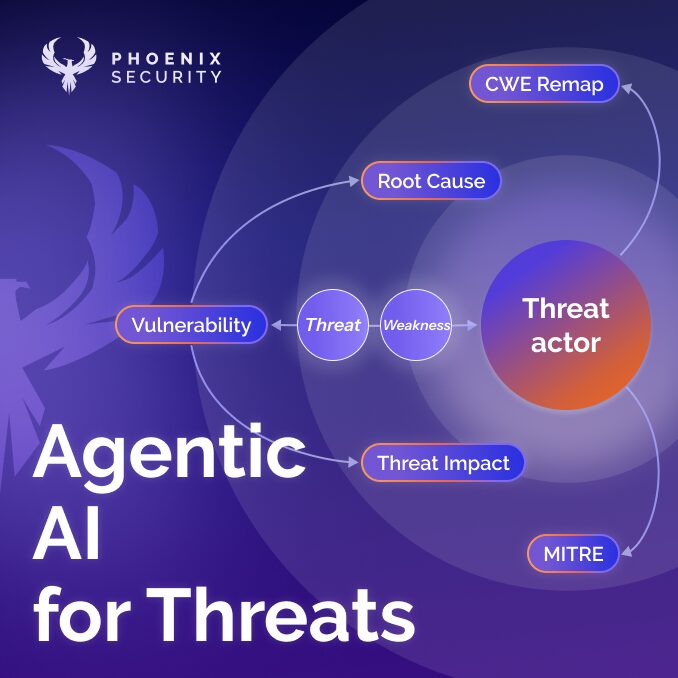
Raleigh, NC 08/10/2025— Phoenix Security is proud to announce the launch of its first AI-powered Threat-Centric Agent at VulnCon, marking a major leap forward in proactive vulnerability management and remediation. This new agent, built on a 3-step threat-centric approach, is designed to work seamlessly alongside Phoenix’s Reachability Analysis AI Agent and Blast Radius Analysis Copilot, enabling organizations to focus on the most dangerous vulnerabilities and apply targeted remediation strategies with unmatched precision.
The new Threat-Centric AI Agent is the result of Phoenix Security’s continuous innovation in the cybersecurity space. With Reachability Analysis AI already achieving a 71.5% reduction in vulnerabilities for high-profile clients like Clear Bank, and the Blast Radius Analysis Copilot providing invaluable insight into the impact of vulnerabilities within network ecosystems, the integration of this agent promises to provide even greater risk mitigation capabilities. Together, these solutions align to ensure comprehensive, accurate, and efficient vulnerability management across diverse IT environments.
Check out the detailed blog: https://phoenix.security/threat-centric/
The information in this article is also available in greater detail in the eBook – A threat-centric approach on vulnerabilities.
Download the eBook on LLM Application for a Threat-Centric Approach on Vulnerabilities
The new agent aligns with a three-step approach: it analyzes threats side by side with the proven Reachability Analysis AI Agent – which has achieved up to 71.5% reduction in vulnerabilities for clients like Clear Bank – and the Blast Radius Analysis Copilot. Early testing and more information are available at
https://ai-threat.phoenix.security
The underlying core is the 4D Risk Formula https://phoenix.security/risk-formula/, a framework built on four critical dimensions:

