With a very large deployment base F5 Big IP and CVE-2023-46747, remote code execution vulnerability has scared both application security professionals and vulnerability management network teams.
With recent exploitation of atlassian, Cisco, Curl, Http/2, and many other the end of the year feels like an endless sprint, except the hurdles are Zero-Day vulnerabilities, and the runners are cybersecurity professionals. F5 recently issued a warning about active abuse of a critical security flaw in its BIG-IP systems. Tracked as CVE-2023-46747 with a CVSS score of 9.8, this vulnerability is no laughing matter. In this blog, we’ll dissect the vulnerability, its exploitability, and the threat intelligence surrounding it.
Contents
ToggleThe Vulnerability: CVE-2023-46747
The CVE-2023-46747 vulnerability allows an unauthenticated attacker with network access to the BIG-IP system through the management port to achieve code execution. It’s like leaving your front door open with a sign that says, “Come on in, the coffee’s hot!”—except instead of coffee, it’s your system’s security at stake.
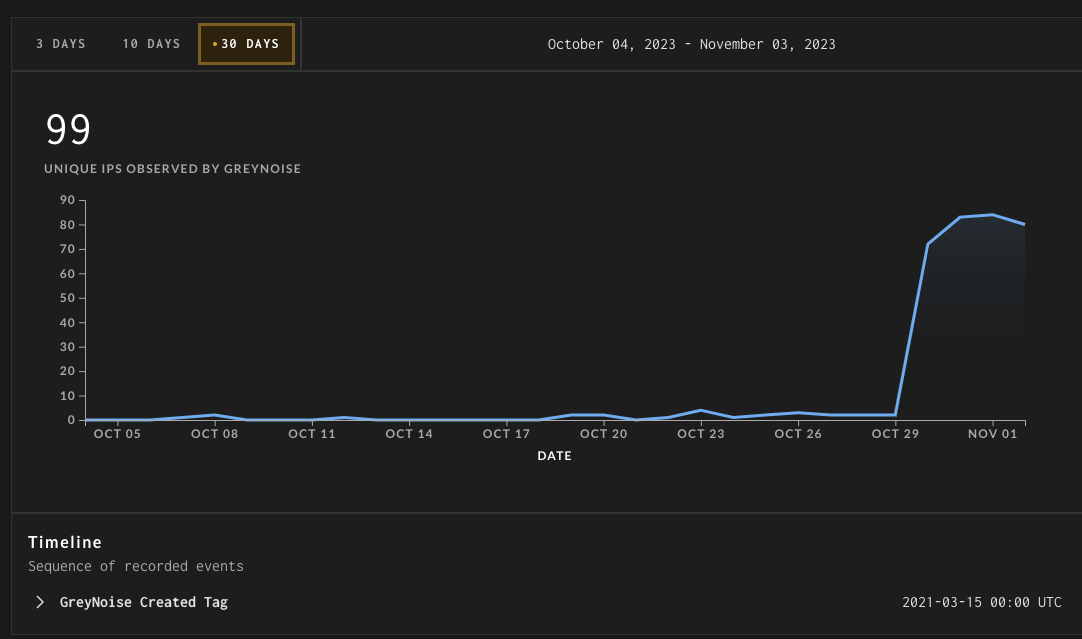
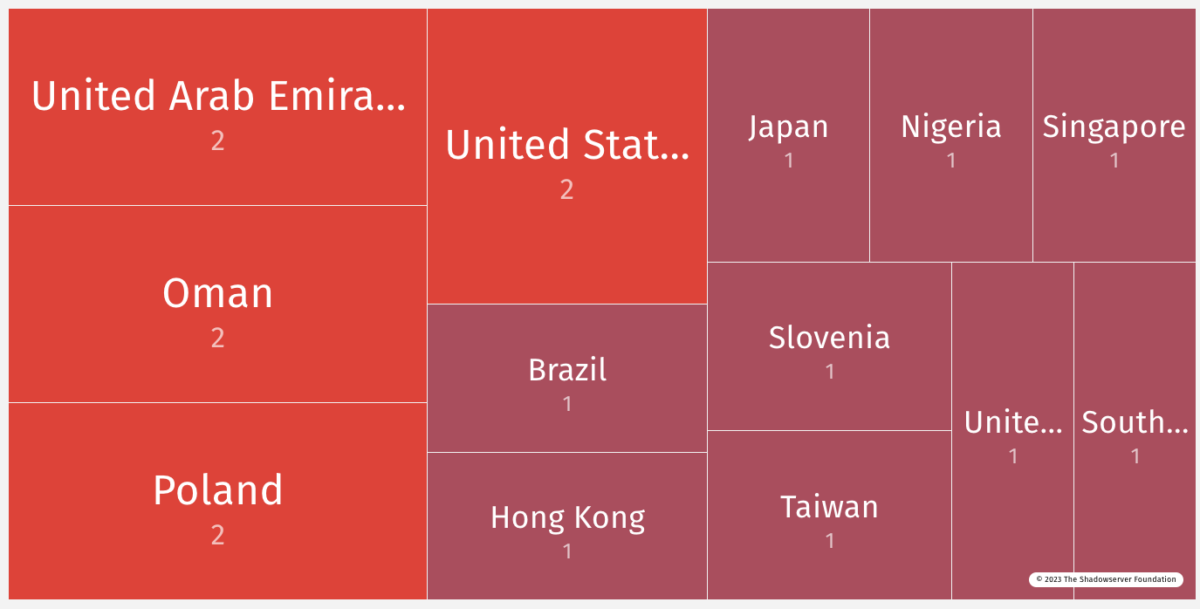
Shadowserver message of increased exploitation
Not surprisingly given its inclusion in the Nuclei scanner, since Oct 30th we are seeing F5 BIG-IP CVE-2023-46747 attempts in our honeypot sensors. Make sure to review your system for signs of compromise and patch before more threat actors jump in: https://my.f5.com/manage/s/article/K000137353
Affected Versions for CVE-2023-46747
- 17.1.0 (Fixed in 17.1.0.3 + Hotfix-BIGIP-17.1.0.3.0.75.4-ENG)
- 16.1.0 – 16.1.4 (Fixed in 16.1.4.1 + Hotfix-BIGIP-16.1.4.1.0.50.5-ENG)
- 15.1.0 – 15.1.10 (Fixed in 15.1.10.2 + Hotfix-BIGIP-15.1.10.2.0.44.2-ENG)
- 14.1.0 – 14.1.5 (Fixed in 14.1.5.6 + Hotfix-BIGIP-14.1.5.6.0.10.6-ENG)
- 13.1.0 – 13.1.5 (Fixed in 13.1.5.1 + Hotfix-BIGIP-13.1.5.1.0.20.2-ENG)
The Exploit Chain: Exploit and CVE-2023-46747
