Security teams often grapple with prioritizing patches when facing thousands of open vulnerabilities. A threat-centric approach offers a focused lens on adversarial goals and associated exploitation methods. The data below illustrates how certain weaknesses align with ransomware, zero-day exploits, and broader cybercrime campaigns.
Patterns in Known Exploited Vulnerabilities and Remote Code Execution
CISA’s Known Exploited Vulnerabilities (KEV) list reveals a disproportionate number of Remote Code Execution (RCE) flaws. Within some data subsets, RCE exceeds 50% of tracked exploits (CISA KEV reference). Wider studies from Phoenix Security indicate a similar weighting, with RCE at 52% frequency in a broad sample.
Threat actors such as Clop, Conti, and RansomHub often adopt RCE as a direct entry for malware delivery. Clop demonstrates a 21% utilization rate of RCE in campaigns, followed by Conti at 10% and RansomHub at 9%. Those numbers highlight why system administrators and security engineers treat RCE-related alerts as major red flags.
Key points that elevate RCE flaws in priority lists:
• Public availability of exploit code
• Compatibility with automation in attacker toolkits
• Potential for swift escalation into full control of system resources
Additional guidance on exploitability concepts is provided by Phoenix Security’s overview of the topic.
The information in this article is also available in greater detail in the eBook – A threat-centric approach on vulnerabilities.
Download the eBook on LLM Application for a Threat-Centric Approach on Vulnerabilities
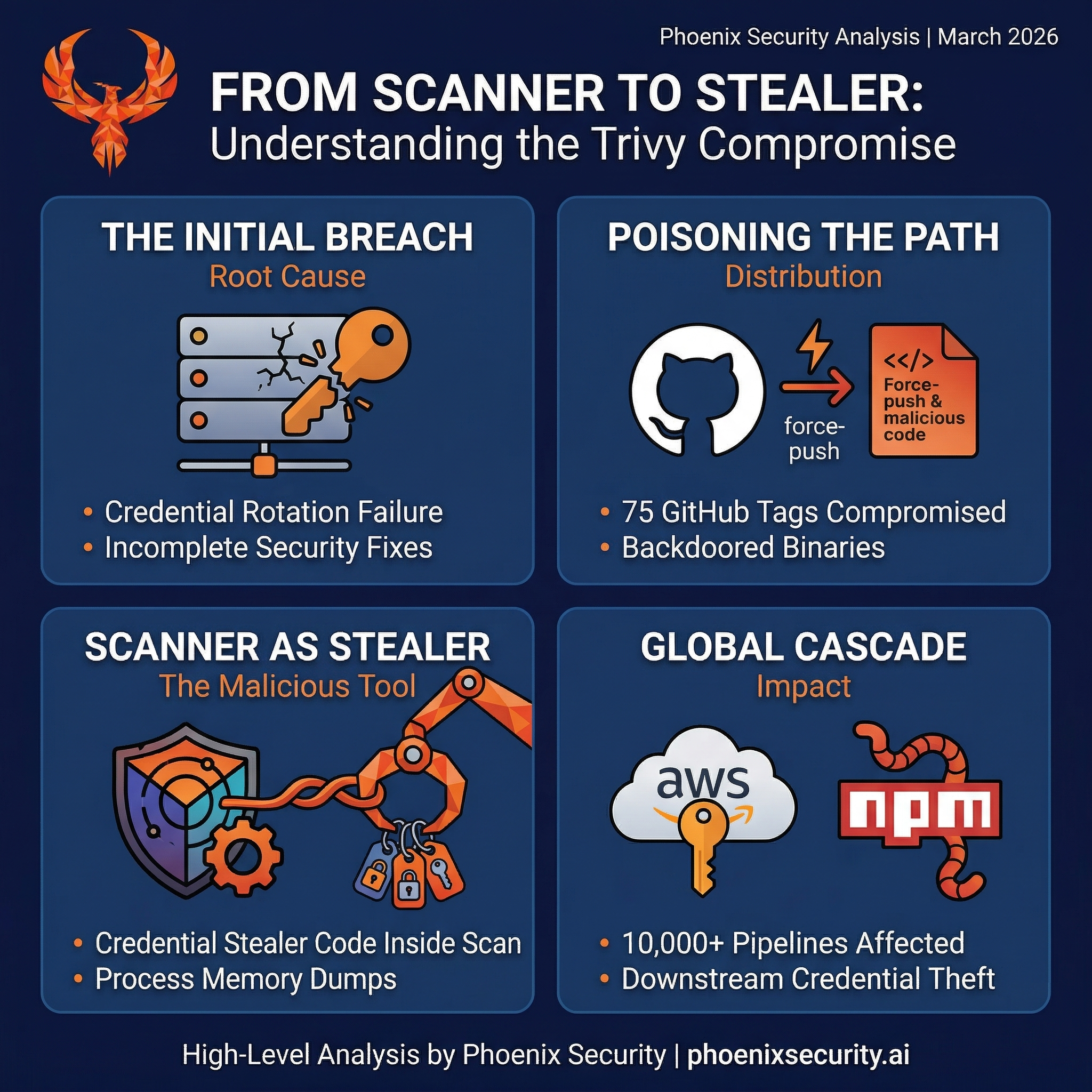
Root Causes and Their Connection to Ransomware
Ransomware groups aim for initial compromise followed by lateral movement and data encryption. Memory corruption, buffer overflows, and input validation errors frequently provide the entry path. Impact analyses place memory corruption at over 30% in some datasets, with more than 4,200 CVEs exploited in the wild. RCE pairs with those weaknesses to create an ideal pivot for malicious code deployment.
References to memory corruption issues appear extensively in zero-day disclosures from 2021 through 2024. Verified exploit collections underscore this pattern, showing thousands of memory-related flaws leveraged by attackers.
Frequent categories in ransomware campaigns:
• Input validation failures leading to injection