1. Business Context (Dimension 1)
Evaluates how vital the software is, highlighting potential disruptions to operations.
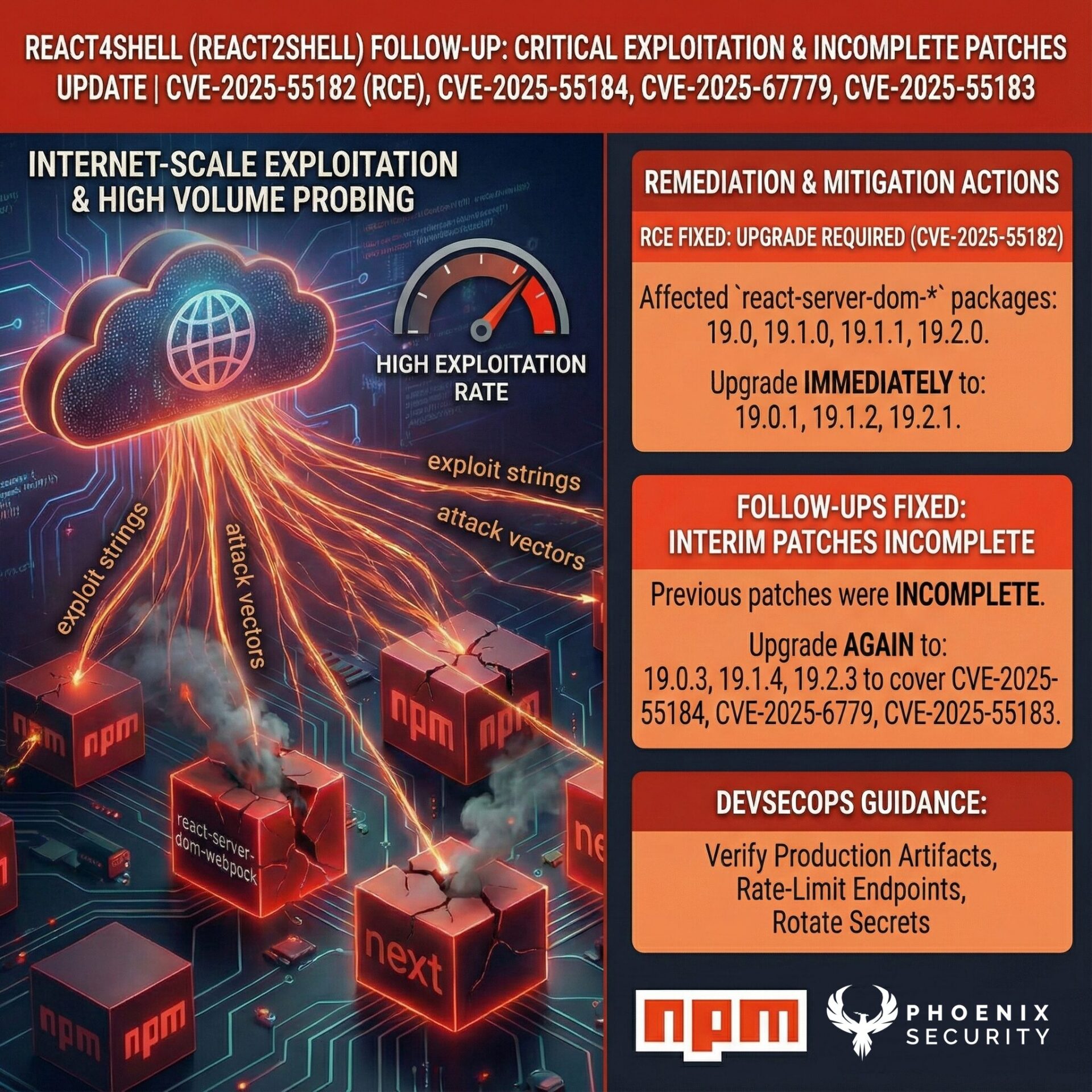
2. Dangerousness of the Vulnerability (Dimension 2)
Leverages CWE/CVE standards to gauge severity levels, covering both known weaknesses and emerging vectors.
3. Probability of Exploitation (Dimension 3)
Factors in exploit weaponization, zero-day risk, and active intelligence feeds for a stronger predictive outlook.
4. Deployment Context (Dimension 4)
Distinguishes production from non-production systems, applying contextual canary tokens to measure real exposure and prioritize remediation actions.
The Threat-Centric Agent combines these dimensions with Phoenix Security’s Application Security Posture Management (ASPM) strategy. By focusing on probability, business impact, and asset exposure, security leaders gain clearer visibility into immediate threats and a streamlined path to remediation. Integrating robust data from the Reachability AI Agent https://phoenix.security/phoenix-security-recheability/ and the Blast Radius Copilot https://phoenix.security/phoenix-security-blast-radius/ ensures comprehensive coverage, from initial detection all the way through to a rapid fix.
This approach cements Phoenix Security’s leadership in cybersecurity, enabling teams to align vulnerability management with real-world attacker behavior and emerging zero-day threats. The synergy of ASPM, precise remediation workflows, and contextual intelligence propels enterprises toward a more resilient security posture. Visit https://phoenix.security/ for additional insights on strengthening application security through this new AI Threat-Centric Agent and the integrated 4D risk methodology.
How Phoenix Security Can Help

Organizations often face an overwhelming volume of security alerts, including false positives and duplicate vulnerabilities, which can distract from real threats. Traditional tools may overwhelm engineers with lengthy, misaligned lists that fail to reflect business objectives or the risk tolerance of product owners.

Phoenix Security offers a transformative solution through its Actionable Application Security Posture Management (ASPM), powered by AI-based Contextual Quantitative analysis and an innovative Threat Centric approach. This innovative approach correlates runtime data with code analysis and leverages the threats that are more likely to lead to zero day attacks and ransomware to deliver a single, prioritized list of vulnerabilities. This list is tailored to the specific needs of engineering teams and aligns with executive goals, reducing noise and focusing efforts on the most critical issues. Why do people talk about Phoenix

• Automated Triage: Phoenix streamlines the triage process using a customizable 4D risk formula, ensuring critical vulnerabilities are addressed promptly by the right teams.
• Contextual Deduplication: Utilizing canary token-based traceability, Phoenix accurately deduplicates and tracks vulnerabilities within application code and deployment environments, allowing teams to concentrate on genuine threats.
• Actionable Threat Intelligence: Phoenix provides real-time insights into vulnerability’ exploitability, combining runtime threat intelligence with application security data for precise risk mitigation.

By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.