The Cloud Security and AppSec teams at Phoenix Security are pleased to bring you another set of new Phoenix Security features and improvements for vulnerability management across application and cloud security engines. This release builds on top of previous releases with key additions and progress across multiple areas of the platform.

We are sure that you’ll find these quite interesting!
- Asset and Vulnerability Management
- Associate assets with multiple Applications and Environments
- Mapping of vulnerabilities to Installed Software
- Find Assets/Vulns by Scanner
- Detailed findings Location information
- Risk-based Posture Management
- Risk and Risk Magnitude for Assets
- Filter assets and vulnerabilities by source scanner
- Integrations
- BurpSuite XML Import
- Assessment Import API
- Other Improvements
- Improved multi-selection in filters
- New CVSS Score column in Vulnerabilities
Asset and Vulnerability Management
Contents
ToggleAssociate assets with multiple Applications and Environments
One of the key features of the Phoenix platform is its ability to use an easy and powerful rule mechanism to associate assets – and their vulnerabilities – with the organisation’s logical applications and environments. This allows our users to define once which assets are associated with which Apps/Envs, and let the platform keep track of them automatically. In a way, this forms the basis for our risk calculation and contextualisation.
Before one asset could only be “placed” inside one Component or Service (the groups of assets that form applications and environments); but that is changing.
Users can still select assets into groups through the usual rules, but now they are able to match the same asset with rules defined for different groups. This seemingly simple change makes the grouping mechanism much more flexible, and opens up a whole new set of possibilities. For example, now one asset could be grouped into a region-based group (e.g. “Europe servers”) and at the same time be part of a technology-based group (e.g. “Linux servers”). Now the same set of assets can be summarised using different criteria, by creating multiple groups.
Naturally, the platform now makes sure that the same asset’s risk is not aggregated multiple times into Applications and Environments, even if it has been matches by multiple rules inside them.
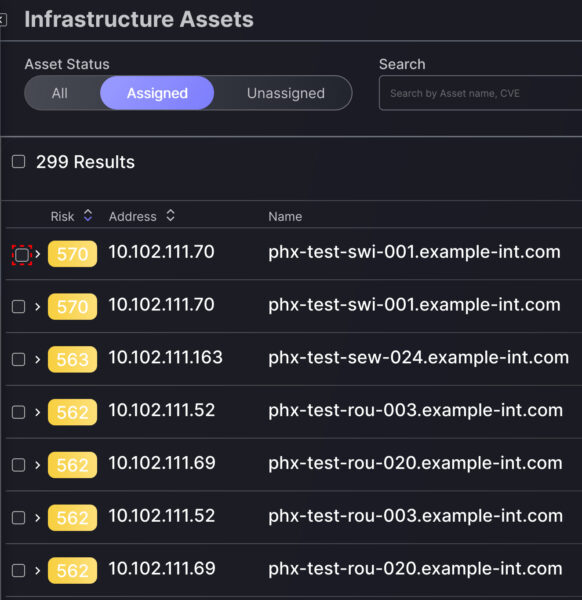
This change doesn’t bring any significant changes to the UI – things just work as per usual. But you will notice that now you can Assign assets from the All and Unassigned view in the asset screens; not just from the Unassigned view.