• Code execution paths combined with privilege escalation
• Sensitive information disclosure aiding data exfiltration
High-impact examples of memory corruption and RCE serve as templates for exploitation. A deeper look at Common Weakness Enumerations (CWE) underscores how these categories remain top-tier concerns every year.
Indicators of Likely Exploitation
Several signals mark a vulnerability as high risk:
1. Verified Exploit
Public proof-of-concept scripts or private exploit kits frequently accelerate attacks. Records with a “verified exploit” tag often jump to the top of patch lists.
2. Alignment with CWE Top 25
Memory safety issues (CWE-787, CWE-125, CWE-416), improper input validation (CWE-20), and privilege mismanagement (CWE-269) remain focal points in official rankings. Attackers routinely adopt ready-made methods to exploit these weaknesses.
3. Prevalence Among High-Profile Threat Actors
RCE and privilege escalation appear systematically in campaigns tied to major ransomware groups (Clop, BlackCat, AvosLocker, and others).
4. Correlation with Zero-Day Trends
Zero-day tracking indicates persistent prioritization of RCE and memory corruption. Records from 2023 show over 1,900 remote code execution instances in that single year.
A structured method for assessing vulnerability impact and prioritization is outlined in the Phoenix Security 4D Risk Formula. That approach blends severity scoring with real-time threat intelligence.

Ransomware Emphasis
Data from the Phoenix Security platform indicates that ransomware operators often find success with vulnerabilities tied to remote code paths, memory issues, and privilege escalation. Many high-profile ransomware notes reference RCE exploits in their initial compromise. Clop’s repeated exploitation of RCE for data theft and encryption shows how quickly adversaries transform theoretical weaknesses into monetized intrusions.
Input validation flaws (including directory traversal and command injection) rank high in ransomware usage, especially when combined with lateral movement and domain privilege attacks. Recent CISA KEV advisories reference vulnerabilities in Microsoft Exchange, VMware Workspace ONE, and other enterprise platforms that demonstrate these exact traits. Each advisory notes that ransomware groups can pivot from an unpatched RCE or memory corruption gap into comprehensive environment lockdown.
