Phoenix Security proudly unveils a powerful suite of new features and enhancements designed to supercharge Application Security Posture Management (ASPM) and vulnerability management across code and cloud environments. These updates mark a significant evolution in how engineering and security teams detect, prioritize, and remediate vulnerabilities with surgical precision.
With a user-driven approach and a relentless focus on unifying AppSec and CloudSec visibility, this release delivers robust improvements that empower organizations to stay ahead of modern threats while streamlining compliance and development workflows.

Contents
Toggle
🔍 What’s New in Phoenix Security Application Security Posture Management (ASPM)
🌐 Unified Dashboards with Deep Context
The new beta dashboard offers a fully refreshed interface to view and manage your security landscape. It now includes:
- AppSec, CloudSec, or Unified Views: Toggle between code, cloud, or both to gain actionable context across your software supply chain.
- Timeframe Selection: Focus on specific periods for trend analysis and SLA tracking.
- Interactive Metrics: Drill into Findings by Severity, Status, SLA compliance, and attack surface filters to prioritize what truly matters.
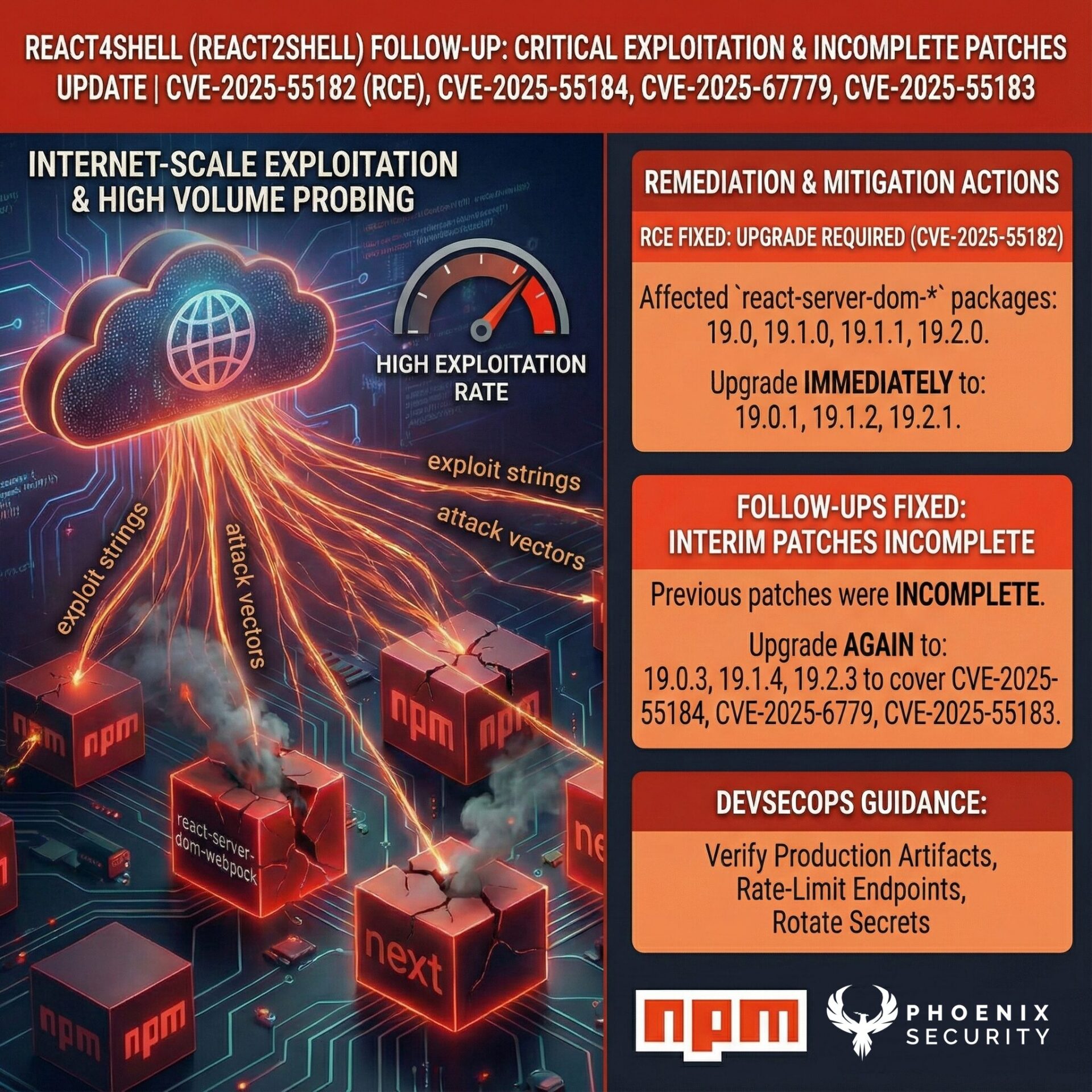
New Preview: Container Lineage Graph

Track container relationships across environments with lineage visualizations—paving the way for runtime-aware ASPM, together with contextual deduplication this feature has enabled our major clients to sca vulnerabilities noise up to 82% and container throttling unified to lineage enabled the reduction of 98% of noise version of container and 78% of non active containers in our ad-tech client.
