Contents
ToggleThe evolution and reborn of the phoenix
We initially chose the phoenix as a symbol of renewal and reborn; the phoenix platform has evolved from appsec cloudsec complete endpoint management.
As our second year comes to a close, we decided to evolve the name as the platform has massively evolved from the original release in September 2022. With the imminent launch of V3 we wanted an evolved name to cover all the functionalities that the platform and us can do for our clients
Now that the platform covers all those areas identifying vulnerabilities from code to cloud, we thought it appropriate to evolve the name,
From appsec Phoenix, we evolve into Phoenix security, a unified platform covering code to cloud with vulnerability prioritization and traceability of user fixing.
We maintain the same philosophy of cyber risk quantification, risk-driven action and vulnerability prioritization.

Why phoenix security?

We choose phoenix security as a community experiment, including the domain name.
Many voted across multiple platforms to make this name happen.
We believe in the power of community, and what people love, so we let the community decide on the name.
The world has changed.
Cloud and DevOps have shifted how applications and software are built.
Open-source and no-code have changed the speed and time it takes to create software.
In the same way, the Cloud and Containers have changed how software is run.
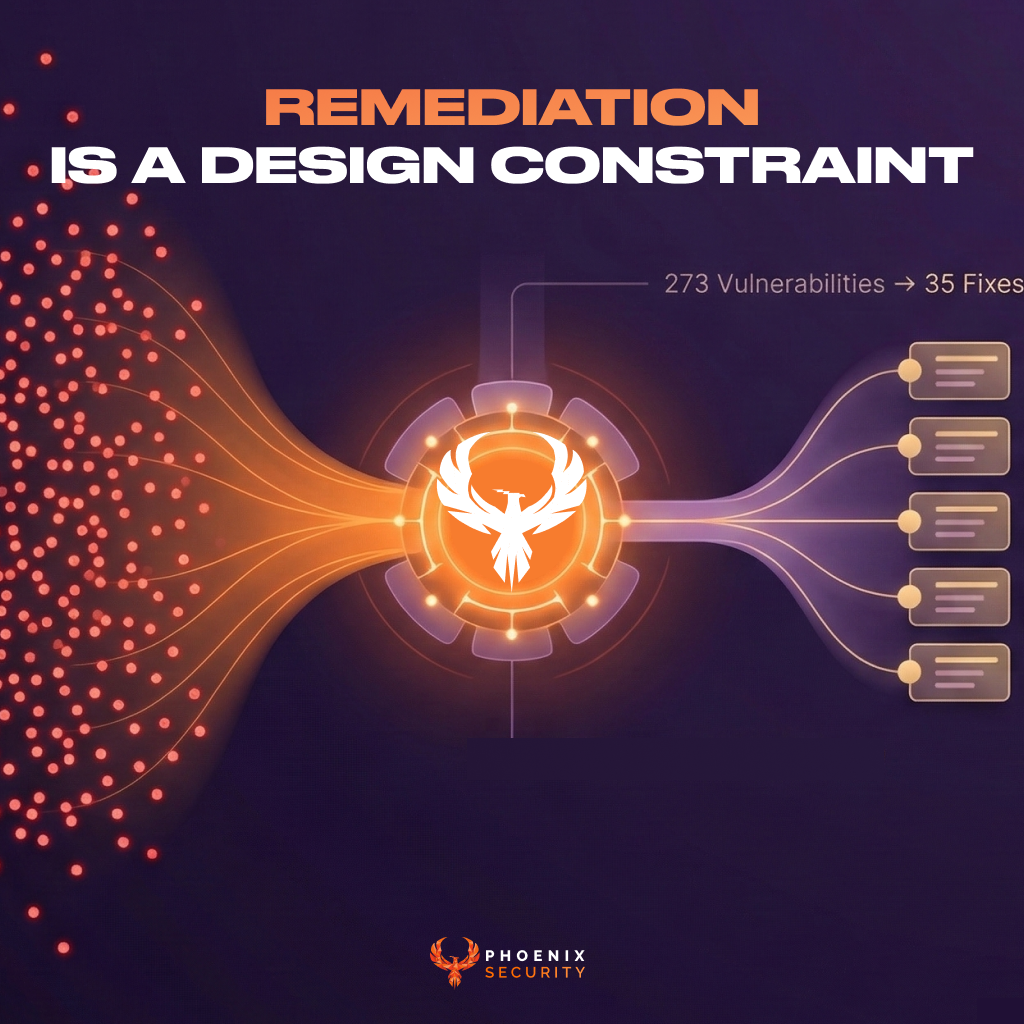
In all this landscape change, we are still trying to address vulnerabilities in the same antiquated ten-year-old method, with manual triage and manual assessment calls. What’s the result? Security teams are drowning in a sea of red/critical alerts that are un-contextualised and spending time arguing with businesses on all the problems that need to be solved. The business leaders don’t speak the vulnerability language and only understand risk and the money spent to reduce risk.
Now is the time for a paradigm shift and to tear down the language barriers.

Where you can find everything:
We choose a new name and domain in the .security domain space phoenix.security is our new home. We will maintain as well the appsecphoenix.com and securityphenix.com as secondary domains
Where can you find the resources
Demo:
Whitepapers:
The app will be reachable at
Securityphoenix.cloud phenixsecurity.app
Support teams:
Support Slack: https://phoenixsec.slack.com/
Support e-mail support at phoenix.security