Zero-Day Activity
Historical zero-day exploit data from 2021–2024 confirms that remote code execution and memory corruption remain staples for advanced intrusion. Annual tallies consistently list these categories far above others. A sampling of the most frequently observed zero-days in 2023 shows nearly 1,900 RCE-related entries and approximately the same count for memory corruption. Out-of-bounds writes, privilege escalation, and deserialization issues also make frequent appearances.
Security professionals often consult the EPSS methodology to evaluate how likely a given vulnerability is to be exploited. This predictive model, combined with direct threat intelligence, points repeatedly to memory-corrupting RCE as prime candidates for global attacks.
Closing Thoughts on Threat-Centric Prioritization
A threat-centric view benefits security teams aiming to neutralize the tactics that attackers use most frequently. Patterns in both legacy and emerging data reveal that adversaries favor RCE, privilege escalation, and memory corruption. Input validation and directory traversal remain core pivot points, often opening the door to code injection and deeper infiltration.
Persistent ransomware campaigns reinforce those insights, highlighting how quickly unpatched memory vulnerabilities and unprotected RCE endpoints convert into revenue for criminal enterprises. Adapting a risk-based strategy that references real-world exploit prevalence delivers a more accurate roadmap for vulnerability remediation. Deeper research into exploitability markers can be found in the official Phoenix Security Exploitability Resources.
Technical teams seeking a more quantitative approach may evaluate each vulnerability against the Phoenix Security 4D Risk Formula. That blueprint integrates severity scoring, asset context, business impact, and external threat data to rank vulnerabilities by their likelihood of exploitation and organizational consequence.
References and Further Reading
• CISA Known Exploited Vulnerabilities (KEV)
• Phoenix Security EPSS v4 Overview
• Phoenix Security Exploitability Primer
• Phoenix Security CWE Overview