Banking Client AD Tech Client
Summary of all the features introduced in this update
- Component Multi-Deployments
- New Suggested Deployment Model
- Enhanced Exception Management
- Enhanced Exception Engine Filtering Capabilities
- A New Garbage Collector added for Missing Targets
- New Matching Conditions for Findings Filters
- New Severity Distribution Bars in Vulnerability Table
🔗 Expanded ASPM Integrations
Integrate seamlessly with new and improved security tools, enhancing data ingestion and unifying your ASPM strategy:
- ✅ Fortify SSC
- ✅ Aikido Security
- ✅ Orca Security
- ✅ Semgrep (SCA & SAST)
- ✅ Arnica enhancements
Get in control of your Application Security posture and Vulnerability management
New Dashboard
This release introduces a revamped version of our key dashboards: main, security and team.
After extensive consultation with our users, we are pleased to introduce an enhanced dashboard layout and functionality. This update includes numerous changes and improvements, but we’ll highlight some of the key ones here.
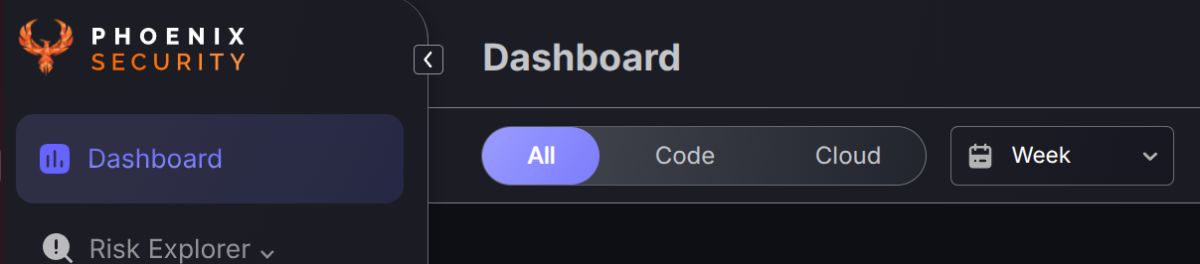
New Dashbaord and Improved filtering
The newly redesigned Phoenix Security dashboard delivers a powerful, user-centric interface that transforms how security and engineering teams manage their application security posture. With its beta release, the dashboard introduces a seamless code-to-cloud view, enabling users to toggle between AppSec (code), OpSec (cloud), or a unified perspective across both domains. Enhanced with global scope and dynamic timeframe selectors, the dashboard offers deep visibility into security metrics such as Findings by Severity, Findings by Status, and SLA compliance. Interactive charts and filters allow teams to drill down by attack surface, making it easier than ever to prioritize vulnerabilities that truly matter. Combined with real-time SLA tracking and actionable visual insights, the new dashboard sets a new standard in ASPM dashboards, aligning perfectly with modern vulnerability management needs.
The all-new Findings per Status chart redefines your vulnerability management process, now allowing you to track new, open, and closed tickets using findings counts based on attack surface.

Global Scope and Time-frame Switches
Users get a more focused and uniform experience by being able to select the time frame to focus on and whether they can see data just for their Appsec (Code), OpSec (Cloud) or both.
