Contents
ToggleWhat is shift smart
Shift left has dominated the scene for application security and vulnerability management, we will analyse this in this article, Shifting Smart: use a Risk-based and contextual approach to vulnerability management. Bringing security tooling from production to the left (development) has generated enormous benefits and improved security practices but also created many vulnerabilities in the backlog.
How to implement a risk-based approach to application security?
In this talk, Francesco Cipollone explores how to avoid solving all the vulnerabilities and focus only on the one that matters most.
Summary of Application security talk
Francesco Cipollone, CEO and founder of Phoenix Security, discusses the challenges of vulnerability management and prioritization in application security. He emphasizes the importance of context and risk management in determining what vulnerabilities to fix and what not to fix. Cipollone suggests involving the business in the decision-making process and contextualizing vulnerabilities in terms of risk. He also stresses the importance of maintaining a positive and light approach to security. The video also discusses the importance of creating a coherent story around why a vulnerability hasn’t been exploited, especially when speaking to executives. The speaker emphasizes the need for context and a rational reason for why a vulnerability may not be a problem in the near future. The complexities of application security are also discussed, specifically focusing on the process of designing, building, testing, and operating. The speaker highlights the need to empower the business to make the right decisions with the right tools at the right time. The triage and staging of vulnerability management are also discussed, with the speaker emphasizing the need for a balance between automated and human decision-making. The importance of contextualizing vulnerability management and prioritizing risks in a way that is understandable to business stakeholders is also discussed. The use of AI and machine learning is suggested as a way to scale vulnerability management, but the speaker cautions that it is important to ensure the data being used is accurate and relevant. The video concludes with a discussion of the potential for AI to improve vulnerability management and the importance of providing context to stakeholders.
Shift Smart: How to implement a Secure SSDLC?
Want to know what a mature SDLC looks like in the modern age? Shift Smart: It’s all about building, testing, and operating with many moving components. With so many decisions to make, sometimes fixing vulnerabilities in a rapid mode is the way to go, but there always needs to be a balance. That’s why fast triage is crucial in the development process. Learn more about prioritizing vulnerability backlogs with a management solution in place.
The vulnerability management can be divided between fast triage and a backlog of security vulnerability fixes.
Shift Smart: How to set risk base targets in application security?
Want to reach the nirvana of business success? Shift smart and Unify your business, dev and ops, and security angles! This will drive business risks, enable better collaboration, and lower application security risks. And don’t be afraid to evolve your SLA – a risk-based approach is the way forward for balanced team management. Check out our articles and books for more insights!
More on risk-based SLA: https://phoenix.security/whitepapers-resources/data-driven-application-security-vulnerability-management-are-sla-slo-dead/
Shift Smart: How to automate triage in application security
Reachability, Exploitability, and Contextualization are all terms used to prioritize vulnerabilities, but what are they?
Automating vulnerability triage? It’s not as straightforward as you think. Nuances in the triage process make it hard to automate everything. But fear not! I’ve broken it down for you. The left side of the triage process can be automated with a degree of complexity, while the right side requires more human decision-making. So, automate what you can and make business decisions where you can’t. Please find out how to strike the perfect balance in our latest research.
What is reachability
Reachability from a network perspective means this vulnerability can even be triggered remotely.
Reachability from a code perspective is very different. Does this function get called? Can you find a code path to trigger the vulnerability in all the code calls?
What is the context of application security?
