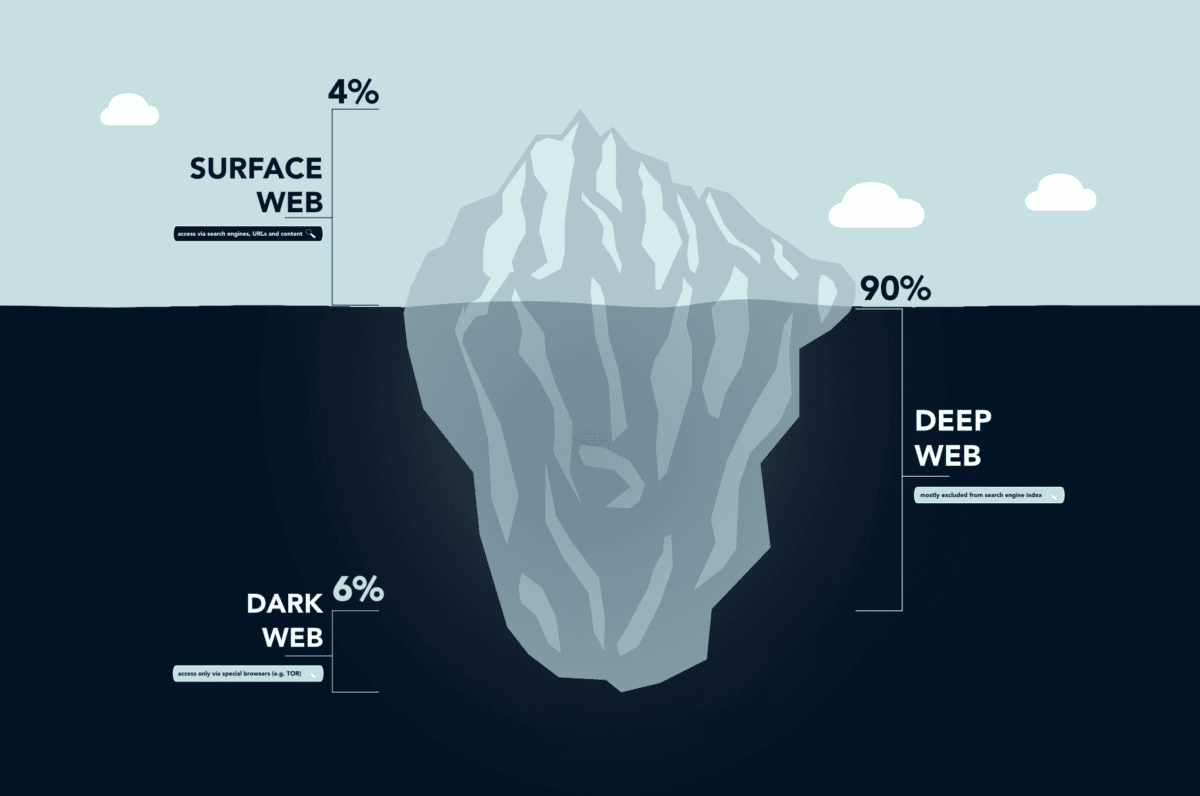
When you hear “dark web”, what do you think? A fraudster’s switchboard? A network of illegal activity? A criminal’s playground? Many people use it that way, but it is also a prime hunting ground for security professionals. Finding out how potential attackers are operating before they attack can give security teams a necessary advantage.
As cyber-attacks such as ransomware, brute-force attacks, and form-grabbing become even more common, threat hunting is a strict necessity in the world of cyber-security. Whether you are developing a website or an application, knowing your adversary is essential in the modern workplace.
Monitoring and understanding the dark web can give your websites and applications a leg-up in the fight against potential attackers. In a world where the data lost in a breach could cost a company on average $3.86 million, getting any advantage on would-be hackers is necessary.