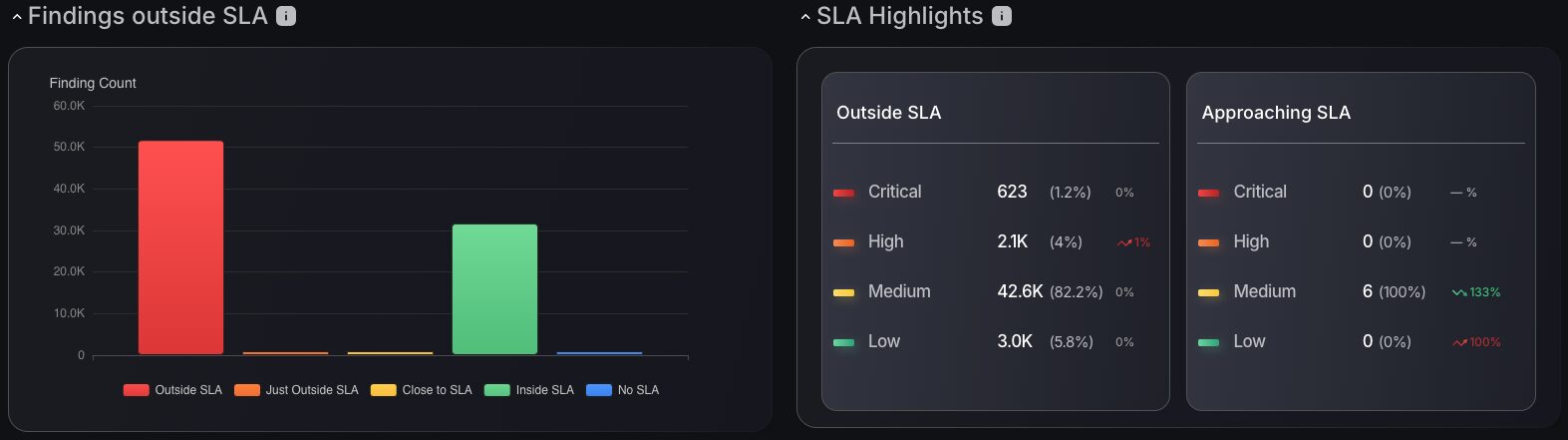
Detailed SLA Status
The introduction of SLA metrics into the dashboard now makes prioritisation of vulnerabilities as clear and efficient as ever. Track SLA based on compliance status, even categorised by severity level, to prioritise vulnerabilities that matter most. The users can now switch between the remediation SLA and the discovery time SLA
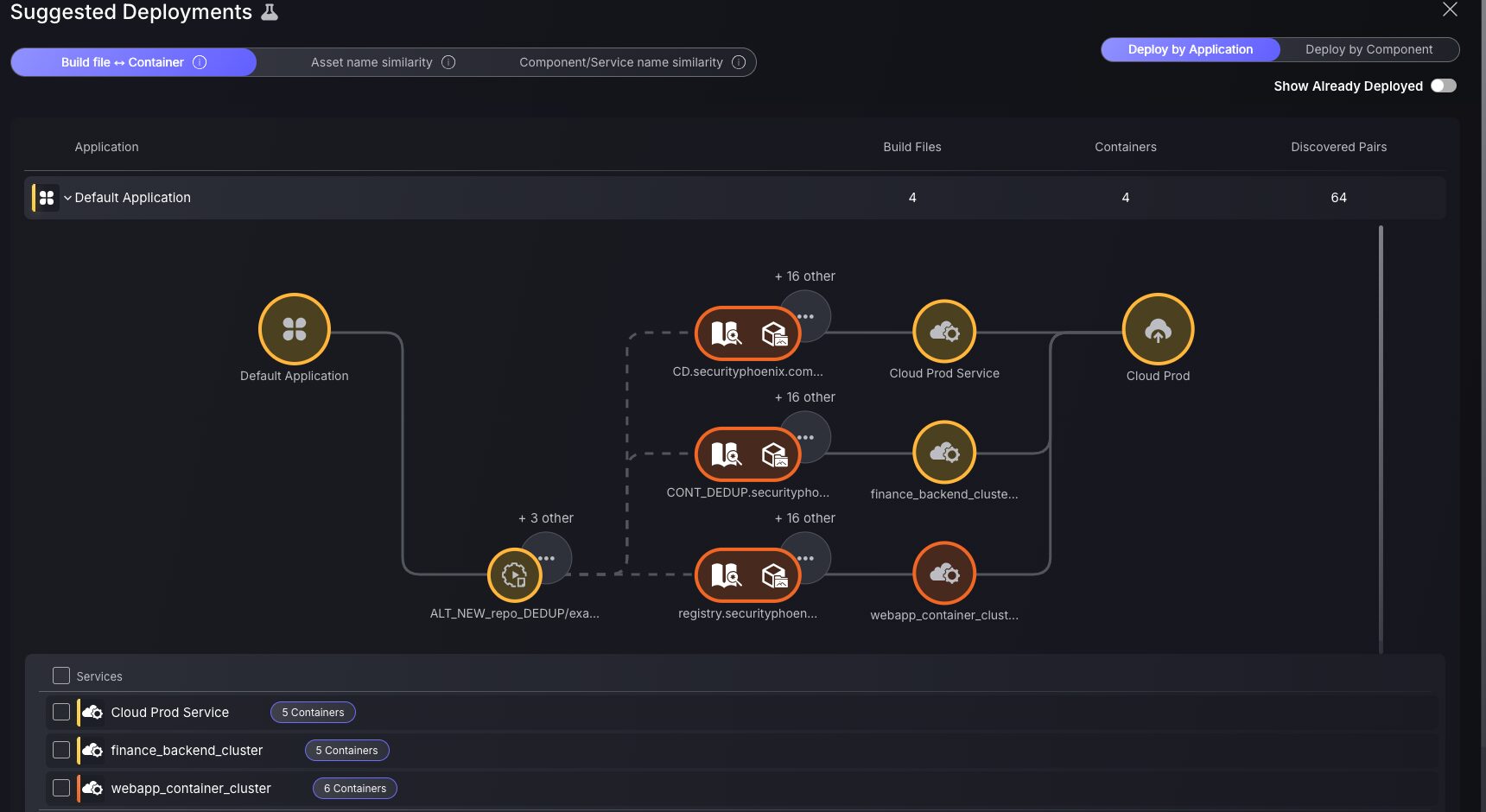
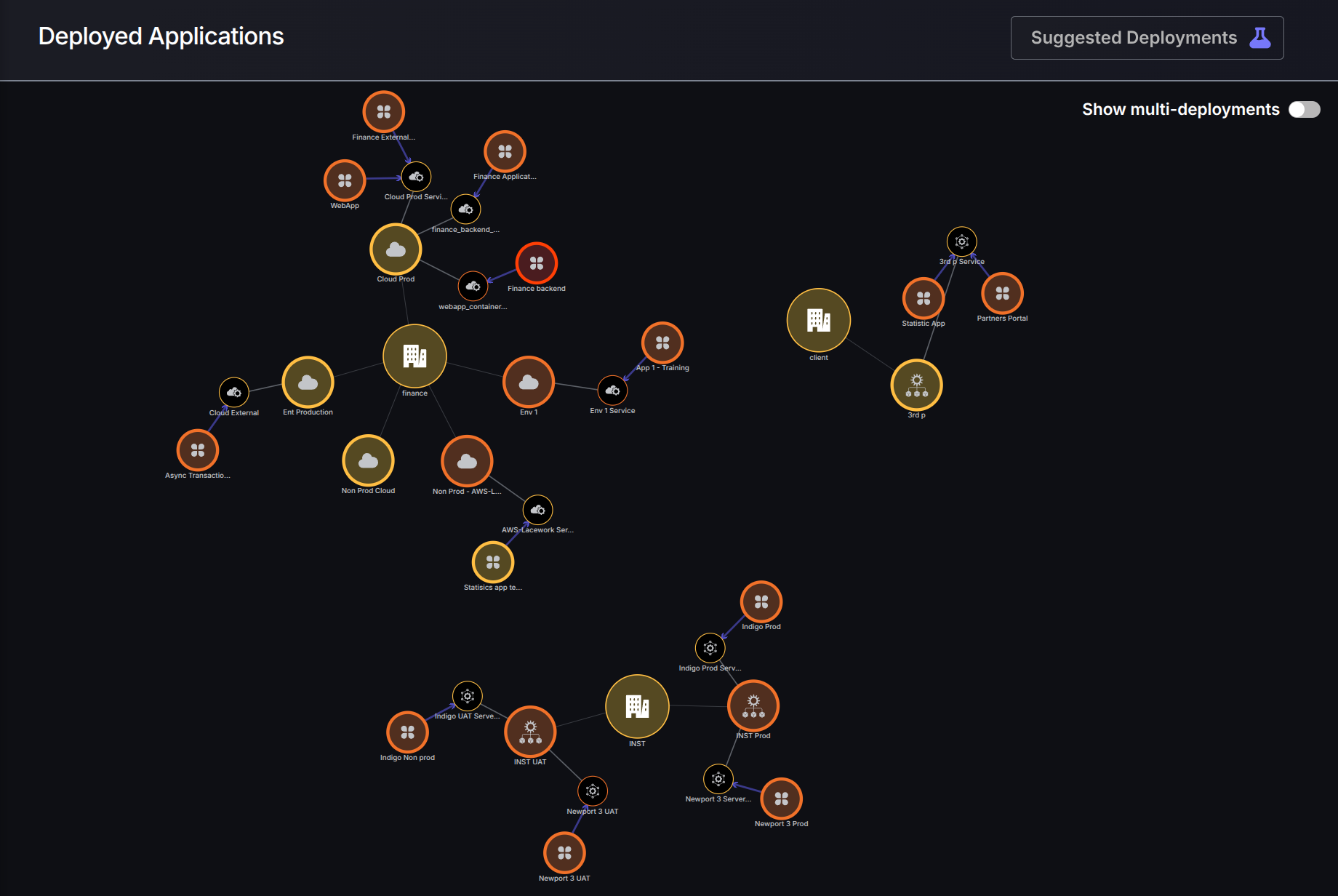
New Suggested Deployment Model
Leverage intelligent insights to automate deployment mapping:
- Get AI-driven recommendations based on file/container similarities and naming conventions.
- Use a dual table + graph interface to visualize and confirm the suggested architecture.
In tandem with the introduction of Component Multi-deployments, this release of the Phoenix platform provides users with a powerful tool to identify and create deployment relationships. The Suggested Deployment table and graph streamlines the process by offering deployment suggestions based on different criteria, while facilitating the confirmation of those suggestions in bulk or with detailed precision.
