Contents
ToggleWhat is the new SEC proposed regulation?
The Securities and Exchange Commission (SEC) has proposed a change regarding cybersecurity disclosures and how they will impact public companies. The rules cover various topics, including cybersecurity, environmental, social, and governance issues. The proposed changes will reshape the cybersecurity function, with increased expectations around incident disclosure and response, board-level involvement, and supply chain scrutiny.
What are the most impactful rules, and how will SEC change impact you
- Material Cybersecurity Incidents Reported Within 4 Business Days: Companies must report any incident that jeopardizes the confidentiality, integrity, or availability of their information systems or any information residing therein. This includes accidental data exposure or inadvertent data sharing. The report should include when the incident was discovered, whether it is ongoing, a brief description of the incident, whether any data was stolen, altered, accessed, or used for any other unauthorized purpose, the effect of the incident on the company’s operations, and whether the company has remediated or is currently remediating the incident.
- Cybersecurity Incident Disclosure in Periodic Reports: The proposed rule does not require public companies to file a separate Form 8-K for such updates; rather, this information would be disclosed in the next filed quarterly or annual report.
- Periodic Disclosures of Cybersecurity Risk Management Policies and Procedures: Companies must disclose if they have a cybersecurity risk assessment program and provide a description of the program. They must also disclose their policies and procedures to oversee and identify the cybersecurity risks associated with the use of any third-party service provider, activities undertaken to prevent, detect and minimize effects of cybersecurity incidents, and whether the company has business continuity, contingency and recovery plans in the event of a cybersecurity incident.
- Governance Disclosures Regarding Cybersecurity: Companies must disclose whether the entire board, specific board members, or a board committee is responsible for the oversight of cybersecurity risks. They must also disclose the process and frequency by which the board is informed about cybersecurity risks and whether and how the board or board committee considers cybersecurity risks as part of its business strategy, risk management, and financial oversight.
How can Security Phoenix Help
Phoenix security enables organizations to ingest vulnerabilities from multiple locations, aggregating them into products and visualizing the risk level of those products. The Phoenix security platform can help with disclosure, reporting and monitoring of specific assets and related vulnerabilities as well as the remediation plan
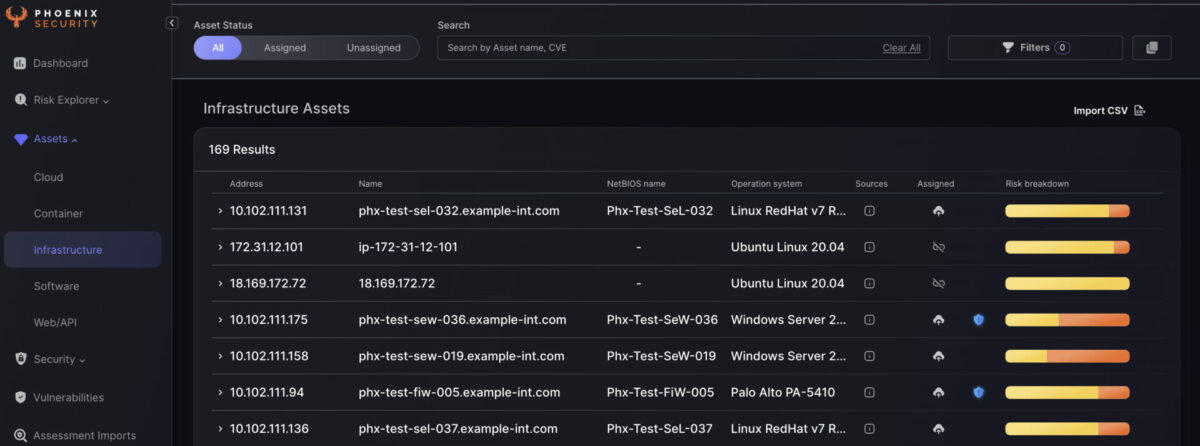
Phoenix security cutting-edge contextual risk-based algorithms enable organisations to prioritise application security vulnerabilities based on context and probability of exploitation and present a unified impact analysis.
The cutting-edge vulnerability selection engine enables organisations to set risk-based targets that translate into specific actions for engineers.
Get in control of your Application Security posture and Vulnerability management
Moreover, Phoenix Security’s correlation capabilities can help organizations link the activities in the code with the context in the shift-right part, ensuring that issues are identified and addressed proactively. Using Phoenix Security’s scorecard, organizations can create a common language between the security, development, and business teams, ensuring everyone is aligned and focused on achieving the same goals.







![Phoenix Security infographic: Claude Code Critical Vulnerability — CI/CD Nightmare, 3 Command Injection Flaws. Dark navy and orange background with circuit-board pattern. Center: terminal window showing attack chain [config] | [shell] | [exfil] with three red arrows pointing to attack targets — CI/CD Pipeline Compromise (top right), Cloud Key Exfiltration via AWS (middle right), and Developer Workstation Compromise leading to Server-to-Server lateral movement (bottom right). Phoenix Security logo at top. Bottom text: "CLAUDE CODE / CRITICAL VULNERABILITY / CI/CD NIGHTMARE / 3 COMMAND INJECTION FLAWS / Credential Exfiltration · CWE-78 · Confirmed / Shell Injection in CLI, Editor, and Auth Helpers."](https://phoenix.security/media/Gemini_Generated_Image_abcn46abcn46abcn.jpeg)