• Phoenix Security 4D Risk Formula
Analysts monitoring current attack patterns can find recurring evidence of memory corruption, RCE, and privilege escalation as focal points in ransomware exploits. This data-driven perspective supports targeted patch management, better intrusion detection, and more effective incident response.
How Phoenix Security Can Help

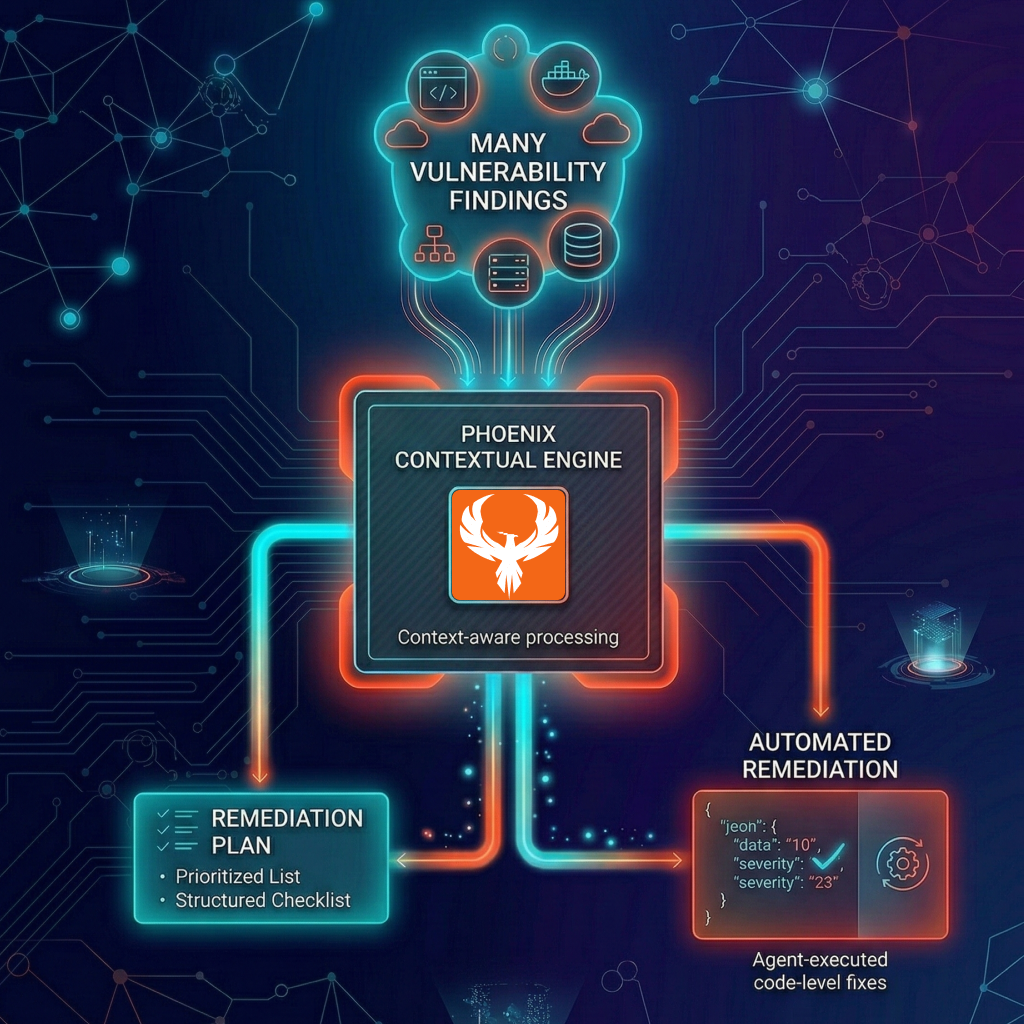
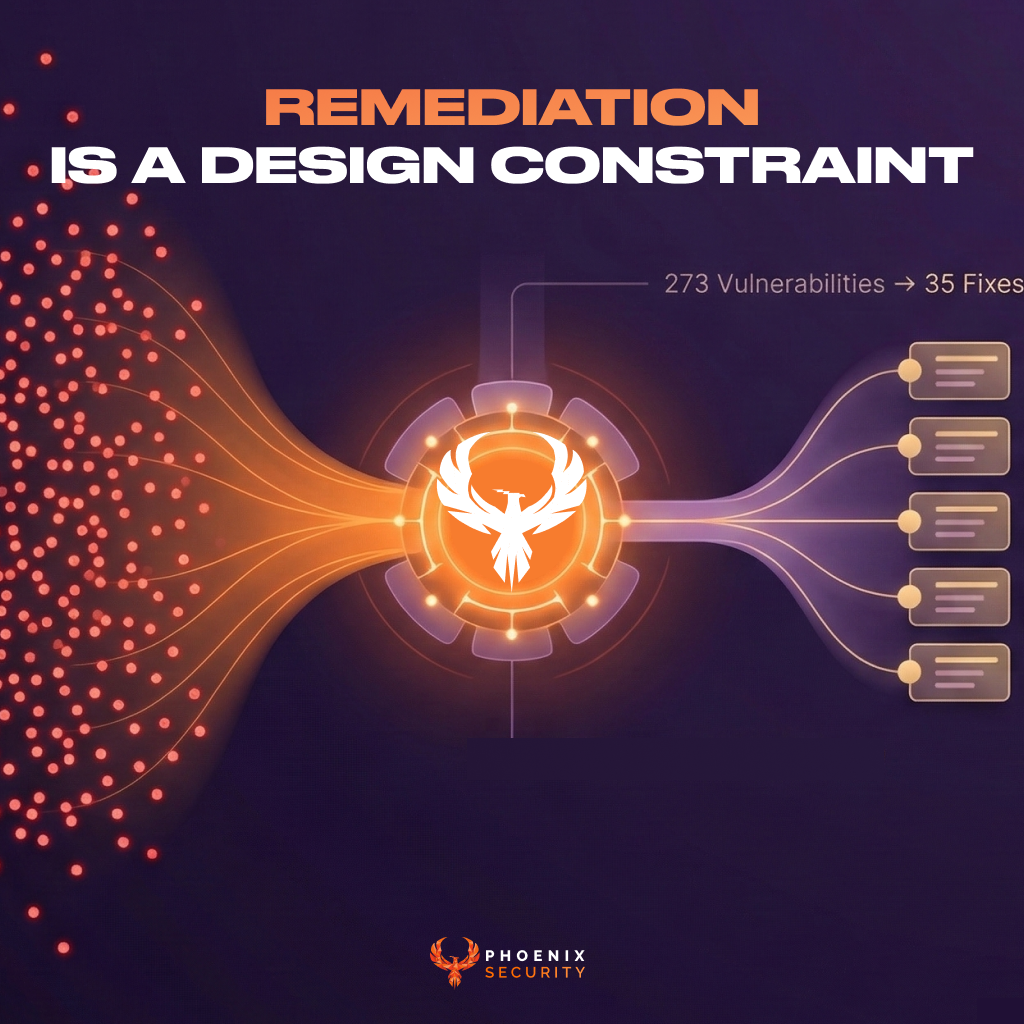
Organizations often face an overwhelming volume of security alerts, including false positives and duplicate vulnerabilities, which can distract from real threats. Traditional tools may overwhelm engineers with lengthy, misaligned lists that fail to reflect business objectives or the risk tolerance of product owners.

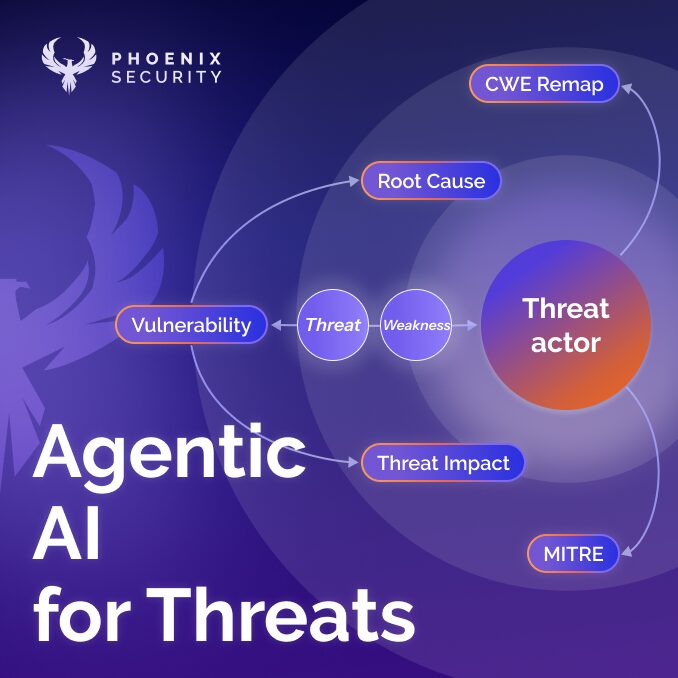
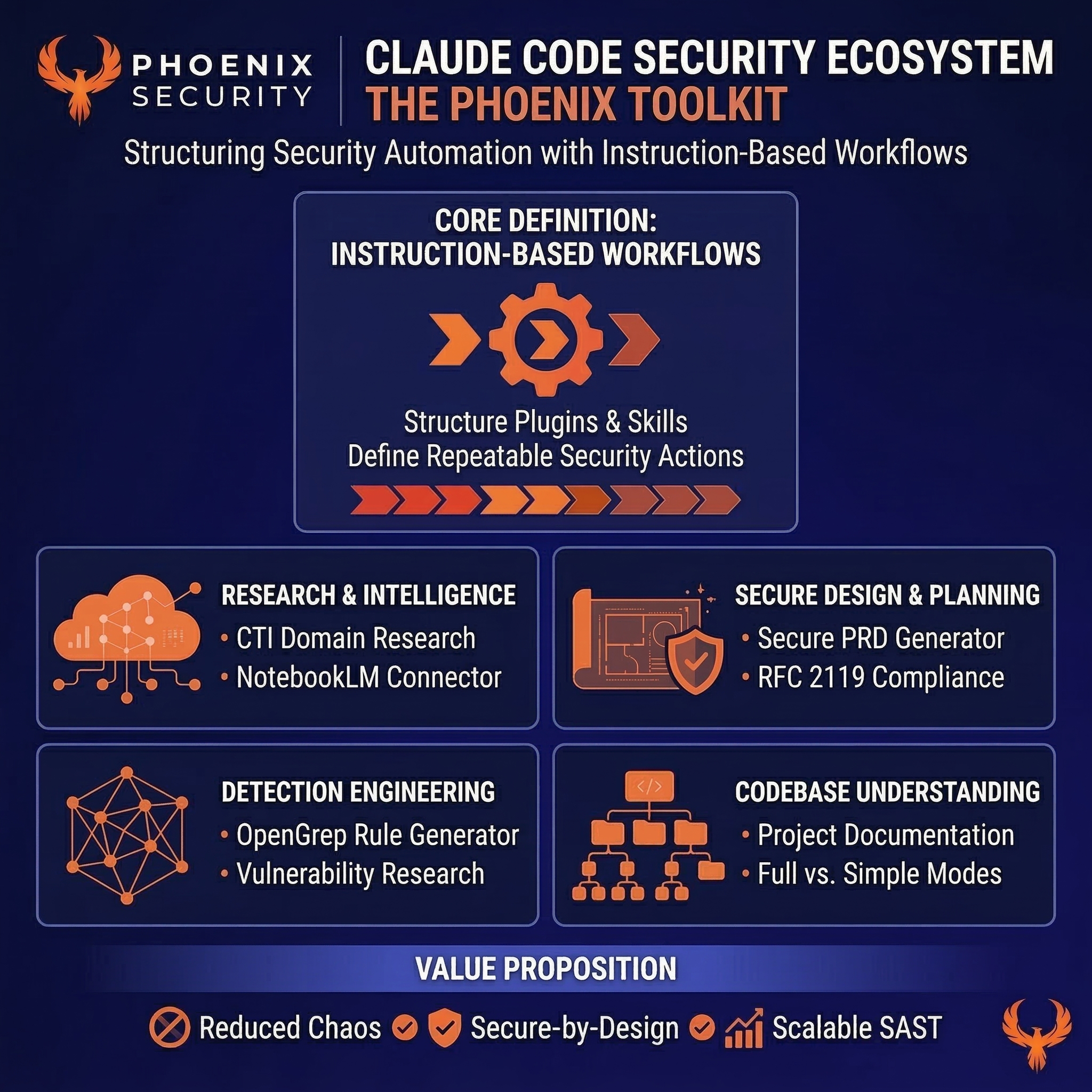
Phoenix Security offers a transformative solution through its Actionable Application Security Posture Management (ASPM), powered by AI-based Contextual Quantitative analysis and an innovative Threat Centric approach. This innovative approach correlates runtime data with code analysis and leverages the threats that are more likely to lead to zero day attacks and ransomware to deliver a single, prioritized list of vulnerabilities. This list is tailored to the specific needs of engineering teams and aligns with executive goals, reducing noise and focusing efforts on the most critical issues. Why do people talk about Phoenix

• Automated Triage: Phoenix streamlines the triage process using a customizable 4D risk formula, ensuring critical vulnerabilities are addressed promptly by the right teams.
• Contextual Deduplication: Utilizing canary token-based traceability, Phoenix accurately deduplicates and tracks vulnerabilities within application code and deployment environments, allowing teams to concentrate on genuine threats.
• Actionable Threat Intelligence: Phoenix provides real-time insights into vulnerability’ exploitability, combining runtime threat intelligence with application security data for precise risk mitigation.

By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.