Use the system architecture diagram to analyse the suggested deployments of services at an application or component level, depending on your preference. Customise your approach to component deployment using suggestions based on: build file to container similarities, build asset name and container asset names similarity, as well as component to service name.
The dual table/graph display provides a mix of visual and detailed information about the context of the suggested deployments, making the review and decision-making process easier than ever.
Component Multi-Deployments
This new release provides an increased level of granularity and flexibility when configuring your deployment relationships. This evolution relies on two key changes:
- Deployment relationships are now established between Components, rather than Applications, and Services. This provides more granularity when defining which parts of your code are deployed where.
- Each Component can be deployed onto multiple Services, which enables organisations to better reflect the reality of the relationships between code and runtime.
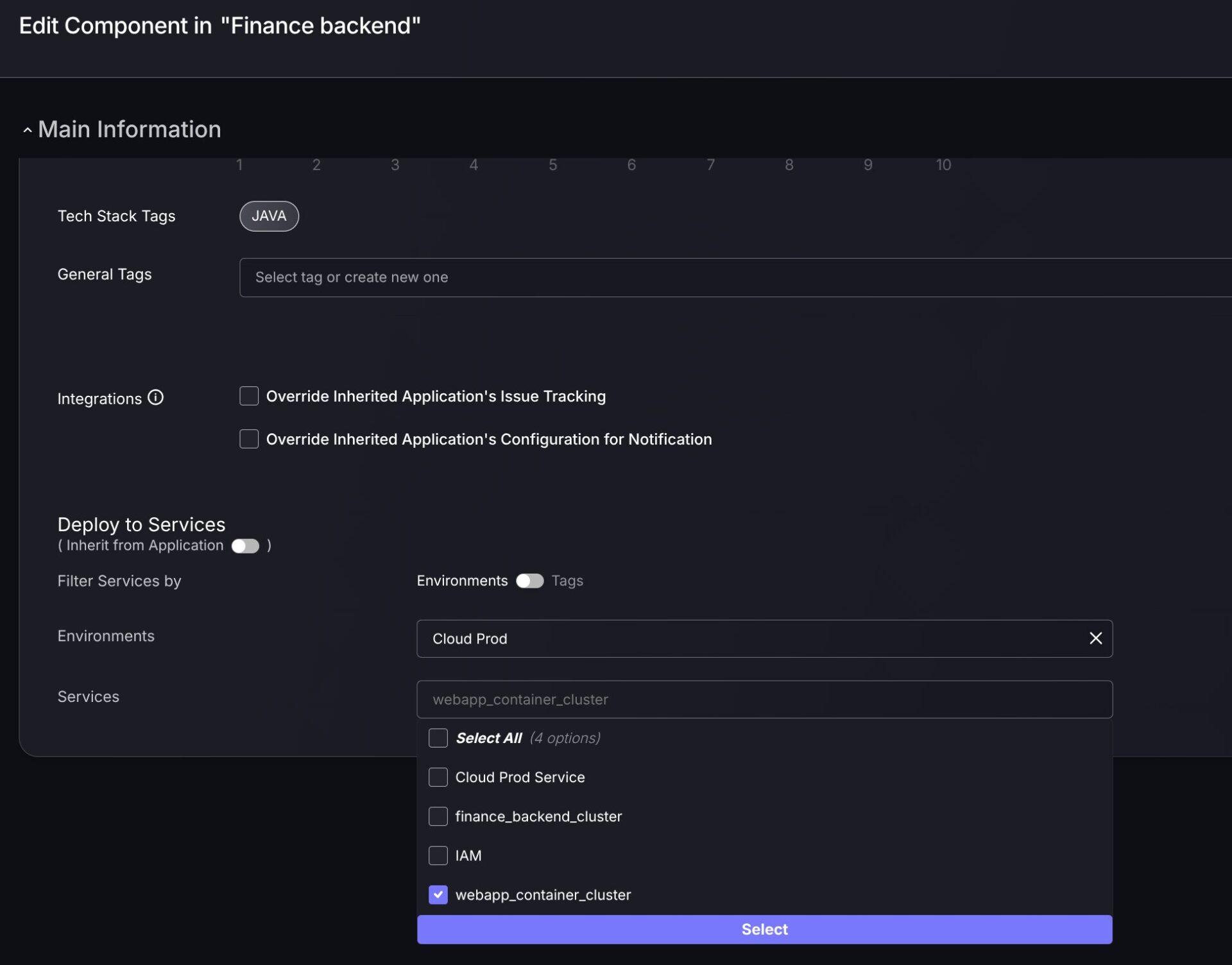
However, to maintain flexibility within deployment relationships, we have kept the option to deploy entire applications in one go. This will now deploy all components (present and future) inside that application to the selected services, with the relationships being between components and services. (See “Inherit from Application” switch in screenshot above.)
