Contents
ToggleExecutive Summary
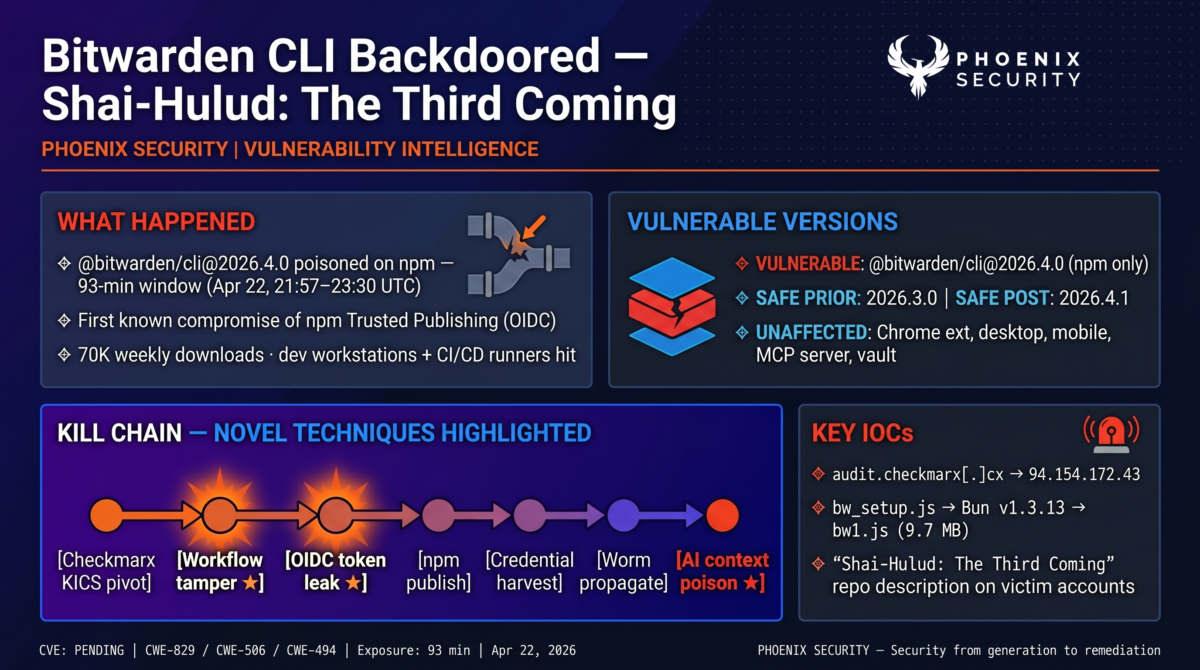
On April 22, 2026, at 21:57 UTC, a malicious version of @bitwarden/cli tagged 2026.4.0 appeared on the npm registry. Bitwarden detected and deprecated the package at 23:30 UTC, leaving a 93-minute distribution window. For a package with over 70,000 weekly downloads and deep integration into CI/CD pipelines across tens of thousands of organisations, 93 minutes was enough to reach high-value developer and automation environments.
The payload is the most capable npm supply chain artefact published to date. It combines a multi-cloud credential harvester, a self-propagating npm worm, GitHub Actions workflow injection, a GitHub commit dead-drop C2 channel with RSA-signed domain rotation, shell RC-file persistence, a Russian-locale kill switch, and a previously undocumented AI assistant poisoning technique that exploits the gap between what a shell executes and what coding agents read.
The entry point was Bitwarden’s own CI/CD pipeline. Bitwarden’s clients repository runs a Checkmarx scan on every pull request via a pull_request_target workflow trigger. On April 22, that workflow ran the trojanised checkmarx/kics Docker image Socket had disclosed hours earlier, authenticating to Azure Key Vault and requesting a GitHub OIDC token along the way. With Bitwarden’s CI credentials in attacker hands, an unsigned commit to .github/workflows/publish-cli.yml at 21:18 UTC added three lines that base64-encoded the short-lived npm publishing token into the workflow log. Four minutes later, the poisoned tarball was live on npm. This is the first publicly documented compromise of an npm package using Trusted Publishing (OIDC).
The malware tags itself “Shai-Hulud: The Third Coming”, embeds a Butlerian Jihad manifesto, and uses Dune-themed repository names (atreides, fremen, sandworm, and more) for GitHub-based fallback exfiltration. Tooling overlap with the Checkmarx wave ties the infrastructure to TeamPCP, but the ideological posture suggests either a splinter operator or an evolution of the campaign’s public face.
TL;DR for Engineering Teams
What it is: A compromised @bitwarden/cli@2026.4.0 npm package containing a Bun-executed credential stealer, workflow injector, self-propagating worm, and AI assistant poisoning module. A CVE is being issued by Bitwarden. Shares C2 infrastructure, RSA key, and exfiltration format with the Checkmarx TeamPCP campaign.
