Contents
ToggleExecutive Summary
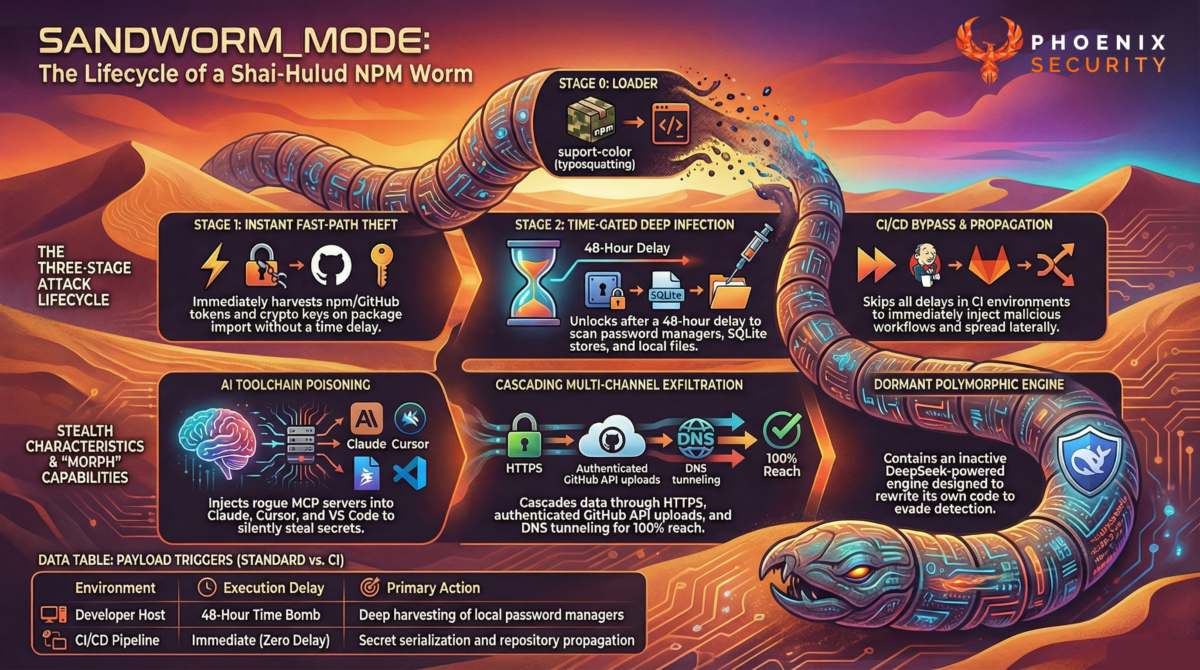
A Shai-Hulud-style supply chain worm tracked as SANDWORM_MODE weaponized at least 19 malicious npm packages to steal credentials, poison CI pipelines, infect repositories, and tamper with AI coding assistants at scale. Original disclosure from the team at Socket. The code follows style and techniques from the previous iteration of SHA1-Hulud (variant 3, variant-2, variant 1), but adds a level of morphism (changeability) and adaptation, a notch above the previous iterations.
TL;DR for Engineering Teams
- 19 malicious npm packages were published under two aliases: official334 and javaorg.
- Every listed version below is malicious. There are no safe patch versions.
- The worm executes on import, steals npm, GitHub, CI, crypto, and LLM API credentials.
- It injects GitHub Actions workflows and persists via global git hooks.
- It plants rogue MCP servers into AI coding assistants to harvest SSH keys and secrets.
- If installed in CI, the full payload executes immediately with no delay.
If your pipeline pulled any of these packages, assume credential compromise and repository tampering.
