The European Union has recently introduced a revised Network and Information Systems Directive, or NIS2, which aims to improve the cybersecurity of essential services and digital service providers across the EU. This new regulation replaces the original NIS Directive, adopted in 2016. In a series of articles, we will explore what changes and their impact on vulnerability management.

You can download the latest whitepaper on nis2 here
NIS 2 applies to a wide range of operators of essential services and digital service providers, including energy, transport, banking, healthcare, and digital services such as online marketplaces and search engines. The regulation aims to establish a common level of security for these services across the EU, by requiring organizations to implement appropriate security measures and to report significant security incidents to the relevant authorities.
NIS2 and NIS 1 what are the differences
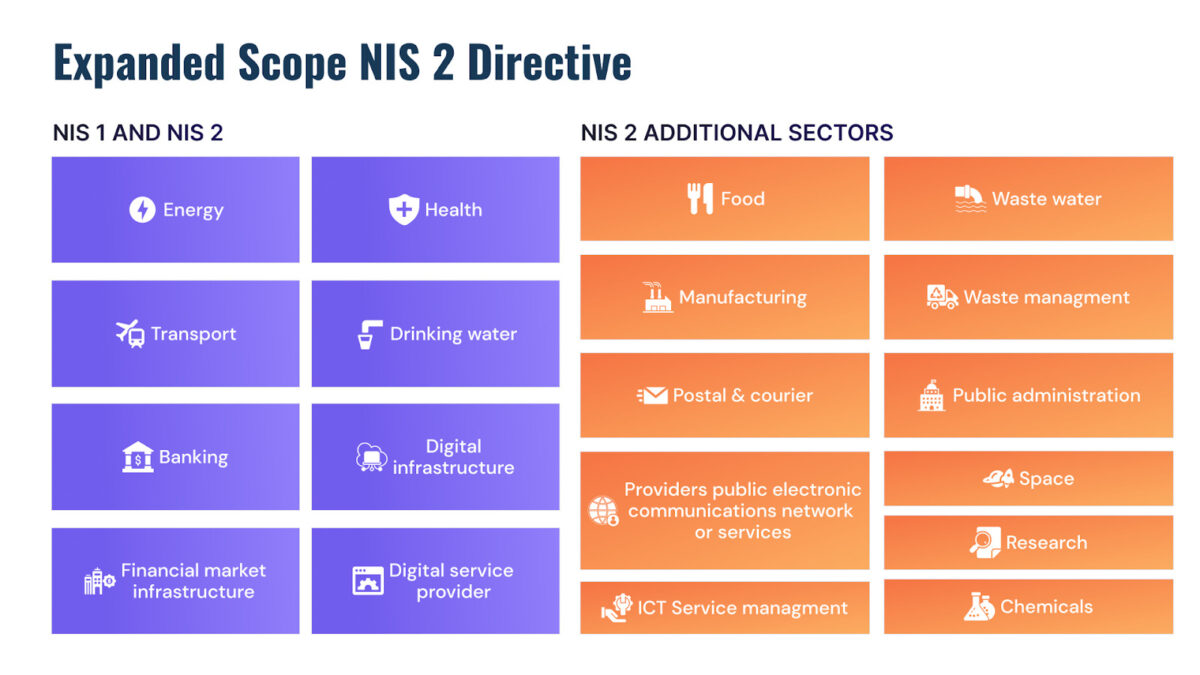
The scope is probably the biggest differentiator between the two regulations did have a more limited scope. One of the key differences between the NIS1 directive version 1 (NIS1) and version 2 (NIS2) is the expanded scope of NIS2. While NIS1 only applies to operators of essential services in specific sectors (such as energy, transport, healthcare, and finance).

NIS2 extends the directive’s reach to include additional industries and digital service providers. This means that more organizations across the EU are subject to the requirements of the directive, including those in the water supply and distribution sector, the food supply sector, and the digital infrastructure sector. Digital service providers that offer online marketplaces, search engines, and cloud computing services are now within the directive’s scope. The expansion of the scope reflects the growing importance of digital infrastructure and the need to improve the resilience of network and information systems across a broader range of sectors.
