October 2024 – Phoenix Security ASPM proudly unveils its latest innovation, the “One Backlog” feature, designed to empower security champions, application security teams, and vulnerability management professionals. This new feature provides a streamlined approach to managing vulnerabilities by creating a single, prioritized backlog tailored to each team. Whether managing application security, cloud security, or a full-stack view, the One Backlog feature enables organizations to address vulnerabilities more efficiently and effectively.
Version: 3.27
Release Date: 7 October 2024
With the team constantly fighting a barrage of findings from application security to cloud security, increasing complexity, this ASPM feature ensures that vulnerabilities are attributed to the right teams, enabling faster resolution, improved risk reduction, and better collaboration between development, security, and operations teams.

With Phoenix Security ASPM One Backlog and Phoenix Security One Team, we want to encourage clarity for engineers and help collaboration between the Security team and the engineering team towards remediation of systemic vulnerabilities. The team feature will pair with the major release of the Vulnerability workflow and remediation campaign in line with CISA recommendation to fix systemic vulnerabilities in the latest CISA Pledge and NCSC recommendations for vulnerability management.
The recent integration between Phoenix Security ASPM and Sysdig, GCP, and upcoming features like vulnerability campaigns and contextual threat intelligence will supercharge the use of the Phoenix One Backlog feature.
Contents
TogglePhoenix Security ASPM’s One Backlog Graph
A single backlog and graph of the Application and Operational Environment guarantees a risk-based view of vulnerabilities regarding whether the team works in full ASPM full-stack mode with code and cloud or separately with Application security and CLoud/Operational Security


1. Single Backlog for Targeted Team Vulnerability Management
The new One Backlog feature allows security teams and security champions to manage vulnerabilities across different environments—including cloud, contextual, and application-level vulnerabilities—in one unified view. By consolidating all issues into a single backlog per team, security professionals can focus on what matters most without being overwhelmed by non-relevant vulnerabilities.
Whether your team is managing application security, cloud security, or both, the One Backlog ensures that all vulnerabilities are directed to the right team, allowing them to take ownership of their security landscape.
• Use Case: An enterprise security team managing cloud and on-premise assets can leverage Phoenix Security’s One Backlog feature to consolidate vulnerabilities. This unified backlog reduces confusion and ensures that vulnerabilities are accurately assigned to the appropriate team, whether they focus on cloud infrastructure, code, or hybrid systems.
The Security Team can switch between Cloud and non-cloud vulnerabilities for a single team saving filter and switching between tabs with the graph-based query system.
2. Contextual Attribution for All Vulnerabilities
Phoenix Security’s One Backlog consolidates vulnerabilities and enables dynamic team attribution. This powerful feature ensures that vulnerabilities from all sources—whether they are the result of manual findings, threat modeling, or automated scans—are automatically assigned to the relevant teams. The team attribution functionality spans across different asset types, including code repositories and cloud environments, ensuring comprehensive coverage.
• Use Case: A DevOps team using threat modeling to identify vulnerabilities early in the development process can now have those findings automatically attributed to their backlog, ensuring timely remediation and more effective cross-team collaboration.
3. One Backlog and ASPM for a Dynamic Attribution and Precise Asset and Vulnerability Visibility

The Phoenix Security Dynamic Attribution System enhances team efficiency by giving security teams granular control over which vulnerabilities and assets are visible to the right teams. This system allows teams to add or remove attribution based on various parameters and manage these actions programmatically, ensuring that the most relevant vulnerabilities are always assigned to the appropriate team. By dynamically adjusting attribution rules, security teams can continuously align their security strategy with organizational needs, ensuring optimal focus and resource allocation.

• Use Case: A security team managing multiple application layers can use dynamic attribution to adjust asset and vulnerability ownership programmatically. For example, a cloud security team can automatically adjust the backlog to reflect new cloud instances, removing irrelevant vulnerabilities as environments evolve.
4. Enhanced training for the team in full ASPM or by Application Security/Operational Security
The One Backlog feature also enables security teams to filter vulnerabilities and assets by team. Whether you’re managing a development team responsible for specific applications or a security team overseeing cloud infrastructure, you can filter down to the relevant vulnerabilities to your specific area. This precision allows teams to focus on what impacts their environment without distractions from unrelated issues.
• Use Case: A security champion managing cloud security can filter vulnerabilities down to those affecting their cloud assets, excluding irrelevant issues tied to other teams or systems.

