Innocuous libraries can pose a significant threat. it’s crucial to keep an eye on potential threats. One such recent threat is the libcue CVE-2023-43641 vulnerability, which has put GNOME Linux systems, including Ubuntu, at risk of Remote Code Execution (RCE).
This flaw, tracked as CVE-2023-43641 with a CVSS score of 8.8, allows for once-click Remote Code Execution (RCE) on affected systems. In this blog post, we’ll delve into the details of this vulnerability, its implications, and what you need to know to stay protected.
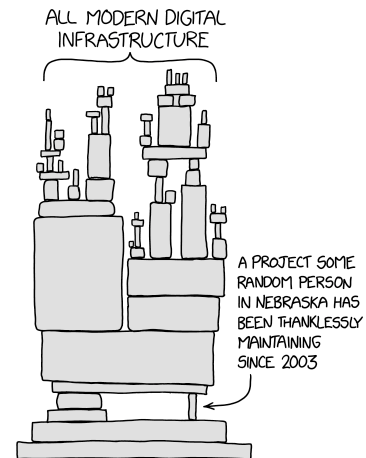
One of my favourite memes, the world relies on a few tiny libraries
Who’s Involved? in disclosing libcue CVE-2023-43641
The GitHub Security Lab, in coordination with Ilya Lipnitskiy, the maintainer of libcue, and the distros mailing list, has disclosed this vulnerability. A text-only version of the disclosure was also sent to the oss-security list.
Systems affected by libcue2 CVE-2023-43641
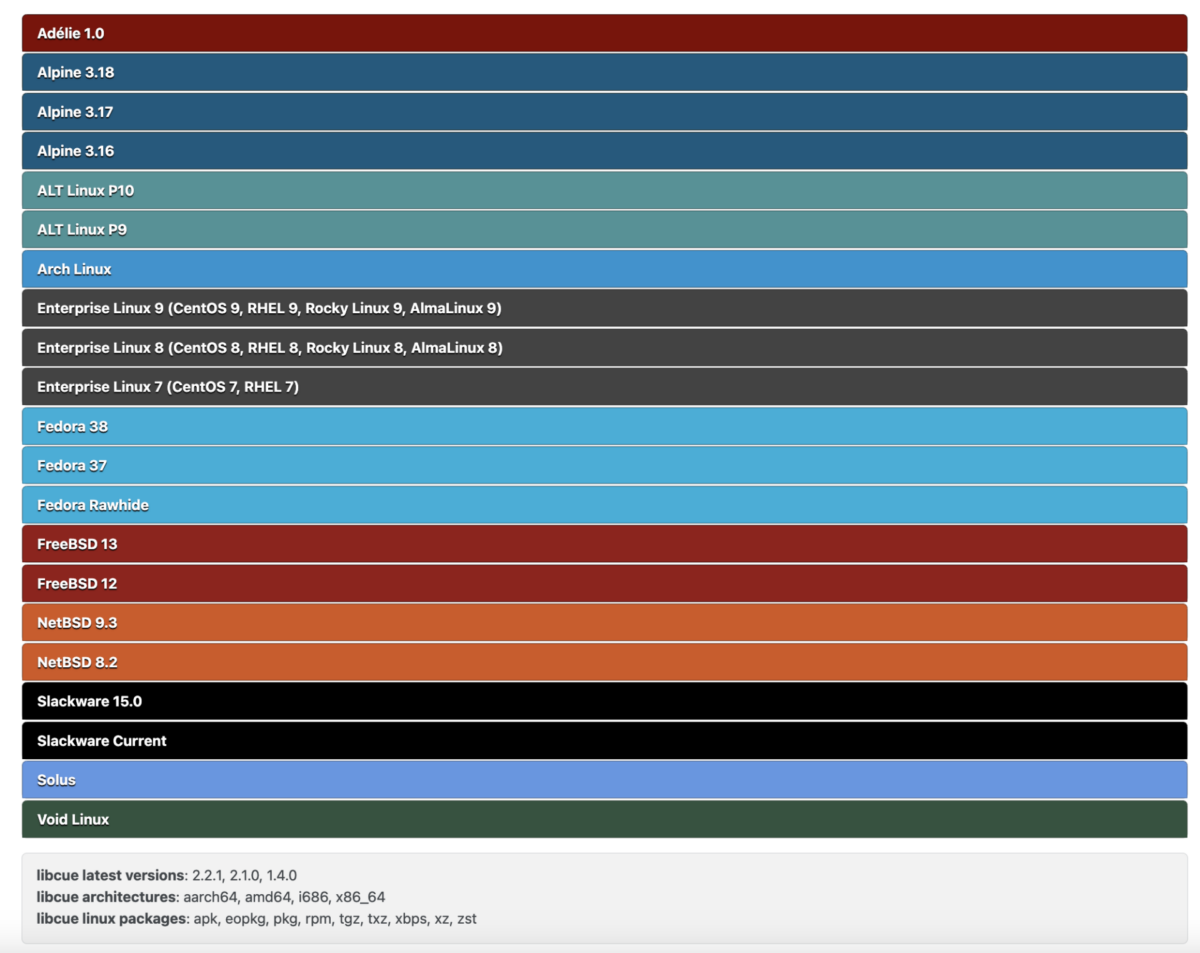
The following systems are affected by this vulnerability, for an updated list:
- Ubuntu Versions:
- Ubuntu 23.04: libcue2 – 2.2.1-4ubuntu0.1
- Ubuntu 22.04: libcue2 – 2.2.1-3ubuntu0.1
- Ubuntu 20.04: libcue2 – 2.2.1-2ubuntu0.1
- Other Systems:
- Adélie 1.0
- Alpine 3.18, 3.17, 3.16
- ALT Linux P10, P9
- Arch Linux
- Enterprise Linux 9 (CentOS 9, RHEL 9, Rocky Linux 9, AlmaLinux 9)
- Enterprise Linux 8 (CentOS 8, RHEL 8, Rocky Linux 8, AlmaLinux 8)
- Enterprise Linux 7 (CentOS 7, RHEL 7)
- Fedora 38, 37, Rawhide
- FreeBSD 13, 12
- NetBSD 9.3, 8.2
- Slackware 15.0, Current
- Solus
- Void Linux
libcue Latest Versions: 2.2.1, 2.1.0, 1.4.0
libcue Architectures: aarch64, amd64, i686, x86_64
libcue Linux Packages: apk, eopkg, pkg, rpm, tgz, txz, xbps, xz, zst
What Does libcue Do and how CVE-2023-43641 affects?