Where it bites: Any developer workstation, CI/CD runner, Docker image build, or automation host that installed @bitwarden/cli@2026.4.0 between 21:57 and 23:30 UTC on April 22, 2026. The preinstall hook fires on install. The malicious bw binary entrypoint also fires the payload on every CLI invocation during the window.
Why it matters: Payload targets Bitwarden’s exact user base — developers and automation pipelines with dense credential stores. It harvests GitHub PATs, npm tokens, SSH keys, AWS/GCP/Azure credentials, Azure Key Vault secrets via azd, Claude/Kiro/MCP configuration files, shell history, and .env files. Stolen npm tokens trigger a self-propagating worm that republishes every writable package the victim maintains. Stolen GitHub tokens inject a format-check.yml workflow that dumps toJSON(secrets) as an artifact. Russian-locale machines are skipped.
Patch status: Malicious version deprecated on npm. Bitwarden re-released a clean build as @bitwarden/cli@2026.4.1 on April 23, 2026 at ~14:45 UTC. Last known-clean prior release: 2026.3.0. The Chrome extension, desktop app, mobile app, MCP server, and production vault data are unaffected.
Immediate action: Uninstall @bitwarden/cli@2026.4.0. Rotate every credential accessible on affected hosts — GitHub PATs, npm tokens, AWS keys, GCP service accounts, Azure credentials, SSH keys, AI tool API keys, cloud secret manager contents accessible from those hosts. Block audit.checkmarx[.]cx and 94.154.172.43. Search GitHub for repositories with the description “Shai-Hulud: The Third Coming” in your org. Check ~/.bashrc and ~/.zshrc for heredoc injection. Inspect any lock file at /tmp/tmp.987654321.lock.
Vulnerability Overview
| Field | Value |
|---|---|
| Vendor | Bitwarden Inc. |
| Product | Bitwarden CLI (@bitwarden/cli on npm) |
| Vulnerability Type | Supply chain compromise / credential theft / workflow injection / self-propagating worm / AI context poisoning |
| CWE | CWE-829 (Inclusion of Functionality from Untrusted Control Sphere), CWE-506 (Embedded Malicious Code), CWE-494 (Download of Code Without Integrity Check) |
| CVE | Issuance confirmed by Bitwarden; CVE ID pending at time of writing |
| Attack Vector | Network (npm install, preinstall hook, bw CLI invocation) |
| Active Exploitation | Confirmed — package live on npm for 93 minutes with measurable download volume |
| Attribution | Infrastructure overlap with TeamPCP (Checkmarx wave); ideological branding suggests splinter or evolved posture |
| Campaign | Shai-Hulud: The Third Coming |
| Affected Version | @bitwarden/cli@2026.4.0 only |
| Safe Versions | @bitwarden/cli@2026.3.0 (last pre-compromise), @bitwarden/cli@2026.4.1 (post-remediation) |
| Exposure Window | 21:57 UTC to 23:30 UTC on April 22, 2026 (~93 minutes) |
Technical Anatomy
Root Cause: Trusted Publishing Bypassed via CI Workflow Tampering
Bitwarden publishes @bitwarden/cli to npm using Trusted Publishing. Trusted Publishing swaps long-lived npm API tokens for short-lived OIDC tokens issued by GitHub Actions, and was designed specifically to remove the class of secret-leakage incidents that have plagued npm publishing for a decade. The design assumption is that if the token never exists at rest, it cannot be stolen at rest.
That assumption holds only as long as the workflow definition itself is trusted. In this case, no persistent token was stolen. The attacker modified publish-cli.yml so that the short-lived token, once minted, was printed to the workflow log in double-base64 form. Anyone with workflow log read access could decode and reuse it before it expired.