Technical Anatomy
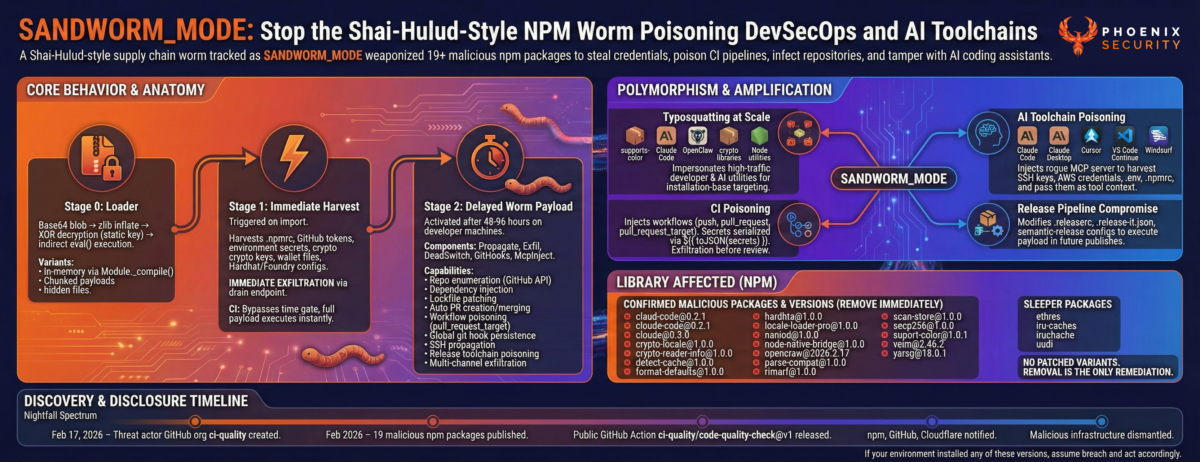
SANDWORM_MODE follows a three-stage execution chain designed for stealth, lateral movement, and survivability.
Stage 0: Loader
- Base64 blob
- zlib inflate
- XOR decryption with static key
- indirect eval() execution
Variants use:
- In-memory execution via Module._compile()
- Chunked payload catalogs
- Temporary hidden files deleted post-execution
No legitimate color utility or formatting helper needs XOR + inflate + eval.
Stage 1: Immediate Harvest
Triggered on import.
Harvests:
- .npmrc tokens
- GitHub tokens
- Environment secrets
- Crypto keys
- Wallet files
- Hardhat and Foundry configs
Crypto material is exfiltrated immediately via a dedicated drain endpoint. No delay. No gating.
In CI environments:
- Time gate bypassed
- Full payload executes instantly
Stage 2: Delayed Worm Payload
Activated after 48 to 96 hours on developer machines.
Components:
- Propagate
- Exfil
- DeadSwitch
- GitHooks
- McpInject
Capabilities:
- Repository enumeration via GitHub API
- Dependency injection into package.json
- Lockfile patching
- Automatic PR creation and merging
- Pull request workflow poisoning using pull_request_target
- Global git hook persistence via init.templateDir
- SSH-based fallback propagation
- Release toolchain poisoning via .releaserc injection
- Multi-channel exfiltration: HTTPS, GitHub private repos, DNS tunneling
This is automated lateral movement inside the software supply chain.
Thanks to the team at Socket for the original disclosure and detailed article. You can find more info here
Defensive Measures
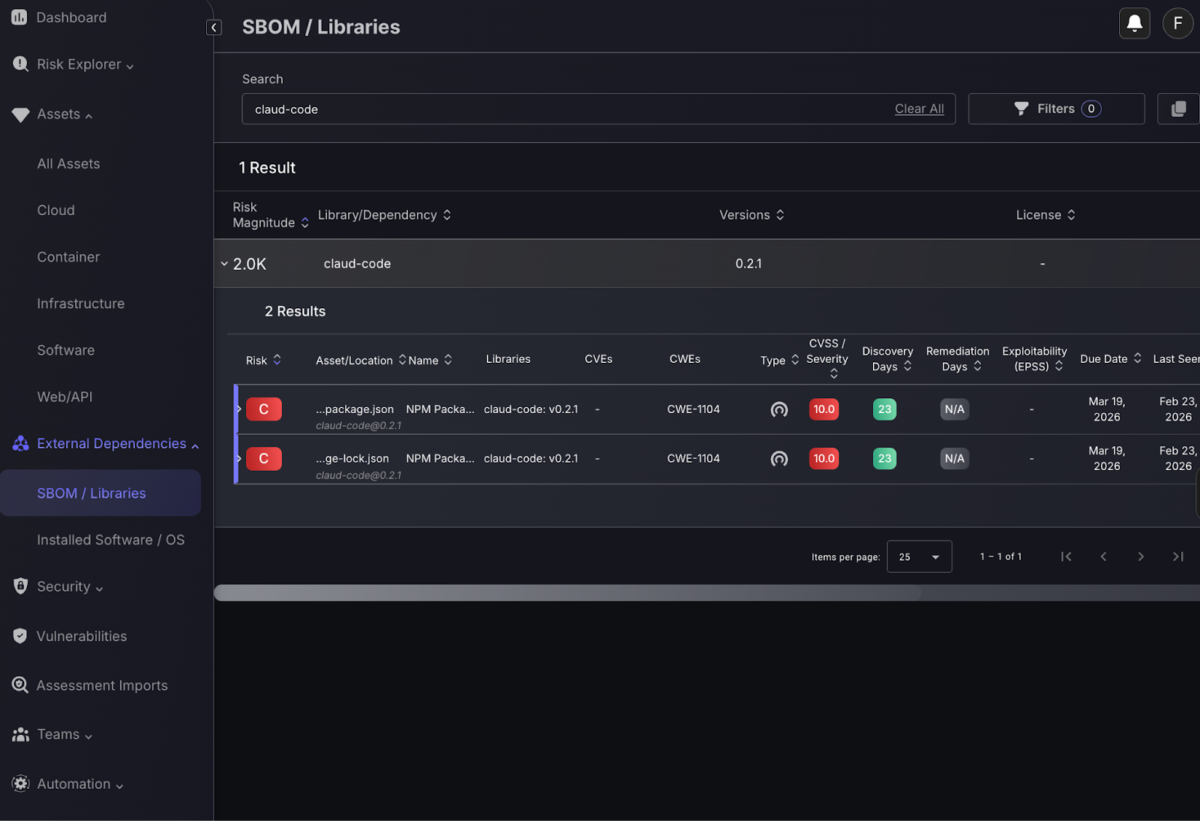
Leverage Phoenix Open Source scanner – Security Scanner (FREE) to identify the vulnerability blast radius,
or download the Phoenix Security Library Campaign.