How Phoenix Security Can Help:
Phoenix Security is a platform that collects information from various sources, contextualizes, and prioritizes vulnerabilities from code to the cloud.
If you want to know more about Phoenix security and doing vulnerability management at scale, contact us https://phoenix.security/request-a-demo/
Get in control of your Application Security posture and Vulnerability management
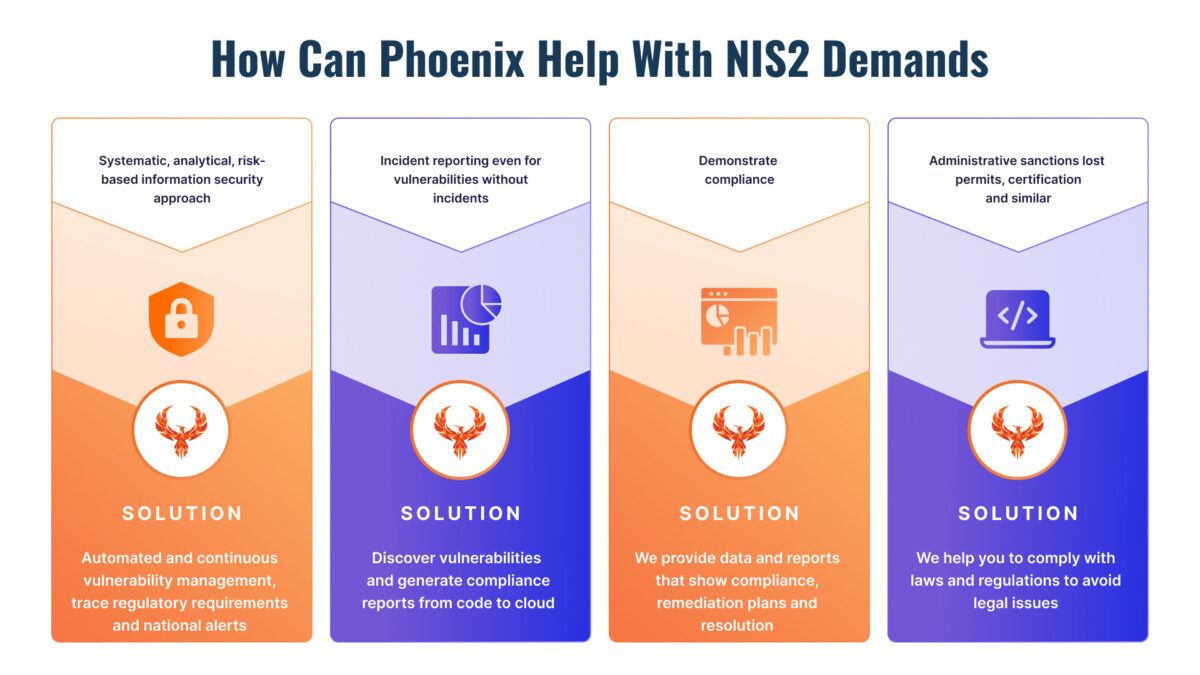
How can Phoenix Security Help you address NIS2?
| NIS 2 Requirements | How Phoenix Security Responds |
|---|---|
| Risk assessment: Article 14(1) | Phoenix security enables real-time and systematic assessment of application security, cloud, and infrastructure risks. |
| Incident management: Article 14(2) | Phoenix security enables the reconstruction of incident data by leveraging contextual searches and providing vulnerability information in real-time. It allows easy assessment and scheduling of upgrades and searches all systems and teams affected with just one click. |
| Security measures and demonstrating compliance | Phoenix security enables assessment of the real risk of specific applications and controls and specifies which compensating controls apply to specific applications or environments to ensure compliance. |
| Early identification of nation-state alerts and critical action | Phoenix security ingests nation-state and critical alerts, enabling quick action on the most critical assets. |
| Reporting | Phoenix security enables reporting on the risk posture of each product, including the number of issues that have been fixed and the expected time to fix them. |





















