The Cloud Security and AppSec teams at Phoenix Security are pleased to bring you another set of new Phoenix Security Features and improvements for vulnerability management across application and cloud security engines. This release builds on top of previous releases with key additions and progress across multiple areas of the platform.
We are sure that you’ll find these quite interesting!
- Manage your Vulnerabilities and Assets
- Filter Vulnerabilities by Asset & Vulnerability Tags
- Export Vulnerabilities page in CSV
- Remove Tickets from External Platforms
- Enhanced linking of Teams to Apps and Envs
- Enable multi-selection in more filters
- Risk-based Posture Management
- Advanced Risk Configuration
- Updated EPSS factor in risk calculation
- Productivity and User Experience
- Updated Vulnerability Detail Views
- More reactive UI: asynchronous operations
- Improved display of existing asset selection rules
- Integrations
- Improved Github Integration
- Improved Snyk Integration
- Improved Qualys Infra Integration
- Improved Nessus Integration
- Improved Rapid 7 Integration
Manage your Vulnerabilities and Assets across application security and cloud security.
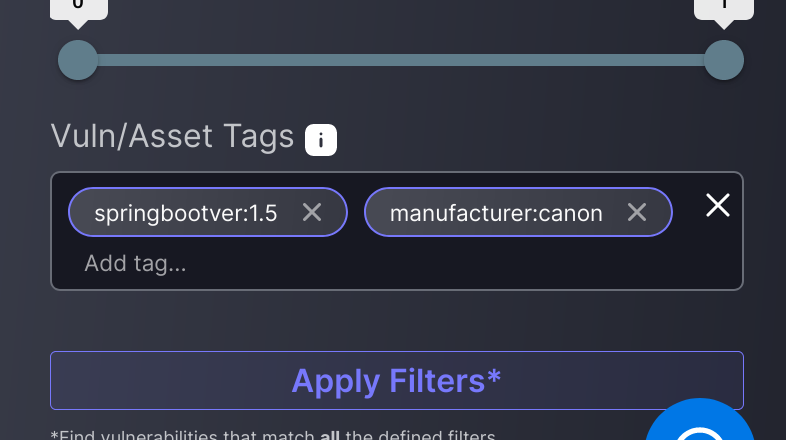
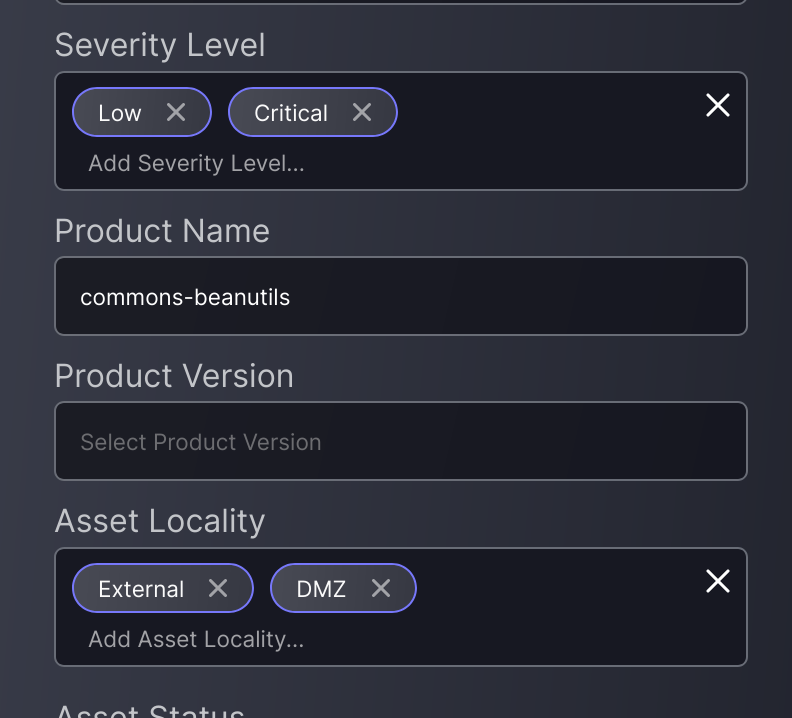
Filter Vulnerabilities by Asset & Vulnerability Tags
Being able to filter vulnerabilities by tag is a flexible and powerful tool, but sometimes the most interesting tags are associated with the asset, rather than the vulnerability. That’s why now you have filters by both asset and vulnerability tags in the Vulnerabilities screen. Happy filtering!
