The Cloud Security and AppSec teams at Phoenix Security are pleased to bring you another series of functionalities for vulnerability management and improvements. This release builds on top of our recent V3 release with key additions and improvements across multiple areas of the platform.
We are sure that you’ll find these quite interesting!
- Manage your Vulnerabilities and Assets
- Risk and business modelling
- Add domain (FQDN) to the set of filters in Software context rules.
- Updated risk formula better captures Application criticality
- Integrations
- Other improvements and features
Manage your Vulnerabilities and Assets across application security and cloud security
Provide additional details in the vulnerability tickets
We want to make engineers’ live as easy as possible, and one important part of that is ensuring that they can continue working with their everyday tools while enjoying the benefits of Phoenix Security.
In this release, we have increased the details included in the issue tickets created by Phoenix Security so that engineers don’t have to leave their favourite workflow tools to gather information about the vulnerability and its resolution. There are still some links to extended information that we include in the ticket, but the key data should now be present directly in the ticket description.
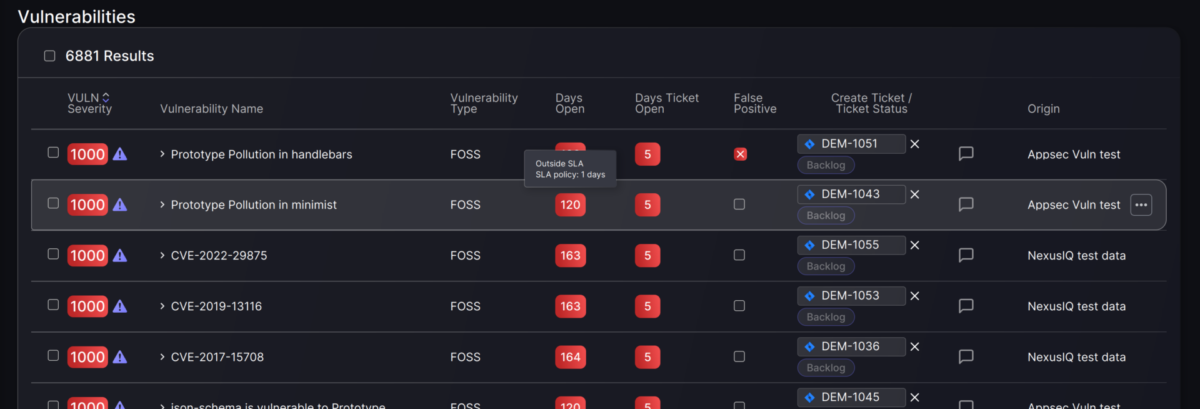
Improve timing and SLA information in the Vulnerabilities list
In an information-rich platform like Phoenix Security times, it’s challenging to balance the level of detail and clean user interfaces. However, we keep trying to hit the sweet spot, and this time we have focused on the timing and SLA information displayed on the Vulnerabilities page.
Now you have a consolidated view of the time that a vulnerability has been open and it’s ticket created while receiving clear indication and details of the status of the vulnerability with regards to defined SLAs.