F5 has observed threat actors exploiting this vulnerability in conjunction with CVE-2023-46748, an authenticated SQL injection vulnerability in the BIG-IP Configuration utility. It’s like a hacker’s version of a double espresso—two exploits for the price of one.
Threat Intelligence and Nation-State Actors exploiting CVE-2023-46747
The exploit chain is particularly concerning because it opens the door for Nation-State actors to execute arbitrary system commands. This is not just a vulnerability; it’s a potential geopolitical weapon.
Which Versions are Vulnerable to CVE-2023-46747?
F5’s advisory has clearly outlined the versions of BIG-IP that are vulnerable to this critical flaw:
- 17.1.0 (Fixed in 17.1.0.3 + Hotfix-BIGIP-17.1.0.3.0.75.4-ENG)
- 16.1.0 – 16.1.4 (Fixed in 16.1.4.1 + Hotfix-BIGIP-16.1.4.1.0.50.5-ENG)
- 15.1.0 – 15.1.10 (Fixed in 15.1.10.2 + Hotfix-BIGIP-15.1.10.2.0.44.2-ENG)
- 14.1.0 – 14.1.5 (Fixed in 14.1.5.6 + Hotfix-BIGIP-14.1.5.6.0.10.6-ENG)
- 13.1.0 – 13.1.5 (Fixed in 13.1.5.1 + Hotfix-BIGIP-13.1.5.1.0.20.2-ENG)
It’s like a cybersecurity version of Russian roulette, except you definitely don’t want to play.
Consequences of the CVE-2023-46747 Vulnerability
The vulnerability allows for unauthenticated remote code execution, rooted in the configuration utility component. F5 has emphasized that there’s no data plane exposure; this is a control plane issue only. In layman’s terms, it’s like having a flaw in the cockpit of an airplane but not in the passenger cabin—still catastrophic, but contained to a specific area.
Mitigations and Workarounds for CVE-2023-46747
F5 has provided a shell script for users of BIG-IP versions 14.1.0 and later. But heed their warning: “This script must not be used on any BIG-IP version prior to 14.1.0 or it will prevent the Configuration utility from starting.” It’s like using a sledgehammer to crack a nut—effective, but potentially disastrous if misapplied.The vulnerability CVE-2023-46747 is still unpatched.
