Overview
We’re excited to unveil a new evolved JIRA Integration with Phoenix Security, a game-changing solution designed to automate and optimize your vulnerability management workflow.
With features like Dynamic Backlog Management and Automatic Closure of Tickets, this integration is the cybersecurity equivalent of a Swiss Army knife. 🎉
With jira being one of the key places where the security team and development team interact we wanted to create a seamless experience where the application security team and vulnerability management team could work together with the development team in planning sprint, remediation campaigns and more
Release Note: JIRA Integration with Phoenix Security
Version: 3
Release Date: 25/10/2023
Knowledge Base: JIRA Integration with Phoenix Security
Why this feature?
We updated jira integration to enable security professionals be dynamic and not bogged down in ticket generation. Automating updates and ticket generation phoenix security empowers security professionals and developers to work seamlessly together. Cyber threat intelligence alerts are automatically delivered to team with comments and ticket are not left hanging if an asset disappears
Key Features

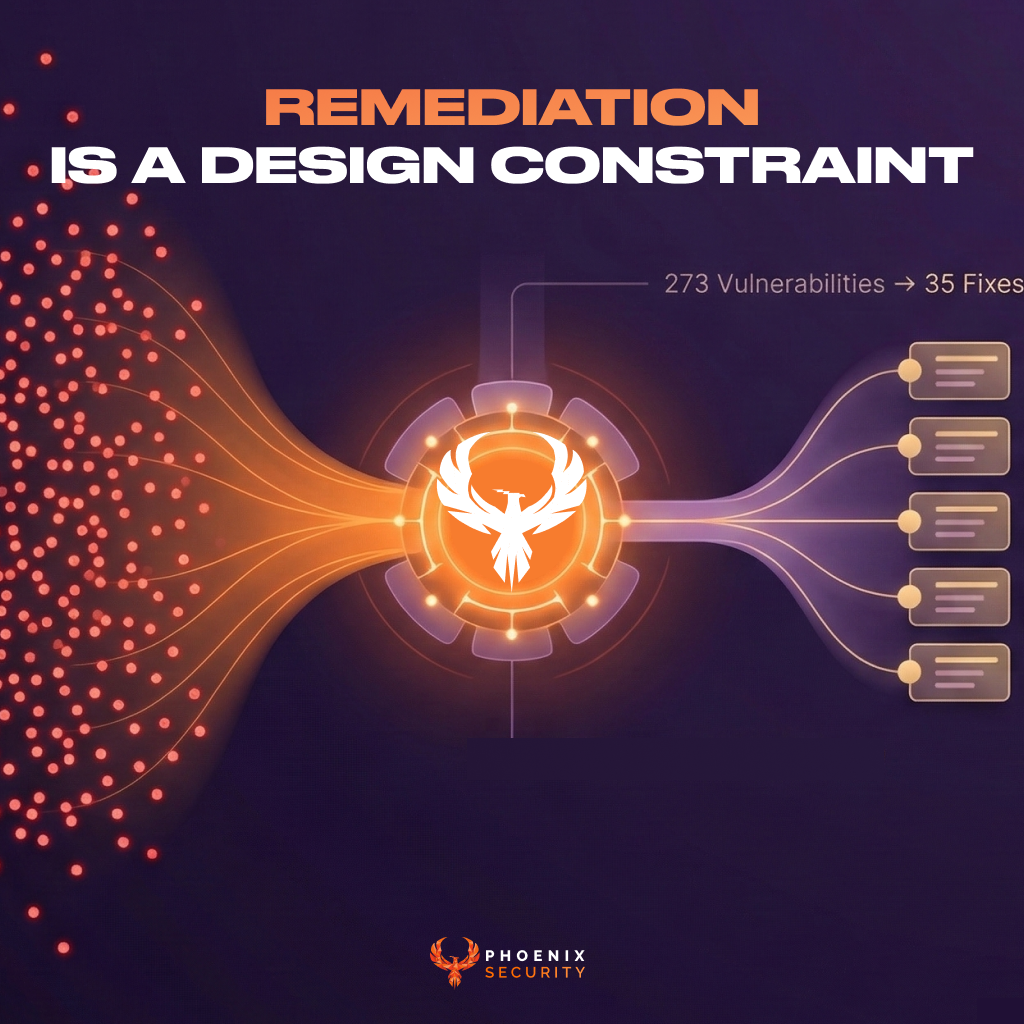
- Risk to actions
- Automatically prioritize vulnerabilities based on risk assessment.
- Real-time backlog updates to ensure you’re always ahead of the curve.