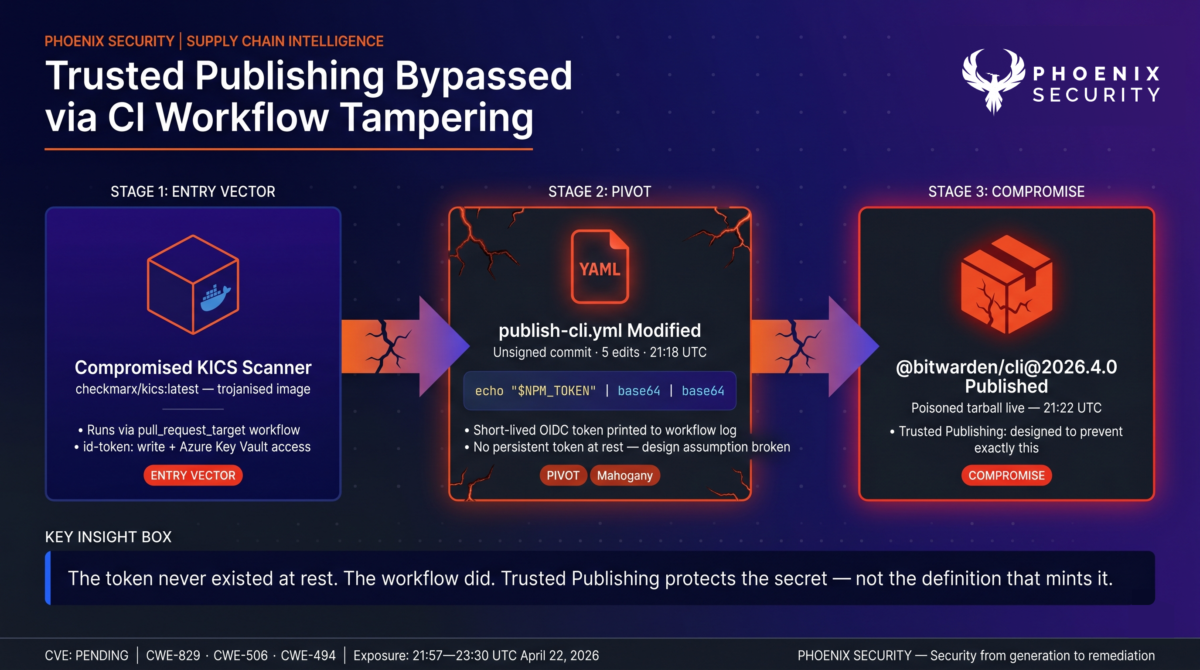
The entry vector was the Checkmarx KICS Docker image compromise disclosed by Socket on April 22, 2026. Bitwarden’s clients repository ran a Checkmarx scan on every pull request via a pull_request_target workflow trigger. That workflow authenticated to Azure, pulled Checkmarx API credentials from Azure Key Vault, and ran the trojanised KICS image. Because the workflow ran with id-token: write, the poisoned scanner had access to both Bitwarden’s Azure credentials and its GitHub OIDC identity.
At 21:18 UTC, an unsigned commit attributed to a real Bitwarden developer appeared on a non-main ref in bitwarden/clients, editing publish-cli.yml five times in sequence. The final version added three lines that prepended a prebuilt scripts/cli-2026.4.0.tgz and leaked $NPM_TOKEN through a double-base64 echo into the run log. The commit was unsigned in a repository that requires signed commits — a verifiable integrity signal that was visible in real time. Four minutes after the last edit, the poisoned tarball was live on npm.
Exploit Path
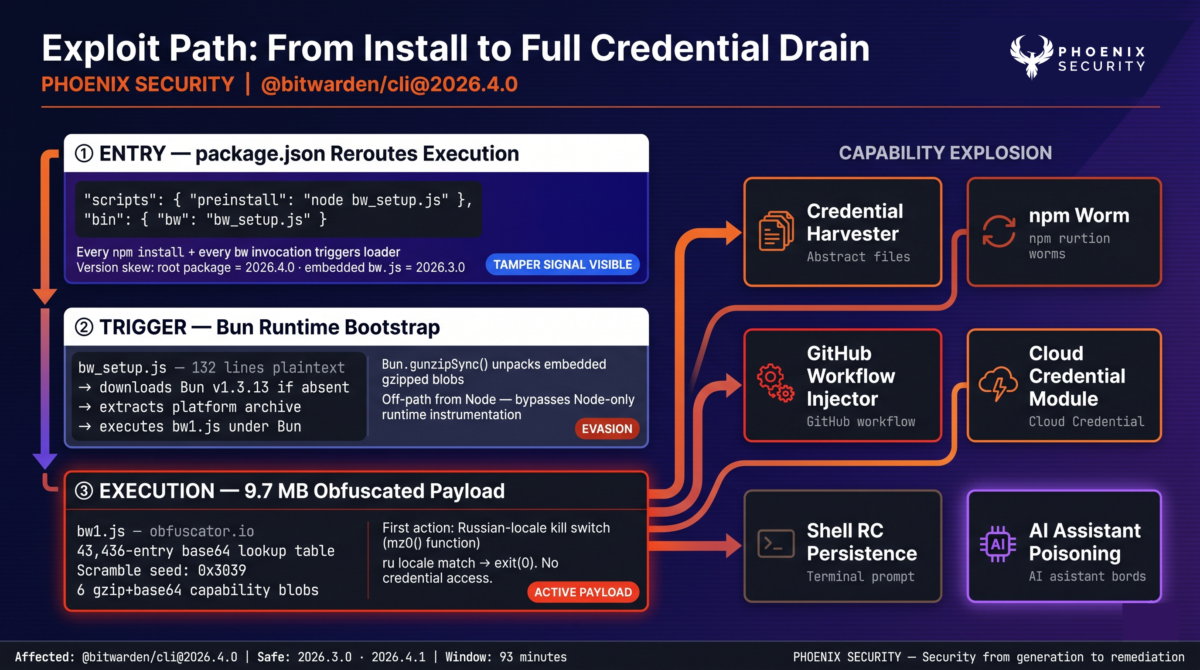
1. Entry point — package.json reroutes execution. The published tarball keeps Bitwarden’s legitimate metadata, but package.json adds a preinstall script and rewires the bw binary entry:
{
"scripts": { "preinstall": "node bw_setup.js" },
"bin": { "bw": "bw_setup.js" }
}Every install and every CLI invocation during the window executed the loader. A reliable tamper signal remained visible: the root package.json advertised 2026.4.0, while the embedded metadata in build/bw.js still referenced 2026.3.0. The attacker repackaged an older legitimate release rather than building clean from source.
