Appreciating Application Security (AppSec) could not be timelier in today’s digital world where cyber-attacks are common occurrences. Insights from a Webinar with Industry Experts, Frank and Sean. This discusses App-Sec, Vulnerability Management, Risk- Based Vulnerabilities, and Digital Supply Chain Security with a Guide to Navigate Complicated Issues in Details.
0:00 – 1:30 Frank and Sean introduce themselves and set the stage for the discussion on Application Security (AppSec).
Challenges in AppSec
1:31 – 5:00 Discuss the various challenges in AppSec, including the conflict between business and security needs.
Why is AppSec Complicated?
5:01 – 8:30 Explain the complexities in AppSec, such as the lack of standardization and the presence of legacy software.Solutions and Approaches
8:31 – 12:00 Sean and Frank discuss potential solutions, including awareness programs and real-time vulnerability detection tools.
Risk Acceptance
12:01 – 15:00 The duo discusses the concept of risk acceptance and why it often becomes the norm.
Vulnerability Management
15:01 – 18:00 Discussions on how to manage vulnerabilities effectively using scoring systems like EPSS.
Closing Remarks18:01 – 20:00 Summary of the key takeaways and a preview of upcoming panels.
Contents
ToggleIntroduction
The recent webinar between Frank and Sean, a Principal Application Security Engineer, provided a wealth of information on the complexities of AppSec. This blog post aims to summarize their key insights, focusing on vulnerability management, risk-based vulnerability, and digital supply chain security.
The Complexity of AppSec (Webinar Time: 1:31 – 5:00)
AppSec is a multifaceted field that poses numerous challenges, including the conflict between business and security needs. Sean emphasizes that understanding these complexities is the first step in effective vulnerability management.
Vulnerability Management: More Than Just Patching (Webinar Time: 5:01 – 8:30)
Vulnerability management goes beyond merely patching software; it involves a comprehensive approach to identifying, classifying, and mitigating vulnerabilities. Sean suggests that real-time vulnerability detection tools can be invaluable in this process.
Risk-Based Vulnerability: A Calculated Approach (Webinar Time: 8:31 – 12:00)
Sean introduces the concept of risk-based vulnerability, which involves prioritizing vulnerabilities based on their potential impact. Scoring systems like the Exploit Prediction Scoring System (EPSS) can be instrumental in this risk-based approach.
Digital Supply Chain Security: The Overlooked Aspect (Webinar Time: 12:01 – 15:00)
The webinar also touches on the importance of securing the digital supply chain. With software often comprising various third-party components, the risk of vulnerabilities entering through the supply chain is high. Sean stresses the need for rigorous vetting processes for third-party vendors.
Risk Acceptance: Handle With Care (Webinar Time: 15:01 – 18:00)
Risk acceptance is often seen as a necessary evil, but Sean points out that it can be a ticking time bomb if not managed carefully. Understanding the exploitability of accepted risks is crucial for informed decision-making.
Conclusion
The webinar offers a comprehensive look into the world of AppSec, vulnerability management, risk-based vulnerability, and digital supply chain security. As businesses continue to navigate the digital landscape, these insights provide a valuable roadmap for enhancing security postures.
Get in control of your Application Security posture and Vulnerability management
Moreover, Phoenix Security’s correlation capabilities can help organizations link the activities in the code with the context in the shift-right part, ensuring that issues are identified and addressed proactively. Using Phoenix Security’s scorecard, organizations can create a common language between the security, development, and business teams, ensuring everyone is aligned and focused on achieving the same goals.
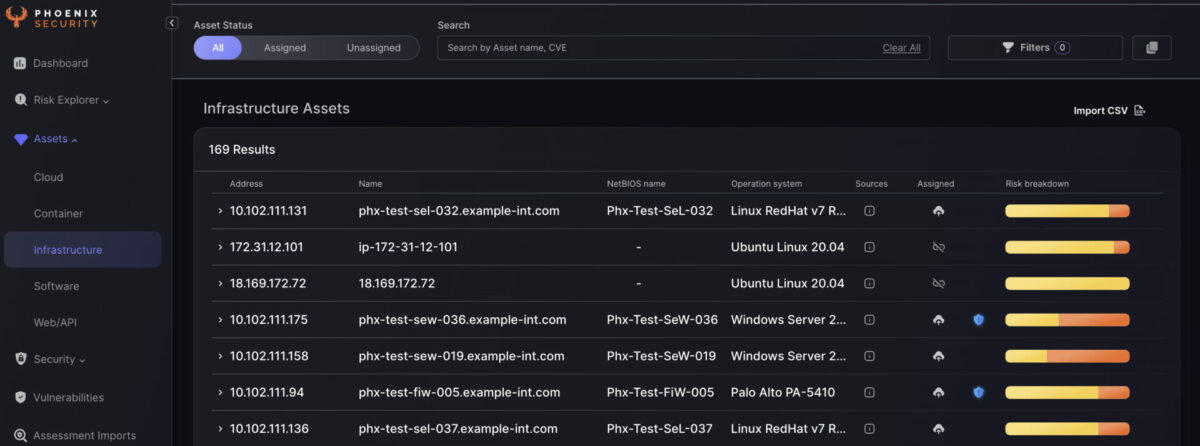
Finally, Phoenix Security’s ability to create risk-based profiles can help organizations translate their security goals into dynamic and smart targets for engineers. By using risk-based profiles, engineers can prioritize their work and focus on the most critical issues, ensuring that they make the most effective use of their time and resources.
Overall, by leveraging Phoenix Security’s powerful capabilities, organizations can implement a smart, risk-based approach to software development that ensures the success of their initiatives while minimizing risk and improving overall efficiency. With Phoenix Security as their partner, organizations can feel confident that they are taking a proactive approach to software development that is aligned with their business objectives and goals.

