libcue is a library designed for parsing cue sheets, which are metadata formats for describing CD tracks. It is a dependency for some audio players like Audacious and is incorporated into Tracker Miners, a search engine tool in GNOME.
How Does the CVE-2023-43641 Exploit Work?
The vulnerability arises from an out-of-bounds array access in the track_set_index function. An attacker can exploit this by tricking a user into clicking a malicious link and downloading a .cue file. The file is then automatically scanned by Tracker Miners, which uses libcue to parse it, leading to code execution.
How Remote Code Execution Occurs
The vulnerability is in the handling of the INDEX syntax in cue sheets. The bug is due to the use of atoi for scanning integers, which doesn’t check for integer overflow, and a lack of boundary checks in track_set_index. A patch has been proposed to fix this issue.
Vulnerability Exploitation Details & POC
CTI – 3.1
EPSS – Not available
Exploit – PoC not widely Available
Affected Systems: Spotlight on Ubuntu
Among the systems impacted by this libcue vulnerability are various versions of Ubuntu:
- Ubuntu 23.04: libcue2 – 2.2.1-4ubuntu0.1
- Ubuntu 22.04: libcue2 – 2.2.1-3ubuntu0.1
- Ubuntu 20.04: libcue2 – 2.2.1-2ubuntu0.1
Tracker Miners’ Role
Tracker Miners is not directly vulnerable but magnifies the impact of this bug. It consists of two processes: tracker-miner-fs and tracker-extract. The vulnerability only affects tracker-extract, which is where libcue is used. Both processes run as the current user, so chaining this vulnerability with a separate privilege escalation bug would be necessary for admin access.
For additional details check the Github Exploitation disclosure
Exploitation Challenges
The exploit had to bypass ASLR and a seccomp sandbox in tracker-extract. The sandbox has since been strengthened to prevent this exploitation path in the future.
Vulnerability Management and Application Security Measures
In the context of vulnerability management and application security, it’s essential to update your GNOME Linux systems and particularly libcue to the latest versions. This will mitigate the risk of Remote Code Execution.
What’s Being Done to fix CVE-2023-43641?
The full Proof of Concept (PoC) is being delayed to give users time to install updates. However, the vulnerability has been tested on Ubuntu 23.04 and Fedora 38, and it’s believed that all GNOME-running distributions are potentially exploitable.
Credit Github and video for exploit PoC
Final Thoughts
As the saying goes, “The devil is in the details,” and this vulnerability proves just that. What seemed like a small library issue turned into a one-click RCE due to its integration with Tracker Miners. So, if you’re using GNOME, don’t wait for a ‘cue’ to update—do it now, or you might find yourself calculating the risks later (literally, with a popped-up calculator).
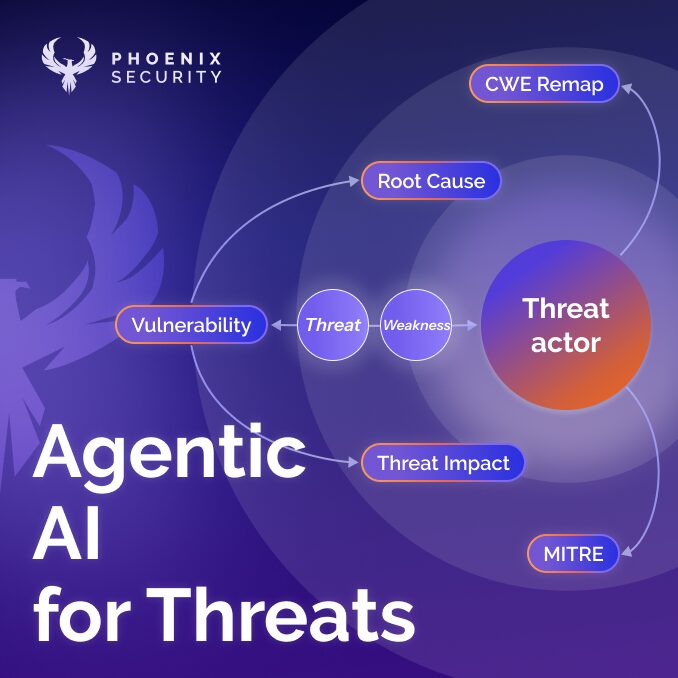
How Phoenix Security Can Help Identify libcue Vulnerabilities in Your Products
Phoenix Security serves as a beacon for security professionals aiming to pinpoint the libcue2 vulnerability within their systems. It meticulously scans through your product, identifying instances where the libcurl vulnerability may be installed or nested within libraries. By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains unassailable against the libcue vulnerability.