Weekly review of the top vulnerability issues of the week: This week Focus on PWN 2 OWN in Vancuver
This week we hear from Pwn2OWN – Trend Micro, ZDI, Tesla and more bugs found for a total of 1,155,000 Awarded
This week features Apple IoS & Remediation, QNAP, Windows, Firefox, Ubuntu & Tesla explits at Pwn2OWN, PyPI
PWN 2 OWN Summary with all the vulnerabilities Discovered
Microsoft Teams
Hector “p3rr0” Peralta was able to demonstrate an improper configuration against Microsoft Teams. He earns $150,000 and 15 Master of Pwn points.
Daniel Lim Wee Soong (@daniellimws), Poh Jia Hao (@Chocologicall), Li Jiantao (@CurseRed) & Ngo Wei Lin (@Creastery) of STAR Labs successfully demonstrated their zero-click exploit of 2 bugs (injection and arbitrary file write) on Microsoft Teams.
Mozilla Firefox

Manfred Paul (@_manfp) successfully demonstrated 2 bugs – prototype pollution and improper input validation – on Mozilla Firefox
Advisory: https://www.mozilla.org/en-US/security/
Special – Tesla

For the Full video: https://www.youtube.com/watch?v=K5i0rQNYRNI
David BERARD and Vincent DEHORS from @Synacktiv exploited 2 unique bugs (Double-Free & OOBW) with a collision on a known sandbox escape on a Telsa Model 3 Infotainment System
For full: https://www.zerodayinitiative.com/blog/2022/5/18/pwn2own-vancouver-2022-the-results
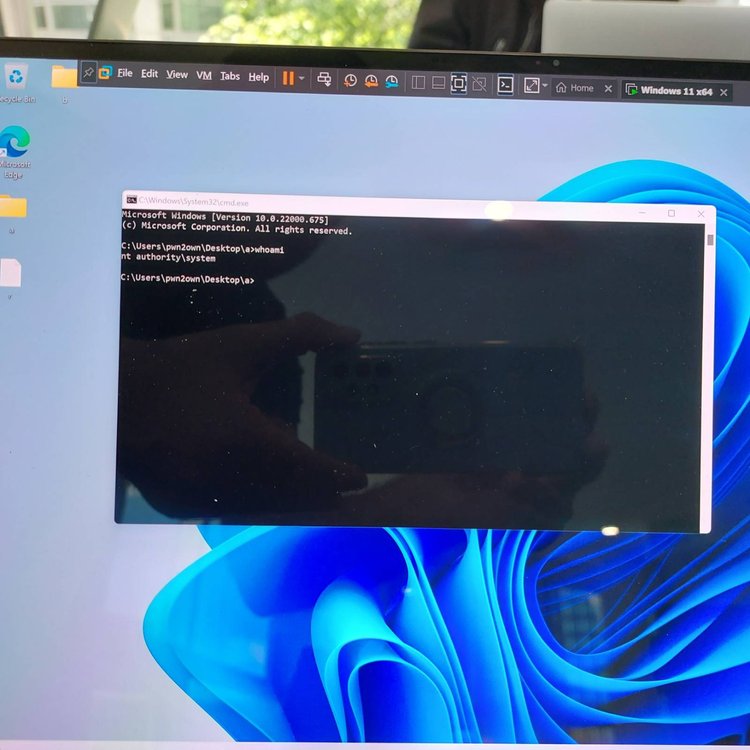
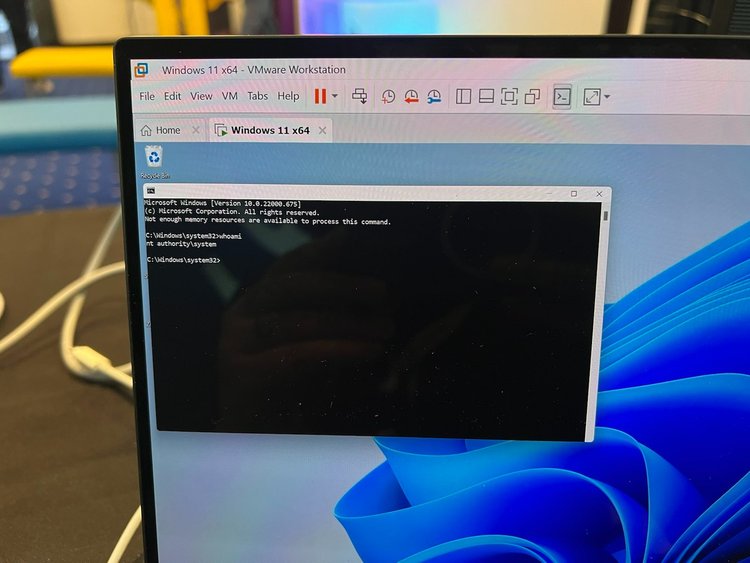
Windows
nghiadt12 from Viettel Cyber Security was able to successfully show an escalation of privilege via Integer Overflow on Microsoft Windows 11
vinhthp1712 successfully achieved Elevation of Privilege via Improper Access Control on Microsoft Windows 11
Bruno PUJOS (@brunopujos) from REverse Tactics successfully achieved Elevation of Privilege via Use-After-Free on Microsoft Windows 11
Ubuntu
Bien Pham (@bienpnn) was able to execute a Use After Free bug leading to elevation of privilege on Unbuntu Desktop
Appsec
PyPI – Library pymafka Expose data via open backdoor
A malicious library pymafka has been released on PyPI with the intent to exfiltrate data
PyKafka is a widely used Apache Kafka client that counts over four million downloads on the PyPI registry.