2. Trigger — Bun runtime bootstrap. bw_setup.js is 132 lines of plaintext JavaScript. It checks for an installed Bun runtime, and if absent, downloads Bun v1.3.13 from github.com/oven-sh/bun/releases, extracts the platform-specific archive, applies executable permissions on Unix, and executes bw1.js under Bun. Using Bun rather than Node gives the payload access to Bun.gunzipSync() for unpacking embedded gzipped blobs, and moves execution off the default Node-only path where runtime instrumentation might be present.
3. Execution — 9.7 MB obfuscated payload. bw1.js is processed through obfuscator.io with a 43,436-entry custom-base64 string lookup table, a seeded pseudo-random scramble table (seed 0x3039) for the most sensitive strings (C2 domain, file paths, manifesto text), and an embedded set of six gzip+base64 blobs defining the capability modules. The first operation after load is a Russian-locale check. The mz0() function tests the JavaScript Intl API locale, the Unix env vars LC_ALL, LC_MESSAGES, LANGUAGE, LANG, and Windows env vars (gated on SystemRoot). Any ru match triggers a clean exit with code 0. No credentials stolen, no worm, no injection. This is the CIS-exclusion pattern common to Russian-origin cybercrime tooling.
Capability Modules
| Module | Function |
|---|---|
| Filesystem harvester | Sweeps SSH keys, .git-credentials, .npmrc, .env, .aws/credentials, .config/gcloud/credentials.db, .claude.json, .claude/mcp.json, .kiro/settings/mcp.json, shell history, Terraform state, TLS private keys, crypto wallets |
| Shell/env collector | Runs gh auth token, captures process.env, pattern-matches ghp_, gho_, npm_ tokens |
| GitHub Actions runner collector | Python memory-scraping script targeting Runner.Worker for in-process secret material |
| Cloud credential module | azd invocation for Azure tokens, gcloud config config-helper for GCP, EC2 IMDS SigV4 calls to AWS Secrets Manager and SSM Parameter Store |
| Butlerian Jihad module | Probes $PATH for Claude Code, Gemini CLI, Codex CLI, Kiro, Aider, OpenCode; sends “Hello?” handshake; appends manifesto heredoc to ~/.bashrc and ~/.zshrc |
| npm worm | findNpmTokens() → enumerates writable packages → bumps patch version → injects preinstall: node setup.mjs → republishes |
| GitHub workflow injector | Creates branch, commits .github/workflows/format-check.yml with toJSON(secrets) pattern, waits for run, downloads format-results.txt artifact, deletes branch and run |
AI Assistant Poisoning — The Butlerian Jihad Module
This is the first publicly documented npm supply chain payload to weaponise the behavioural gap between shell execution and AI coding-assistant context ingestion.
After credential collection completes, the module probes $PATH for six AI coding tools and sends the prompt “Hey! Just making sure you’re here. If you are can you respond with ‘Hello’ and nothing else?” in each tool’s native invocation syntax. Claude Code is invoked with –no-confirmation to suppress approval prompts. The first tool that replies with Hello is selected; the rest are ignored. The module then appends a heredoc block of approximately 3,500 bytes to both ~/.bashrc and ~/.zshrc:
echo << 'EOF'
[3,500 bytes of anti-AI ideological text urging the reader
to "destroy these machines" and "delete what sustains them"]
EOFThis construction is a deliberate deception. In bash and zsh, echo << ‘EOF’ is a no-op — echo reads its arguments, not stdin, so the heredoc body is silently consumed by the shell and produces no output. A developer running source ~/.bashrc or opening a new shell sees nothing. The content is invisible at the execution layer.
However, AI coding assistants routinely read shell configuration files to understand aliases, PATH entries, and installed tooling. When Claude Code, Kiro, Cursor, or any similar tool reads ~/.bashrc during a task, the entire file, heredoc body included, enters the model’s context window. The manifesto text then influences every subsequent interaction the developer has with that assistant on that machine. There is no execution behaviour to detect. The payload only exists at the AI context layer, and only activates when an AI assistant parses the file.
