ASPM application security vulnerability management just leveled up. Phoenix Security 3.30 delivers smarter exception handling, richer dashboards, and visual vulnerability intelligence to help DevSecOps teams remediate faster across code-to-cloud environments. This release adds automation, context, and clarity — turning complex data into decisions that strengthen your application security posture.
Contents
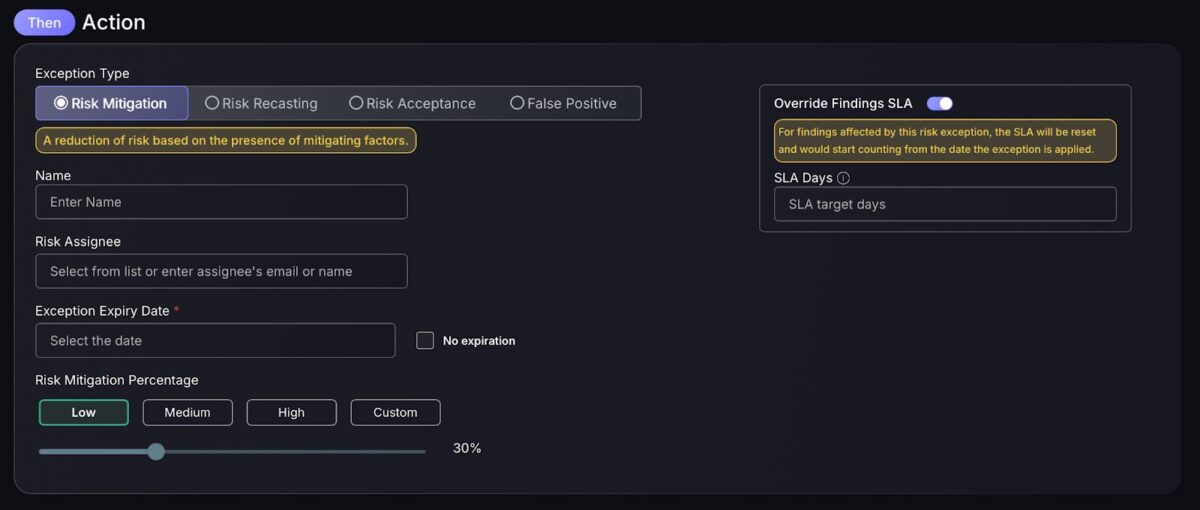
ToggleException Engine Improvements — Now with SLA Overrides
The Exception Engine automates how Phoenix handles findings that require special treatment based on predefined matching conditions. This can be through marking items as false positives, increasing risk scores through recasting, or decreasing them via mitigation.
In this release, we’ve added the ability to apply SLA overrides directly within Exception Engine rules. This enhancement ensures that when findings are marked as exceptions, their remediation timelines can be automatically reset to a specified number of days, providing teams with finer control and greater flexibility in managing compliance and response expectations. This also ensures that where exceptions are applied, remediation timelines are set to factor in the new criticality level.