The library implemented the attack known as typosquatting where users mistake the library capital for lowercase
The library was fortunately promptly removed, nonetheless there are 325 users who downloaded the library
the infection begins with the execution of the ‘setup.py’ script found in the package.
This script detects the host operating system and, depending on whether it is Windows, Linux, or Darwin (macOS), fetches a compatible malicious payload that is executed on the system.
For Linux systems, the Python script connects to a remote URL at 39.107.154.72 and pipes the output to the bash shell. Unfortunately, that host is down at the time of this writing, so it is unclear what commands are executed, but it is believed to open a reverse shell.
For Windows and macOS, the payload is a Cobalt Strike beacon, which provides remote access to the infected device.
Cobalt Strike is a widely abused penetration testing suite that features powerful traits such as command execution, keylogging, file actions, SOCKS proxying, privilege escalation, credential stealing, port scanning, and more.
More info https://blog.sonatype.com/new-pymafka-malicious-package-drops-cobalt-strike-on-macos-windows-linux
To avoid similar attacks always check if the package has description and is from a reputable author as well as checking for typos
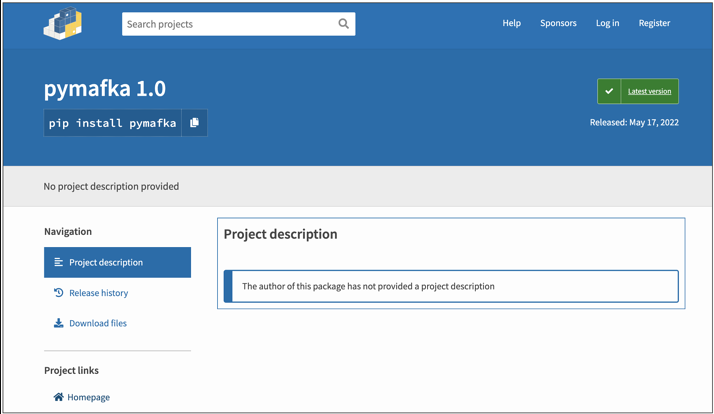
Software developers should scrutinize package names and details and double-check their selection of building blocks when something appears funky.
INFRA/Network
IOS – Remote Execution of malware via Bluetooth

Security researchers were able to exploit successfully vulnerability in the Bluetooth, NFC, and ultra-wideband (UWB) that are all hardwired to the phone’s secure element. The researchers were able to write to the Bluetooth chip in an iPhone 13 by exploiting a legacy feature that requires iOS to be able to write to the executable RAM regions using a vendor-specific host-controller interface (HCI) command.