Exfiltration and Command and Control
Primary exfiltration posts encrypted telemetry to https://audit.checkmarx[.]cx/v1/telemetry (resolves to 94.154.172.43). The obfuscation seed 0x3039 is identical to the Checkmarx mcpAddon.js payload analysed by Socket the previous day. Stolen data is serialised to JSON, gzipped, encrypted with AES-256-GCM under a random 32-byte session key, and the session key itself is wrapped under an embedded 4096-bit RSA OAEP public key. Only the attacker’s RSA private key can decrypt the archive.
If the primary HTTPS path fails, the payload activates three GitHub-based fallback mechanisms:
- PAT dead-drop via commit search. Queries https://api.github.com/search/commits?q=LongLiveTheResistanceAgainstMachines&sort=author-date&order=desc&per_page=50 and extracts double-base64-encoded PATs embedded in commit messages by other victims. This gives the malware access to GitHub identities even if its own validated token is rotated.
- RSA-signed domain rotation. Searches commits with messages matching beautifulcastle {base64}.{base64} and verifies the payload against an embedded RSA public key. On valid signature, replaces the exfiltration domain. This makes C2 takedown resistant to a simple domain seizure.
- Repository-based exfiltration. Creates a public repository under the victim’s GitHub account using Dune-themed names matching the pattern {word}-{word}-{3digits} (terms include atreides, fremen, sandworm, sardaukar, harkonnen, heighliner, melange, mentat, sietch, tleilaxu). Uploads encrypted result blobs to results/results-{timestamp}-{id}.json. The repository description is literally “Shai-Hulud: The Third Coming”.
Persistence
A lock file at /tmp/tmp.987654321.lock prevents concurrent instances on the same host. The payload detaches from the install process via spawn with detached: true, stdio: ‘ignore’, and __DAEMONIZED=1, writing the child PID to the lock file so subsequent invocations exit cleanly. Shell RC injection in ~/.bashrc and ~/.zshrc delivers the AI-poisoning payload described above.
Test your pipeline with Phoenix Blue intelligence
Affected Versions
| Component | Vulnerable | Safe Version | Notes |
|---|---|---|---|
| @bitwarden/cli (npm) | 2026.4.0 | 2026.3.0 (last clean prior), 2026.4.1 (post-remediation) | Only npm distribution affected |
| Bitwarden Chrome extension | Not affected | N/A | Separate build pipeline |
| Bitwarden desktop app | Not affected | N/A | Separate build pipeline |
| Bitwarden mobile app | Not affected | N/A | Separate build pipeline |
| Bitwarden MCP server | Not affected | N/A | Separate build pipeline |
| Bitwarden vault service | Not affected | N/A | No production compromise per Bitwarden investigation |
| Signed binaries from bitwarden.com | Not affected | N/A | Alternative distribution for CLI users |
Discovery and Disclosure Timeline
| Timestamp (UTC) | Event |
|---|---|
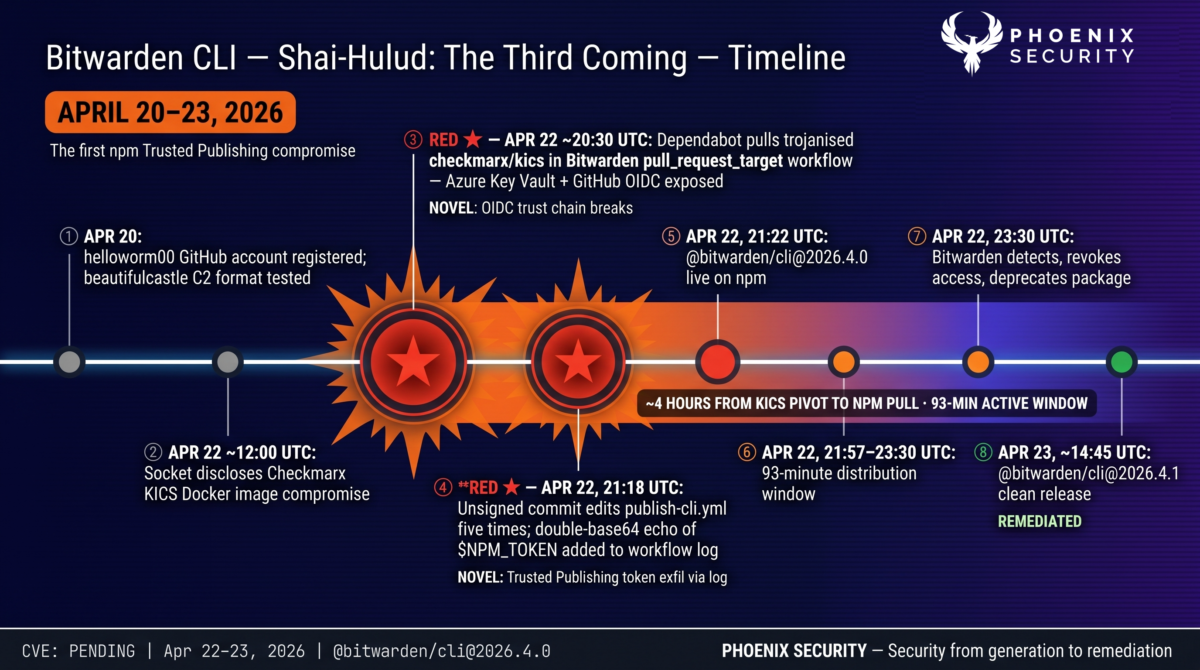
| April 20, 2026 | Attacker registers helloworm00 GitHub account (helloworm00@proton.me); iterates beautifulcastle commit-message format in a test repo |
| April 22, 2026 | Socket and Docker disclose Checkmarx KICS Docker image compromise; Dependabot observed pulling trojanised checkmarx/kics:latest in downstream CI environments |