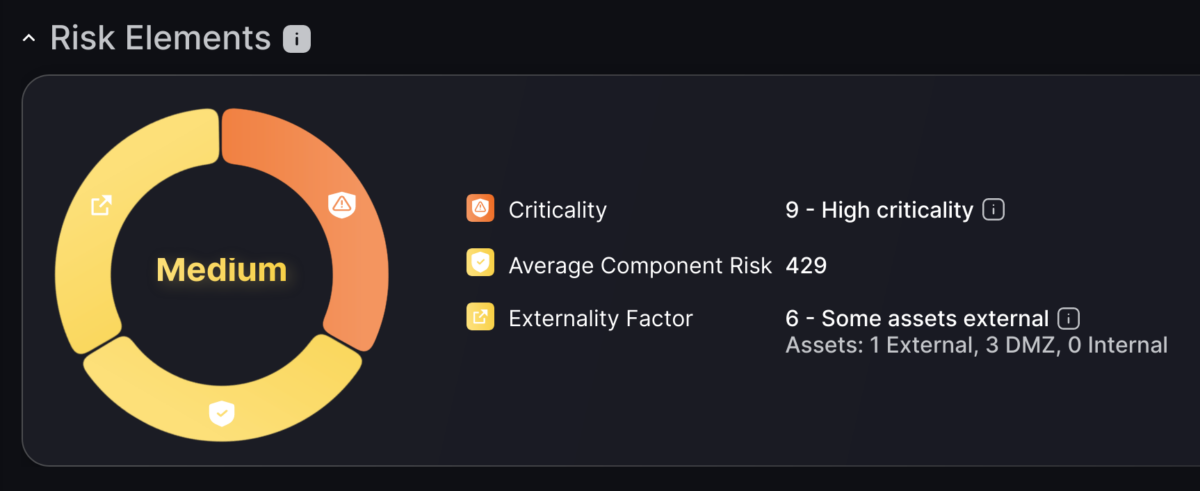
Update Risk Elements and Impact information display.
With the improvement of the risk formula during our V3 release cycle, we introduced and updated adjustment factors at different levels of the calculation. In line with those changes, we are updating our information display to reflect better the key elements that conform to the risk calculation.
Evolve reporting functionality
Phoenix Security is primarily a real-time risk exploration platform; however, there are times when a snapshot report is necessary for external communication. We are in the process of updating our PDF reporting infrastructure and have, temporarily removed this feature from the front until it’s fully updated.
Risk and Business Modelling
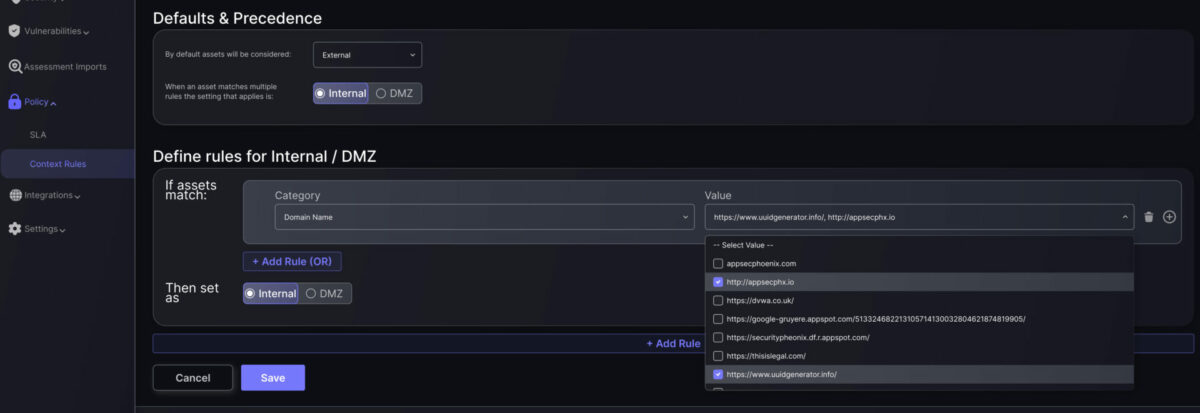
Improved filters in Software context rules
Now you can use the domain name (FQDN) as part of the Context Rules for software assets. These rules make it easy to define the locality (Internal, External, DMZ) of assets based on their attributes.
Updated risk formula better captures Application criticality
In our constant quest to refine our risk calculation, we have adjusted the weight and range that the application criticality (impact) factor has on vulnerability risk. This ensures that vulnerabilities affecting critical applications get a larger risk uplift, in line with expectations.