With network reachability, we can prioritize externally facing vs internally facing web and with a sound asset inventory,
Complexity is business complexity or the number of assets an application or service has
When it comes to exploitability, we’ve got several factors, from Threat intelligence to fixability and exploitability if an exploit is available to the likelihood of exploitation in the next 30 days leveraging EPSS data and more! #VulnerabilityManagement #AutomationWins 🤖💪
How can Security Phoenix Help
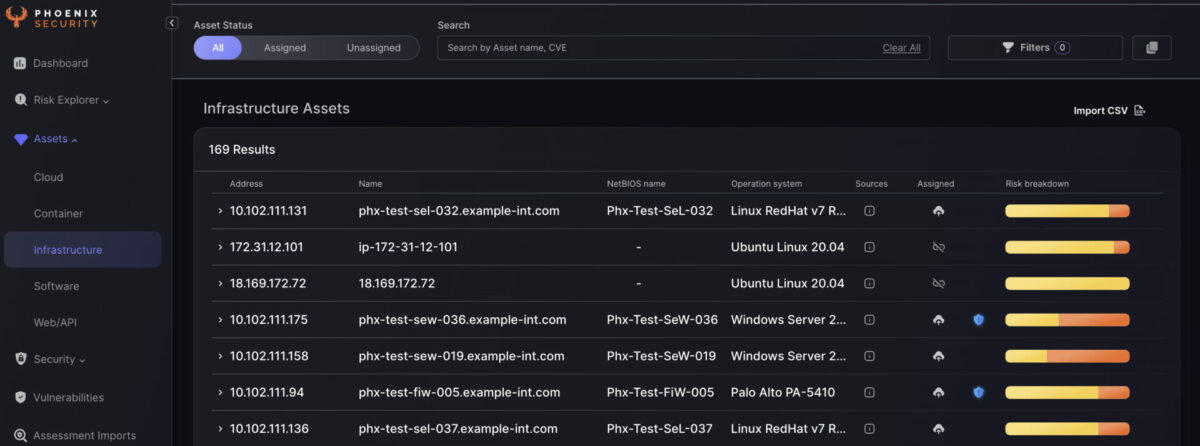
Phoenix security enables organizations to ingest vulnerabilities from multiple locations, aggregating them into products and visualizing the risk level of those products.
Phoenix security cutting-edge contextual risk-based algorithms enable organisations to prioritise application security vulnerabilities based on context and probability of exploitation and present a unified impact analysis.
The cutting-edge vulnerability selection engine enables organisations to set risk-based targets that translate into specific actions for engineers.
Get in control of your Application Security posture and Vulnerability management
Moreover, Phoenix Security’s correlation capabilities can help organizations link the activities in the code with the context in the shift-right part, ensuring that issues are identified and addressed proactively. Using Phoenix Security’s scorecard, organizations can create a common language between the security, development, and business teams, ensuring everyone is aligned and focused on achieving the same goals.
Finally, Phoenix Security’s ability to create risk-based profiles can help organizations translate their security goals into dynamic and smart targets for engineers. By using risk-based profiles, engineers can prioritize their work and focus on the most critical issues, ensuring that they make the most effective use of their time and resources.
Overall, by leveraging Phoenix Security’s powerful capabilities, organizations can implement a smart, risk-based approach to software development that ensures the success of their initiatives while minimizing risk and improving overall efficiency. With Phoenix Security as their partner, organizations can feel confident that they are taking a proactive approach to software development that is aligned with their business objectives and goals.








![Phoenix Security infographic: Claude Code Critical Vulnerability — CI/CD Nightmare, 3 Command Injection Flaws. Dark navy and orange background with circuit-board pattern. Center: terminal window showing attack chain [config] | [shell] | [exfil] with three red arrows pointing to attack targets — CI/CD Pipeline Compromise (top right), Cloud Key Exfiltration via AWS (middle right), and Developer Workstation Compromise leading to Server-to-Server lateral movement (bottom right). Phoenix Security logo at top. Bottom text: "CLAUDE CODE / CRITICAL VULNERABILITY / CI/CD NIGHTMARE / 3 COMMAND INJECTION FLAWS / Credential Exfiltration · CWE-78 · Confirmed / Shell Injection in CLI, Editor, and Auth Helpers."](https://phoenix.security/media/Gemini_Generated_Image_abcn46abcn46abcn.jpeg)








