Release Note: Azure Integration Defender, Endpoint Devops
Version: 3.0.0
Release Date: 25 October
Knowledge Base: Azure Integration with Phoenix Security
Why we extended the integration for Azure Devops, Azure Defender for endpoint, Azure Defender for cloud
We are thrilled to announce the Azure Integration with Phoenix Security, featuring three key integrations: Azure Defender for Endpoint, Azure Defender for Cloud, and Azure DevOps. This integration offers a comprehensive approach to vulnerability management, prioritizing risks across container images, running containers, and cloud misconfigurations. Azure now joins the ranks of 70+ integrations supported by Phoenix Security, offering contextual aggregation from code to cloud. 🌟
With this integration, the security team will be able to track the cloud environments, the security of their container and related endpoints, and the applications deployed in the various environments.
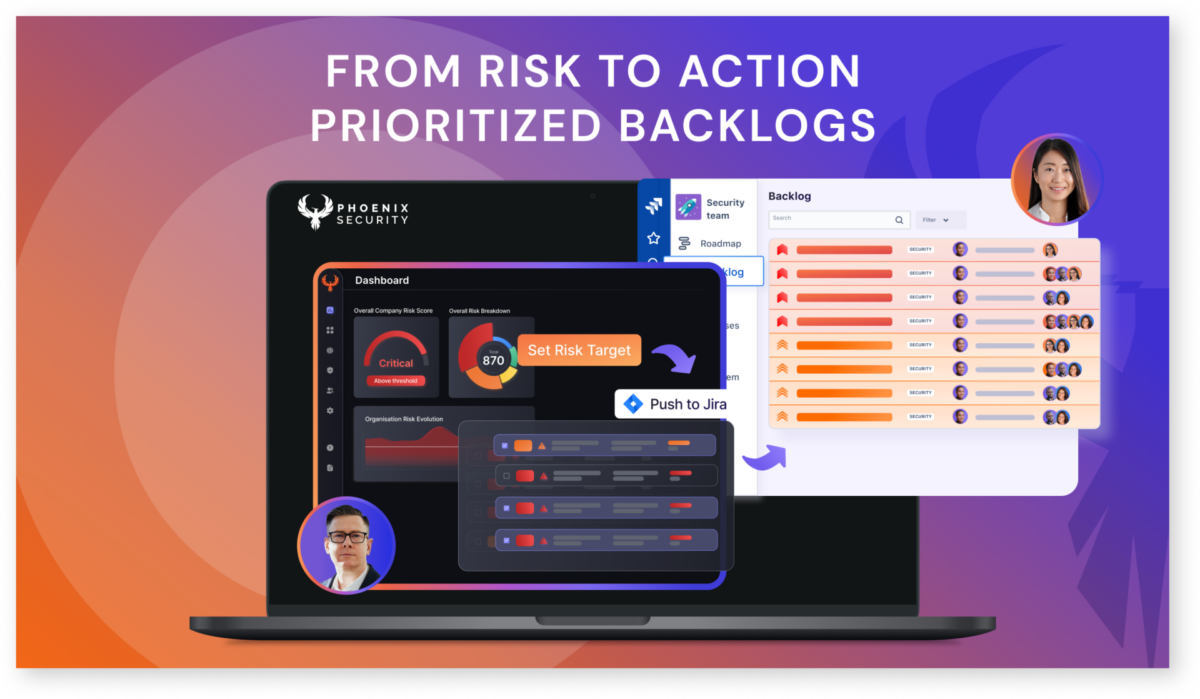
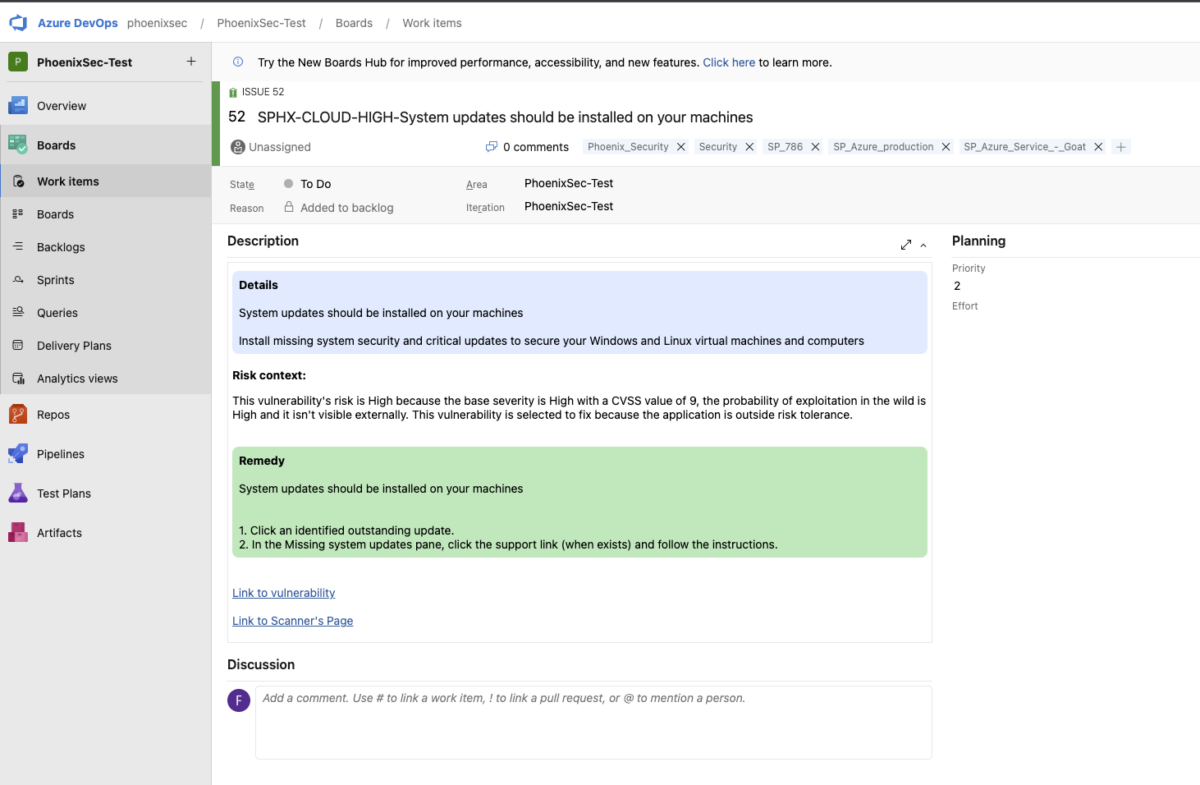
With a seamless integration into azure devops, the development team can quickly act on the latest vulnerability and deploy with one click a fix.
With the Team screen the engineer can monitor the progress towards the path to green and the resolution of the top vulnerabilities to fix.
Key Features for Azure Devops, Azure Defender for endpoint, Azure Defender for cloud
- Azure Defender for Endpoint:
- Prioritized vulnerabilities for better endpoint security.
- Link to automated resolution actions for quick remediation.
- Azure Defender for Cloud:
- Identify and prioritize cloud misconfigurations.
- Automated resolution actions to secure your cloud infrastructure.
- Enable linkback for one click-fix
- Azure DevOps:
- Real-time monitoring and vulnerability assessment for your DevOps pipeline.
- Seamless integration for a secure CI/CD process.
- 70+ Integrations Supported:
- Azure and its components become part of the 70+ integrations supported by Phoenix Security.
- Benefit from contextual aggregation of data from code to cloud.
Additional Resources
Azure Defender Integration with Phoenix Security
Azure Devops Integration with Phoenix Security
Support
Need help? Contact our support team at support @ phoenix.security.