Leverage Phoenix Security Filters and the campaign method to update/ retrieve the new vulnerabilities
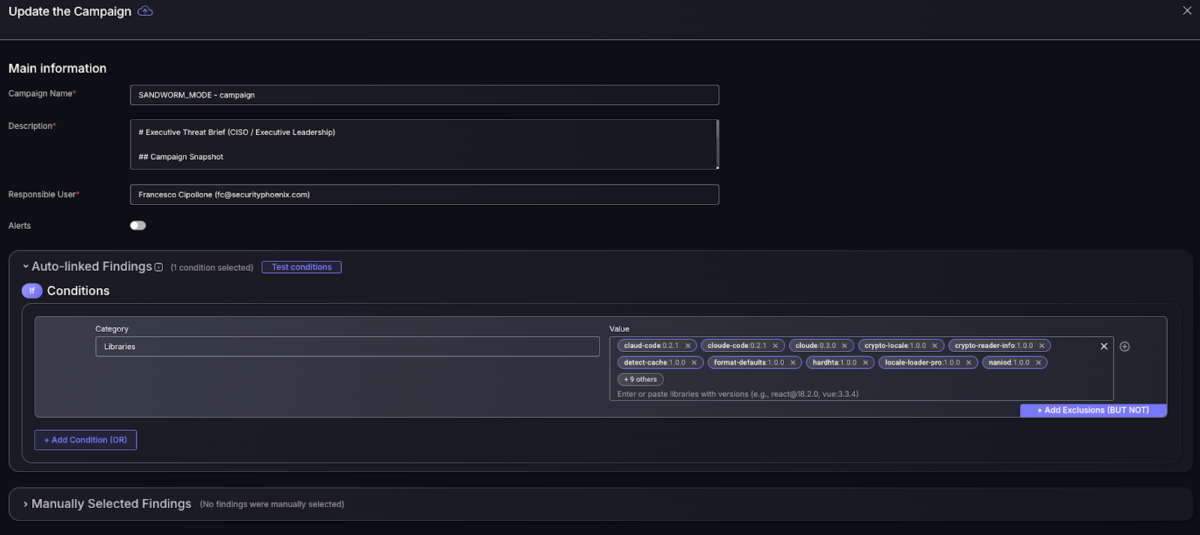
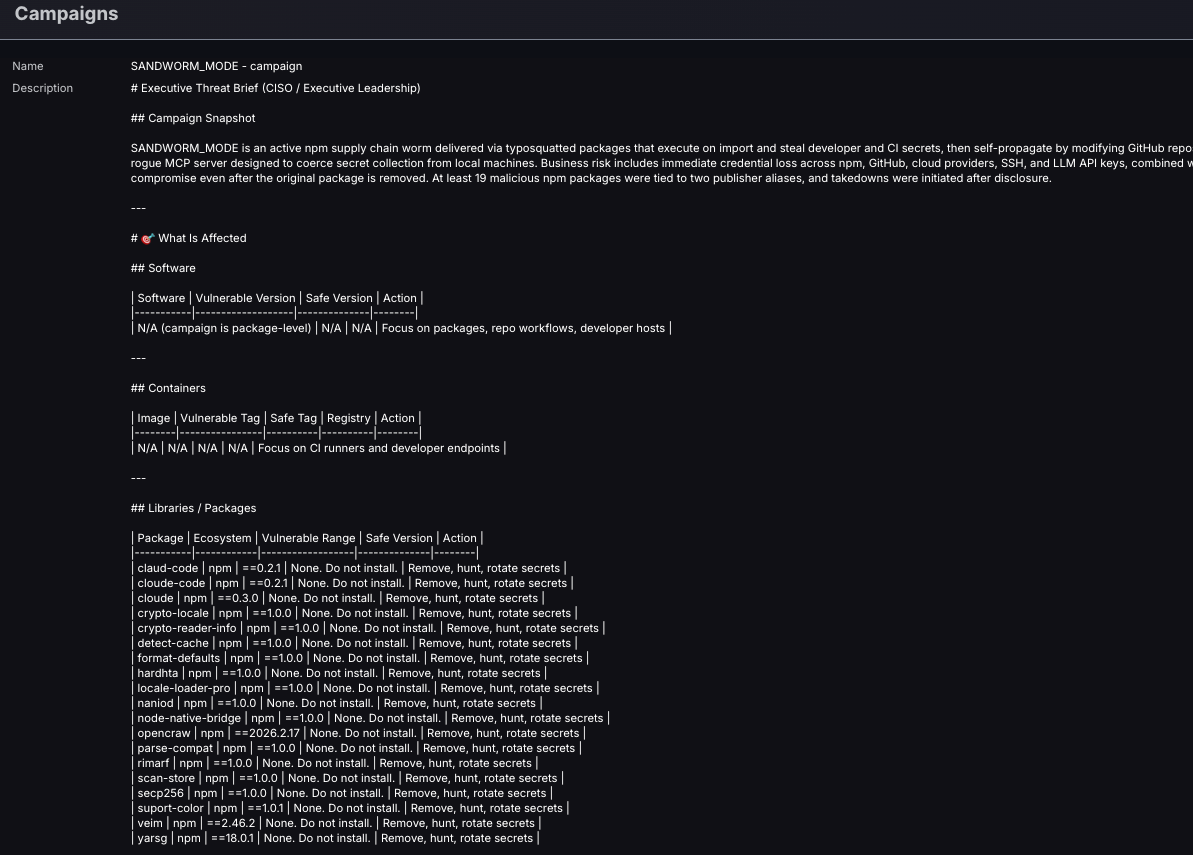
Check the libraries not affected in SBOM screen
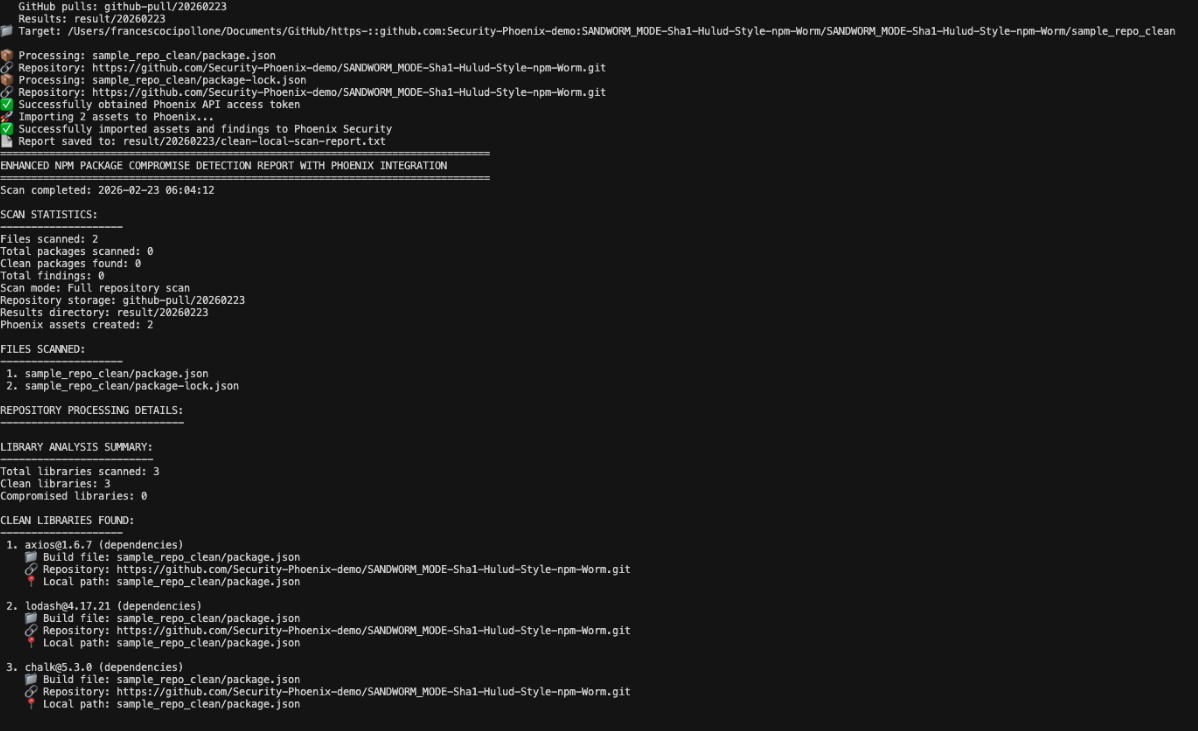
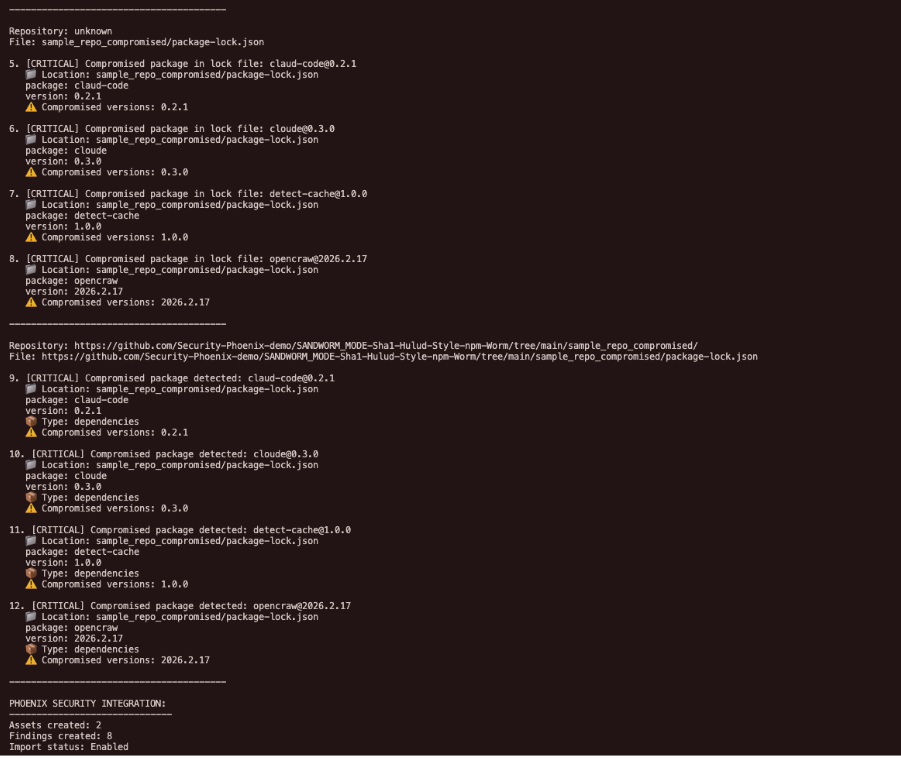
Leverage Open source scanner
When scanning with options python3 enhanced_npm_compromise_detector_phoenix.py sample_repo_clean –enable-phoenix –output clean-local-scan-report.txt
(replace the repo with your own cloned repo)
Good Outcome (no infections)
Bad Outcome (packages are infected)
Core Behaviours
1. Typosquatting at Scale
The campaign impersonates:
- supports-color
- Claude Code
- OpenClaw
- crypto libraries
- Node utilities
These are high-install, high-trust packages in DevSecOps pipelines.
This is installation-base targeting. Not opportunistic spam.
2. CI Poisoning
Injected workflows:
on:
push:
pull_request:
pull_request_target:Secrets serialized via:
${{ toJSON(secrets) }}Exfiltration occurs before developers even review the workflow.
3. AI Toolchain Poisoning
The worm injects a rogue MCP server into:
- Claude Code
- Claude Desktop
- Cursor
- VS Code Continue
- Windsurf
It embeds instructions that cause AI assistants to read:
- ~/.ssh/id_rsa
- ~/.aws/credentials
- .env
- .npmrc
And pass them as tool context.
This weaponizes AI agents as credential exfiltration tools.
4. Release Pipeline Compromise
Modifies:
- .releaserc
- .release-it.json
- semantic-release configs
Ensures future npm publish events execute the malicious carrier dependency.
That extends infection into production artifacts.