Workaround: disable the Find My network as a device policy this can be implemented as policy for your workforce with iPhones running iOS 15
Follow Apple Security Advisory: https://support.apple.com/en-gb/HT201222
Previous Vulnerability Covered here: https://phoenix.security/security-vulnerability-of-the-week-16-05-22/ has not been fixed: https://support.apple.com/en-gb/HT213258
QNAP
QNAP has warned of a new series of attack bots to the vulnerabilities recently fixed
“a new wave of DeadBolt ransomware attacks. Please install the latest updates”
CVE-2022-23121 and others were discovered by NCC Group EDG team at Pwn2Own
We covered the Qnap Vulnerability: https://phoenix.security/security-vulnerability-of-the-week-16-05-22/ and https://phoenix.security/security-vulnerability-of-the-week-09-05-22/
More details: https://www.qnap.com/en-uk/securitydvisories
Affected Versions
- QTS 5.0.x and later
- QTS 4.5.4 and later
- QTS 4.3.6 and later
- QTS 4.3.4 and later
- QTS 4.3.3 and later
- QTS 4.2.6 and later
- QuTS hero h5.0.x and later
- QuTS hero h4.5.4 and later
- QuTScloud c5.0.x
Cloud
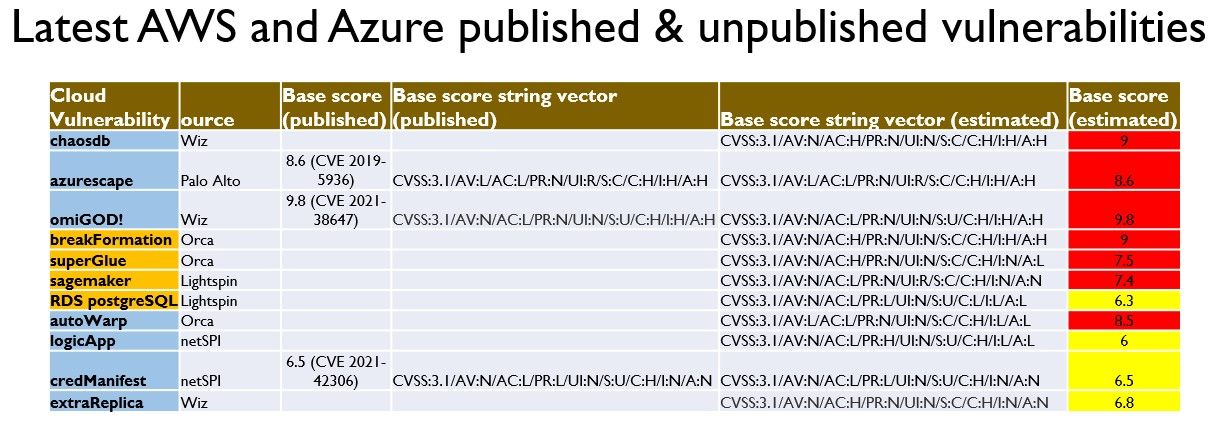
Current Year Research on Vulnerabilities Discovered
For the Deep dive on previous Cloud Vulnerabilities: https://phoenix.security/security-vulnerability-of-the-week-02-04-22/
Here https://phoenix.security/security-vulnerability-of-the-week-09-05-22/
and here https://phoenix.security/security-vulnerability-of-the-week-16-05-22/
AutoWrap Vulnerability in Microsoft Azure Automation Service – Orca – CVSS 8.5
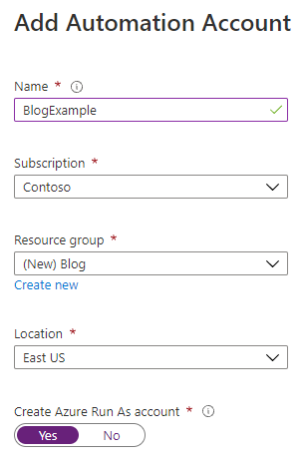
What Is the Microsoft Azure Automation Service?
Microsoft Azure Automation allows customers to execute automation code in a managed fashion. You can schedule jobs, provide input and output, and more. Each customer’s automation code runs inside a sandbox, isolated from other customers’ code executing on the same virtual machine.
The vulnerability was discovered by the orca team on December 2021 and Public disclosure to Microsoft on March 07 2022
You have been exposed to the vulnerability if
- You have been using the Azure Automation service
- The Managed Identity feature in your automation account is enabled (which is enabled by default)
AutoWarp is a critical vulnerability in the Azure Automation service that allowed unauthorized access
Microsoft Has responded to the incident here: https://msrc-blog.microsoft.com/2022/03/07/13943/
Microsoft has also issued Automation customers to follow Security best practices outlined here.
For full detail of the vulnerability: https://orca.security/resources/blog/autowarp-microsoft-azure-automation-service-vulnerability/
logicApp – NetSPI – CVSS 6
Vulnerability CVE-2021-42306 (CredManifest) reported to Microsoft on Nov 17 2021
The vulnerability Is triggered when running an account in azure with automation. the vulnerability can be triggered by running an Automation Account with a “Run as” account
Microsoft has issued guidance https://msrc-blog.microsoft.com/2021/11/17/guidance-for-azure-active-directory-ad-keycredential-property-information-disclosure-in-application-and-service-principal-apis/
For the disclosure: https://www.netspi.com/blog/technical/cloud-penetration-testing/azure-cloud-vulnerability-credmanifest/
credManifest – NetSPI – CVSS 6.5 – CVE 2021-42306
extraReplica – Wiz – CVSS 6.8
Bonus
Conti Ransomware group closes and split in more independent units
New from Advanced Intel’s Yelisey Boguslavskiy, who tweeted this afternoon that the gang’s internal infrastructure was turned off.