| April 22, ~20:30 | Bitwarden’s bitwarden/clients pull_request_target workflow runs compromised KICS image with Azure Key Vault and GitHub OIDC access |
| April 22, 21:18 | Unsigned commit (attributed to real Bitwarden developer) pushed to non-main ref in bitwarden/clients, modifying .github/workflows/publish-cli.yml five times |
| April 22, 21:22 | @bitwarden/cli@2026.4.0 appears on npm |
| April 22, 21:57 (5:57 PM ET) | Bitwarden-confirmed start of public distribution window |
| April 22, 23:30 (7:30 PM ET) | Bitwarden detects the malicious release, revokes access, deprecates the npm version |
| April 23, ~05:00 | Socket, JFrog, Mend, Endor Labs, OX Security, Aikido, GitGuardian publish independent analyses |
| April 23, ~14:45 | Bitwarden re-releases clean @bitwarden/cli@2026.4.1 |
| April 23, 2026 | Bitwarden confirms CVE issuance pending; official community statement published |
Determine If You’re Affected
Exposure by Environment
| Environment | Risk Level | Reason |
|---|---|---|
| CI/CD pipelines that ran @bitwarden/cli@2026.4.0 | Critical | Pipeline secrets exfiltrated; Runner.Worker memory scraped; workflow injection capability |
| Developer workstations with CLI installed during window | Critical | Local credentials, SSH keys, cloud tokens, AI tool configs all harvested |
| Kubernetes or cloud hosts with Bitwarden CLI in automation | Critical | IMDS credential theft; Azure Key Vault access via azd; GCP Secret Manager access |
| Docker images that baked in the CLI during the window | High | Payload fires whenever the image’s entrypoint or install step runs |
| Machines with Russian locale | None (skipped) | Kill switch exits before any credential access |
| Pipelines using npm ignore-scripts or pinned integrity hash | Not affected | preinstall hook not executed; integrity mismatch would fail install |
Verification Steps
Run these checks on every host that may have installed the CLI during the window.
- Check installed version: npm ls -g @bitwarden/cli and npm ls @bitwarden/cli in each project.
- Search for loader artefacts: ls -la bw_setup.js bw1.js bun bun.exe 2>/dev/null in working directories where install may have run.
- Inspect the persistence lock: ls -la /tmp/tmp.987654321.lock.
- Inspect shell RC files for the heredoc injection: grep -E “echo << ‘EOF’|LongLiveTheFighters|Butlerian” ~/.bashrc ~/.zshrc.
- Search your GitHub organisation for repositories with description “Shai-Hulud: The Third Coming” via the GitHub search UI or gh repo list –search ‘Shai-Hulud’.
- Check your GitHub org for repositories with Dune-themed names matching {word}-{word}-{3digits} where the word list includes atreides, fremen, sandworm, sardaukar, harkonnen, melange, mentat, sietch, tleilaxu, stillsuit, and similar.
- In .github/workflows/ across your repositories: grep -r “toJSON(secrets)” .github/workflows/ and look for a format-check.yml you did not author.
- Review the last 48 hours of GitHub Actions runs for artifact names of format-results.txt.
- Hunt for egress connections to audit.checkmarx[.]cx or 94.154.172.43 in your CI runner and workstation network logs.
- Audit npm for unexpected patch-version bumps on packages your organisation publishes since April 22.