The One backlog and precise team attribution also allow a precise review of the top issues introduced by the releases and tailor the training initiatives to the typical mistakes made.
ASPM and the ability to review the top trending mistakes to tailor the development team’s training
• Use Case: A security champion team tailoring the training program based on the typical issues introduced
5. Measuring Progress Toward Risk Reduction
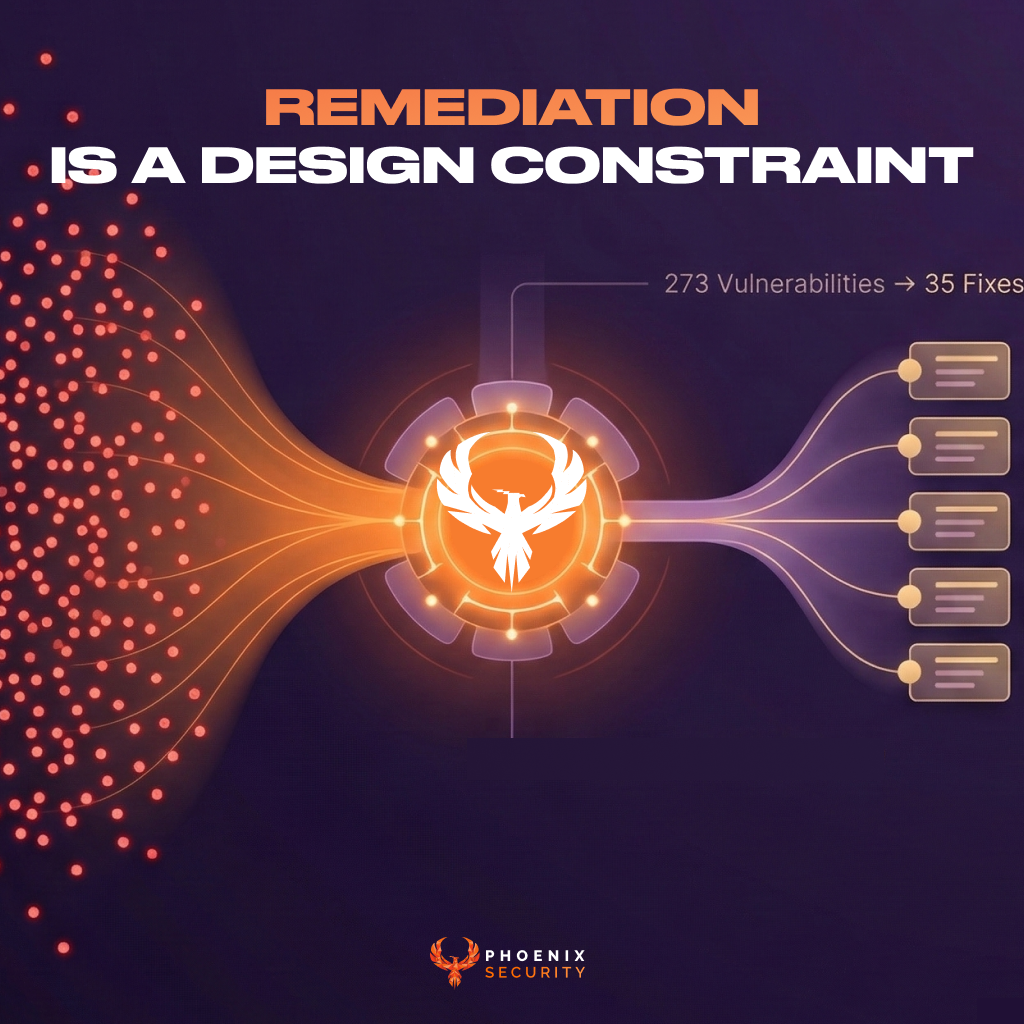
Phoenix Security’s One Backlog feature isn’t just about organization—it’s also about progress. By providing a single view of vulnerabilities for each team, security teams can easily measure their progress toward the ultimate goal: risk reduction. The platform recommends the vulnerabilities that, when resolved, will maximize risk reduction and help teams move swiftly toward a path to green.
• Use Case: A company aiming to reduce risk across its infrastructure can use the One Backlog feature to track progress toward risk reduction, ensuring that the most critical vulnerabilities are prioritized and resolved first.
5. Seamless Integration with Manual Findings, Exception Management, and Automation
This feature comes with full support for manual vulnerability findings and exception management, giving teams the flexibility to manage both automated and manual inputs. With upcoming automation features, security champions will be able to streamline their vulnerability management workflows even further, reducing manual effort and driving operational efficiency.
6. Dynamic Attribution and Upcoming Integrations
Phoenix Security’s dynamic attribution capabilities work hand-in-hand with the One Backlog feature, ensuring that assets and vulnerabilities are consistently mapped to the correct teams. Additionally, Phoenix Security has an upcoming integration with Backstage, an open platform for building developer portals. This integration will synchronize assets and vulnerabilities between Backstage and Phoenix Security, allowing for seamless alignment between the two platforms and ensuring that both are fully mapped to your organization’s structure
ASPM and One single Backlog for Real-World Client Benefits
Phoenix Security’s One Backlog feature is already showing results for our clients. Early adopters have reported:
• Increased efficiency: Organizations have seen up to 40% faster remediation times by consolidating vulnerabilities into a single, team-specific backlog.
• Improved collaboration: The dynamic team attribution feature has enabled smoother workflows between application security and cloud security teams.
• Enhanced risk management: Teams can now precisely track progress toward risk reduction, aligning security efforts directly with business goals.