Dashboard & Visualization Enhancements
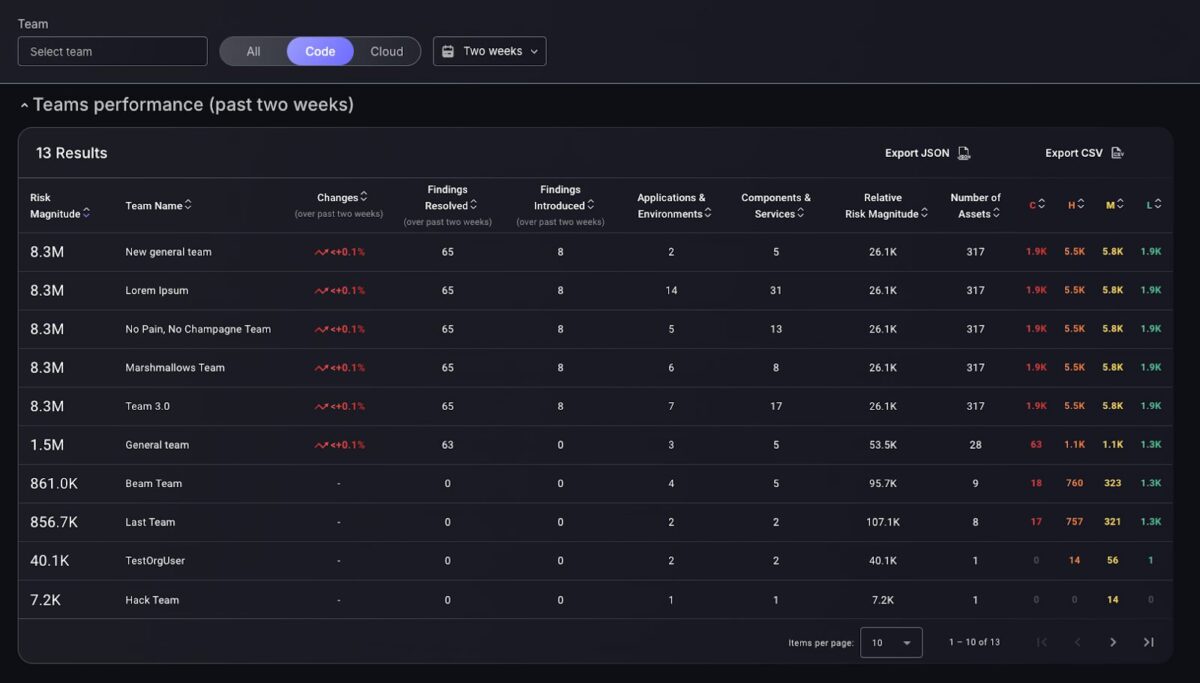
Code / Cloud Toggle for All Teams Dashboard
A highly rated feature from our clients is the global scope toggling, which enables users to toggle their organizations scope between code and cloud to review dashboard metrics. This feature, previously introduced to main dashboards, has now been introduced to the main team dashboard. This gives team leaders the ability to review team performance based on cloud or code improvements, unlocking clear insight into which teams are progressing best in certain areas. Revealing which teams perform best on cloud or code issues, giving the context for making changes to teams and providing support to teams which do not perform as well in specific areas.
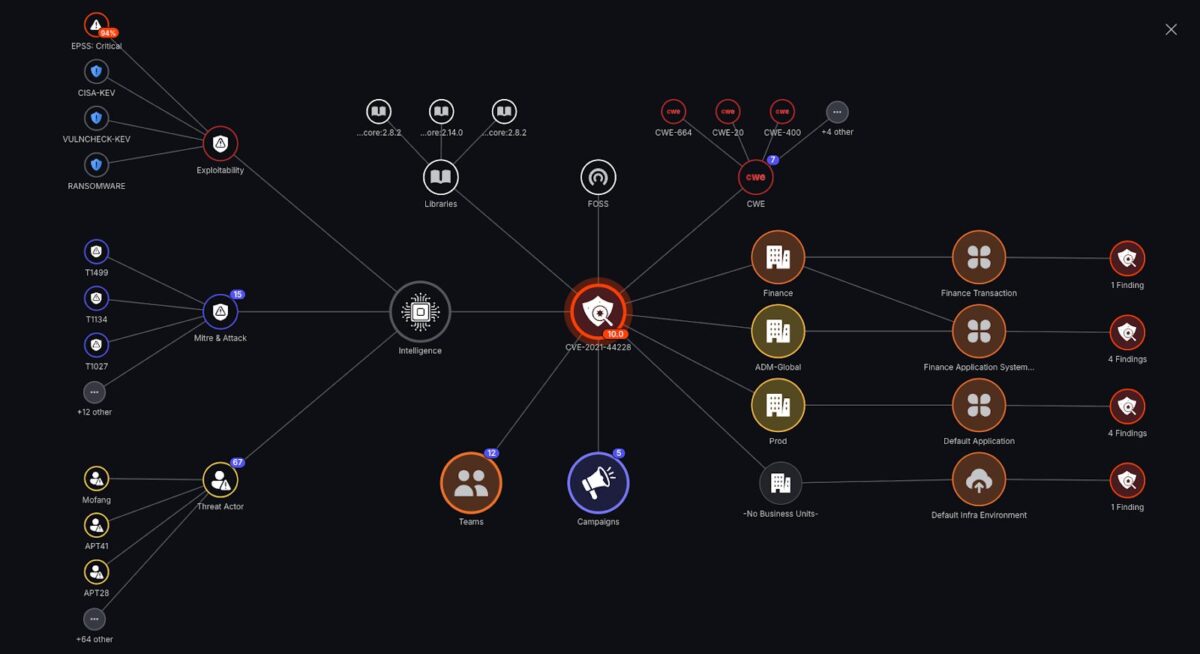
Vulnerability Intelligence Graph (Preview)
Leverage the Vulnerability Intelligence Graph for a complete, visual analysis of how vulnerabilities are connected and distributed across your organization.
