The vulnerability management application will offer OWASP members access to its open-source security tools and access to the community edition

LONDON, England (October 12, 2021)—AppSec Phoenix, an innovative risk-based vulnerability management software, has announced its collaboration with OWASP, a non-profit foundation that works to improve software security. Through the partnership, AppSec Phoenix will make accessing open-source security tools easier for many more organizations.
OWASP is a community dedicated to enabling organizations to conceive, develop, acquire, operate, and maintain applications that can be trusted. As a non-profit, the organization provides tools and resources, community and networking, and education and training to its members. Working together for nearly 20 years, OWASP leadership and its community have sought to improve software security.
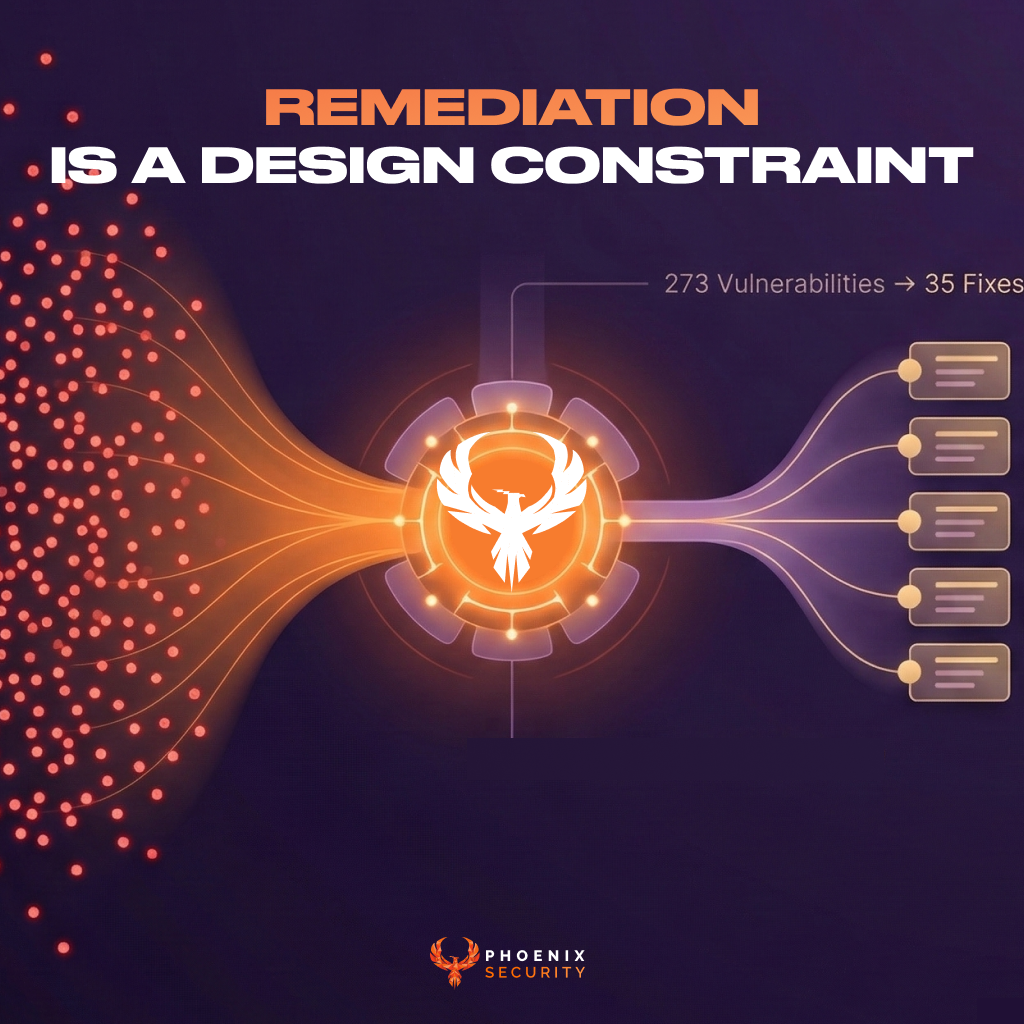
AppSec Phoenix is a smart security and risk-based vulnerability management platform for small- to medium-sized enterprises. In developing the programme, founder Francesco Cipollone and his team created it to scan for areas most likely to be targeted by cybercriminals and alert users to any vulnerabilities so they can quickly fix them. AppSec Phoenix’s approach saves its partners time and money by giving them a quick and easy way to identify risks and solve them before costly breaches occur.
With this newly announced collaboration, AppSec Phoenix will offer a free community edition license to OWASP members. This partnership will give member organizations access to AppSec’s open-source tools. The partnership also exemplifies AppSec’s shared vision with OWASP as the two organizations embrace innovative, open collaboration and making software more secure.
“We are proud to partner up with OWASP and give back to the community,” said Cipollone. “As an individual member and long friend of OWASP, I’m pleased to be able to help organizations gain access to an application security open-source project to create a simpler application security programme. By offering AppSec Phoenix to all OWASP members, we hope that more people will get started on the application security journey with a simple integration that makes open source scanning technologies available for everyone.”
“I’m thrilled by this collaboration with AppSec Phoenix, and I look forward to moving it ahead,” said Andrew van der Stock, Executive Director of OWASP. “Phoenix Security brings additional value to the OWASP subscription and OWASP’s members and aligns with the core value of open collaboration and making all software more secure. In celebration of the 20th anniversary of OWASP, we are looking forward to this exciting collaboration.”
To schedule a free demo of AppSec Phoenix’s capabilities and to learn more, visit https://www.phoenix.security/request-a-demo/.
About AppSec Phoenix
AppSec Phoenix was established to provide an effective all-in-one security solution for application developers and businesses. With our easy-use platform, we’ve simplified a notoriously complex problem faced by many companies, small and large, working in the finance field and beyond. Learn more by visiting https://www.phoenix.security/.
###