When looking at the Deployed Applications graph, the new Multi-deployments switch allows you to view cross-relationships between Components and services (indicated by Blue arrows) in a simplified or detailed manner.
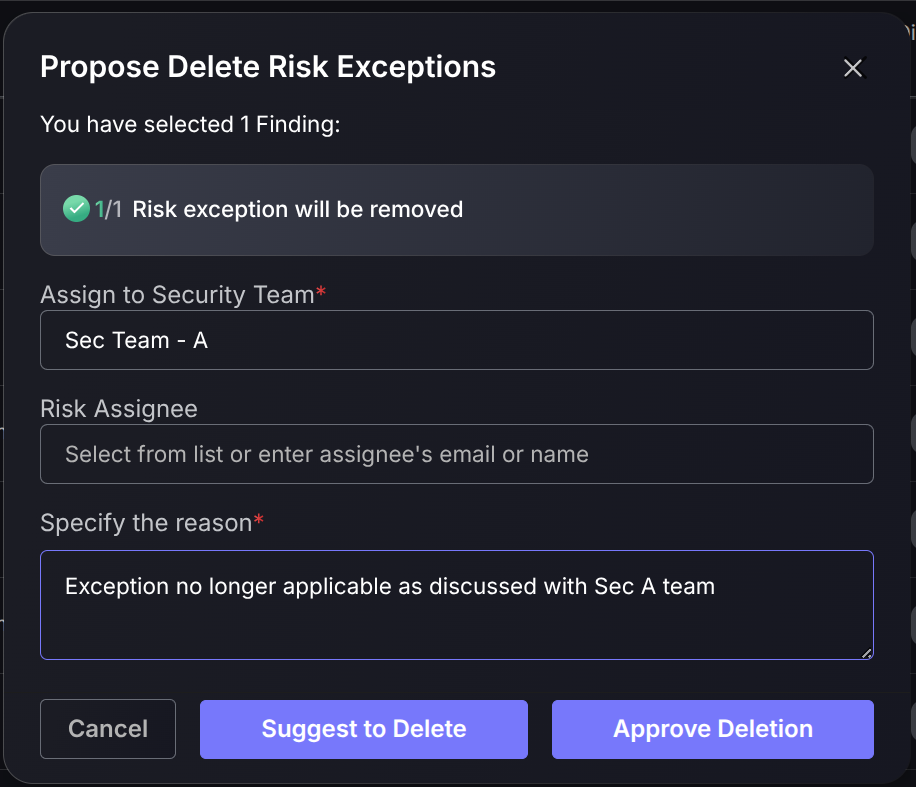
Enhanced Exception Management
The risk exception management flow allows engineers and security specialists to request the removal of an existing exception. This complements the ability to modify an existing exception by requesting a new request that would overwrite the previous one.
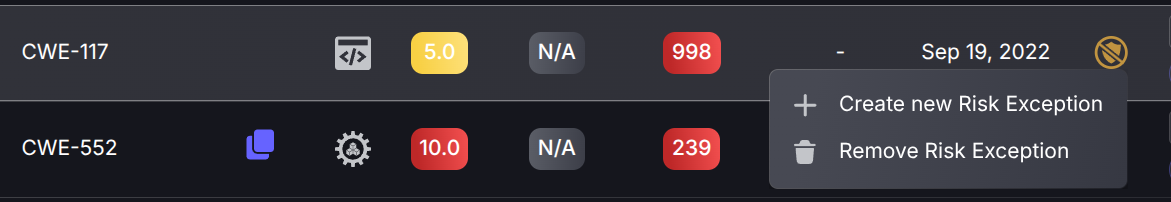
The deletion of risk exceptions is, obviously, managed through an approval flow in order to ensure that only users with the right permissions can apply the removal. If the requesting user has the permissions to approve as well, then this option would be available right in the request form.