This new capability provides a unified view linking vulnerabilities to campaigns, libraries, business units, teams, applications, assets, and even down to the individual finding level — including associated CVEs, CWEs, and threat intelligence.
But it goes further: the graph merges this organizational mapping with insight intelligence, delivering a contextual threat analysis layer that visualizes exploitability, threat actors, attack techniques, and related threat types. This combination gives teams a holistic view of both where vulnerabilities exist and how they are being leveraged in the wild — helping prioritize remediation based on real-world risk.
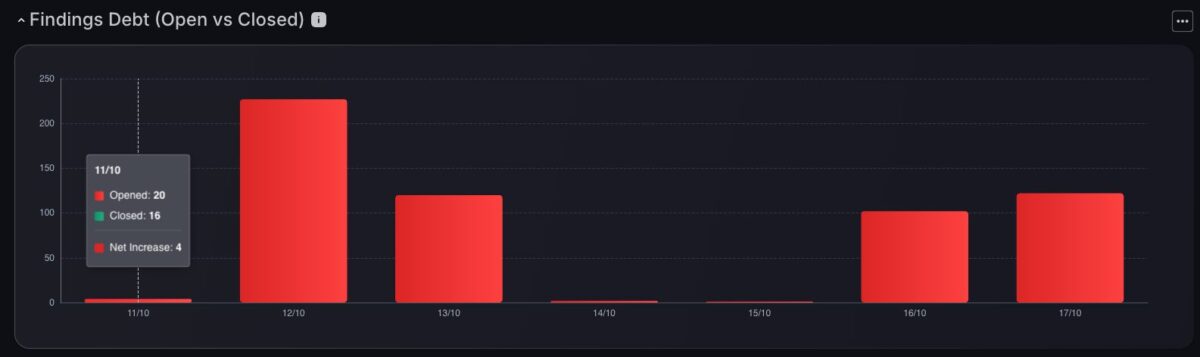
Findings Debt Chart
The new Findings Debt Chart transforms raw data into actionable insight. Instead of only tracking how many findings are open, teams can now measure progress: “This week, we opened X more tickets than we closed.”
Color-coded bars show whether you’re in finding debt (red) or achieving net reduction (green) – giving a clear snapshot of remediation velocity.
Findings & Correlation Enhancements
Sort Findings by Last Seen
At Phoenix, we are dedicated to providing unlimited freedom to filter for specific findings in as many ways as possible. The new Last Seen filtering option accompanies the findings Reported in the Range feature to provide a new way of filtering for findings based on when they were last reported. This enables you to manually track findings which are no longer being picked up by scanners or imports. As well as this you can use the Reported in the Range feature to filter for findings which have existed in the platform for the longest and have also recently been reported.

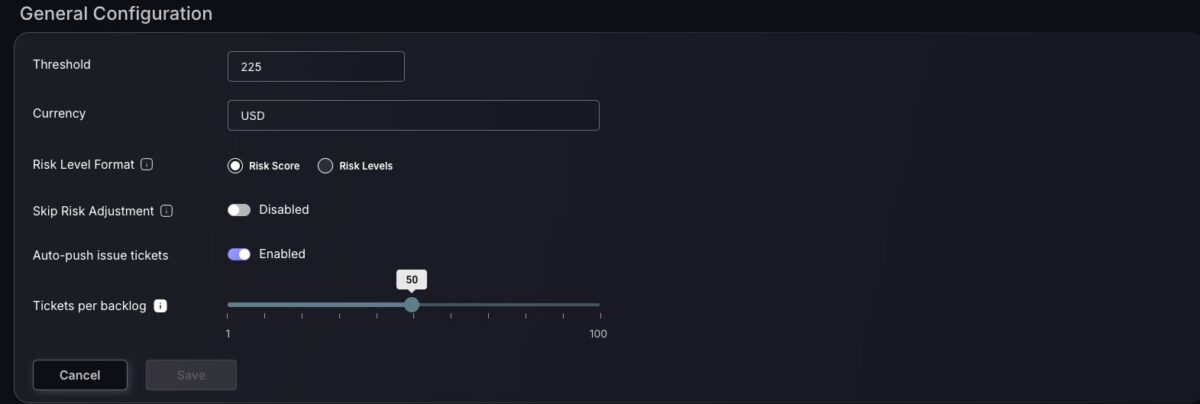
Switch for Contextual Deduplication Risk Adjustment
Contextual deduplication risk adjustment will refactor the risk score given to findings based on their correlation and deployment type. This ensures that contextual deduplicates are treated differently within your organization, based on factors such as the number of linked deduplicates. However, we have introduced a feature to disable this risk adjustment to give users the flexibility to adjust the risk scores themselves by applying exceptions such as risk mitigation and recasting.
