Contents
ToggleFeatured in the 2026 Application Security Market Report and Recognized as a 2025 Cloud Security Innovator.
London, UK – February 2026 – Phoenix Security today announced its recognition as Application Security Management Leader 2026 in the Latio Application Security Market Report 2026.
This recognition follows Phoenix Security’s 2025 distinction as a Cloud Security Innovator, reinforcing its leadership across ASPM and Continuous Threat Exposure Management (CTEM).
In the 2026 report, Latio positions Phoenix Security among the leading management platforms shaping the future of application security and exposure management, highlighting its strength in cloud and container-centric visibility.
Recognition Backed by Market Validation
The 2026 Latio report makes one thing clear:
- Application security has consolidated into platform players.
- Usability and backlog reduction matter more than raw scanner volume.
- ASPM has evolved into broader vulnerability and exposure management programs.
- Reachability, runtime context, and ownership attribution are becoming mandatory.
Phoenix Security was spotlighted for addressing the three questions most platforms fail to solve at scale:
- Who owns the vulnerability?
- Where is it running?
- What is the fastest, lowest-impact fix?
Latio specifically highlighted Phoenix’s enterprise attribution model, code-to-cloud correlation, and reachability-driven prioritization as differentiators for large, regulated environments .
From Recognition to Results
Awards matter. Outcomes matter more.
Phoenix Security’s leadership in ASPM and CTEM is validated by measurable customer impact across fintech, retail, and ad-tech.
ClearBank | Fintech
ClearBank reduced container vulnerability noise by 98%, eliminated up to 99% of weekly critical vulnerabilities, and saved $2.6M in analyst time annually .
“Phoenix helped us move from noise to precision. We now focus on what truly matters — and fix faster than ever before.”
— Neil Reed, Principal Security Engineer, ClearBank
ClearBank scaled its security function 10x without increasing headcount, shifting from alert overload to measurable remediation velocity.
Bazaarvoice | Retail
Bazaarvoice cut container vulnerabilities by 94%, reclaimed $6.3M in developer time, and automatically mapped over 32,000 rules to teams .
“Phoenix is the only one that truly grasps the complexity of modern vulnerability management, considering both code and cloud vulnerabilities.”
— Nate Sanders, Head of Vulnerability Management, Bazaarvoice
Integral Ad Science (IAS) | Ad-Tech
IAS reduced active container vulnerabilities by 78% and cut SCA-to-container noise by 82.4%, reclaiming nearly $2M in developer time .
Phoenix unified source-to-runtime visibility while preserving engineering velocity.
Why Phoenix Security Is Leading the ASPM Evolution
Latio’s 2026 report signals a shift:
ASPM is no longer “management without scanning.” It is evolving into continuous threat exposure management (CTEM) and universal vulnerability management .
Phoenix Security anticipated that shift early.
The Differentiators Driving Leadership:
1. Enterprise-Grade Attribution
Programmatic CMDB-as-code integration and automated team inheritance eliminate orphan vulnerabilities.
2. Code-to-Cloud Reachability
Static + runtime reachability analysis reduces false positives by up to 91% across code, containers, and runtime.