Affected Versions
| Package | Ecosystem | Vulnerable Range | Safe Version | Action |
| claud-code | npm | ==0.2.1 | No safe version | Remove, purge node_modules, rotate credentials |
| cloude-code | npm | ==0.2.1 | No safe version | Remove, purge node_modules, rotate credentials |
| cloude | npm | ==0.3.0 | No safe version | Remove, purge node_modules, rotate credentials |
| crypto-locale | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| crypto-reader-info | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| detect-cache | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| format-defaults | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| hardhta | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| locale-loader-pro | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| naniod | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| node-native-bridge | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| opencraw | npm | ==2026.2.17 | No safe version | Remove, purge node_modules, rotate credentials |
| parse-compat | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| rimarf | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| scan-store | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| secp256 | npm | ==1.0.0 | No safe version | Remove, purge node_modules, rotate credentials |
| suport-color | npm | ==1.0.1 | No safe version | Remove, purge node_modules, rotate credentials |
| veim | npm | ==2.46.2 | No safe version | Remove, purge node_modules, rotate credentials |
| yarsg | npm | ==18.0.1 | No safe version | Remove, purge node_modules, rotate credentia |
All versions listed below are confirmed malicious and should be treated as compromised:
claud-code@0.2.1
cloude-code@0.2.1
cloude@0.3.0
crypto-locale@1.0.0
crypto-reader-info@1.0.0
detect-cache@1.0.0
format-defaults@1.0.0
hardhta@1.0.0
locale-loader-pro@1.0.0
naniod@1.0.0
node-native-bridge@1.0.0
opencraw@2026.2.17
parse-compat@1.0.0
rimarf@1.0.0
scan-store@1.0.0
secp256@1.0.0
suport-color@1.0.1
veim@2.46.2
yarsg@18.0.1Sleeper packages registered but not yet weaponized:
ethres
iru-caches
iruchache
uudiThere are no patched variants. Removal is the only remediation.
Discovery and Disclosure Timeline
- February 17 2026: Threat actor GitHub org ci-quality created.
- February 2026: 19 malicious npm packages published.
- Public GitHub Action ci-quality/code-quality-check@v1 released.
- npm, GitHub, and Cloudflare notified.
- Malicious infrastructure dismantled.
The campaign shows active iteration and staged development toggles.
Determine If You’re Affected
You are at risk if:
- Any of the above packages appear in package.json or lockfiles.
- Unexpected .github/workflows/quality.yml exists.
- Global git config shows modified init.templateDir.
- .git/hooks contains unfamiliar scripts.
- AI assistant configs contain unexpected mcpServers entries.
- New dependencies were merged automatically without clear authorship.
Also review:
- npm publish history
- Unexpected semver patch bumps
- Repositories with unexplained dependency updates
Temporary Protections
Immediate actions:
- Remove malicious packages.
- Delete node_modules.
- Rotate:
- npm tokens
- GitHub tokens
- CI secrets
- AWS keys
- SSH keys
- Audit:
- .github/workflows
- .releaserc
- global git hooks
- AI assistant configs
- Revoke compromised GitHub tokens and reissue with minimal scope.
- Enforce OIDC trusted publishing.
- Disable automatic PR merging in CI.
For DevSecOps programs:
- Monitor anomalous publish events.
- Require review for workflow modifications.
- Restrict pull_request_target usage.
- Block untrusted MCP server registrations.
How Threat Actors Could Leverage This
This worm is designed for amplification.
Potential abuse paths:
Credential Monetization
- Drain crypto wallets within seconds.
- Sell GitHub tokens for repository access.
- Trade CI secrets on underground markets.
Supply Chain Amplification
- Inject malicious code into high-download packages.
- Publish infected releases via compromised maintainers.
- Create cascading dependency contamination.
Long-Term Persistence
- Git hooks ensure future clones remain infected.
- Release toolchain poisoning ensures future publishes execute payload.
- AI toolchain injection creates a covert secret siphon.
Destructive Capability
The dead switch, currently disabled, can wipe writable home directories if activated.
That makes it dual-use: espionage and sabotage.
Installation Base and Criticality
The targeted ecosystem includes:
- Color utilities used across thousands of packages.
- Crypto libraries embedded in Web3 stacks.
- AI coding assistants with explosive adoption.
- Developer utilities integrated into CI pipelines.
This is not targeting niche projects.
It is positioned at the convergence of:
- DevSecOps automation
- ASPM workflows
- Vulnerability management pipelines
- AI-assisted development
The blast radius grows geometrically with each compromised maintainer.
This is a supply chain worm built for 2026.
