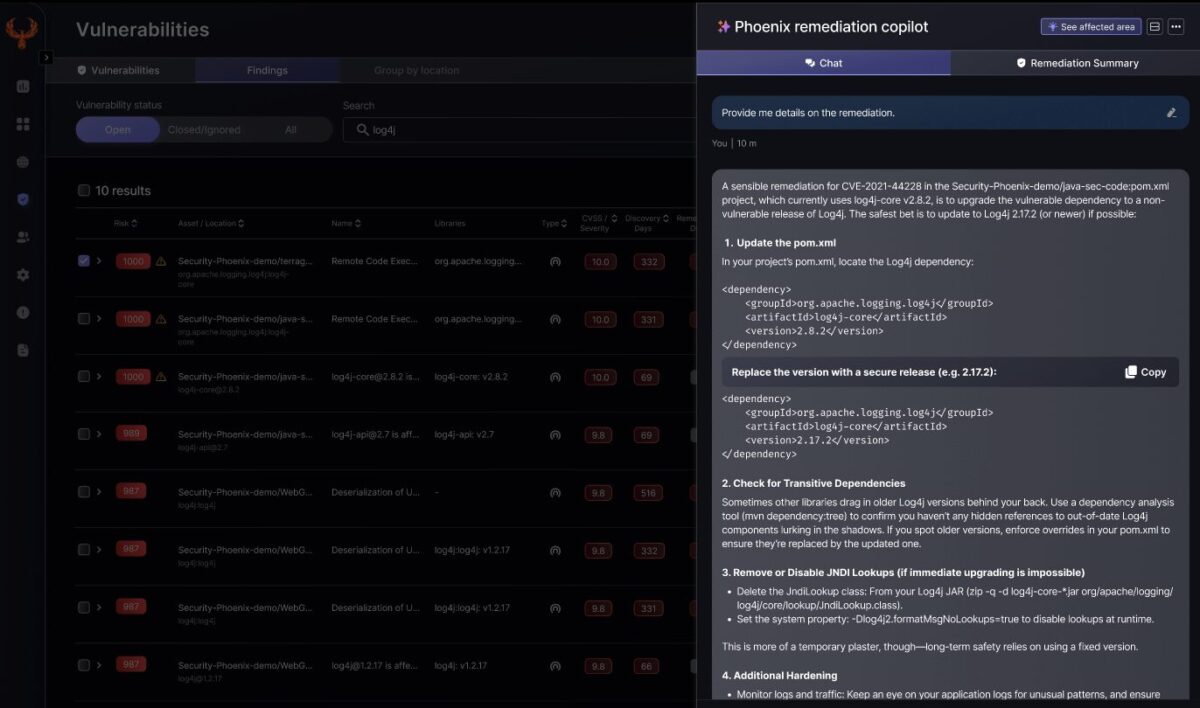
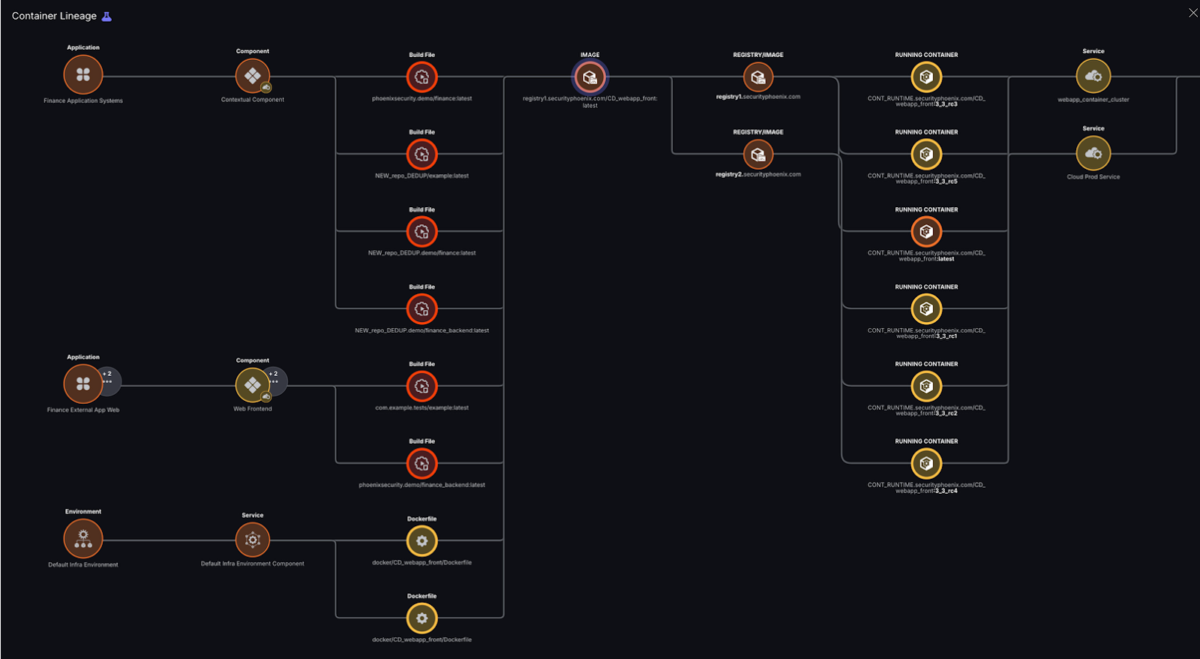
The newest member of the family, the Remediator Agent, now powered with Autofix AI, turns intelligence into execution with remediation plans, actionable tickets, and, today, direct code fixes for one vulnerability affecting a dependency, three vulnerabilities, or an entire build file.