Additional options:
Block configuration utility access trough self IP address or management interface to prevent CVE-2023-46747 exploitation
for the script: https://my.f5.com/manage/s/article/K000137353
Indicators of compromise
This information is based on the evidence F5 has seen on compromised devices, which appear to be reliable indicators. It is important to note that not all exploited systems may show the same indicators, and, indeed, a skilled attacker may be able to remove traces of their work. It is not possible to prove a device has not been compromised; when there is any uncertainty, you should consider the device compromised. For information about handling suspected compromised systems, please review K11438344: Considerations and guidance when you suspect a security compromise on a BIG-IP system.
All versions
F5 has observed threat actors using this vulnerability to exploit CVE-2023-46748. For indicators of compromise for CVE-2023-46748, please refer to K000137365: BIG-IP Configuration utility authenticated SQL injection vulnerability CVE-2023-46748.
Vulnerability Management and Application Security Measures
Given the critical nature of this flaw, vulnerability management and application security should be at the forefront of your cybersecurity strategy.
Indicators of Compromise (IoCs)
To check for IoCs associated with the SQL injection flaw in CVE-2023-46747 users are recommended to check the /var/log/tomcat/catalina.out file for suspicious entries like:
java.sql.SQLException: Column not found: 0.
sh: no job control in this shell
sh-4.2$ <EXECUTED SHELL COMMAND>
sh-4.2$ exit.To note
In the line of Column not found: 0, the 0 can be replaced with a different number.
In the line of <EXECUTED SHELL COMMAND>, the command will be replaced with a different command.
Exploitation details for F5 CVE-2023-46747
Details for CVE-2023-46747
- CVSS: 9.8
- CTI interest: Low 0.76 (low but increasing)
- RCE Type Remote: High, Access through HTTPS port (recommended disabling) with chance of Privilege escalation
- Exploit Availability: Yes
- Status: Disclosed
- EPSS Score: – a recent addition – 0.05214, date November 3 2023
With exploitation progress increasing and various targeted countries, the attention should be high according to Shadowserver foundation data)

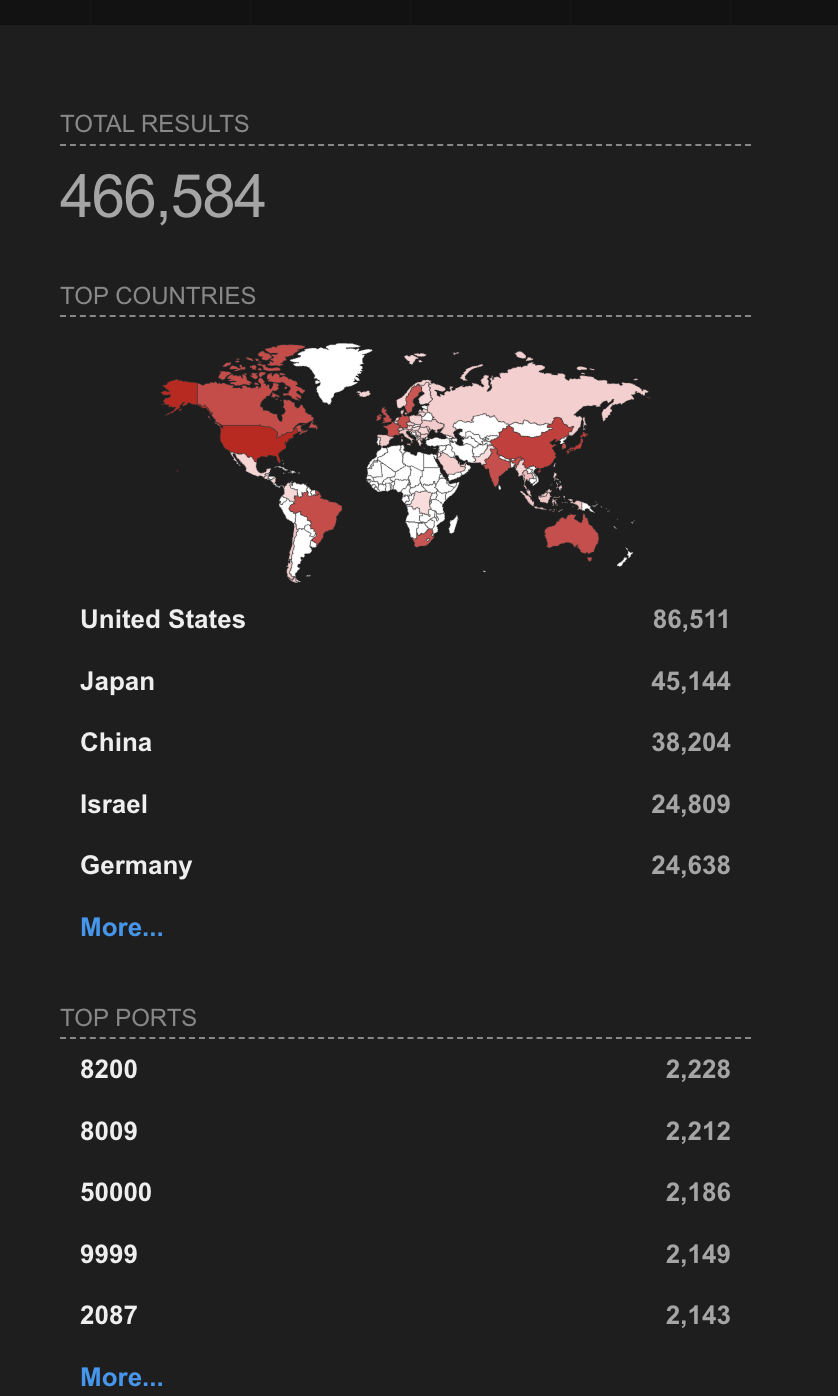
Currently, there are 466,584 big ip systems in the world according to shodan statistics (note a lot of those systems are used for honeypot
- Block Configuration utility access through self IP addresses
- Block Configuration utility access through the management interface
Credits and Additional Recommendations
Kudos to Michael Weber and Thomas Hendrickson of Praetorian for discovering and reporting this vulnerability. Their technical report describes the flaw as an authentication bypass issue that can lead to a total compromise of the F5 system. They also recommend restricting access to the Traffic Management User Interface (TMUI) from the internet.