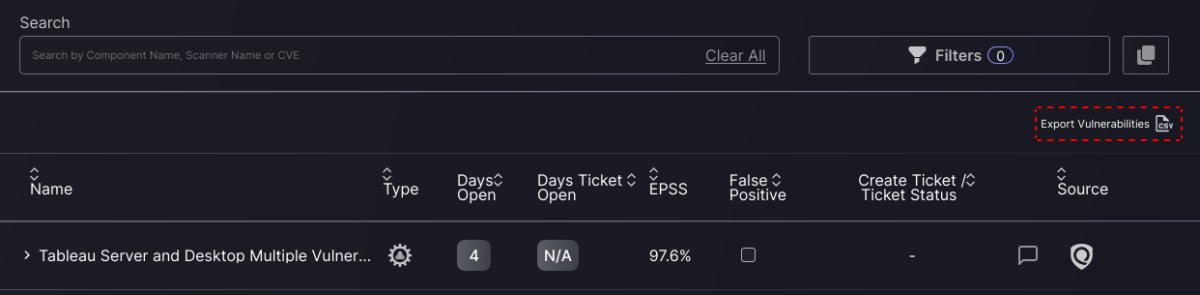
Export Vulnerabilities page in CSV
Even though the extraction of information from the Phoenix platform hinges on the use of the API, we recognise that sometimes it’s easier or more useful to get a quick “snapshot” from the list of vulnerabilities already filtered in the user interface.
Now users can export the list of vulnerabilities – the current selection and page – as a CSV file for further processing and sharing.
Remove Tickets from External Platforms
At Phoenix Security we are quite cautious when it comes to deleting stuff, especially if that stuff lives on an external platform. However, being able to manage vulnerabilities from a centralised platform is one of the main reasons why users come to Phoenix, and that includes getting rid of stuff when it’s not required any more.
In this case we are talking about issue tickets created on external platforms (e.g. Jira, ADO, GitHub, ServiceNow). Now users can choose to delete the actual ticket on the external platform when they delete tickets in Phoenix, either manually or through the removal of a workflow integration.

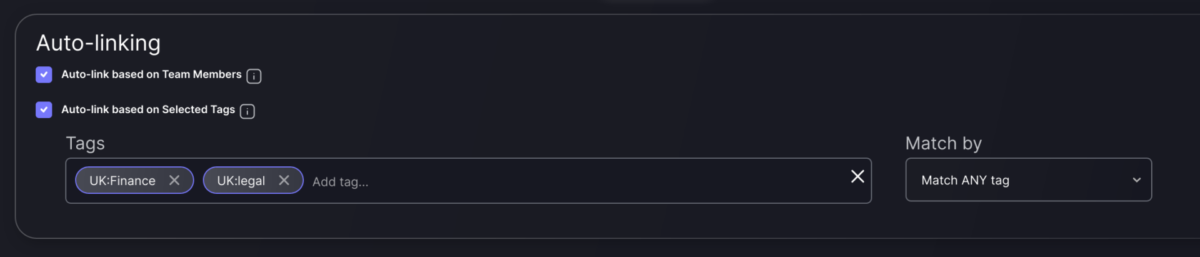
Enhanced linking of Teams to Apps and Envs
So far it was fairly straightforward to add applications and environments to your teams: just find the entity you want to add – potentially using tags search to find it – and then add it to the list.
Now this process has gained additional flexibility and power. You can dynamically assign Apps and Envs to the team by selecting a set of tags; the platform will ensure that any application or environment that matches those tags is linked to the team.
Not only that, but you can now also link applications and environments to Teams through the users that are responsible for them. By selecting this option, any Apps/Envs that team members are responsible for (App/Env configuration) will be automatically linked to the team.
Enable multi-selection in more filters
Continuing with the filtering improvements, now users can easily select multiple values within the same category where it makes sense. This capability was present in some filters and has now been extended to even more of them.
Risk-based Posture Management
Advanced Risk Configuration
One of the cornerstones of the Phoenix platform is the contextualised calculation of risk for each vulnerability. This involves several factors like the Impact of the application affected by the vulnerability or the asset’s Locality (internal vs external).
These factors influence the final risk calculated in different proportions or weights, which the platform has previously predetermined. Now users can alter those weights to reflect the different levels of sensitivity of the organisation to each factor.
Not only that but users can “fine tune” those factors by observing how they modify the risk calculation for a set of vulnerabilities with different severities, impacts, localities, etc.

Updated EPSS factor in risk calculation
As part of our improvements to the risk calculation formula, we have modified the EPSS factor by fine-tuning its impact on the final risk. This better reflects the level of exploitability the EPSS represents.