Table of Contents
- Data Breaches – The Facts for Businesses in 2021
- Websites and Data Breaches
- Developer Account Leaks – The Worst-Case Scenario
- Conclusion
Data Breaches – The Facts for Businesses in 2021
Since an all-time high of 1,632 data breaches in 2017, companies around the world have started to understand that security is serious business. The COVID-19 pandemic became a breeding ground for cyber-attacks – many due to social engineering, but a wave of cloud computing solutions and new SaaS tools also left many businesses exposed.
The Real Costs of Data Breaches
The average cost of a lost record is $150 and the average cost of a ransomware attack has grown to $312,493 (the record payout from CWT Global equaling $4.5 million). These are costs that small-to-medium businesses can’t ignore.
60% of businesses shut down within 6 months of suffering data breaches. Whether due to a loss of trust in the organization or crippling financial problems, most businesses never recover from large-scale leaks. Can you afford not to make security a top priority?
The Disastrous Effects of PII Breaches
Personally identifiable information (PII) is the most compromising type of data that businesses keep. Full names, social security numbers, and passport numbers are all examples of this information that is personal and unique to the individual.
When a hacker accesses PII, fraud is around the corner. Loans can be taken out in someone’s name or compromising medical records can be leaked to the public. Organizations that hold a great deal of personal data are the most likely to suffer the heavy financial side-effects of breaches – healthcare organizations on average suffer $7.13 million of damage after a data breach.
Websites And Data Breaches
With the massive proliferation of websites since the 2010s, skilled hackers have turned their attention to penetrating the sometimes shaky defenses of popular CMSs such as WordPress or Joomla. In fact, the global penetration rate has increased from 35% in 2013 to 55.1% – attackers are becoming more sophisticated and technical, with many cybersecurity professionals saying that the hackers are constantly one step ahead.
Websites and applications with poor or weak configurations are prime real estate for malicious attackers. Using a variety of attacks such as form-grabbing and living-off-the-land attacks, hackers can easily gain access to credit card details and PII credentials such as passport numbers.
Building successful defenses against the attacks your applications will face means understanding the enemy. Sometimes this can mean venturing to the Dark Web to find out more about hackers.
Brute-Force / Rainbow Table Attacks
Brute-force attacks are attacks that focus on overloading systems with a flurry of rapid log-in attempts. These attempts try to gain access to a system by sending a large number of log-in requests to a website in quick succession.
Strong password practices are the best way to defend against brute-forcing. End-user education and password management settings are integral to maintaining high-quality passwords.
Rainbow table attacks use, as the name suggests, rainbow tables to gain access to a system. These attacks use pre-programmed hash functions in accordance with leaked hash tables to crack passwords that are hashed. Salting is an effective way to defend against rainbow table attacks.
As far as cyber-attack types go, brute-force attacks are incredibly diverse. In addition to the examples listed above, learning to defend against dictionary attacks and credentials stuffing is key to setting up robust security systems on your applications and web servers.
Form-Grabbing
Form-grabbing malware is most notoriously used to capture online banking information. Generally gaining access to a system via a Trojan Horse, the malware logs keystrokes for information that is entered into a form – typically banking details when buying things online.
Infamous malware such as the Linux-based Hand of Thief and the Windows-based Zeus function (at least in part) as form-grabbing software. Whether through infiltrating a website and causing Drive-by Download attacks or other nefarious means, form-grabbers establish themselves in a system and activate when an online form is detected.
Because form-grabbing software is almost always brought in through a backdoor, constant analysis of network activity is necessary. As Trojan and RAT software dig into a system or network, the outgoing data should be enough to set off alarm bells in security systems. Then you can just hope that nothing valuable has been stolen yet.
Living-Off-The-Land Attacks
When hackers use your own tools against you, it can be almost impossible to know that someone has gained access to your system. Living-off-the-land attacks use the same tools that were used to develop or maintain a piece of software – using malicious PowerShell commands against Microsoft-based victims, for example.
Because malicious files aren’t left on the targeted system, traditional security tools for signature comparison don’t work. Think of it like an inside job in a bank heist and PowerShell is acting as the double-crossing agent – it’s incredibly difficult to know that an attack has occurred because there is nothing out of the ordinary.
