The Cloud Security and AppSec teams of Phoenix Security Cloud are pleased to bring you another batch of functional additions and improvements. This release is packed full of key additions across multiple platform areas.
We are sure that you’ll find these quite interesting!
- Explore your Assets and Posture
- Pre-fetch assets & vulns from integrated scanners
- Quick Time-to-value: Default App & Envs
- Asset Screens: add asset type-specific filters
- Enhanced hierarchy navigation and summaries
- Display unassigned assets in the Assets pages
- Risk and business modelling
- Flexible definition of components in Apps and Envs
- Improved Risk Formula: ACT-ON
- Transfer of locality from Environment to App
- Asset Locality based on Rules
- Improved import of Assets and Vulnerabilities
- Integrations
- Sonatype IQ server
- SonarQube
However, this time around, we are releasing these features as part of a preview initiative. Customers interested in getting their hands on these enhancements and additions can register using the form at the bottom of this post.
Explore your Assets and Posture
Pre-fetch assets & vulns from integrated scanners
We strive to provide value to our users as soon as they use the platform. To do this, we have changed how we interact with their scanners. We start pre-fetching asset and vulnerability information as soon as the scanner credentials are configured on the platform. This allows us to start modelling the organisation’s state within minutes of sign-up, presenting an initial overview of assets and vulnerabilities and the organisation’s risks as soon as they are fetched from the scanners.
Quick Time-to-value: Default App & Envs
Leveraging the above point is one of the latest additions to the platform: the automatic creation of Default Applications and Environments to capture any and all assets that are not included in user-defined components. This provides several benefits:
- As soon as users connect to their scanners, the platform captures those assets into the Default components, providing a complete – if still not fully modelled – view of the organisation’s risk posture and security landscape.
- As users start carving out parts of the assets into their Apps and Envs, the default components still ensure that non-assigned assets’ impact is still considered when calculating the organisation’s risk posture.
- Furthermore, since Default components are just like normal ones (almost), they can be navigated and configured similarly.

Enhanced hierarchy navigation and summaries
With our Risk Explorer now, it’s easier than ever to navigate from the Application or Environment down to the individual asset and back.

Additionally, our Overview pages for these navigation levels have been improved and completed with consistent information and charts that focus on the item the user is interested in.
Display unassigned assets in the Assets pages
Now Applications and Environments are modelled by selecting flexible lists of assets that naturally map to the organisational view of the security landscape (see “Flexible definition of components in Apps and Envs” below).
However, it is important not to lose sight of those assets that are not yet mapped to any App or Env. That’s why our asset screens allow users to focus on “unassigned” assets to understand where the gap is.

Not only that, but when looking at all the assets, we mark every asset with a flag to indicate if it’s assigned.

Risk and Business Modelling
Flexible definition of components in Apps and Envs
One of the key evolutions of the platform has been breaking the scanner’s target boundaries. The organisation’s business applications and teams are not organised in line with the scanner’s view of the world, nor should their representation in the platform. Using flexible matching (or filtering) rules, users can define exactly what set of assets form part of a component or service – allowing them to model their state in whichever way best fits their organisation.