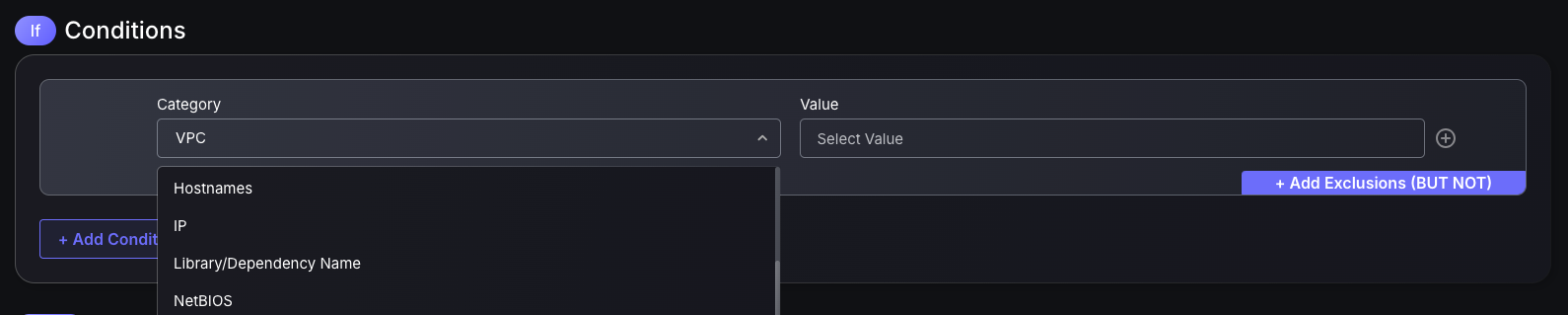
Enhanced Exception Engine filtering capabilities
Creating Exceptions couldn’t be more straightforward. With our newly introduced filtering capabilities, you’ll never have an issue filtering for a finding. We have introduced a series of asset attribute-based filtering options, e.g. NetBIOS, Hostname and IP, to ensure that exception rules can be defined for any finding.
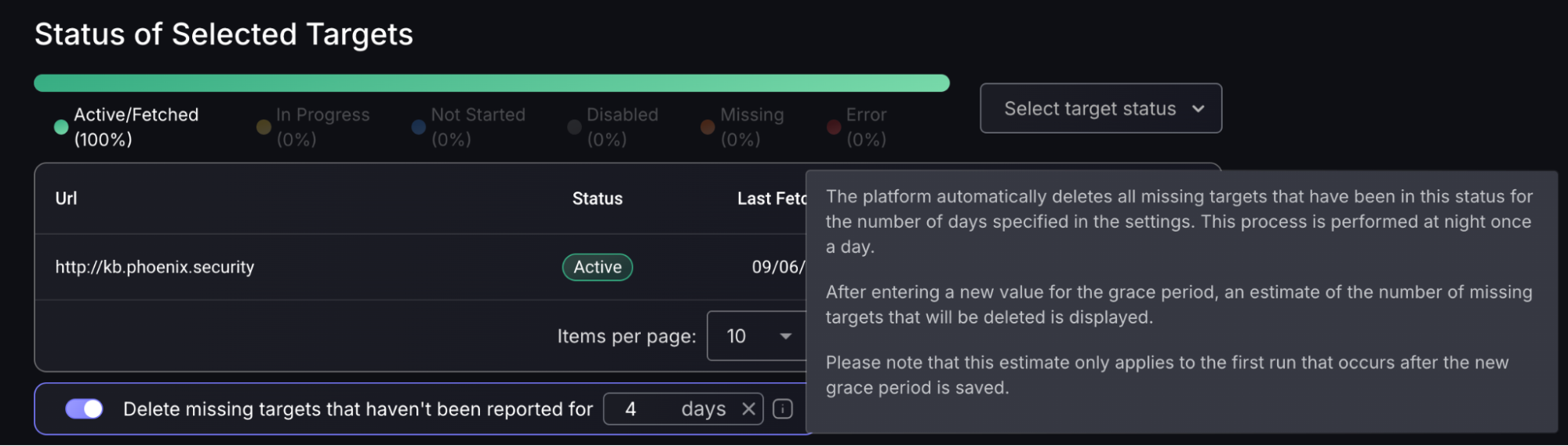
New lifecycle management for missing Scanner Targets
Phoenix Security has released another way to keep ASPM clean and focused on relevant and up-to-date information. Automate the deletion of missing targets using custom-selected grace periods to keep Security teams focused on the vulnerabilities that matter most. This feature will automatically declutter obsolete missing targets, ensuring scanner targets are up to date and not displaying outdated vulnerabilities.
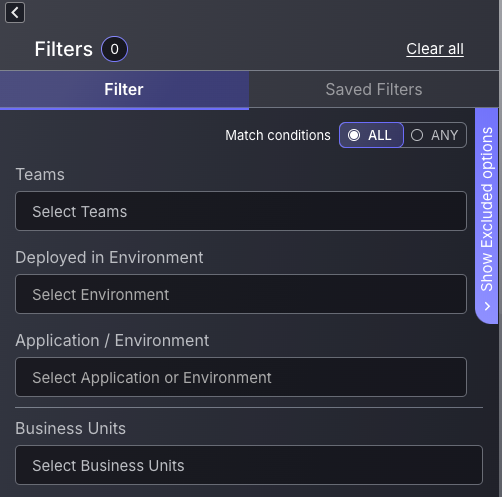
New matching conditions for Findings filters
At Phoenix Security, we never fail to introduce innovative ways to approach vulnerability management. Searching for a specific group of findings can be a long and tedious process, which is why we have made it as simple and efficient as possible. Use our new ALL/ANY matching conditions to filter findings based on your specific preferences. The “ALL” condition acts as an AND condition, meaning findings displayed will only be shown if all filtering options selected have been met. The “ANY” matching condition acts as an OR condition, meaning findings displayed will be shown if at least one of the filtering conditions has been met.
