Contents
ToggleVulnerabilities and the problem of scale for cloud and application security
Vulnerability management is the system or process of identifying, evaluating, treating, and reporting security vulnerabilities in systems and the software that runs on them.
Security professionals triage vulnerabilities daily and face the challenge of too many alerts coming from all parts of the organization and technology stacks.
According to the Verizon Data Breach investigation report, Vulnerabilities mismanagement is one of the four factors that leads to vulnerabilities.
According to research from the Ponemon Institute, 53% of companies spend more time navigating manual processes than responding to vulnerabilities.
Credit: EPSS – 35% more CVE declared yearly (source EPSS)
With the current trend of 35% more CVE declared yearly and security teams being unable to cope with the stress and quitting, 54% of security professionals are considering a career change; it is ever more important to focus on the vulnerabilities that matter most.
The cost of the vulnerability management lifecycle is done manually

The cost of manually running a vulnerability management system is far greater than what organizations realize.
By triaging manually, the security operation team can scale to a maximum of one security professional to 10 development teams.
On average, a security triage consists of
- Analysing the organization’s applications
- Performing a threat assessment
- Identifying the source of vulnerabilities across 3-4 security scanners
- Review the latest security pentest
Only those efforts require days of research with an average of 570 minutes and 9.5 fully dedicated hours of work for each application daily.
This cost and time grow higher considering the number of applications/teams required
Why is it this complex to analyse and triage vulnerabilities? Challenges come from not well-documented organisational structure, absent ownership information, and multiple vulnerability reports that need to be correlated, contextualized and quantified. The picture below provides an overview of the elements considered for each vulnerability report.
Download here the infographic that explains the true cost of triaging and how much it costs to triage vulnerabilities manually

Check out Phoenix Pricing
The number of security professionals required to triage vulnerabilities
Let’s take, as an example, a small to medium organization with 100-200 developers; not all developers will need assistance at times but for the sake of argument, let’s assume so. To cover the manual triage of 100 development teams, you would require at least 5-10 Security professionals to achieve a ratio of 1:20 to 1:10 security professionals to developers. The average annual salary for a mid-level vulnerability management consultant in the UK is £40,000; in the US, it’s $75,000. To cover an organization with 100 developers, you would need an average of 400,000 in the UK and 750,000 $ in the US.

Health Cost
Source: ThreatConnect
Burnout and triage fatigue is a real problem and is claiming the health of many security professionals starting to consider a different career due to burnout and loss.
According to a recent article from Gartner, more than a third of cybersecurity professionals are considering quitting their jobs.
Recent research from Acutec, UK businesses lose an average of 4.3 days a year per employee to sick absents due to burnout – an average of £554 per employee. For a team of 10, that’s £5,540 just on sick days.
As the team is absent, triaging and prioritizing the vulnerability is left unattended. This increases the probability of exploitation as the average time from discovery to exploitation is seven days.
Cybersecurity Skill Shortage Challenge
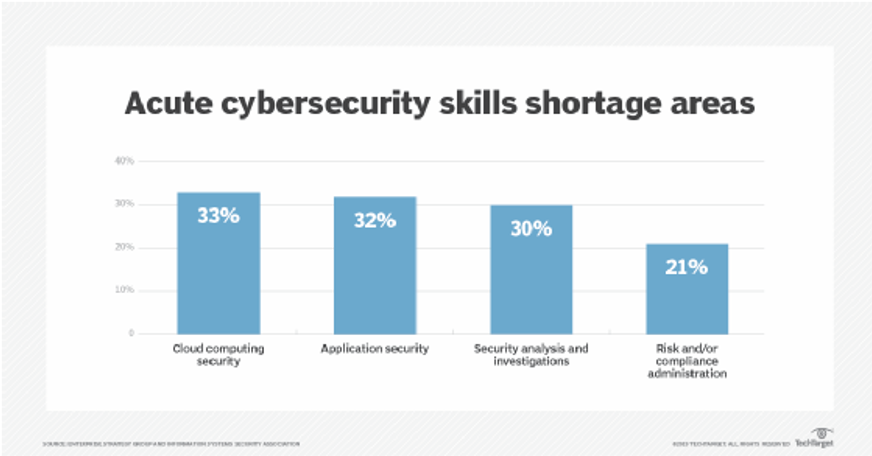
On top of the cost recruiting for security roles is increasingly difficult. Half (49%) of all cyber firms have faced problems with technical cyber security skills gaps, either among existing staff or among job applicants, according to a recent UK Government study on skill gaps. With Security engineers (35% demand) and security analysts (18%) being the most in-demand job accessing the right talent, retaining it is a key tactic to keep your business safe.
Risk Potential breach and cost
It is always difficult to put a cost of vulnerability exploitation or business interruption. According to IBM, the global average data breach cost is a hefty $4.24 million.
What’s the solution?
Phoenix offers a way to scale triaging and prioritizing vulnerabilities, removing the manual part of security analysis and enabling the security team to scale better, from a 1:10 to 1:40 ratio, react faster (from 290 days average resolution time to 30) and be more efficient in the time spent on each vulnerability.