Improved Risk Formula: ACT-ON
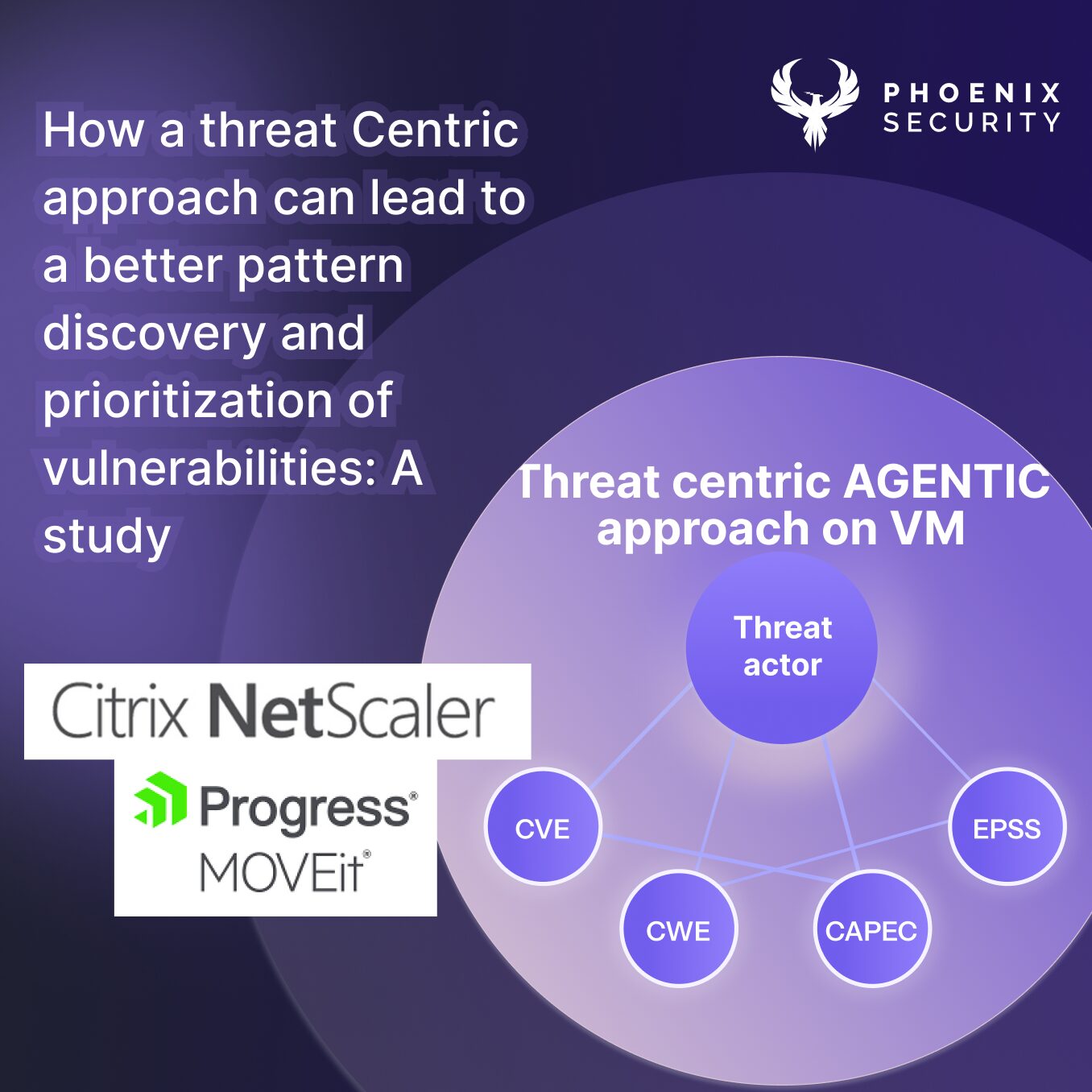
Evolution of our risk calculation to the current ACT-ON risk formula – Actionable Contextualized Threat. In previous posts, we discussed the former ARCTIQ (now ACT-ON Risk). Still, it’s important to highlight how we’ve evolved our risk calculation to better reflect the vulnerabilities and assets’ context and provide real-time actionable and quantifiable information that leverages threat intelligence sources. For example, exploitability information like EPSS plays an important role in determining the effective risk score of a vulnerability and hence the assets and components that contain it.

Transfer of locality from Environment to App
One of the cornerstones of our platform has always been the correlation of AppSec with Cloud and Infra, helping organisations get the proper context for their product vulnerabilities by ensuring that application vulnerabilities are evaluated within the context of where they run. This is why our risk calculation logic considers where applications are deployed and “transfers” the locality factor of the environment (how internal or external it is) to the deployed application.
Asset Locality based on Rules
With locality being such an important factor, we want to ensure that our users can easily define the value of the factor for every asset in the state. This provides a flexible and powerful way to set the locality value of an asset using rules based on its tags, IP address or any other attribute it might have. And, since there is always a common case, users can define the default value for all assets that are not matched by any explicit rule. All assets are always accounted for.

Improved import of Assets and Vulnerabilities
We place a big emphasis on automatic asset and vulnerability retrieval through native API integrations with scanners. However, there will always be weaknesses discovered through a manual process, whether regular pentests or ad-hoc security reviews. And we want to ensure that those vulnerabilities can seamlessly be integrated with those provided by scanners. This is why asset and vulnerability import is a key feature in Cloud Security Phoenix, with dedicated screens to define “assessments” (or engagements) and to keep track of previous imports. All this ensures that imported information is fully integrated into the platform’s features and flows.
Integrations
Sonatype IQ server
Users can now take advantage of the vulnerability reports created by Sonatype IQ Infra by using our native integration with the scanning platform.

SonarQube
Additionally, users can integrate with their SonarQube instances to retrieve vulnerability reports through the native API of the server.

Conclusion
This is a big release with a plethora of significant additions and improvements. Register now if you want to be the first to enjoy these features in preview mode.