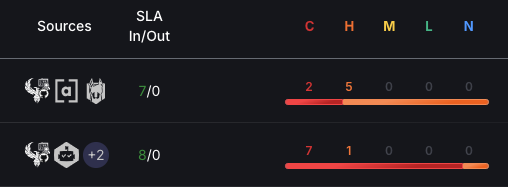
New Severity distribution bars in Vulnerability table
The new severity distribution bar is your ultimate weapon for prioritising threats with laser focus. At a glance, it transforms complex vulnerability data into a clear, colour-coded bar highlighting critical, high, medium, low, and negligible risks. This streamlines your vulnerability management process by providing a clear colour-coded representation of the criticality of each vulnerability. Each numeric value within a criticality grouping represents a finding, giving you insight into the criticality of specific findings within a vulnerability.
Integrations
As usual with every Phoenix release, a new set of native API integrations the extensive list already available out of the box.
Fortify SSC Scanner Integration
A new addition to the WEB scanner line-up included in this release is Fortify SSC.
Customers using Fortify SSC as part of their security scanning would be able to integrate with their account using Phoenix’s native API-based integration.

Aikido Security Scanner Integration
with this release, customers using Aikido Security as part of their security scanning would be able to integrate with their account using Phoenix’s native API-based integration.

Orca Security Scanner Integration
A new addition to the Phoenix scanner integration line-up included in this release is Orca Security.
Customers using Orca as part of their security scanning would be able to integrate with their account using Phoenix’s native API-based integration.

Others Enhancements
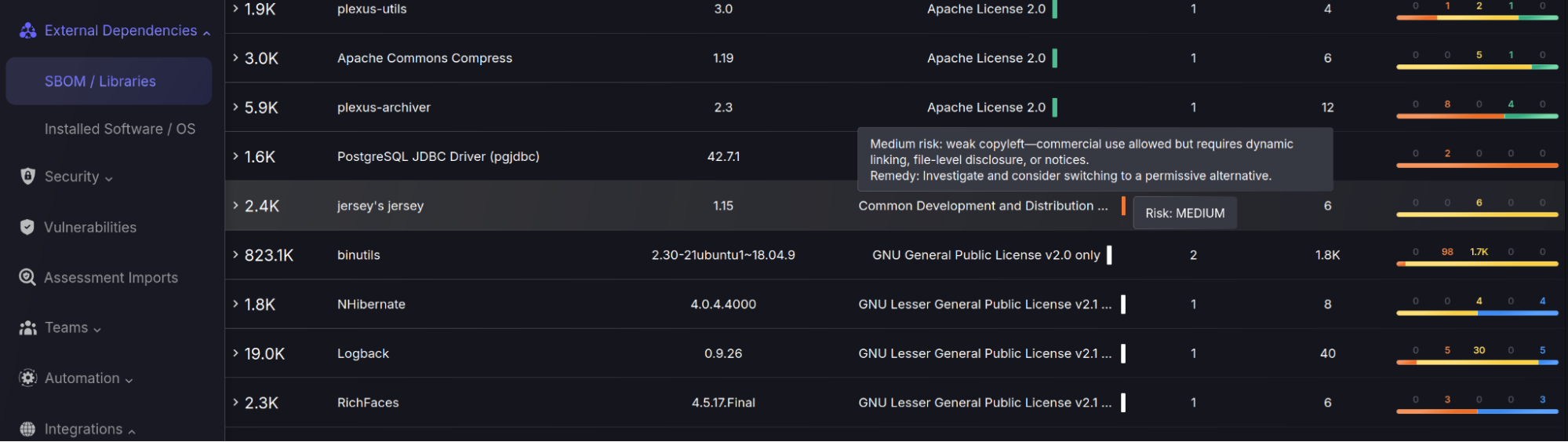
License information for SBOM/Libraries
Keep up to date with legal and organisational policies with the new Licence column in the SBOM libraries table. Licence criticality is even indicated by colour-coded tiles, with a breakdown of the key information of the selected Licence and remediation actions recommended to be taken, such as switching to a better alternative. This transparency helps mitigate risks of unintentional license violations and supports informed decision-making when selecting or updating components.
Get in control of your Application Security posture and Vulnerability management
🔐 Why It Matters
This release solidifies Phoenix Security’s position as a leading ASPM platform by delivering:
- Greater visibility across the application lifecycle
- Smarter prioritization powered by real-time SLAs, lineage, and context
- Cleaner vulnerability management with automated lifecycle control
- Deeper integrations with industry-standard tools and scanners
Organizations embracing Phoenix Security can now align their security operations more tightly with engineering workflows, transforming vulnerability management from reactive to predictive.