The Remediator with contextual knowledge proposes compensating controls and WAF rules to mitigate categories of vulnerabilities
Whether you want to:
- Autofix vulnerabilities directly in GitHub via AI-agentic pull requests, understanding context and suggesting the minimal-impact change across direct and indirect dependencies
- Provide contextual remediation plans through ticket Jira or ServiceNow, or
- Execute remediation campaigns that coordinate multiple teams to remediate a vulnerability with AI augmented descriptions
The Remediator adapts to your workflow. It can fix single dependencies, chains of libraries, or even entire build files, with automated breaking-change assessment and full traceability. The Remediator takes into account the code-to-cloud context, prioritizing vulnerabilities that are reachable, and avoids pushing container vulnerabilities that are not fixable in the container file.
This flexibility empowers every organization — from fintech to ad-tech — to remediate in the way that fits their process maturity.
The Phoenix Philosophy: Context Before Automation
Phoenix Security’s approach to AI isn’t about replacing humans — it’s about enabling better decisions through contextual understanding.
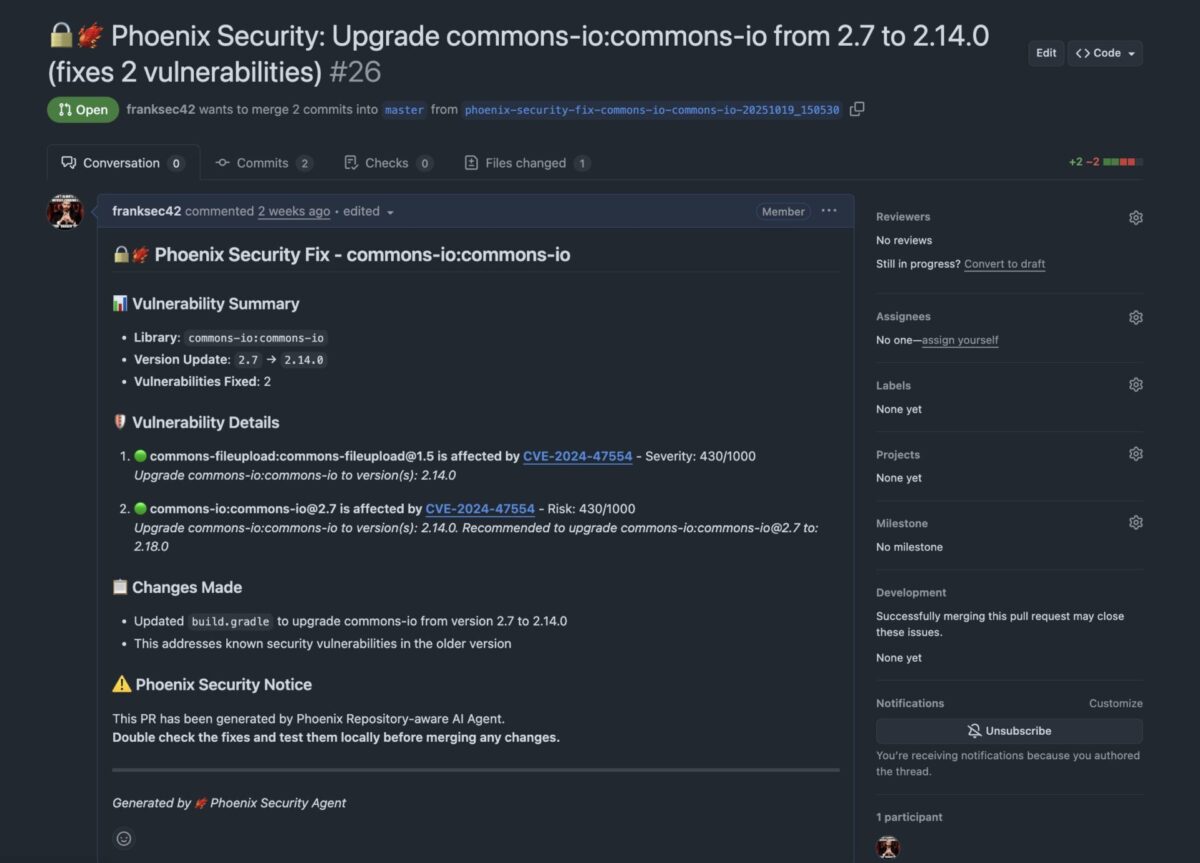
The Contextual ASPM Engine powers this philosophy by combining:
- Reachability Analysis in code and from code2cloud to cut false positives up to 87%.