Mapping of vulnerabilities to Installed Software and concept of product in vulnerability management
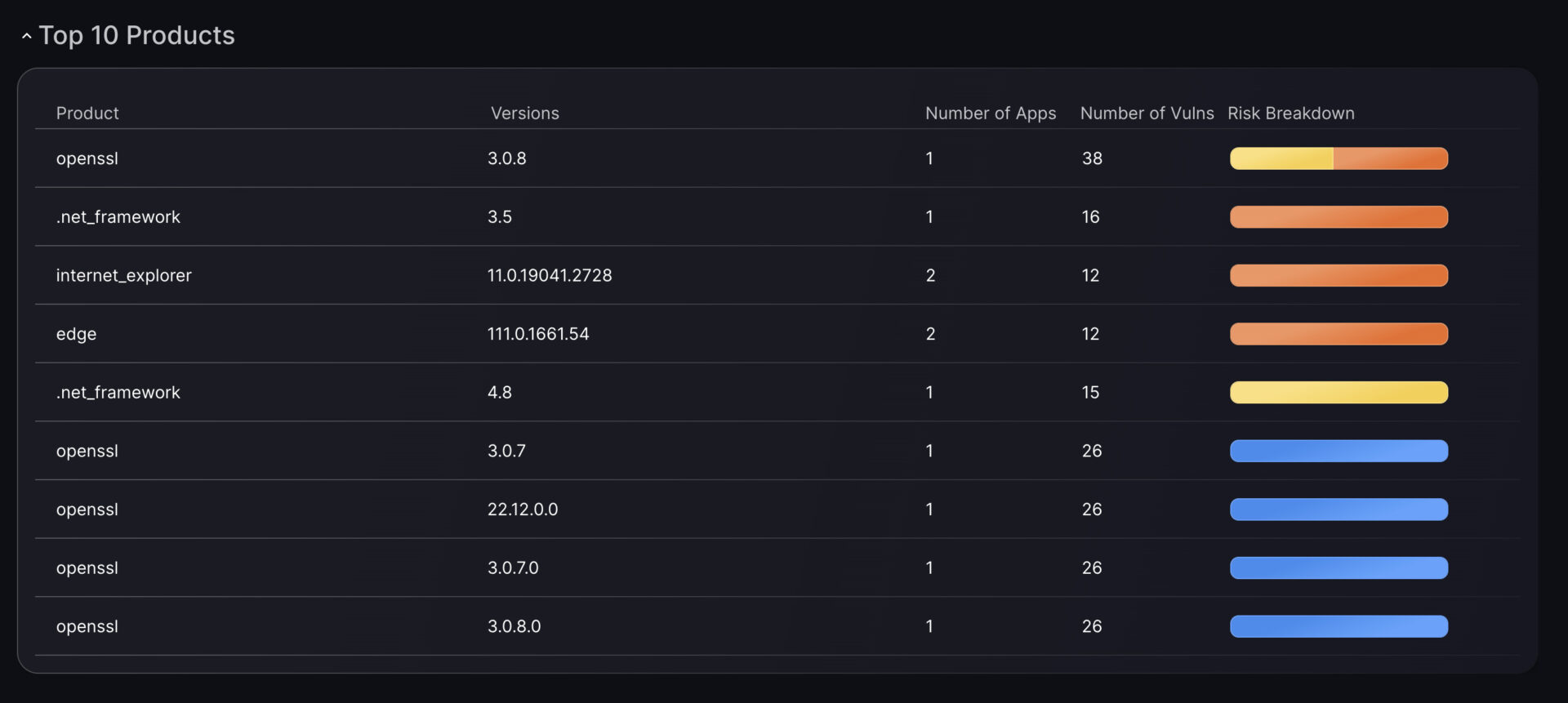
Most Infra scanners will typically report the software installed in a host and the findings for that host separately. These two pieces of information are related – most vulnerabilities would come from the installed software – but that relationship is not always clear or explicit from the scanner data.
Phoenix Security combines scanner-provided data with external vulnerability and product databases to correlate installed software products and their vulnerabilities. This allows us to provide our users with insights and trends around the software and versions used across the state.
The first manifestation of these new insights is the Top 10 Products report, inside the Security Dashboard. But there are many more coming up in future releases.
Find Assets/Vulns by Scanner
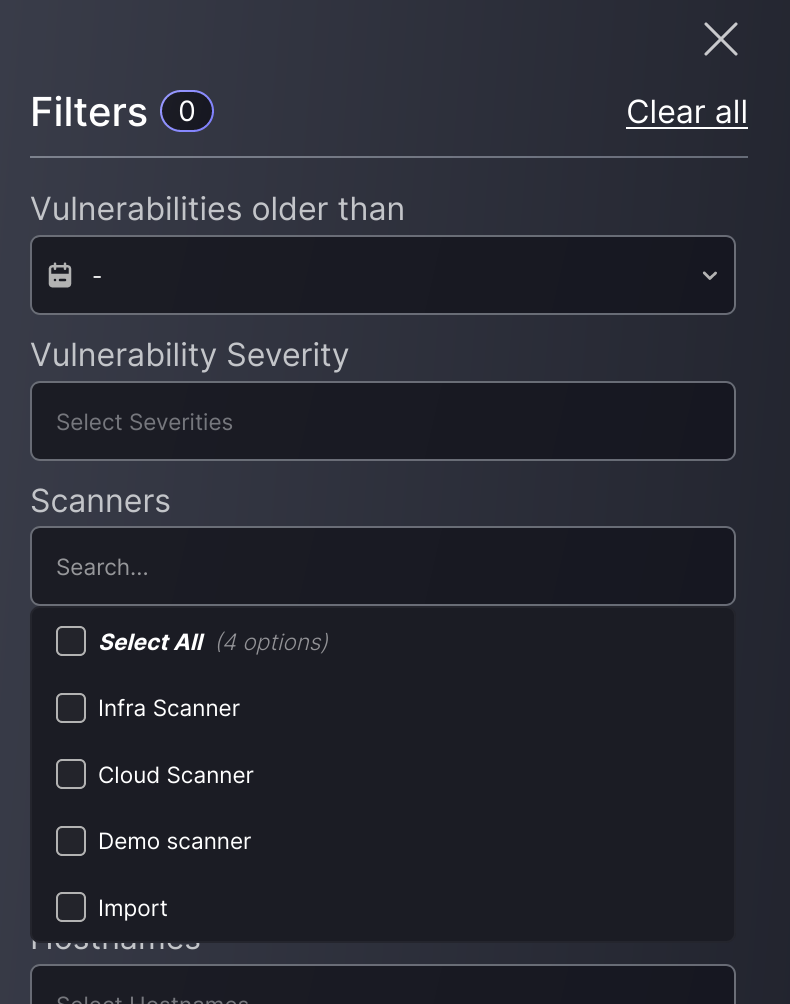
Sometimes, you want to understand which assets or vulnerabilities are reported by each scanner with which you have integrated Phoenix. Other times, you might want to explore information you know is coming from a particular scanner.
Whatever the use case, our users can now filter assets and vulnerabilities by the scanner they came from. Just another step forward in our quest to make asset and vulnerability management as easy as possible.
Detailed findings Location information
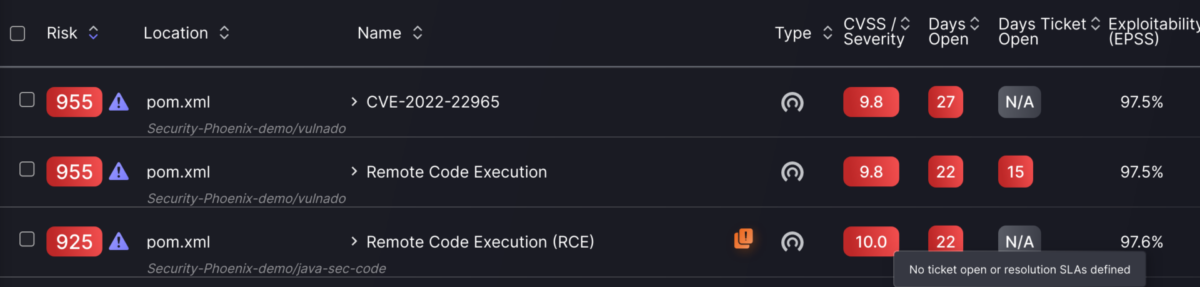
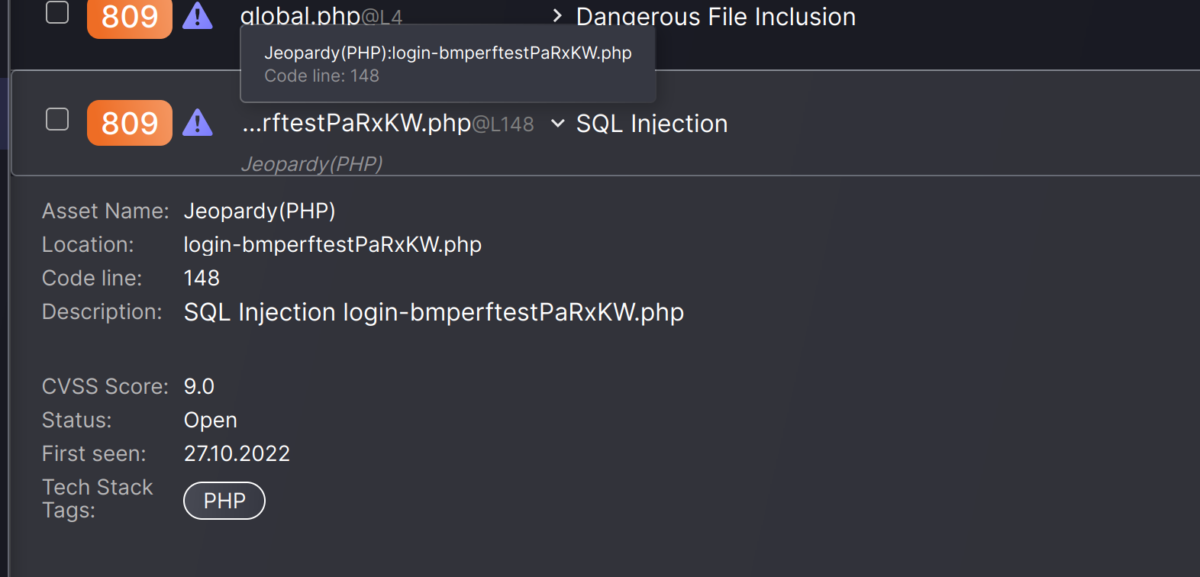
When looking at lists of findings, it’s sometimes easy to get lost within the repetition of names and CVEs. At the end of the day, the same vulnerability is often found on multiple places across an organisation’s state, so there are multiple findings with very similar details.
To help user better differentiate one finding from another, and to provide as much information as possible at a glance, we have added the vulnerability list with more detailed information about the precise location of each finding.
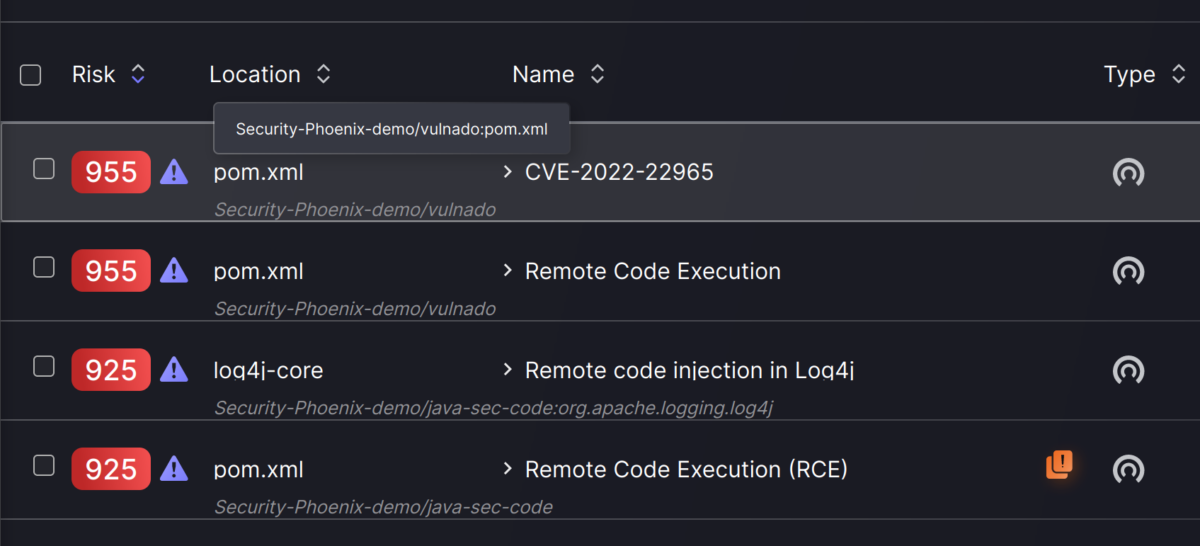
This information is detailed a bit more in the expanded row view.
Risk-based Posture Management
Risk and Risk Magnitude for Assets
Assets are a natural grouping of findings since the represent a physical or logical entity susceptible to vulnerabilities. As such, they aggregate and contextualise the risk from their findings. This is reflected in their Risk and Risk Magnitude values, which are now displayed on the assets list pages.
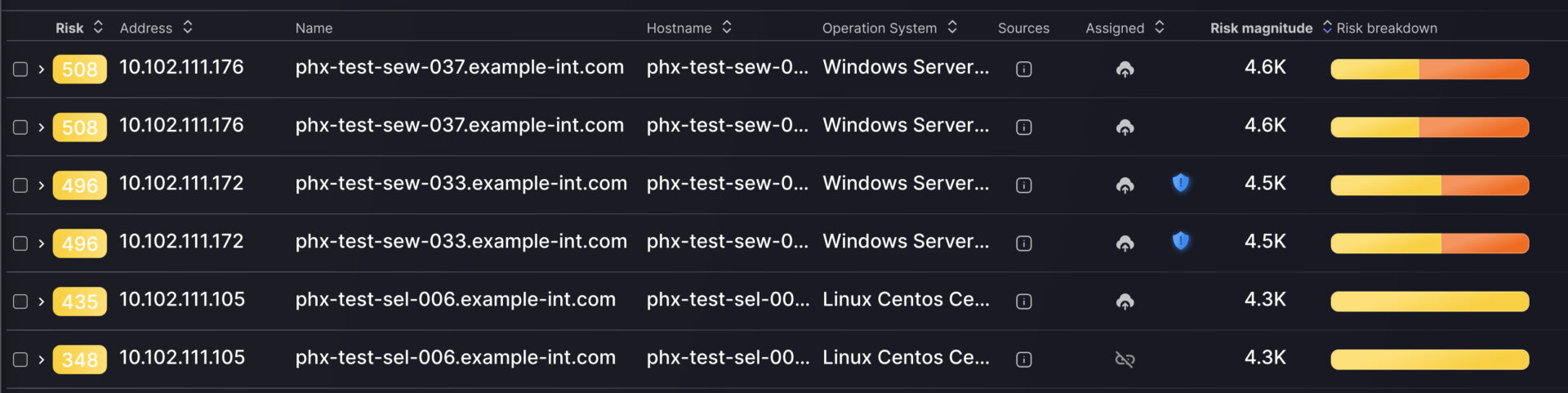
While Risk represents the average risk from the vulnerabilities, modified by the asset’s density, the Risk Magnitude reflects the “amount of risk” represented by the asset. Or put another way, the Risk Magnitude is the sum of the risk from its vulnerabilities.
Integrations
BurpSuite XML Import for appsec vulnerabilities
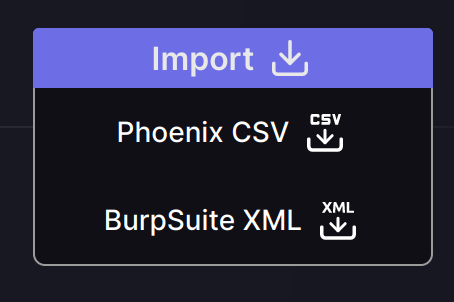
In parallel with its native scanner integrations, Phoenix Security offers a flexible Import functionality for assets and vulnerabilities. So far the format for this import was CSV only; however, users can now directly import BurpSuite XML reports in their native format.
The platform “knows” that these reports are for DAST scanning (Web/API), so it ensures that the option is offered in the right context. When importing a new assessment, you will now see both formats available to import.
Assessment Import API
Importing vulnerability assessments has become easier and more powerful than ever! Our API now supports importing assessment reports in JSON format.
Phoenix Security’s preferred report ingestion mechanism is still directly integrated with the scanner’s native API. However, there are situations where this is not possible or doesn’t fit our client’s workflows. This addition will enable our users to automate the importing of reports from external systems, using a straightforward JSON format that captures even more details than the manual imports.
In an upcoming release, the formats supported by this import mechanism will expand to cover most of the commonly used scanners and tools. Watch this space!
Other Improvements in Vulnerability and appsec
Improved multi-selection in filters
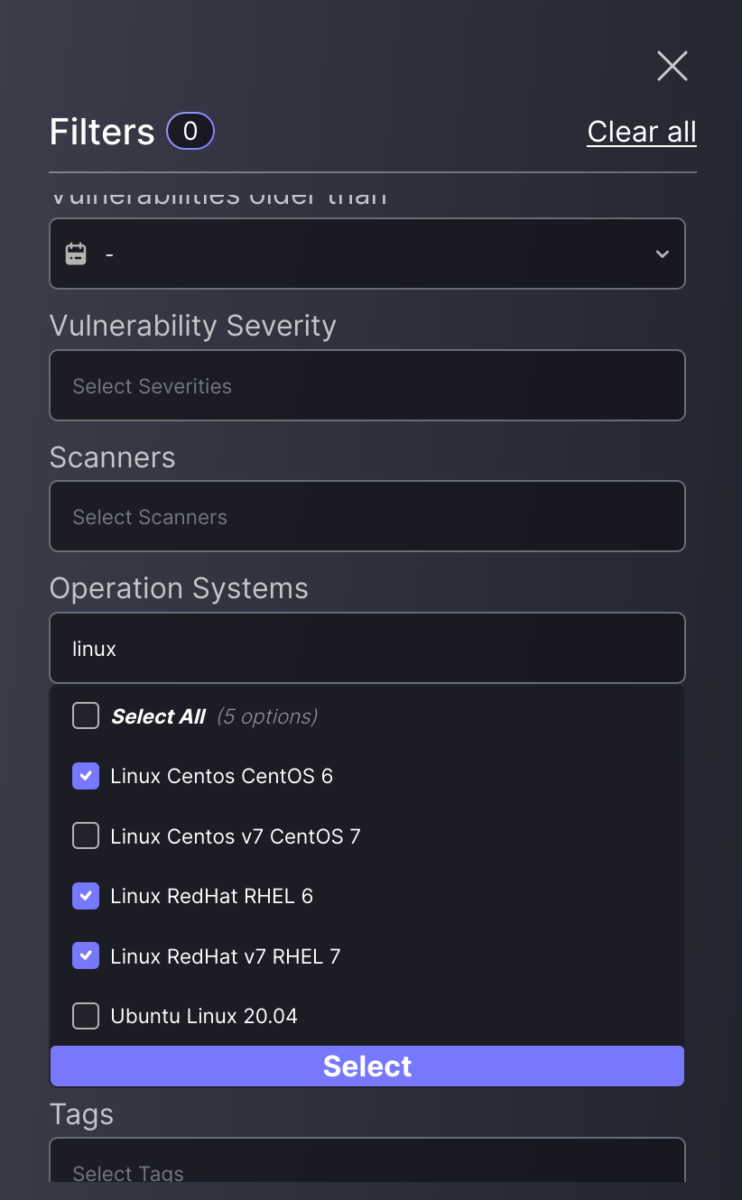
Whether for creating asset grouping rules or selecting a specific set of vulnerabilities, filtering is a key functionality of the Phoenix platform, and this release will bring a new quality-of-life improvement to our filters.
Users can easily select multiple options within those filters that support multi-selection. The new selection widget makes it very easy to find and select multiple options quickly and intuitively.
New CVSS Score column in Vulnerabilities
There are use cases where the “raw” severity of each vulnerability is important information to have at hand. In this release, we have included that information in the vulnerability list, under the “CVSS / Severity” column. This column can be sorted to help users focus on the vulnerabilities of interest.