With a proven methodology adopted by over 1000 Security professionals, Phoenix enables security engineers to communicate more effectively with the business regarding risk and loss and automatically prioritize vulnerabilities for developers.
How Can Phoenix Security Help
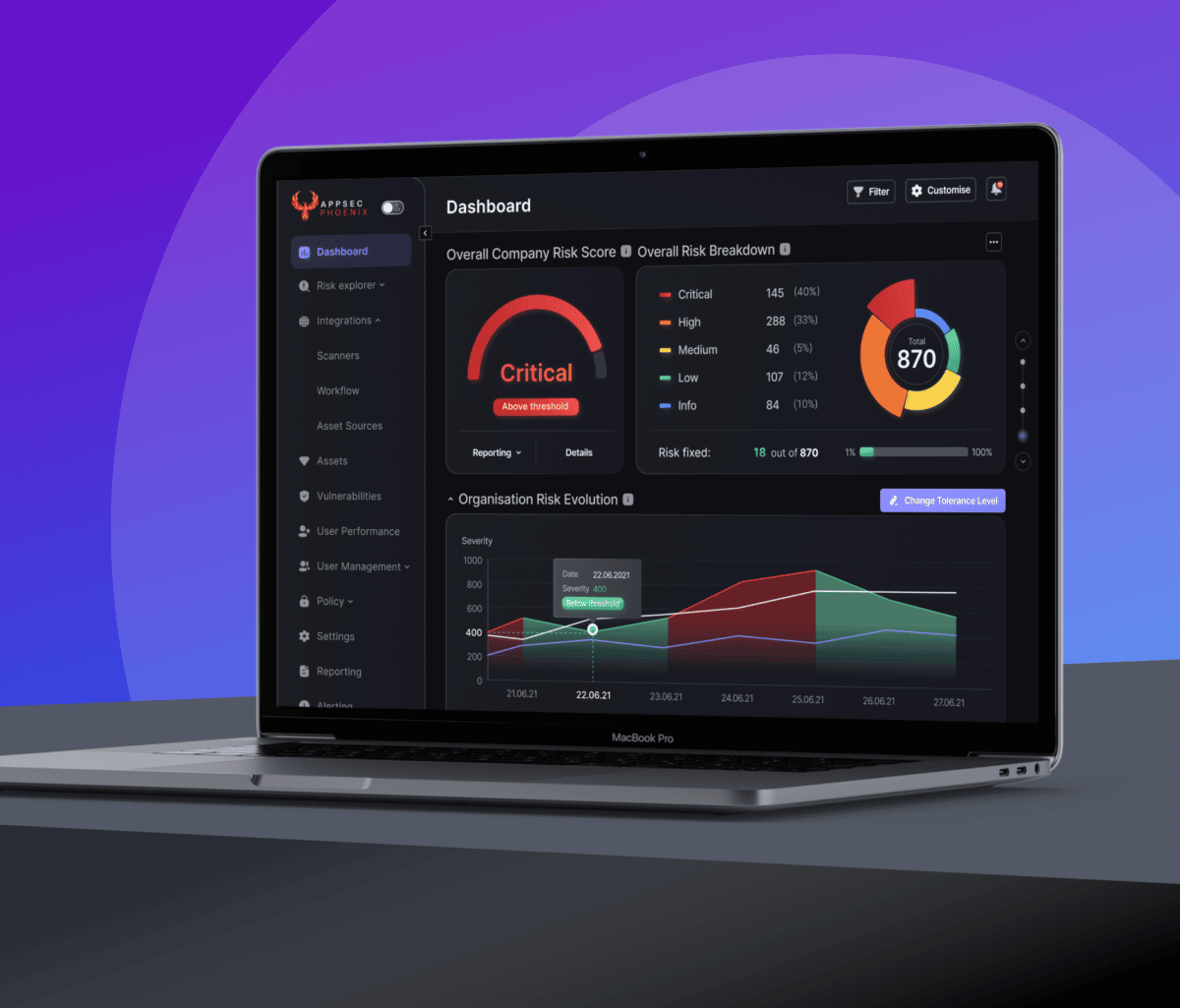
Appsec phoenix is a saas platform that ingests security data from multiple tools, cloud, applications, containers, infrastructure, and pentest.
The phoenix platform Deduplicate correlates, contextualises and shows risk profile and the potential financial impact of applications and where they run.
The Phoenix platform enables the security team to scale, automate triage and focus on the tasks that require more attention and the triages that cannot be automated.
Phoenix also enables clearer risk-based communication between the development team and the rest of the business translating vulnerabilities into risk-based posture and position for applications and environments.

