Historical Context
It’s worth noting that CVE-2023-46747 is the third unauthenticated remote code execution flaw uncovered in TMUI, following CVE-2020-5902 and CVE-2022-1388. As the researchers pointed out, “A seemingly low impact request smuggling bug can become a serious issue when two different services offload authentication responsibilities onto each other.”
Conclusion
This vulnerability poc is actively exploited and templates as well as exploit evidence is widely available. The devil is often in the details—or in this case, the versions and mitigations. Understanding the nuances of each can be the difference between a secure system and a compromised one.
How Phoenix Security Can Help

Phoenix Security helps organizations identify and trace which systems have vulnerabilities, understanding the relation between code and cloud. One of the significant challenges in securing applications is knowing where and how frameworks like Struts are used. ASPM tools can scan the application portfolio to identify instances of Struts, mapping out where it is deployed across the organization. This information is crucial for targeted security measures and efficient patch management. Phoenix Security’s robust Application Security Posture Management (ASPM) system is adept at not just managing, but preempting the exploitation of vulnerabilities through its automated identification system. This system prioritises critical vulnerabilities, ensuring that teams can address the most pressing threats first, optimising resource allocation and remediation efforts.
The Role of Application Security Posture Management (ASPM):
ASPM plays a vital role in managing and securing applications like those built with Apache Struts. It involves continuous assessment, monitoring, and improvement of the security posture of applications. ASPM tools can:
- Identify and Track Struts Components: Locate where Struts is implemented within the application infrastructure.
- Vulnerability Management: Detect known vulnerabilities in Struts and prioritize them for remediation.
- Configuration Monitoring: Ensure Struts configurations adhere to best security practices.
- Compliance: Check if the usage of Struts aligns with relevant cybersecurity regulations and standards.
By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.
Get in control of your Application Security posture and Vulnerability management
Previous Issues of Vulnerability Weekly
- How to update curl and libcurl without panic fixing
- Critical Vulnerabilities in Atlassian Confluence: Zero-Day
- Detect & Mitigate HTTP/2: Rapid Reset Vulnerabilities
- Understanding the libcue Vulnerability CVE-2023
- Understanding and fixing Curl and libcurl
- CVE-2023-3519 Update on Critical RCE in Netscaler ADC (Citrix ADC) and Netscaler Gateway (Citrix Gateway) details on vulnerability timeline and compromise
- MOVEit Transfer breach, Zellis compromise CVE-2023-34362




