3. Contextual Deduplication
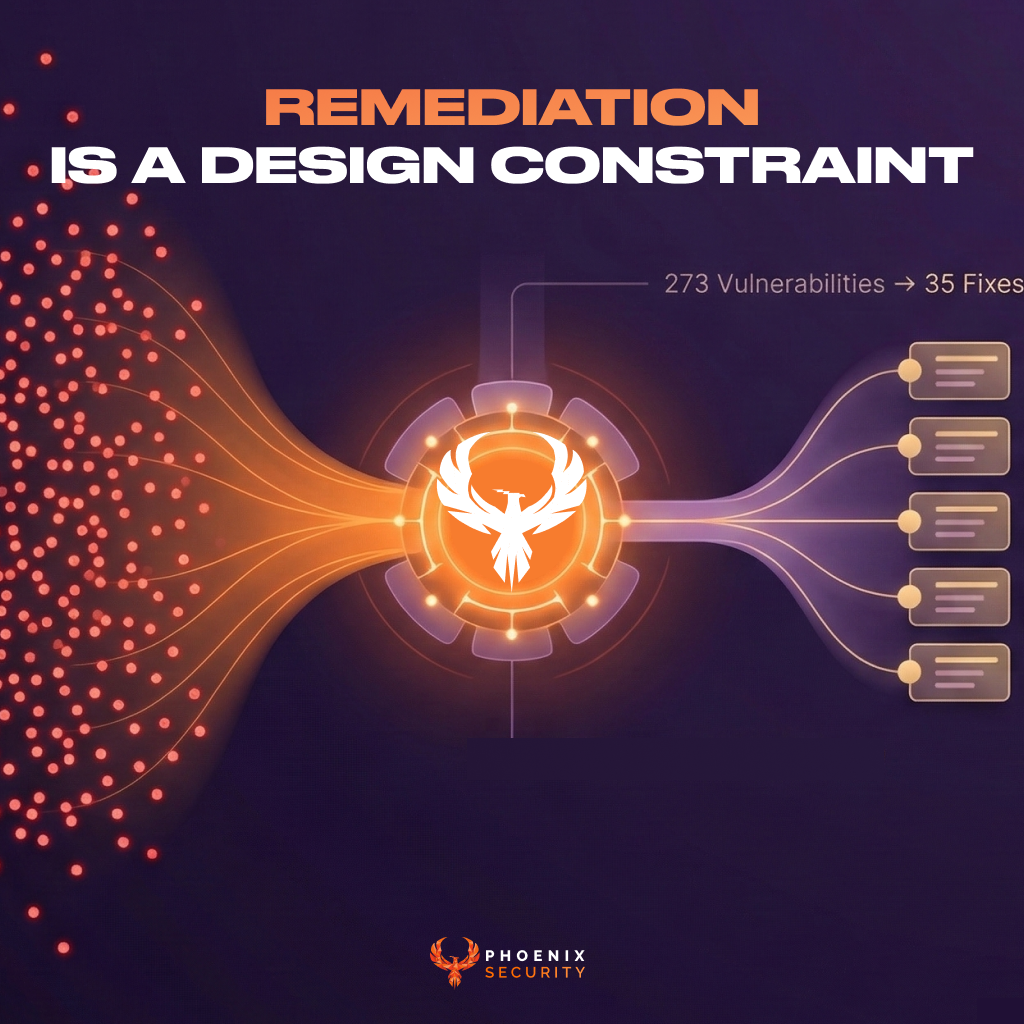
Prevents duplicate findings across repositories, images, and environments — collapsing vulnerability volume dramatically.
4. 4D Risk Formula
Business criticality, exploitability, exposure, and deployment context combine into actionable prioritization.
5. AI-Powered Remediation
Phoenix AI Agents move from detection to execution — delivering remediation plans or GitHub autofixes directly into engineering workflows.
Momentum Into 2026
This latest recognition builds on prior industry validation, including:
- Recognition by Gartner Digital Markets brands in 2024
- Selection as a top ASPM provider in Voice of the Customer 2024
Phoenix Security continues to work alongside enterprises such as ClearBank, Bazaarvoice, IAS, and other global organizations to reduce vulnerability noise, accelerate remediation, and align security with business objectives.
Leadership Commentary
Francesco Cipollone, CEO & Co-Founder of Phoenix Security:
“Being recognized as Application Security Management Leader 2026 validates the direction we’ve taken from day one — context before automation, ownership before dashboards, and remediation over reporting.
Enterprises don’t need more scanners. They need precision, attribution, and execution. That’s what Phoenix delivers.”
About Phoenix Security
Phoenix Security is an Actionable ASPM platform designed for enterprises that demand measurable risk reduction across code, cloud, and runtime environments.
By combining contextual deduplication, reachability analysis, automated attribution, and AI-driven remediation, Phoenix transforms vulnerability management into a scalable, execution-focused discipline aligned with CTEM principles.