Contents
ToggleRedefining the journey from ASPM to ASM with remediation embedded in Application Security Vulnerability Management: AI Agents That Don’t Just Identify Vulnerabilities — They Fix Them.
Washington, DC – Nov 2025 – Phoenix Security, he leader in ASPM application security vulnerability management, announced today at OWASP Global Application Security DC the early availability of its latest AI innovation – the Phoenix Autofix Remediator Agent.
Built to work hand-in-hand with developers, the Remediator brings AI-powered, context-aware plans or fixes directly into GitHub, giving teams the choice to patch a single dependency, an entire chain of libraries, or rewrite a full build file – all with automated impact analysis and breaking-change assessment.
With this release, Phoenix Security’s AI agents move beyond research and contextual analysis – they now fix vulnerabilities directly in code, aligning remediation speed with DevSecOps and code-to-cloud security workflows.
“The goal was never to automate people out of the loop, but to give them a trusted co-pilot that understands risk, business impact, and context,” said Francesco Cipollone, CEO & Co-Founder of Phoenix Security. “Our Remediator Agent doesn’t just tell you what’s broken — it tells who should fix what and where, why it’s important, if it’s going to break the flow, and delivers the fixes directly in the hands of engineering teams. The objective is to give teams flexibility to work in the way they want — with autofix or suggested remediation.”
AI Remediation in Action: Fix Directly in GitHub
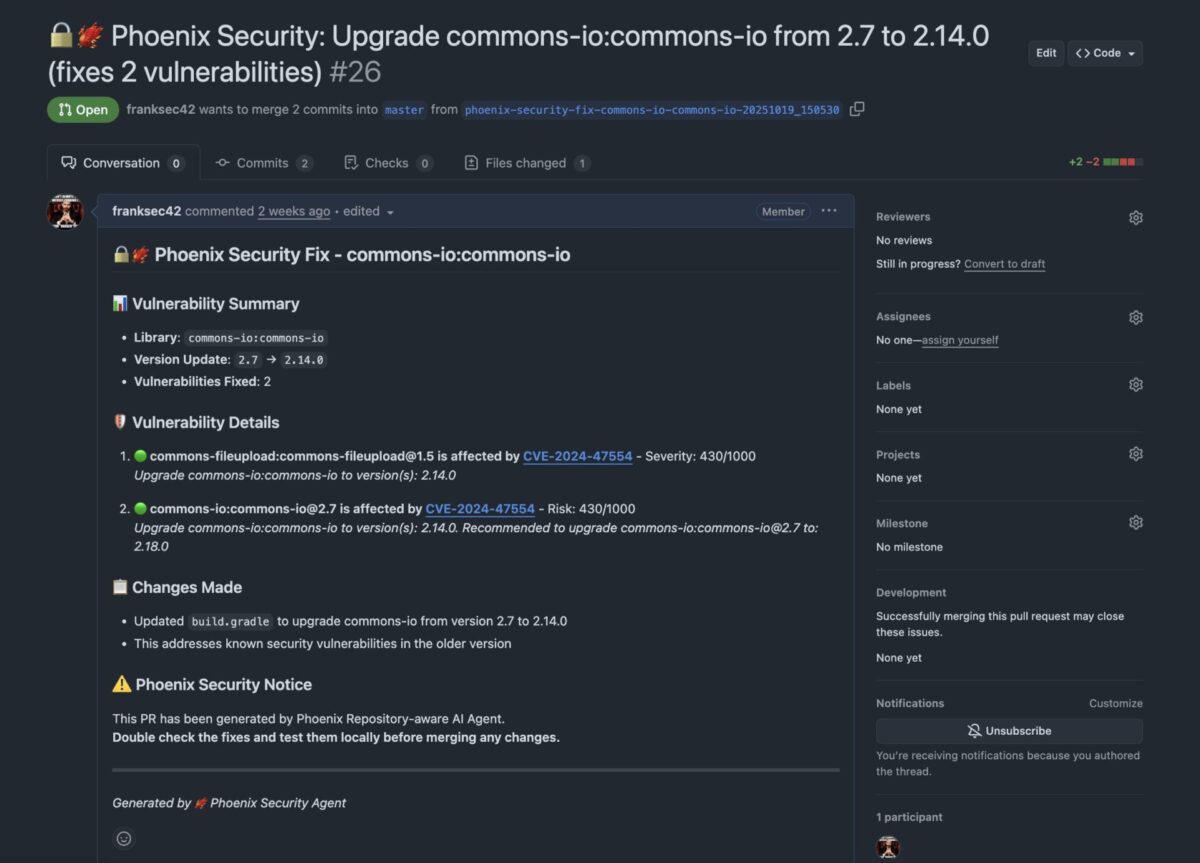
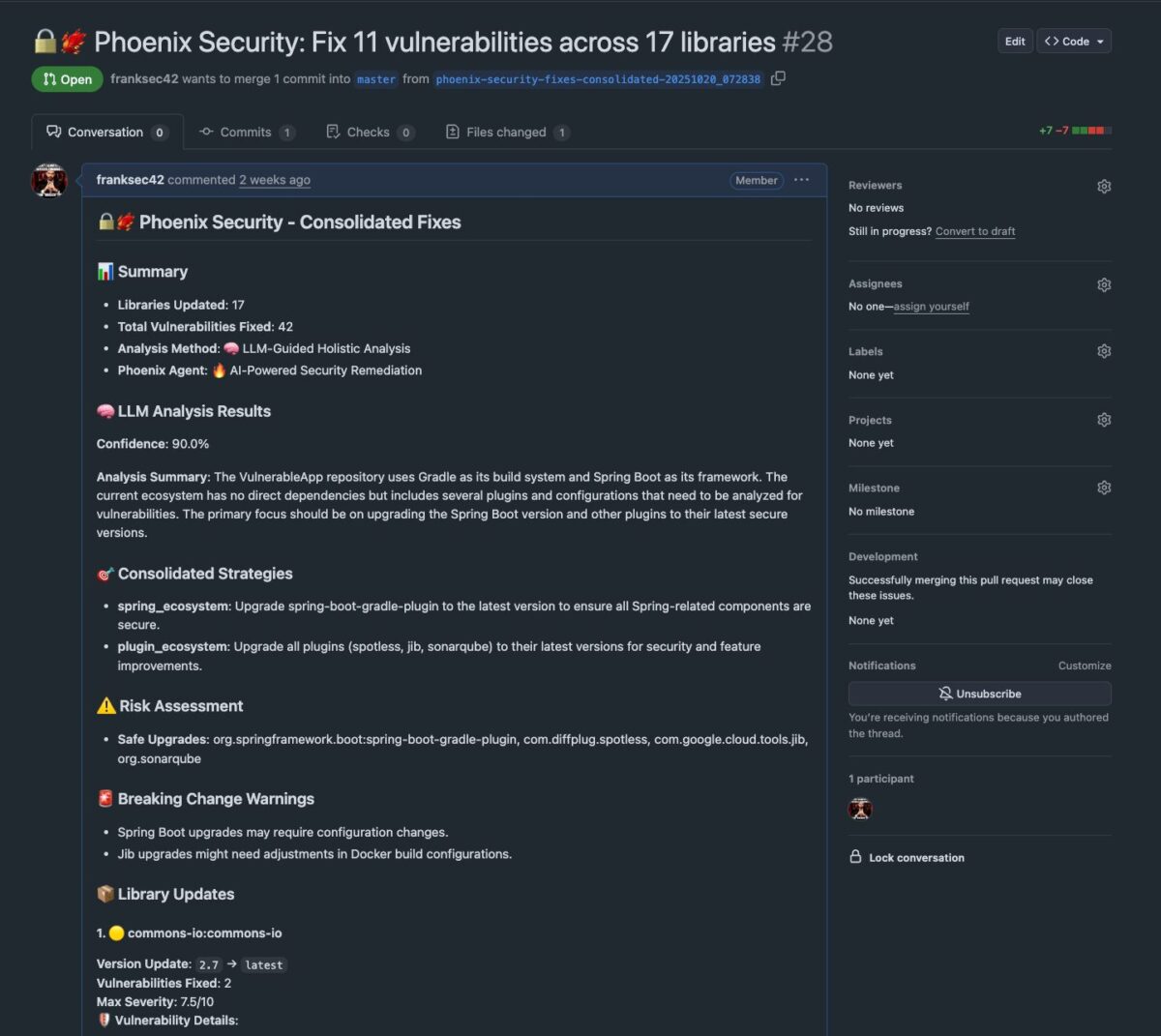
The Phoenix Remediator Agent integrates natively with GitHub, enabling automated PR creation and contextual autofix generation. Developers can now review, approve, or merge AI-proposed fixes with full transparency. The agent supports:
- Single dependency fixes — resolve isolated vulnerabilities with minimal code change.