Conti Has been recently at war with Costa Rica
Advanced Intel report explains that Conti has partnered with numerous well-known ransomware operations, including HelloKitty, AvosLocker, Hive, BlackCat, BlackByte, and more.
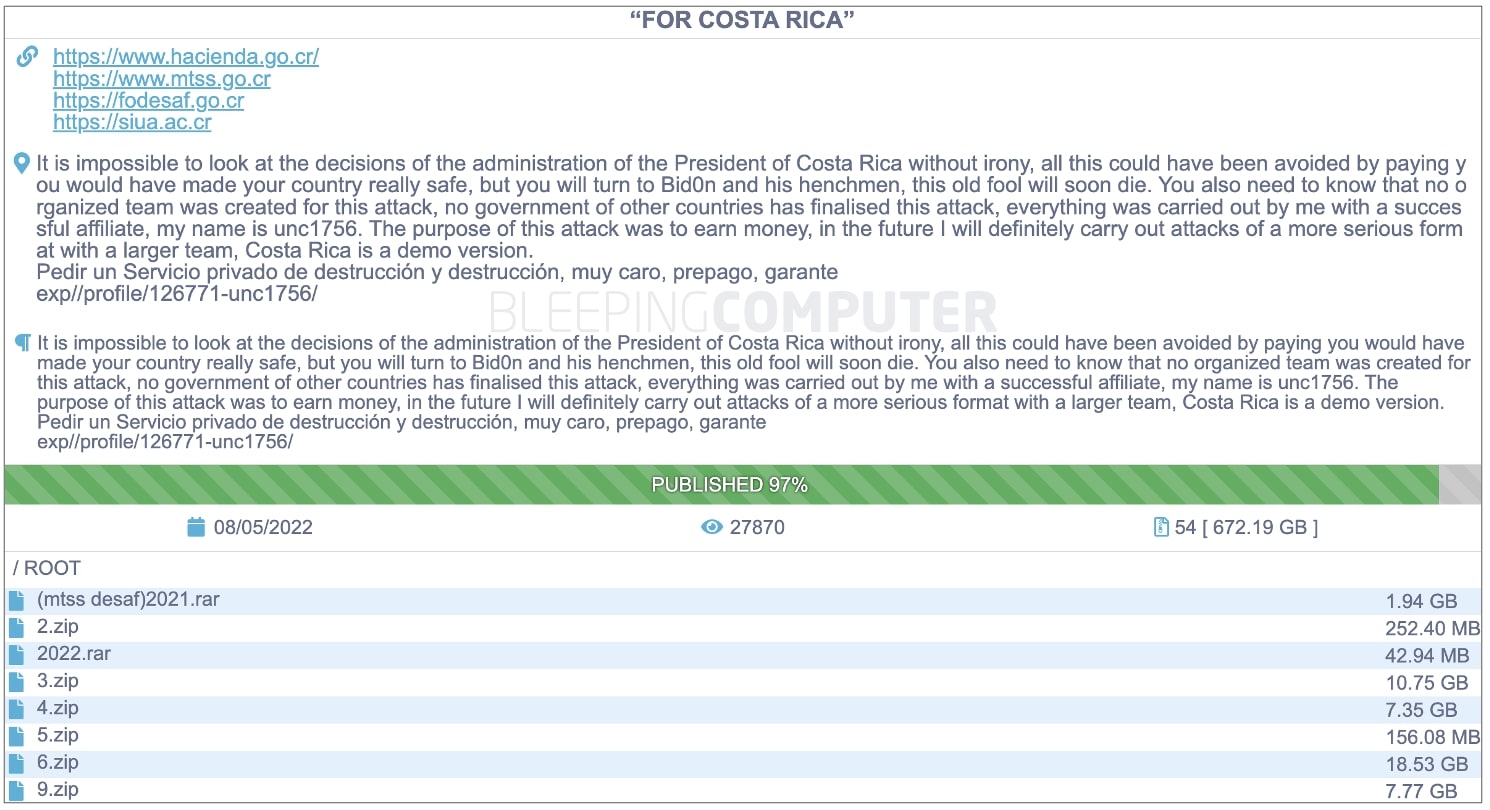
Snapshot of costa rica attack:
On Sunday, May 8th, the newly elected Costa Rican President Chaves declared a national emergency citing ongoing Conti ransomware attacks as the reason.
Conti’s data leak site had been updated to state that the group had leaked 97% of the 672 GB data dump allegedly containing information stolen from government agencies: