The Cloud Security and AppSec teams at Phoenix Security are pleased to bring you another set of new Phoenix Security Features and improvements for vulnerability management across application and cloud security engines. This release builds on top of previous releases with key additions and progress across multiple areas of the platform.

We are sure that you’ll find these quite interesting!
- Manage your Vulnerabilities and Assets
- Simplified App/Env creation flow
- Create Apps/Envs directly from Asset screens
- Update asset filters layout in Component forms
- Productivity and User Experience
- Updated Demo Data logic and feedback
- User Experience Improvement
- Integrations
Manage your Vulnerabilities and Assets across application security and cloud security.
Simplified Application and Environment Creation
Currently, one of our key focus is the simplification of the platform’s workflows. The aim is to improve the user experience and minimise the effort required to model and manage your vulnerability and risk landscape inside Phoenix Security.
This release features a simplified Application creation flow, where non-essential configuration and decisions can be addressed later in the cycle. The screenshot below illustrates this: users must name the Application/Environment, select which assets form part of it and… done! All the other fields are optional.
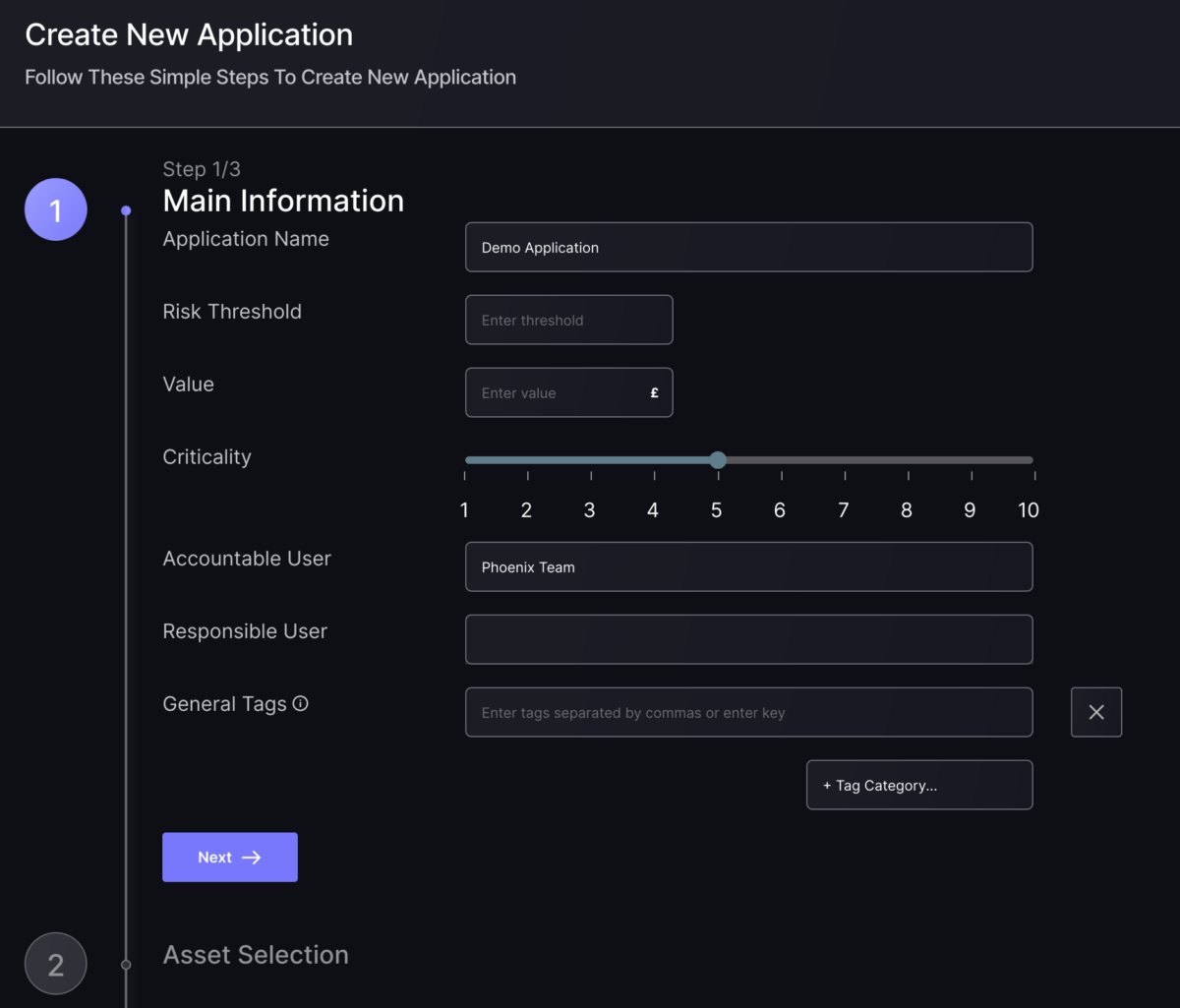
Now you have a full functions Application (or Environment) populated with a dynamic set of assets, vulnerabilities and risks assessed individually and as part of the Organisation.
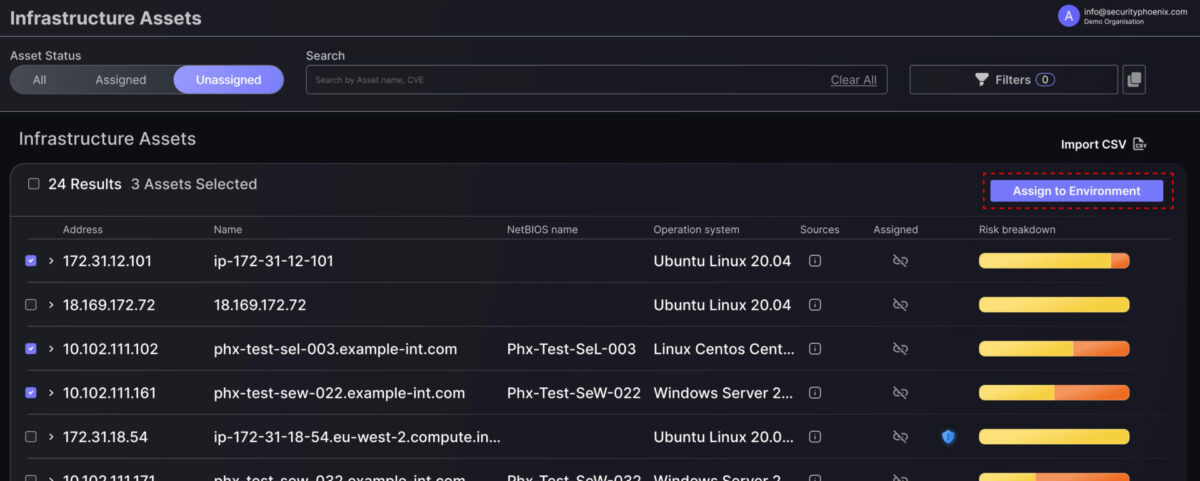
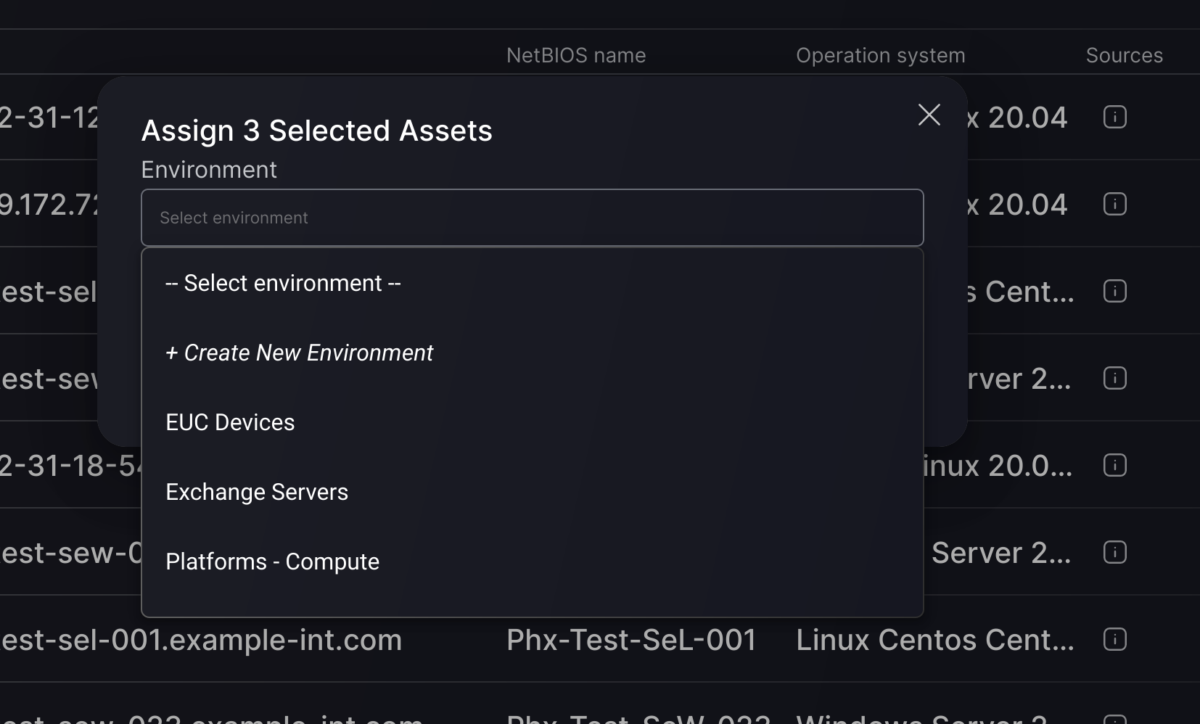
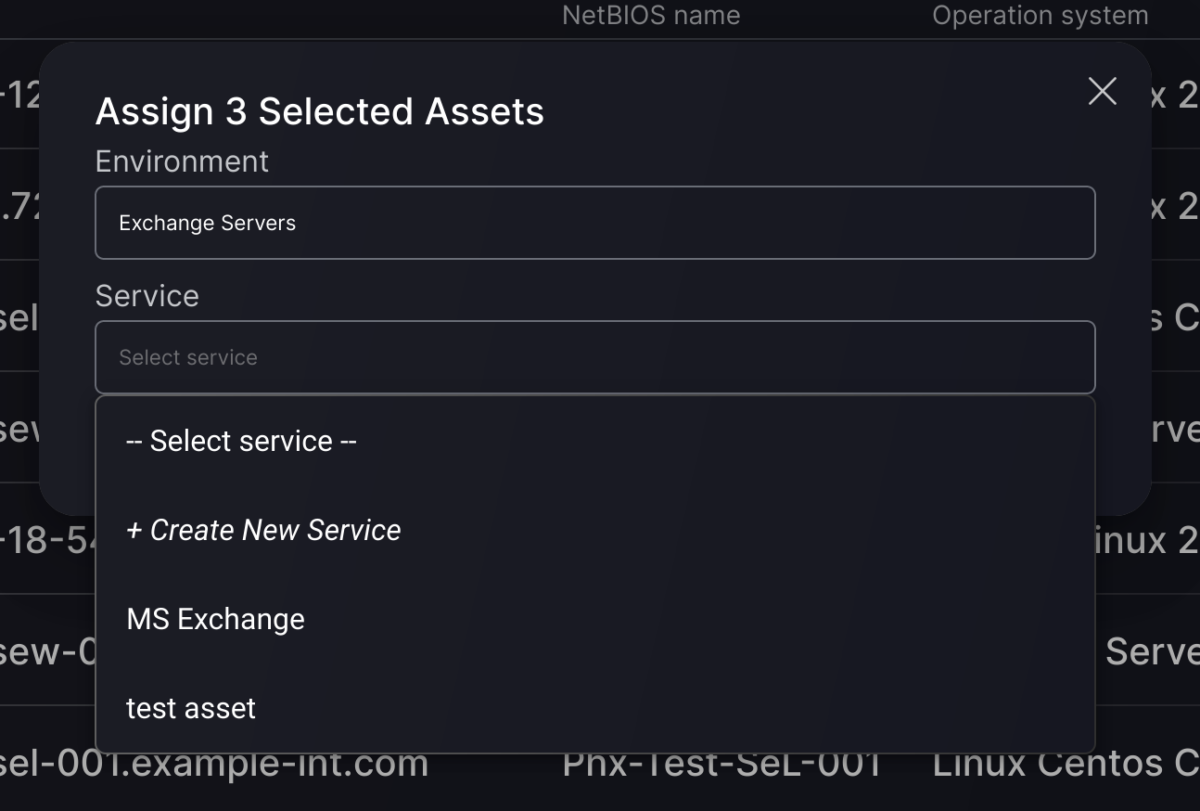
Create Apps/Envs from the Assets screen.
Continuing with the “simplified flows” theme, this release introduces a new way of adding assets to applications and environments. The new flow allows users to create applications and components “on the fly” directly from the assets screens.
Now you can select several assets from any Assets screens (from Unassigned view) and directly add them to an existing application or environment. Similarly, you can create a new App/Env for them or even create a new Component or Service inside an existing App/Env.
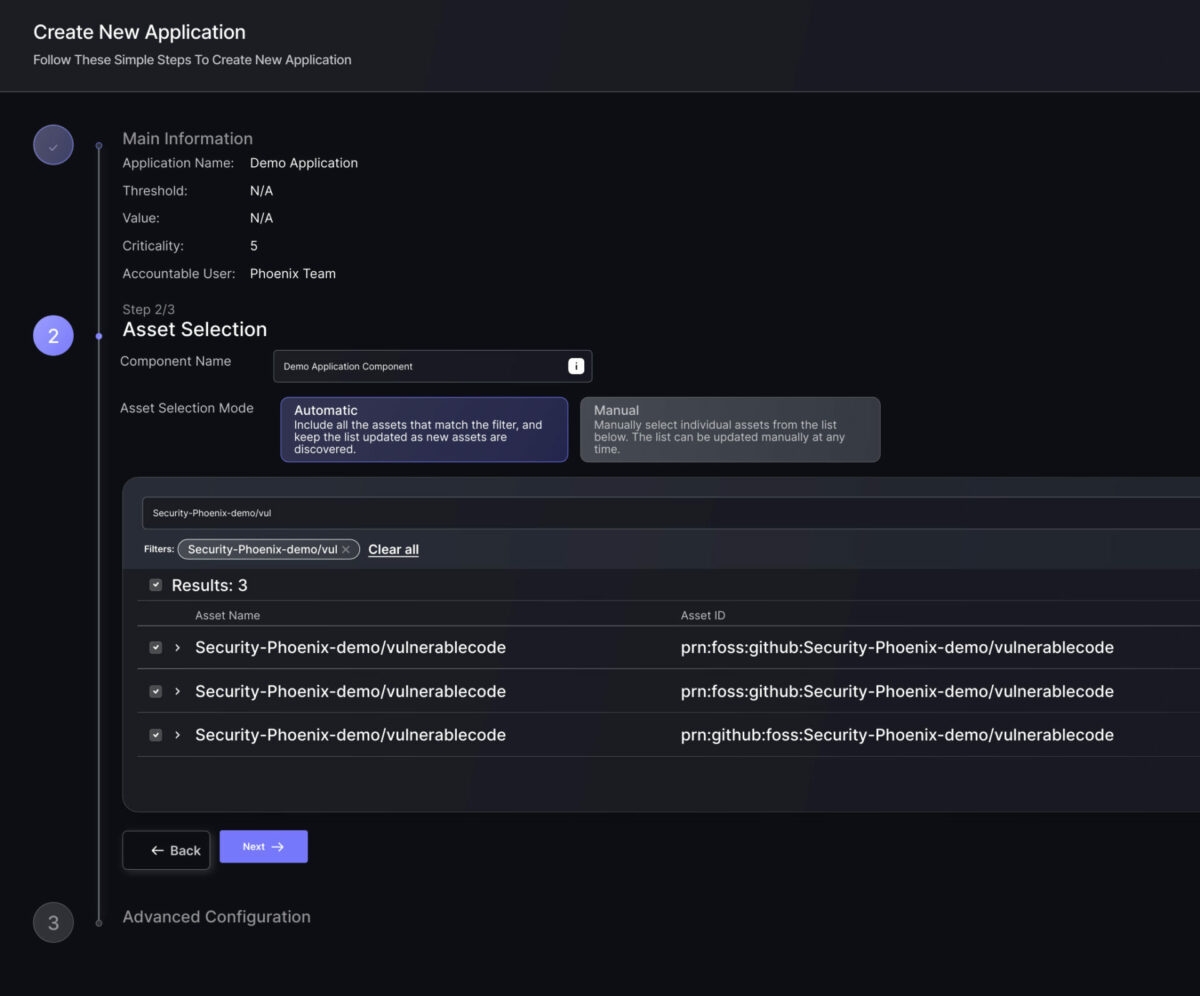
Update asset filter layout in Component forms.
