Phoenix Security ASPM is proud to announce the latest integration with the Google Cloud Platform (GCP) Security Center, further enhancing our ability to provide top-tier Application Security Posture Management (ASPM). This integration complements our existing support for Microsoft Azure and Amazon Web Services (AWS), enabling comprehensive vulnerability management and contextualization across all three leading cloud providers.
version: 3.25.0
Release Date: 25 September 2023
Knowledge Base: GCP SCC Integration with Phoenix Security
Overview
In addition to GCP integration, we’re also expanding our capabilities with AWS and Azure Integration. This update allows Phoenix Security clients to monitor vulnerabilities across container images, running containers, and cloud misconfigurations. AWS and Azure join over 280+ existing integrations, offering seamless, contextual aggregation of security insights from code to cloud, providing deep security visibility across your Google Cloud infrastructure and beyond. 🚀
Why this feature?
By integrating with the GCP Security Center, Phoenix Security now empowers businesses using Google Cloud to ingest, prioritize, and manage vulnerabilities, expanding their ASPM capabilities. This integration, combined with AWS and Azure, enables our customers to monitor running containers and cloud misconfiguration alerts across GCP, AWS, and Azure, helping teams quickly prioritize and resolve vulnerabilities with a risk-based approach.
Key Features
Prioritized Vulnerabilities Across Container Images:
• Rank vulnerabilities in container images based on severity and impact.
• Make data-driven decisions to tackle the most critical issues first.
• Automatic tracking of application exposure across Google Cloud, Azure, and AWS.

Running Containers:
• Real-time monitoring and vulnerability assessment of running containers in GCP, AWS, and Azure.
• Ensure your containers in Google Cloud are as secure as a bank vault.
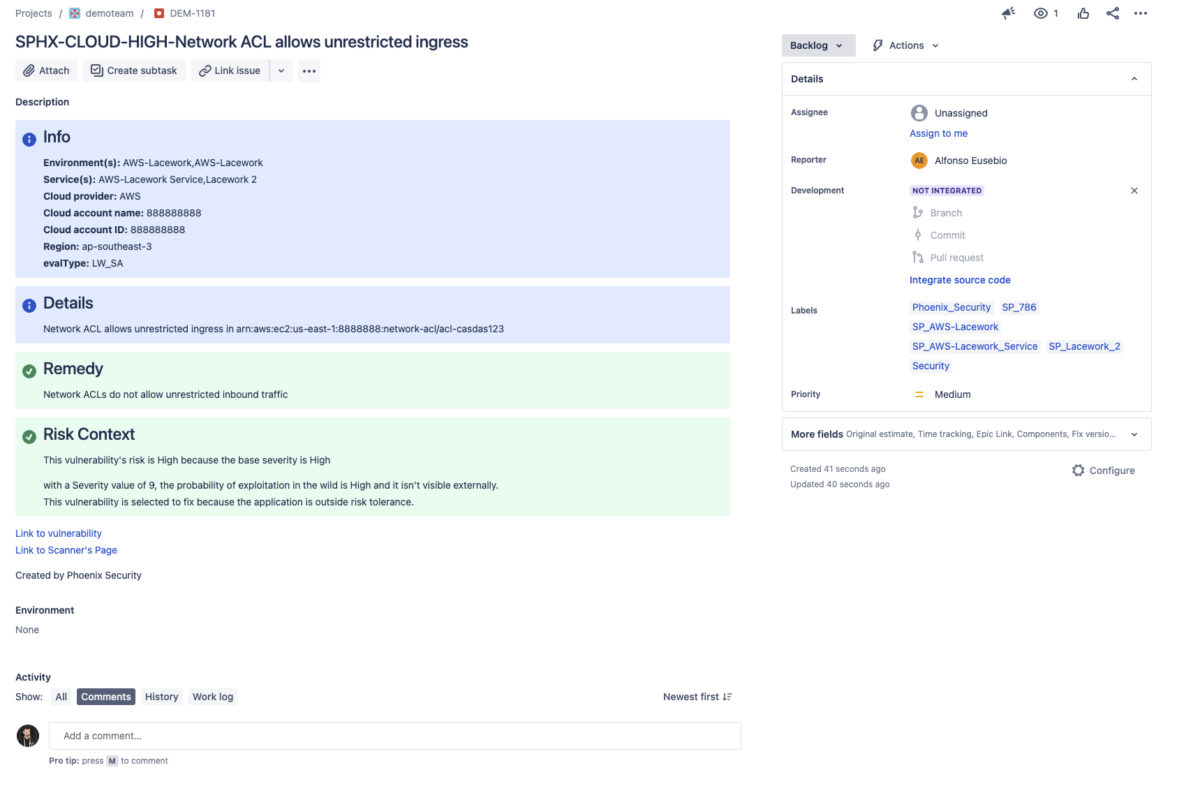
Cloud Misconfiguration:
• Detect and prioritize misconfigurations in Google Cloud Security Center, AWS, and Azure that could expose your infrastructure to security risks.
• Get actionable insights to secure your entire cloud environment.

