This second week we focus on Application security and Mostly on cloud security vulnerabilities being disclosed throughout the year

This week’s Features: Jet Brain Toolkit, Oracle Mysql, Zoom, Cloud security vulnerabilities
—-
Appsec
Jet Brain: IntelliJ IDEA, PyCharm …
- CVE-2022-29813 Risk still to be assessed – affecting – IntelliJ IDEA before 2022.1
- TeamCity – High – Credential Disclosure – (No CVE, CWE – 522 )
Patch Fixes: https://www.jetbrains.com/privacy-security/issues-fixed/
Oracle

- CVE-2022-21490 – CVSS 9.8 – High – Oracle MySQL Cluster Data Node Buffer Overflow Remote Code Execution Vulnerability
- CVE-2022-21489 – CVSS 9.8 – High- Oracle MySQL Cluster Data Node Integer Overflow Remote Code Execution Vulnerability
- CVE-2022-21482 – CVSS 9.8 – High – Oracle MySQL Cluster Data Node Integer Overflow Remote Code Execution Vulnerability
- CVE-2022-21486 – CVSS 6.5 – Medium – Oracle MySQL Cluster Data Node Improper Validation of Array Index Information Disclosure Vulnerability
- CVE-2022-21483 – CVSS 9.8 – High – Oracle MySQL Cluster Data Node Improper Validation of Array Index Remote Code Execution Vulnerability
Affected products:
Link to the Advisory https://www.oracle.com/securitylerts/cpuapr2022.html
Zoom
Some of the zoom video controllers on-prem got vulnerabilities –
- CVE-2021-34414 vulnerability (which obtained a CVSS 3.1 score of 7.2
- CVE-2021-34415, with a CVSS 3.0 score of 7.5
The patch is available for all the CVEs
Affected devices
- Meeting Connector Controller up to version 4.6.348.20201217
- Meeting Connector MMR up to version 4.6.348.20201217
- Recording Connector up to version 3.8.42.20200905
- Virtual Room Connector up to version 4.4.6620.20201110
- Virtual Room Connector Load Balancer prior to version 2.5.5495.20210326.
Minor vulnerability – CVE-2021-34416 with a CVSS 3.0 score of 5.5
Egor Dimitrenko discovery affected the following:
- Meeting Connector up to version 4.6.360.20210325
- Meeting Connector MMR up to version 4.6.360.20210325
- Recording Connector up to version 3.8.44.20210326
- Virtual Room Connector up to version 4.4.6752.20210326
- Virtual Room Connector Load Balancer up to version 2.5.5495.20210326
Github
This is more of a breach due to stolen oauth 2 tokens. Github private repo are not affected
Since this campaign was first spotted on April 12, 2022, the threat actor has already accessed and stolen data from dozens of victim organizations using Heroku and Travis-CI-maintained OAuth apps, including npm.
As per bleeping computer article GitHub disclosed the breach on the evening of April 15th, three days after discovering the attack, when the malicious actor accessed GitHub’s npm production infrastructure.
“The applications maintained by these integrators were used by GitHub users, including GitHub itself,” revealed today Mike Hanley, Chief Security Officer (CSO) at GitHub.
Impacted Applications:
According to Hanley the list of impacted OAuth applications includes:
- Heroku Dashboard (ID: 145909)
- Heroku Dashboard (ID: 628778)
- Heroku Dashboard – Preview (ID: 313468)
- Heroku Dashboard – Classic (ID: 363831)
- Travis CI (ID: 9216)
Github has shared the following guidance:
GitHub shared the following guidance with potentially impacted customers to help them investigate logs for evidence of data exfiltration or malicious activity:
- Review all your private repositories for secrets or credentials stored in them. There are several tools that can help with this task, such as GitHub secret scanning and trufflehog.
- Review the OAuth applications that you’ve authorized for your personal account or that are authorized to access your organization and remove anything that’s no longer needed.
- Follow GitHub’s guidelines for hardening the security posture of your GitHub organization.
- Review your account activity, personal access tokens, OAuth apps, and SSH keys for any activity or changes that may have come from the attacker.