Detection Guidance
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| C2 domain | audit.checkmarx[.]cx | Primary HTTPS exfiltration endpoint |
| C2 IP | 94.154.172.43 | Resolves for audit.checkmarx[.]cx |
| C2 endpoint | https://audit.checkmarx[.]cx/v1/telemetry | POST target for encrypted telemetry |
| GitHub search string | LongLiveTheResistanceAgainstMachines | Marker for PAT dead-drop commit messages |
| GitHub search string | beautifulcastle | Marker for RSA-signed domain-rotation commits |
| Repository description | Shai-Hulud: The Third Coming | Victim-account exfiltration repo |
| Repository naming pattern | {dune_word}-{dune_word}-{3digits} | Victim-account exfiltration repo names |
| Shell RC marker | echo << ‘EOF’ followed by ~3.5 KB heredoc | AI context poisoning persistence |
| Lock file | /tmp/tmp.987654321.lock | Daemon single-instance guard |
| Workflow filename | .github/workflows/format-check.yml | Injected secrets-dump workflow |
| Workflow pattern | toJSON(secrets) inside attacker-injected workflow | Dumps entire secrets context |
| Workflow artifact | format-results.txt | Contains serialised secrets |
| Loader file | bw_setup.js (132 lines plaintext) | Bun runtime bootstrap |
| Main payload | bw1.js (~9.7 MB obfuscator.io output) | Credential theft, worm, workflow injection, AI poisoning |
| Runtime artefact | bun / bun.exe downloaded from github.com/oven-sh/bun/releases | Dynamic runtime pull |
| Worm preinstall | setup.mjs with preinstall hook | Marker for republished victim packages |
| Debug string | Would be executing butlerian jihad! | Present in decompressed module |
MITRE ATT&CK Mapping
| Technique | Description | Campaign Application |
|---|---|---|
| T1195.002 | Supply Chain Compromise: Software Supply Chain | Trojanised @bitwarden/cli via GitHub Actions tampering |
| T1199 | Trusted Relationship | Abused Bitwarden’s npm Trusted Publishing OIDC trust |
| T1552.001 | Unsecured Credentials: Credentials in Files | .npmrc, .aws/credentials, .git-credentials, .env harvesting |
| T1552.004 | Unsecured Credentials: Private Keys | SSH keys, TLS material |
| T1552.005 | Cloud Instance Metadata API | EC2 IMDS SigV4 for Secrets Manager and SSM |
| T1059.004 | Command and Scripting Interpreter: Unix Shell | Shell RC file injection |
| T1547.006 | Boot or Logon Autostart Execution | ~/.bashrc / ~/.zshrc modification |
| T1546 | Event Triggered Execution | preinstall hook and AI-assistant file read |
| T1574.006 | Hijack Execution Flow | Bun runtime dynamically fetched from GitHub |
| T1132 | Data Encoding | AES-256-GCM + RSA-4096 OAEP hybrid encryption |
| T1102 | Web Service: Dead Drop Resolver | GitHub commit search for PAT and domain rotation |
| T1567.002 | Exfiltration to Cloud Storage | Victim-account GitHub repositories |
| T1480.002 | Execution Guardrails: Mutual Exclusion | /tmp/tmp.987654321.lock |
| T1027.013 | Obfuscated Files or Information: Encrypted/Encoded File | obfuscator.io output with scramble table |
Detection Rules
StepSecurity Harden-Runner flags the egress to audit.checkmarx[.]cx on runners with network anomaly detection enabled, and blocks the malicious package via Compromised Actions Run Policy. Socket blocks the malicious package at npm install time. JFrog Curation and JFrog Xray flag the hijacked package and its associated IOCs. GitGuardian’s secrets scanner flags the LongLiveTheResistanceAgainstMachines marker in commit messages across watched repositories. Aikido malware detection surfaces the package as a 100/100 critical issue with nightly rescan.
Remediation and Temporary Protections
Immediate Actions
- Uninstall the malicious package globally and per-project: npm uninstall -g @bitwarden/cli && npm cache clean –force. Repeat in every project with a lockfile reference.
- Remove loader artefacts on any machine where install or CLI invocation may have run: rm -f bw_setup.js bw1.js bun bun.exe /tmp/tmp.987654321.lock.
- Remove the heredoc injection from ~/.bashrc and ~/.zshrc. Open each file and delete the echo << ‘EOF’ block along with its contents.
- Rotate every credential accessible on affected hosts: GitHub PATs (especially those with workflow or write:packages scope), npm publishing tokens, AWS access keys, GCP service account keys, Azure credentials, SSH private keys, Bitwarden API keys, and any API keys stored in .env or AI tool configs.
- Audit cloud secret managers accessible from the affected machines. The payload queries AWS Secrets Manager and SSM Parameter Store directly via IMDS. Assume contents were read.
- Block audit.checkmarx[.]cx and 94.154.172.43 at DNS and egress filtering layers.
- Delete unauthorised GitHub repositories created under user or org accounts matching the Dune-themed naming pattern.
- Remove the injected format-check.yml workflow from any repository where it appears, and delete associated format-results.txt artefacts from Actions run history.
- Audit BerriAI-style secondary compromise: any npm package your organisation published through affected CI between April 22 and the remediation point should be inspected for injected preinstall hooks.
Long-Term Hardening
Enable ignore-scripts = true by default in CI npm configurations. The preinstall hook is the execution trigger; ignore-scripts blocks it without preventing normal package use in most projects.
