- 17th October 2023
Is Curl and Libcurl Vulnerability Critical? Read the article for more details.
The Curl and libcurl project has recently rattled the industry with a high-severity vulnerability labeled as CVE-2023-38545. This blog post offers a deep dive into the intricate details of this potentially catastrophic flaw, which has the capability to trigger a heap overflow condition and compromise countless systems globally.
Going beyond the surface, we delve into the background and complexity of the attack vector. The vulnerability roots itself in libcurl’s support for the SOCKS5 proxy protocol. It’s not just a flaw—it’s a ticking time bomb if not addressed immediately. The article unpacks the technicalities involved in exploiting this vulnerability, making it a must-read for both security professionals and system administrators.
We don’t just stop at identifying the problem; we offer solutions. Starting from the urgency of releasing a security patch to recommendations for immediate action, this article serves as a comprehensive guide for risk mitigation. Furthermore, we take a retrospective look at Curl vulnerabilities over the years, offering a broader perspective on the evolving trends in security flaws.
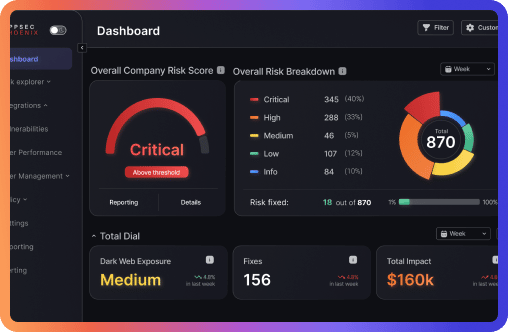
But what sets this article apart is its focus on how Phoenix Security can be your safeguard against such vulnerabilities. With our state-of-the-art Vulnerability Management and Asset Management tools, we guide organizations in quickly identifying and acting upon threats, ensuring an impregnable defense against vulnerabilities like CVE-2023-38545.
Whether you’re a cybersecurity veteran or a concerned user, this article is your roadmap to understanding, mitigating, and ultimately defeating CVE-2023-38545. Don’t let your guard down; read on to fortify your systems against this formidable security flaw.
Francesco Cipollone