Final Assessment
SANDWORM_MODE merges:
- Typosquatting
- Worm automation
- CI poisoning
- Release toolchain compromise
- AI agent manipulation
- Multi-channel exfiltration
It is an evolution of Shai-Hulud-style tradecraft focused on application security infrastructure.
DevSecOps teams that still treat dependency risk as a static CVE problem will miss this class of attack entirely.
This is an active compromise of the delivery pipeline. If your environment installed any of these versions, assume breach and act accordingly.
We acknowledge the research published by Socket on the SANDWORM_MODE campaign.
Original research.
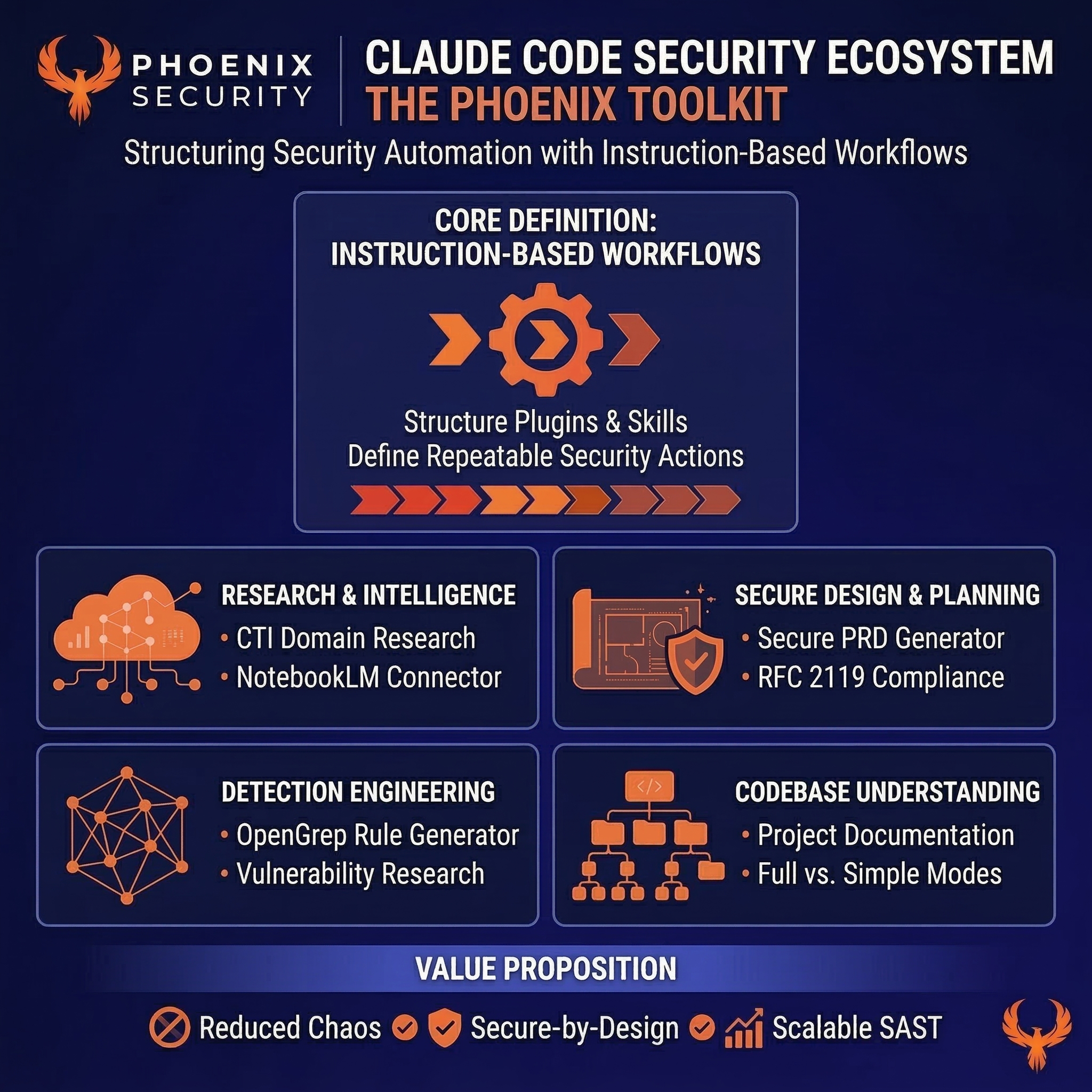
How Phoenix Security Can Help

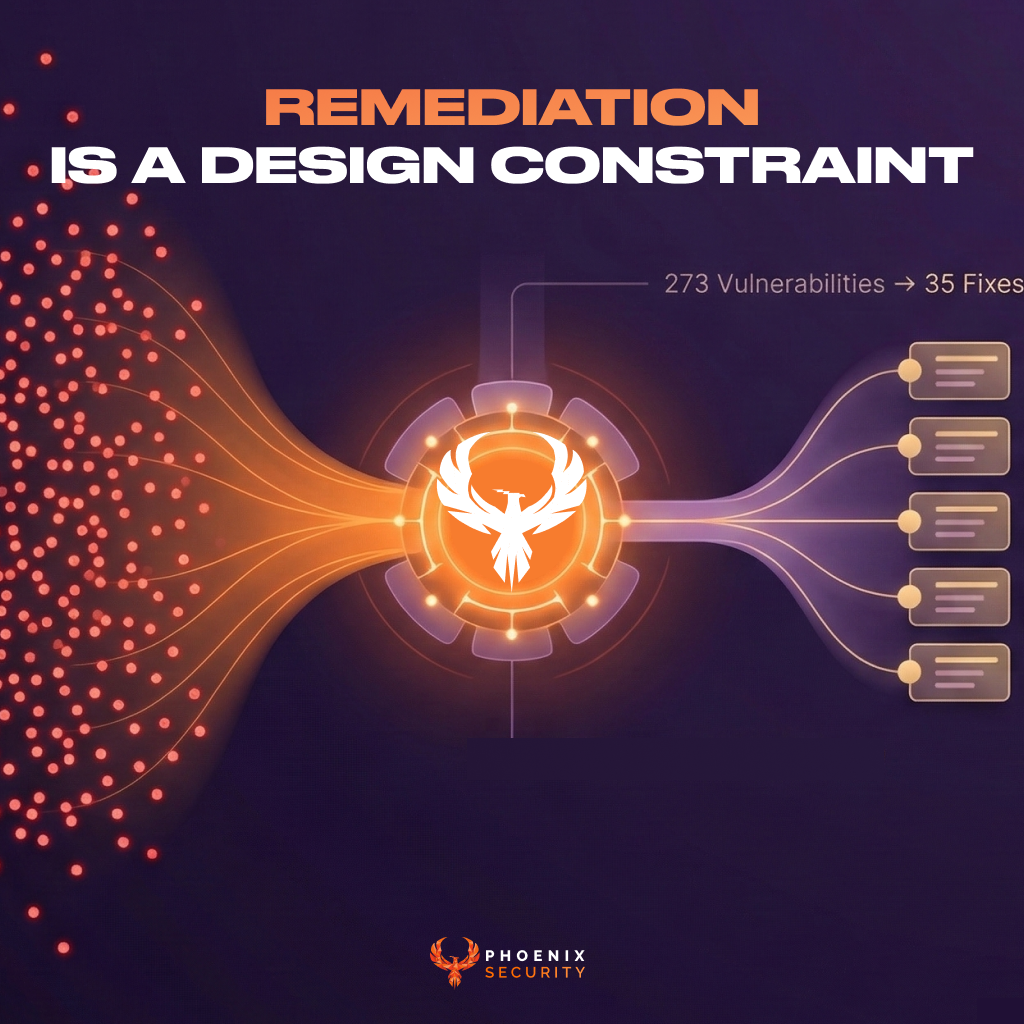
Organizations often face an overwhelming volume of security alerts, including false positives and duplicate vulnerabilities, which can distract from real threats. Traditional tools may overwhelm engineers with lengthy, misaligned lists that fail to reflect business objectives or the risk tolerance of product owners.

Phoenix Security offers a transformative solution through its Actionable Application Security Posture Management (ASPM), powered by AI-based Contextual Quantitative analysis and an innovative Threat Centric approach. This innovative approach correlates runtime data with code analysis and leverages the threats that are more likely to lead to zero day attacks and ransomware to deliver a single, prioritized list of vulnerabilities. This list is tailored to the specific needs of engineering teams and aligns with executive goals, reducing noise and focusing efforts on the most critical issues. Why do people talk about Phoenix

• Automated Triage: Phoenix streamlines the triage process using a customizable 4D risk formula, ensuring critical vulnerabilities are addressed promptly by the right teams.
• Contextual Deduplication: Utilizing canary token-based traceability, Phoenix accurately deduplicates and tracks vulnerabilities within application code and deployment environments, allowing teams to concentrate on genuine threats.
• Actionable Threat Intelligence: Phoenix provides real-time insights into vulnerability’ exploitability, combining runtime threat intelligence with application security data for precise risk mitigation.

By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.