Integrations
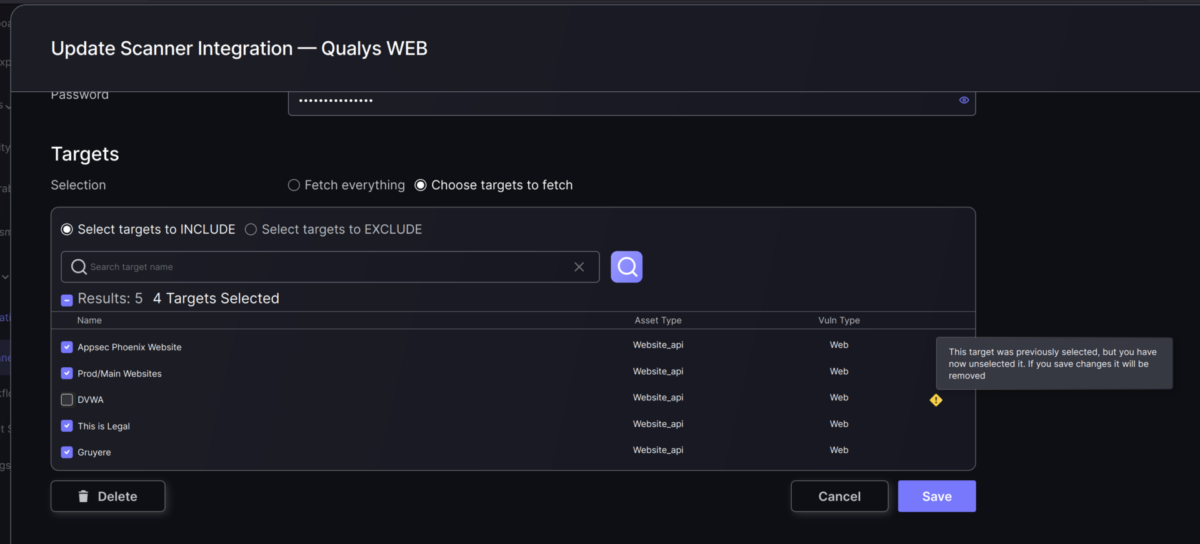
Ability to select scanner targets when creating integrations
Phoenix Security is all about gathering and consolidating any assets and vulnerabilities your organisation is already detecting through scanners. However, there are times when some of the projects or targets included in the scanning are not relevant for day-to-day vulnerability and risk management.
This is where another of our key principles comes into play: avoid noise and duplication. And with this release, users can select exactly which scanner targets (projects, applications, etc.) are ingested by our engine. This is as simple as selecting to fetch all targets, only those specifically selected or all of them except for a few exclusions, whatever suits your use case.
Notify users if they reach their asset license limit
With the release of V3, much of the interaction with the scanners happens asynchronously in the background. This is necessary in order to properly manage the volumes of data that our clients have, but it makes feedback loops a bit more complicated.
With this release, we have included a notification event whenever a client reaches their licensed asset limit during a background operation. The user will receive an email as well as an on-screen notification.
Outbound asset API (preview)
As a technical preview, we are releasing the initial implementation of our outbound API. If you are interested in this feature, please let us know so we can guide you through your specific use case.
Other improvements and features
Improve progress feedback in the frontend.
We are continuously working on improving our user’s experience, and this time around, we have focused on the “interaction feedback loop”. When our users interact with Phoenix Security’s front end, it’s essential that they know when the platform is working to provide the results of each interaction: vulnerability lists, data updates, etc. These might seem like a secondary feature of the platform, but letting the user know when she has to wait for a page or data refresh avoids confusion. Fortunately, these feedback elements (e.g. loading spinners) don’t spend too long on our screens!
Update 3-rd party dependencies in line with security policies
We are constantly updating our frameworks and libraries to ensure that they are free of vulnerabilities. Most of the time, these are just minor updates (patches) to individual components.
In this release, it was the turn of one of our key frameworks to get a significant update. This will ensure that we work with the latest and better-maintained version of the framework.