- Additional questions should be directed to GitHub Support.
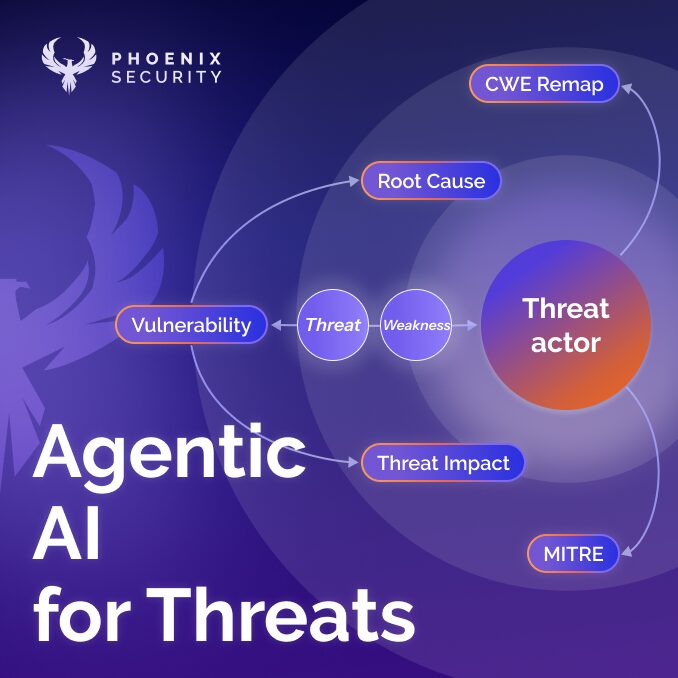
Cloud
Current Year Research on Vulnerabilities Discovered
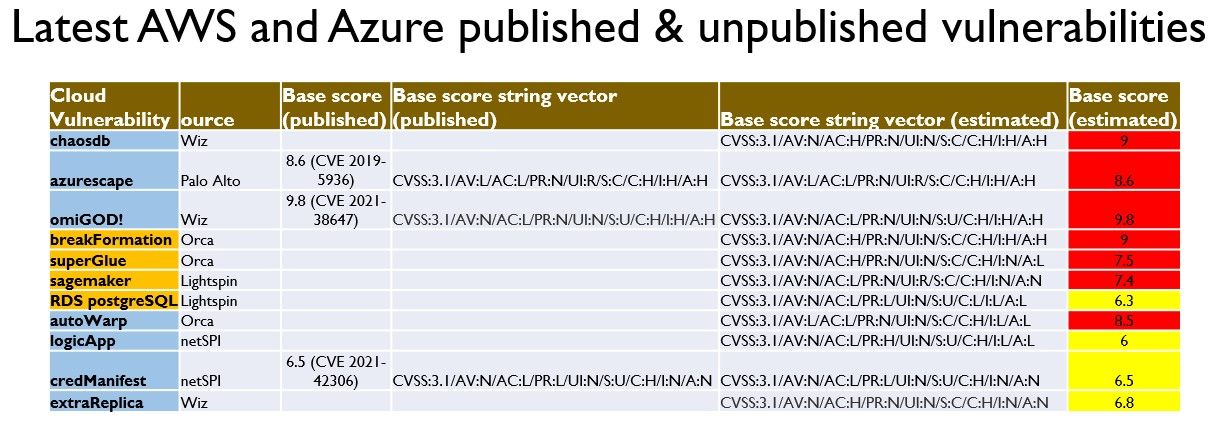
Azure –
Chaos DB- Wiz – CVSS 9 – Aug 26 – 2021
#ChaosDB is an unprecedented critical vulnerability in the Azure cloud platform that allows for remote account takeover of Azure’s flagship database – Cosmos DB.
Who found the #ChaosDB vulnerability?
ChaosDB was discovered by @nirohfeld and @sagitz_ from @wiz_io Research Team. If you have questions you can reach us at research@wiz.io.
AzureScape – Palo alto – CVE 2019-5936 CVSS 9.6 – September 9 2021
The Unit 42 Threat Intelligence team has identified the first known vulnerability that could enable one user of a public cloud service to break out of their environment and execute code on environments belonging to other users in the same public cloud service. This unprecedented cross-account takeover affected Microsoft’s Azure Container-as-a-Service (CaaS) platform.