Contextual Deduplication:
• Detect and prioritize duplicates in Google Cloud Security Center, AWS, Azure Laceworks, Wiz, Orca, Prisma Cloud, and more to reduce the noise of libraries deployed in the cloud. Only focus on O/S level vulnerabilities for containers that are controllable
• Get actionable insights on which vulnerability is fixable and not a duplicate
GCP Security Center Integration:
• Seamless ingestion, prioritization, and contextualization of vulnerabilities directly from Google Cloud Platform (GCP) Security Center.
• Enhance your ASPM strategy by managing vulnerabilities across Google, AWS, and Azure cloud environments in a single dashboard.
70+ Integrations Supported:
• Phoenix Security supports over 280 tools, including Google Cloud, Azure, AWS, and other integrations.
• Leverage contextual aggregation of data spanning from code to cloud across all major platforms, including Google Cloud Platform.
Why Choose Phoenix Security for GCP?
Phoenix Security provides a unified platform that simplifies ASPM across multiple cloud environments. With our integration into Google Cloud Security Center, you can rest assured that your vulnerabilities are prioritized, contextualized, and managed efficiently across Google, AWS, and Azure. Stay ahead of the curve with advanced insights that help you secure your cloud applications and infrastructure.
Additional Resources
For more detailed information on leveraging our new GCP Security Center integration, check out our GCP integration Knowledge Base (Coming Soon)
Support
Need assistance with the Google Cloud or GCP Security Center integration? Contact our support team at support@phoenix.security.
This version includes keyword optimization around GCP, Google Security Center, Google Cloud, and ASPM, while maintaining clarity and relevance.
Why this feature?
We integrated GCP container and cloud to allow our customers to monitor running containers and cloud misconfiguration alerts. Phoenix enables apps to be deployed and tracked in a container to understand the real risk-based prioritizing and how fast are team resolving vulnerabilities

Key Features
- Prioritized Vulnerabilities Across Container Images:
- Automatically rank vulnerabilities in your container images based on severity and impact.
- Make informed decisions on which issues to tackle first.
- Automatic tracking of application exposure
- Tickets tracking with aggregation of results
- Running Containers:
- Real-time monitoring and vulnerability assessment of running containers.
- Ensure your containers are as secure as a bank vault.
- Contextual Deduplication:
- Phoenix dynamically deduplicates containers from code to cloud
- Cloud Misconfiguration:
- Identify and prioritize cloud misconfigurations that could pose security risks.
- Get actionable insights to secure your cloud infrastructure.
- 280+ Integrations Supported:
- GCP becomes one of the 280+ integrations supported by Phoenix Security.
- Benefit from the contextual aggregation of data from code to cloud.
Additional Resources
For a comprehensive guide on leveraging this integration, check out our Lacework Integration with Phoenix Security
Support
Need help? Contact our support team at support@phoenix.security.





![Phoenix Security infographic: Claude Code Critical Vulnerability — CI/CD Nightmare, 3 Command Injection Flaws. Dark navy and orange background with circuit-board pattern. Center: terminal window showing attack chain [config] | [shell] | [exfil] with three red arrows pointing to attack targets — CI/CD Pipeline Compromise (top right), Cloud Key Exfiltration via AWS (middle right), and Developer Workstation Compromise leading to Server-to-Server lateral movement (bottom right). Phoenix Security logo at top. Bottom text: "CLAUDE CODE / CRITICAL VULNERABILITY / CI/CD NIGHTMARE / 3 COMMAND INJECTION FLAWS / Credential Exfiltration · CWE-78 · Confirmed / Shell Injection in CLI, Editor, and Auth Helpers."](https://phoenix.security/media/Gemini_Generated_Image_abcn46abcn46abcn.jpeg)