- Contextual Deduplication to eliminate duplicate findings across code and runtime up to 91%.
- Container Version Control for precise lineage tracking with up to 91% vulnerability noise reduction
- 4D Risk Quantification to prioritize by business impact and exposure.
This foundation ensures AI agents act responsibly — suggesting, validating, and only then applying fixes — so organizations can accelerate remediation without introducing risk.
Real-World Results: What Happens When Context Meets Action
Organizations using Phoenix Security have achieved transformational outcomes:
- ClearBank scaled security 10X without adding headcount — cutting container noise by 98% and saving millions in developer time.
- Bazaarvoice reduced critical vulnerabilities to 0 in the first month and high-risk findings by 40%, resulting in an overall 98% reduction in vulnerability false positives.
- Ad-Tech achieved a 78% reduction in container vulnerabilities and reclaimed nearly $2M in developer hours.
Across all industries, the result is the same — security teams move faster, developers stay in flow, and organizations fix what truly matters.
Flexible by Design: Adapting to Every Workflow
Every enterprise works differently — and Phoenix’s AI agents are built to respect that.
- Security-driven organizations can use campaign-based remediation and ticket automation.
- Engineering-led teams can enable auto-generated GitHub pull requests for instant fixes.
- Hybrid enterprises can choose guided remediation paths that explain why, how, and when to fix issues.
Phoenix meets you where you are, integrating into your workflow — seamlessly integrating with your DevSecOps pipeline and letting teams stay in control.
Conclusion: Human-Aligned AI for Real-World Remediation
Phoenix Security’s AI Agents mark a milestone for application security, integrating the power of scale and refined Agentic work, moving from raising vulnerabilities to delivering actionable plans in the hands of the team that require it.
The message is clear: Security and development can move fast, together.
With the Researcher providing threat context, the Analyzer modeling real risk, and the Remediator delivering intelligent fixes, Phoenix Security enables organizations to reduce risk by up to 99% while keeping humans in the driver’s seat.
Because AI shouldn’t replace your security team — it should empower them to do their best work, faster.
How Phoenix Security Can Help

Organizations often face an overwhelming volume of security alerts, including false positives and duplicate vulnerabilities, which can distract from real threats. Traditional tools may overwhelm engineers with lengthy, misaligned lists that fail to reflect business objectives or the risk tolerance of product owners.

Phoenix Security offers a transformative solution through its Actionable Application Security Posture Management (ASPM), powered by AI-based Contextual Quantitative analysis and an innovative Threat Centric approach. This innovative approach correlates runtime data with code analysis and leverages the threats that are more likely to lead to zero day attacks and ransomware to deliver a single, prioritized list of vulnerabilities. This list is tailored to the specific needs of engineering teams and aligns with executive goals, reducing noise and focusing efforts on the most critical issues. Why do people talk about Phoenix

• Automated Triage: Phoenix streamlines the triage process using a customizable 4D risk formula, ensuring critical vulnerabilities are addressed promptly by the right teams.
• Contextual Deduplication: Utilizing canary token-based traceability, Phoenix accurately deduplicates and tracks vulnerabilities within application code and deployment environments, allowing teams to concentrate on genuine threats.
• Actionable Threat Intelligence: Phoenix provides real-time insights into vulnerability’ exploitability, combining runtime threat intelligence with application security data for precise risk mitigation.

By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.
