Optimized for Security Champions and Application Security Professionals
With a focus on security champions and professionals managing application security and vulnerability management. The One Backlog feature is tailored to meet the needs of teams tasked with reducing security risks in complex environments. By streamlining vulnerability management workflows, Phoenix Security ASPM helps teams focus on what matters most, drive meaningful risk reduction, and improve overall security posture.
If you’re looking to consolidate and optimize your application security and vulnerability management processes, Phoenix Security’s One Backlog feature is here to revolutionize your approach.
Would you like to explore more about how Phoenix Security’s One Backlog feature can help streamline your vulnerability management? Contact us today for a personalized demo.
These advancements allow security teams to streamline the vulnerability landscape by focusing on what truly matters—vulnerabilities that are actively exploitable in both code and running containers. This leads to significant noise reduction and a more targeted, efficient approach to remediation.
Get on top of your code and container vulnerabilities with Phoenix Security Actionable ASPM
Organizations often face an overwhelming volume of security alerts, including false positives and duplicate vulnerabilities, which can distract from real threats. Traditional tools may overwhelm engineers with lengthy, misaligned lists that fail to reflect business objectives or the risk tolerance of product owners.
Phoenix Security offers a transformative solution through its Actionable Application Security Posture Management (ASPM), powered by AI-based Contextual Quantitative analysis. This innovative approach correlates runtime data with code analysis to deliver a single, prioritized list of vulnerabilities. This list is tailored to the specific needs of engineering teams and aligns with executive goals, reducing noise and focusing efforts on the most critical issues. Why do people talk about Phoenix?
• Automated Triage: Phoenix streamlines the triage process using a customizable 4D risk formula, ensuring critical vulnerabilities are addressed promptly by the right teams.
• Contextual Deduplication: Utilizing canary token-based traceability, Phoenix accurately deduplicates and tracks vulnerabilities within application code and deployment environments, allowing teams to concentrate on genuine threats.
• Actionable Threat Intelligence: Phoenix provides real-time insights into vulnerabilities’ exploitability, combining runtime threat intelligence with application security data for precise risk mitigation.
By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains current and focuses on the key vulnerabilities.