- Chained dependency updates — tackle multi-layered vulnerabilities across dependent libraries.
- Full build file regeneration — generate a clean, validated replacement build file when vulnerabilities are systemic.
- Breaking change prediction — evaluate dependency upgrades and propose minimal paths to stability.
- Remediation plans — for complex issues, generate structured, context-aware plans rather than auto-commits.
Three Agents, One Mission: Precision From Research to Fix
Phoenix’s AI-powered agent architecture brings together three synergistic components:
The Researcher (GA)
Continuously monitors threat intelligence feeds, mapping vulnerabilities to MITRE ATT&CK, CWE, and ransomware campaigns — powered by proprietary models developed with Google Cloud.
The Analyzer
Uses Phoenix’s code-to-cloud reachability and STRIDE threat modeling to reveal exactly how a vulnerability impacts a business service or application.
The Remediator (New)
Moves context into actions with a remediation plan in reports, code pushed directly to GitHub, translating all intelligence into real, executable change. Using reachability, contextual deduplication, and lineage data, it generates environment-specific autofixes, remediation campaigns, and Jira or ServiceNow remediation plans — or commits changes directly to GitHub.
Together, they transform vulnerability management from “find and report” to “analyze and fix,” cutting remediation time from weeks to minutes.
AI Fixes That Understand Context
This capability is built on Phoenix’s proven Contextual ASPM Engine, combining:
- Reachability Analysis – Removes non-exploitable vulnerabilities, reducing noise by 91%.
- Contextual Deduplication – Prevents duplicate findings across code, containers, and runtime.
- Container Version Control – Tracks lineage for precise remediation paths.
- 4D Risk Formula – Balances exploitability, exposure, and business impact for risk-based prioritization.
AI fixes aren’t just applied — they’re validated against real-world deployment context, advancing the state of ASPM application security vulnerability management.
Proven Results Across Industries
- ClearBank cut container noise by 98%, eliminated up to 99% of criticals, and saved $2.6M in analyst time annually – equivalent to four hours per security engineer every week.
- Bazaarvoice eradicated all critical vulnerabilities in two weeks and reduced high-risk findings by 40%, creating immediate alignment between security and engineering.
- An Ad-tech enterprise achieved a 78% reduction in container vulnerabilities while unifying code-to-cloud security visibility.
Human-Aligned AI: Fix Faster, Stay in Control
Unlike generic LLM copilots, Phoenix Security’s AI Agents are purpose-built for application security. Every action is traceable, reviewable, and aligned to the business context. Teams decide when to apply fixes automatically, when to review, or when to generate compensating controls.
Security remains in command — AI eliminates the manual grind.
Availability
- Researcher Agent — Generally Available
- Remediator Agent with AI Autofix in GitHub — Rolling out globally through Q4 2025–Q1 2026
- Analyzer Agent — Q2 2026
For demos or early access to the AI Autofix capabilities, visit phoenix.security.
