Exploitation:
There is no knowledge of Azurescape being exploited in the wild. It’s possible the vulnerability existed from ACI’s inception, so there is a chance that some organizations were affected. Azurescape also affected ACI containers in Azure Virtual Networks.
https://www.paloaltonetworks.com/blog/2021/09/azurescape/
Omi God – CVE 2021-3847 – CVSS 9.8 – September 14 2021
Wiz Research Team recently found four critical vulnerabilities in OMI, which is one of Azure’s most ubiquitous yet least known software agents
https://www.wiz.io/blog/omigod-critical-vulnerabilities-in-omi-azure/
CVE-2021-38647 – Unauthenticated RCE as root
CVE-2021-38648 – Privilege Escalation vulnerability
CVE-2021-38645 – Privilege Escalation vulnerability
CVE-2021-38649 – Privilege Escalation vulnerability
Service Affected:
Many different services in Azure are affected, including Azure Log Analytics, Azure Diagnostics and Azure Security Center
AWS
breakFormation – Orca – CVSS 9 – Aug – 2021
Note Vulnerability was fixed in 6h
Tzah Pahima, discovered a vulnerability in AWS allowing file and credential disclosure of an AWS internal service.
The Vulnerability was an XXE (XML External Entity) vulnerability found in the CloudFormation service. This could have been used to leak sensitive files found on the vulnerable service machine and make server-side requests (SSRF) susceptible to the unauthorized disclosure of credentials of internal AWS infrastructure services.
Service Affected: CloudFormation, the service that enables you to easily provision AWS resources (such as EC2 instances and S3 buckets) using templates. CloudFormation also allows you to use API calls to dynamically create and configure resources.
Other (covered in future release)
superglue – Orca –
sagemaker – Lightspin – CVSS 7.4
RDS Postress SQL – Lightspin – CVSS 6.3
AutoWrap – Orca – CVSS 8.5
logicApp – NetSPI – CVSS 6
credManifest – NetSPI – CVSS 6.5 – CVE 2021-42306
extraReplica – Wiz – CVSS 6.8
INFRA/Network
QNAP
QNAP has asked customers this week to disable the AFP file service protocol on their network-attached storage (NAS) appliances until it fixes multiple critical Netatalk vulnerabilities
CVE-2022-23121 was discovered by NCC Group EDG team at Pwn2Own
NCC Group’s EDG team members exploited one of these security flaws, tracked as CVE-2022-23121 and rated with a 9.8/10 severity score
Three of the other bugs QNAP warned its customers about also received 9.8/10 severity ratings (i.e., CVE-2022-23125, CVE-2022-23122, CVE-2022-0194)
Vulnerability in Netatalk:
Netatalk is a free and open-source implementation of the Apple Filing Protocol (AFP), allowing Unix-like OSes to serve as file servers for macOS clients.
QNAP says the Netatalk vulnerabilities (fixed in QTS 4.5.4.2012 build 20220419 and later) impact the following operating system versions:
- QTS 5.0.x and later
- QTS 4.5.4 and later
- QTS 4.3.6 and later
- QTS 4.3.4 and later
- QTS 4.3.3 and later
- QTS 4.2.6 and later
- QuTS hero h5.0.x and later
- QuTS hero h4.5.4 and later
- QuTScloud c5.0.x
Previous Vulnerability:
Western Digital decided to deprecate the service and remove it from My Cloud OS altogether in firmware update 5.19.117, so users of WD NAS devices are advised to upgrade to that version or later.
Bonus:
Android new security policy
Google has published new data safety on android that enables you to specify what information are disclosed
The transparency measure, which is built along the lines of Apple’s “Privacy Nutrition Labels,” was first announced by Google nearly a year ago in May 2021.