Productivity and User Experience
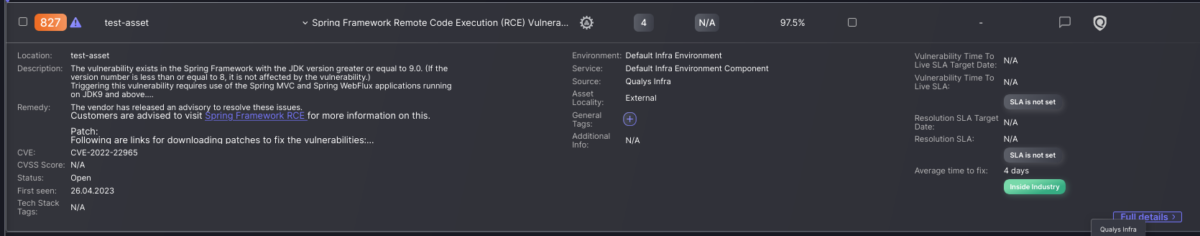
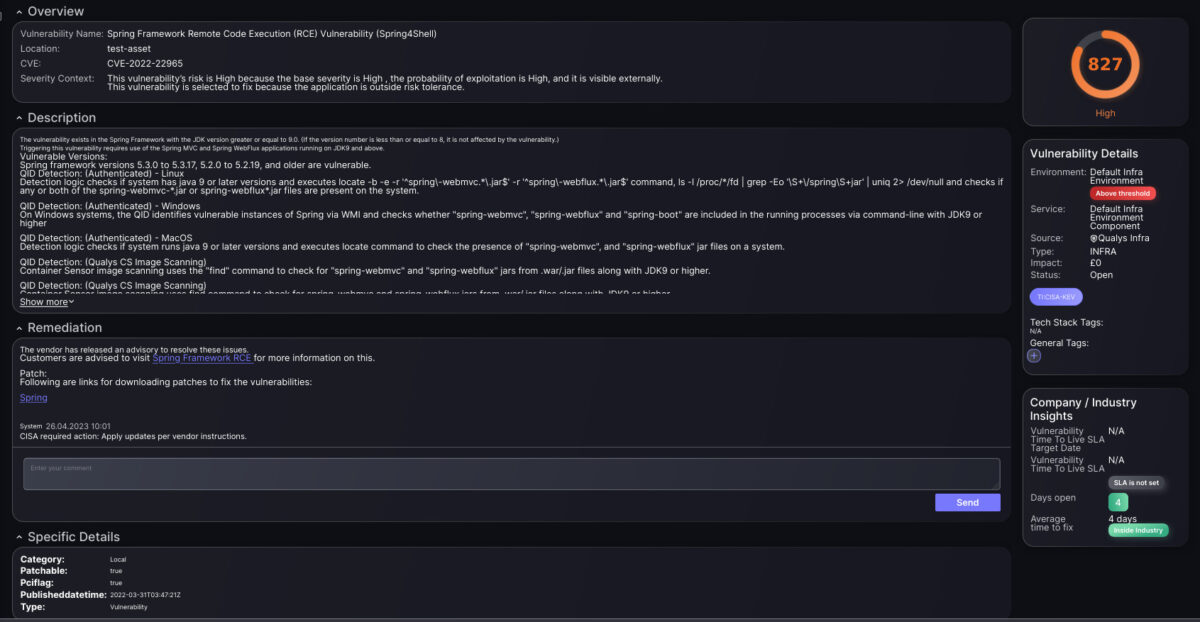
Updated Vulnerability Detail Views
Our users have spoken, and we have listened. Through our constant engagement with users and stakeholders, we have identified several improvements to the vulnerability details display (partial and full views). These changes aim to make it even easier for engineers to have all the information they require where it’s easier to see at a glance.
More reactive UI: asynchronous operations
Phoenix Security platform performs several processing steps for information around assets and vulnerabilities. This means that each change in asset grouping involves updates to components, applications, environments, etc.
To ensure that UI actions provide immediate feedback while maintaining the sophistication of the internal recalculations, we have made some interactions asynchronous. In other words, the change (for example, creating a new Component directly from a list of assets) is captured and confirmed immediately; however, some of the action’s consequences would occur in the background. This is communicated so that users know what to expect.
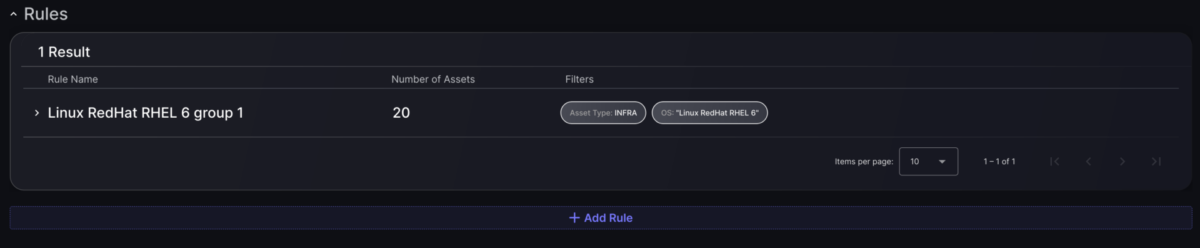
Improved display of existing asset selection rules
Other visual improvements have been made to display asset selection rules defined for components and services. Now there is more consistent and detailed information about the rules already created.
Integrations
Improved scanner interaction
Each scanner has a different API, and a different approach as to how it’s assets and vulnerabilities can be fetched for it. In practical terms, this means that we have to deal with many different situations and look for strategies to optimise how we interact with each scanner.
Especially for those scanners with high numbers of assets (e.g. Infra and Cloud), breaking down the interaction in smaller, more manageable chunks brings benefits in terms of speed, resilience and user experience.
In the last few months, we have been improving our interaction with Tenable.io, Qualys VM and Rapid7 scanners. All of them are key elements within our client’s vulnerability discovery toolset.