We have been working to bring the latest asset selection capabilities to all areas of the platform. This process is completed with the update of the Component/Service creation and updates screens.
Users can now enjoy the same functionality and user experience across all asset filtering and selection areas when working on their application security and cloud security programmes.
Productivity and User Experience
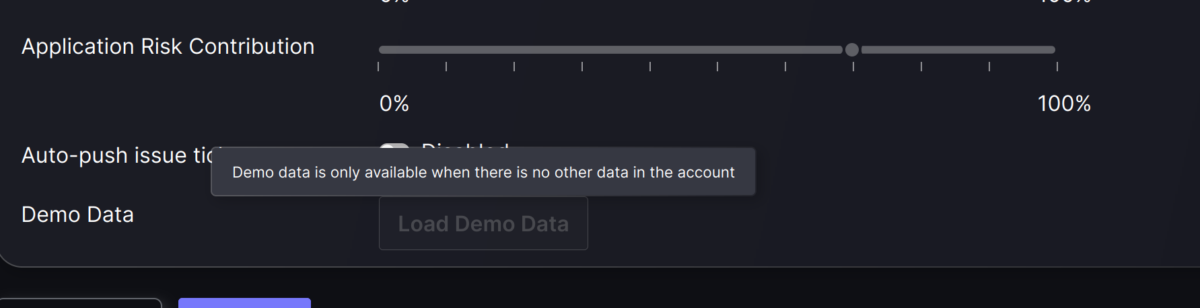
Updated Demo Data logic and feedback
We want to ensure that our users can explore the benefits of Phoenix Security even before they connect to their scanners or load their data. That’s why we’ve always provided the Load Demo Data functionality.
However, working with static, fake data – and keeping track of it – is not always easy. That’s why there are limitations regarding when demo data can be loaded. And now, we are introducing additional controls and feedback to guide our users through the process.
User Experience Improvement
Along with simplification, improving the user experience is another important focus for the Phoenix Security team. Great features are always important, but the small things sometimes make a big difference (the infamous “paper cuts”).
We have been working hard on small changes that significantly improve user experience, from additional loading animations and feedback to smother transitions.
Another area of improvement is reducing the “cognitive load” of the platform: previous knowledge is required to understand each screen and function. We will continue to work on these as we progress through our roadmap.
Integrations
Improve Snyk Integration: capture SAST vulns
Due to the structure of Snyk’s API, code vulnerabilities are not reported through the same API as the rest of the vulnerabilities. However, these SAST vulnerabilities have recently become available through a new API, so we wanted to ensure that our integration provides the complete details.
With this release, “code” Snyk projects will be processed using the new, dedicated API endpoints from Snyk. This means our users can now manage them inside Phoenix Security like they’ve done so far for other vulns.
Rebrand Code Inspector to Codiga
Our friends at Code Inspector have rebranded their platform to Codiga, and we want to ensure that our users recognise the new brand inside the Phoenix platform.

Update and realign existing integrations.
As an ongoing effort, we are constantly updating our integrations to align with the latest changes to the scanners’ APIs. In this round, we have:
- Dependabot: Aligned authentication credentials exchange with the latest API
- Phoenix ZAP/WPScan: updated/improved configuration options