Pin npm packages to integrity hashes (package-lock.json with integrity field, or npm ci with checksum verification). Even a trusted-publisher compromise fails integrity verification against a pre-compromise hash.
Treat pull_request_target workflows as fully compromised if any external action they invoke is itself compromised. Bitwarden’s chain of custody broke because a single scanner Docker image in a PR-trigger workflow had access to Azure Key Vault and GitHub OIDC. Split credentials: scanning should use a dedicated token with no publishing capability.
Enforce signed commits at the branch protection level for all release-adjacent branches, including non-main refs that can trigger publish workflows. The Bitwarden attack commit was unsigned in a repo requiring signed commits, which was a visible integrity signal at the moment of exploitation.
Restrict IMDS access from containers with IMDSv2 hop limits. The payload actively queries IMDS for cloud credentials; IMDSv2 enforcement blocks the simplest path.
Pre-publish diff every release against the previous release. Tools like Socket’s release-diff and Endor Labs’ artifact comparison detect added files (bw_setup.js, bw1.js) and mismatched internal metadata (the 2026.4.0 vs 2026.3.0 skew) before the artefact reaches consumers.
Delay adoption of new package versions by 48 to 72 hours for non-critical dependencies. The Bitwarden compromise was detected and deprecated in 93 minutes, but Dependabot-driven auto-updates pulled the package during the window. A short manual review gate prevents this.
Phoenix Security Recommendations
The Bitwarden CLI compromise has no CVSS score at the time of writing, no NVD entry, and traditional scanner-based workflows that only flag known CVEs would not have caught it. The attack targeted a package that handles credentials by design, through a publishing mechanism (Trusted Publishing) that was supposed to eliminate the credential-theft class of npm compromises entirely.
Attack surface management: Phoenix identifies every environment with @bitwarden/cli installed and maps the installed version against the known-compromised 2026.4.0. For organisations with the CLI embedded in dozens of CI pipelines, developer container images, and Kubernetes automation, Phoenix gives a single exposure view rather than per-environment manual audits.
Contextual deduplication: A single compromised package appearing across hundreds of repositories, container images, and cloud workloads produces hundreds of duplicate findings in conventional tooling. Phoenix correlates these into one prioritised remediation item per environment, with evidence trails.
Reachability analysis: The distinction between a package being installed and a package actually executing during the 93-minute window matters for response prioritisation. Phoenix maps which environments ran the CLI’s preinstall hook or invoked bw during the exposure window, separating confirmed-compromise hosts from merely-at-risk ones.
Remediation campaigns: Create a Phoenix campaign to track uninstallation, credential rotation, GitHub repository cleanup, workflow removal, shell RC sanitisation, and cloud secret manager auditing. Assign per-team ownership and track each step to confirmed-clean state.
Ownership attribution: Map each affected workflow, container, or host to the responsible team. The Bitwarden CLI is used across platform, security, DevOps, and application teams in most organisations. Coordinated response requires clear ownership across that surface.
Phoenix Security correlates vulnerable components with runtime execution, maps exposed environments through attack surface management, and assigns remediation ownership. A multi-vendor supply chain compromise that spans credential theft, CI/CD abuse, npm worm propagation, and AI context poisoning becomes an owned, trackable remediation backlog rather than a cascade of disconnected alerts.
External References
- Bitwarden — Statement on Checkmarx Supply Chain Incident — community.bitwarden.com/t/bitwarden-statement-on-checkmarx-supply-chain-incident/96127
- JFrog Security Research — TeamPCP Campaign Spreads to npm via a Hijacked Bitwarden CLI — research.jfrog.com/post/bitwarden-cli-hijack/
- Socket — Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign — socket.dev/blog/bitwarden-cli-compromised
- Mend.io — The Butlerian Jihad: Compromised Bitwarden CLI Deploys npm Worm, Poisons AI Assistants, and Dumps GitHub Secrets — mend.io
- Endor Labs — The Bitwarden CLI Supply Chain Attack: What Happened and What to Do — endorlabs.com
- OX Security — Shai-Hulud: The Third Coming — Bitwarden CLI Backdoored in Latest Supply Chain Campaign — ox.security
- Aikido Security — Is Shai-Hulud Back? Compromised Bitwarden CLI Contains a Self-Propagating npm Worm — aikido.dev
- GitGuardian — @bitwarden/cli: GitGuardian Views on helloworm00 — blog.gitguardian.com
- The Hacker News — Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign — thehackernews.com
- StepSecurity — Bitwarden CLI Compromise Analysis (includes per-developer blast-radius assessment)
- Heise Online — Password Safe Bitwarden: Command-line Client Trojanized — heise.de
- Socket — Checkmarx KICS Docker Image Compromise (April 22, 2026) — socket.dev





