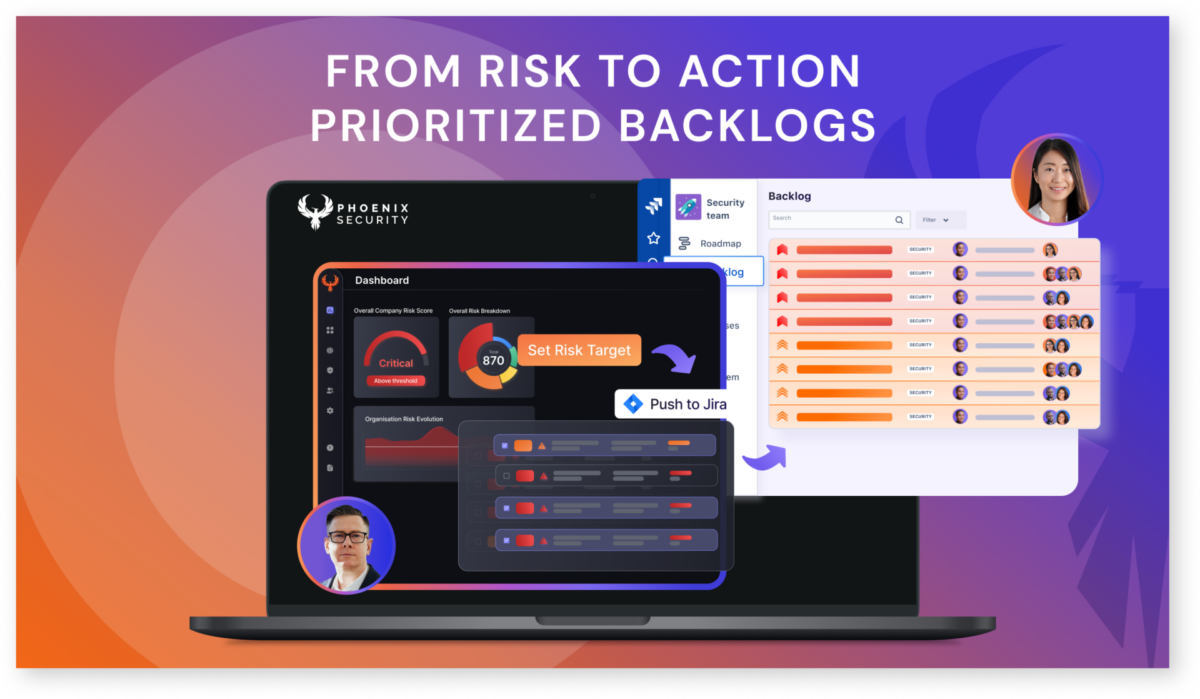
- Dynamic Backlog Management:
- Automatically prioritize vulnerabilities based on risk assessment.
- Real-time backlog updates to ensure you’re always ahead of the curve.
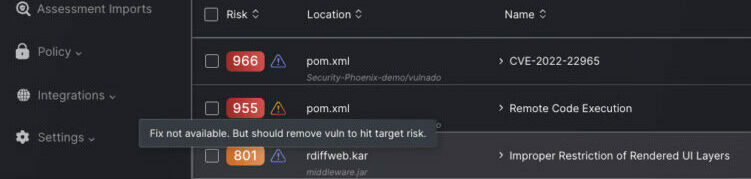
- Automatic Closure of Tickets:
- Risk-accepted vulnerabilities trigger automatic ticket closure.
- Automatic ticket generation based on risk targets
- Say goodbye to the tedious manual process of closing tickets.
- stop the generation of tickets if a vulnerability is not fixable
- Monitoring and Tracking Resolution of Vulnerabilities:
- Receive real-time status updates for each vulnerability.
- Stay in the loop with instant notifications for risk level changes.
- Projected Resolution Time:
- Accurate estimates for vulnerability resolution times.
- Make data-driven decisions for your upcoming sprints.
- Limiting Ticket Overflow:
- Control the number of generated tickets to prevent backlog overflow.
- Because nobody likes a ticket tsunami. 🌊
- Link Back to Vulnerabilities:
- Directly link JIRA tickets back to the corresponding vulnerabilities in the Phoenix Security dashboard.
- One-click navigation for seamless vulnerability management.
- Automatic update when new threat intel becomes available
- Phoenix security automatically updates tickets with new threat intelligence information and comments
- Different SLA and tracking methodologies to measure SLA timers from ticket creation

Additional Resources
For a comprehensive guide on leveraging this integration, check out our Knowledge Base.
Support
Need help? Contact our support team at support@phoenix.security.