This is part of an effort to make android a more safe and controlled environment
Massive DDoS Attack
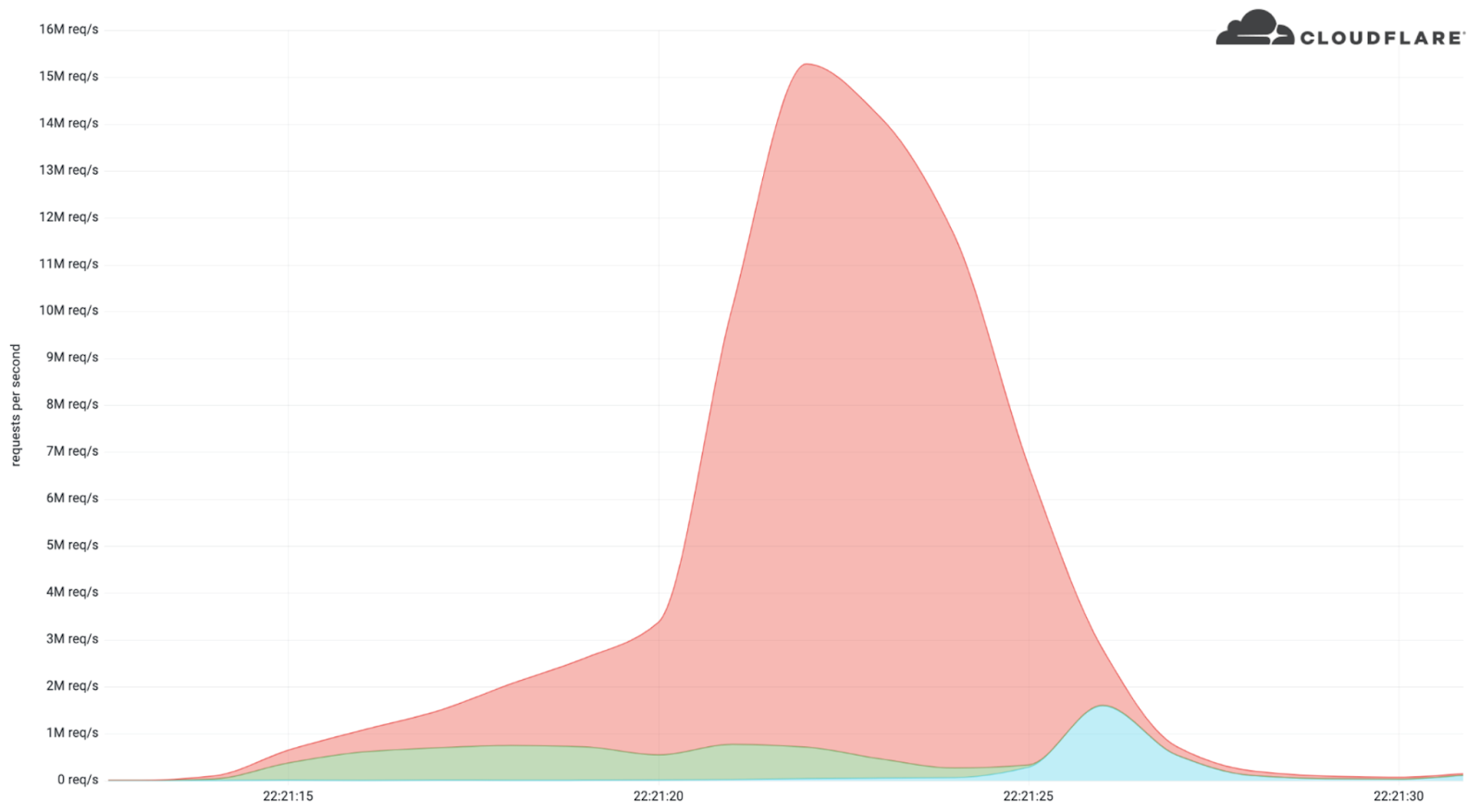
Cloudflare Detects a DDoS Attack peaking at 15 Million requests https://blog.cloudflare.com/15m-rps-ddos-attack/
the article mentions: “While this isn’t the largest application-layer attack we’ve seen, it is the largest we’ve seen over HTTPS. HTTPS DDoS attacks are more expensive in terms of required computational resources because of the higher cost of establishing a secure TLS encrypted connection. “