Data Export & Reporting
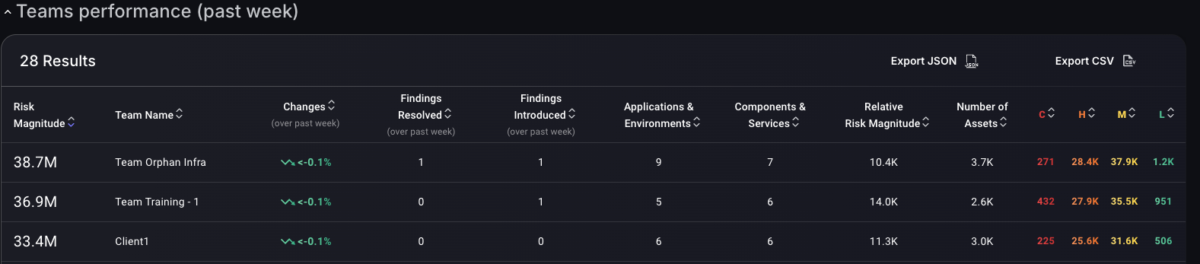
Export Team Stats in CSV or JSON
We’ve introduced the ability to export team performance statistics directly from Phoenix in both CSV and JSON formats.
This enhancement gives team managers and security leaders greater flexibility in how they analyze and share performance data. Whether you want to conduct deeper trend analysis, or integrate team metrics into internal reporting workflows, exports make it simple to extract and reuse data outside of the Phoenix platform.
By supporting multiple formats, Phoenix ensures that performance insights can be tailored to your organization’s preferred tools and reporting standards — enabling a more transparent, data-driven view of team progress.
Export Assets in CSV or JSON
We’ve introduced the ability to export asset details directly from Phoenix in both CSV and JSON formats.
Asset exports provide a comprehensive, single-table view of all relevant asset information — making it easy to analyze, compare, and share data across your organization. Each export reflects your active filters, meaning the output dynamically adapts to the scope and criteria you’ve selected in the platform.
This feature enables faster reporting, simplified integration with external tools, and more flexible asset management workflows — giving teams immediate access to the precise data they need for deeper analysis and informed decision-making.

Phoenix 3.30 brings sharper visibility, smarter automation, and deeper context to application security posture management — helping teams move faster from detection to resolution across their code-to-cloud environments.
How Phoenix Security Can Help

Organizations often face an overwhelming volume of security alerts, including false positives and duplicate vulnerabilities, which can distract from real threats. Traditional tools may overwhelm engineers with lengthy, misaligned lists that fail to reflect business objectives or the risk tolerance of product owners.

Phoenix Security offers a transformative solution through its Actionable Application Security Posture Management (ASPM), powered by AI-based Contextual Quantitative analysis and an innovative Threat Centric approach. This innovative approach correlates runtime data with code analysis and leverages the threats that are more likely to lead to zero day attacks and ransomware to deliver a single, prioritized list of vulnerabilities. This list is tailored to the specific needs of engineering teams and aligns with executive goals, reducing noise and focusing efforts on the most critical issues. Why do people talk about Phoenix

• Automated Triage: Phoenix streamlines the triage process using a customizable 4D risk formula, ensuring critical vulnerabilities are addressed promptly by the right teams.
• Contextual Deduplication: Utilizing canary token-based traceability, Phoenix accurately deduplicates and tracks vulnerabilities within application code and deployment environments, allowing teams to concentrate on genuine threats.
• Actionable Threat Intelligence: Phoenix provides real-time insights into vulnerability’ exploitability, combining runtime threat intelligence with application security data for precise risk mitigation.

By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.

















