- 9th March 2026
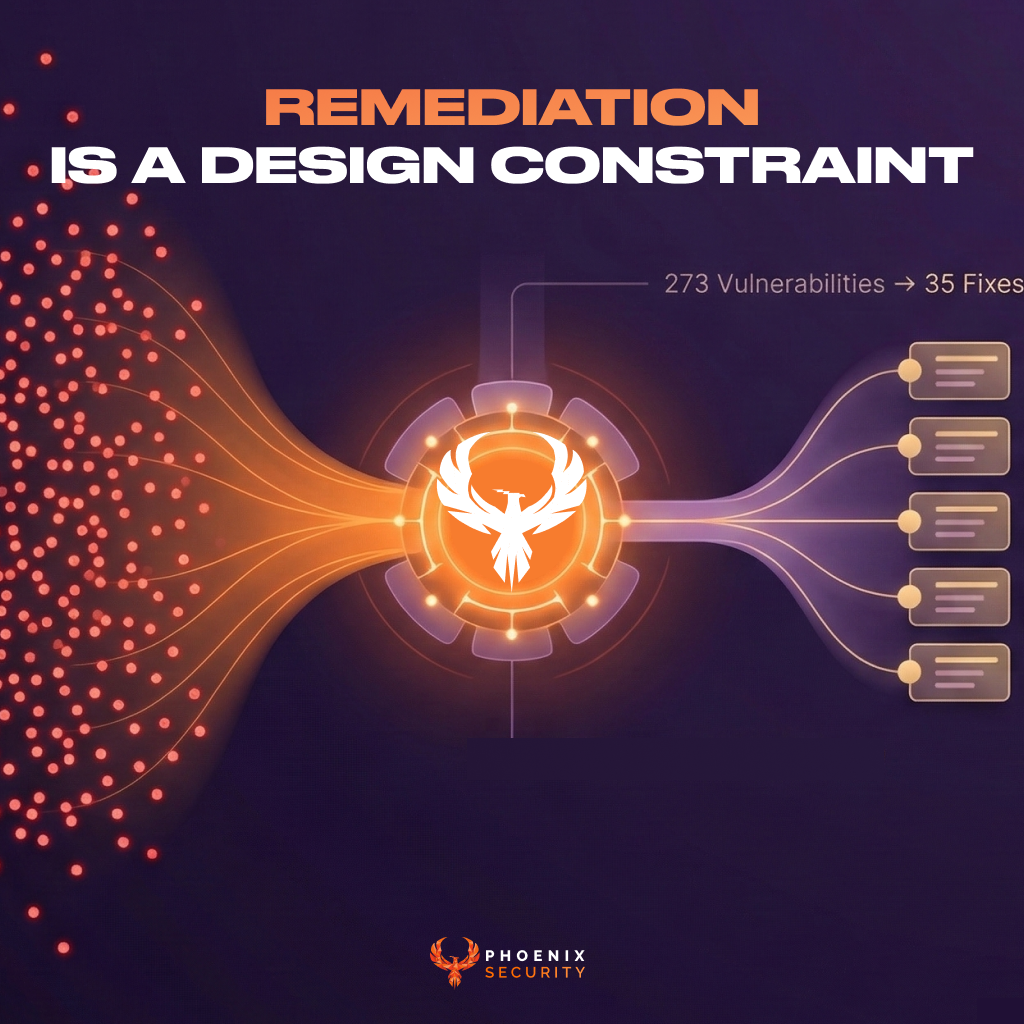
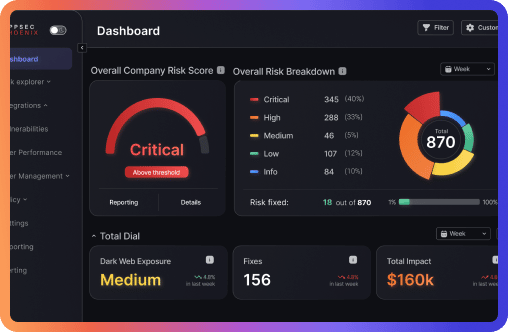
Phoenix Security approaches vulnerability management as a remediation engineering problem. By combining reachability analysis, contextual deduplication, and minimal-impact upgrades, Phoenix transforms hundreds of findings into a small set of changes engineers can actually ship.
Francesco Cipollone