Defending against living-off-the-land attacks is extremely difficult, especially as hackers using legitimate tools can bypass whitelists. The best defense against these attacks is a combination of active threat hunting and Endpoint Detection and Response techniques.
SQL Injection
Code-injection is both a type of attack and a facilitator to other kinds of attacks. SQL injection in particular takes aim at back-end databases, aiming to find errors in the code that deals with external calls.
If a piece of software allows users to cause an error in the underlying code, an attacker could bypass password security entirely. By creating an error in the code (such as through a stray ‘ or “ to end a line of code), the hacker can then manipulate the application through conditionals that break the back-end’s logic.
Well-designed code is the best defense against SQL injections. Using parameterized statements and sanitizing the input are the two best methods for stopping hackers in their tracks. Failing to do so exposes accounts as well as entire websites/applications.
Developer Account Leaks – The Worst-Case Scenario
Some of the most catastrophic data breaches occur when developer account details are leaked. Although lowered permissions can save a company when a general employee’s credentials leak, developer accounts have admin permissions and access to key infrastructure. This can lead to catastrophic attacks.
Credential Stuffing
Credential stuffing is a type of brute-force attack where stolen credentials are used on a variety of websites. When username-password combinations are leaked to the internet after a data breach, malicious hackers will attempt to use them to access a variety of sites. This plays on the fact that many people use the same username-password combinations for everything online, leaving them extremely exposed in the event of a leak.
Common username-password combinations are also prone to credential stuffing attempts, especially if common pairings make it onto leaked credential lists. For that reason,
To establish if your credentials have been leaked and you are at risk of credential stuffing, check your email or phone number on Have I Been Pwned?. If you have, it’s time to change your email/username-password combinations to stay ahead of malicious actors.
The Github Healthcare Leaks
Sometimes, hackers don’t even need to use complicated cyberattack techniques. Sometimes developers leave the “front keys” to an app sitting in plain sight.
The most infamous case of developer account credentials being leaked was in the Github Healthcare Leak. Poor development practices lead to credentials being listed on Github – much of it in the form of hardcoded username-password combinations to employee accounts.
There has been an 80% increase in health data breaches in recent years. Despite that, major healthcare organizations such as the 9 listed in this report by Jelle Ursem and DataBreaches.net have had their credentials publicly listed on Github. Thanks to sloppy development, in one of these cases, 7,000 patients had their medical records exposed.
Careless application development practices allow thousands of PII records to be exposed. Hardcoding passwords into the code and/or inappropriately using public depositories is poor from a development point of view and disastrous from a business perspective.
How Could PII Lead To A Leak?
– secondary information -> how PII leaked could affect the probability of guessing credentials
But PII isn’t only a risk due to fraud. When sensitive information is leaked onto the internet, hackers start looking for other places to unlock with these credentials. This is why these kinds of data breaches are incredibly serious – not only is the hacked organization exposed but so is any other database where the same credentials are used.
52% admit that they use the same password for multiple sites, if not all sites. When their personal information is leaked to malicious actors, that information is quickly tested out on other platforms.
This is a pressing concern for businesses. If employees are using the same passwords for all accounts (both professional and personal), business processes could be exposed thanks to careless surfing at home. PII leaks will give a malicious actor an easy way to discover where someone works, meaning that reused passwords become an immediate business risk.
Strong password rotation policies and multi-factor authentication practices are two strong ways to defend against these kinds of leaks. Although there is nothing a business can do to stop people from being caught up in a data breach, it is possible to minimize the risk of credential stuffing and exposing the organization.
Conclusion
As the techniques that malicious hackers use become more sophisticated, security professionals have to remember that getting the basics right matters. Most security breaches are caused by human error, along with amateur errors in code. Cutting down on these could cut down on up to 95% of security issues that companies face.
Active threat hunting and examining the dark web (or consulting with those who do) goes a long way to cutting down on that last 5%. Exploring your systems for malicious code and evidence of data breaches needs to be carried out as often as possible. Slashing the number of PII records that are leaked can not only defend your customers but your business’s reputation as well.
With Phoenix Security you could monitor the data before it becomes visible have a look