Application security (AppSec) has traditionally been about securing individual software applications, concentrating on code integrity, vulnerability testing, and patch management. It is now evolving into a new concept called ASPM. For a comprehensive view, we covered application security here. Understanding and managing the complexities of application security is akin to mastering a game of chess. This analogy, eloquently presented by Francesco Cipollone, CEO and founder of Phoenix Security, in his recent talk, sheds light on the vital role of Application Security Posture Management (ASPM) in today’s digital age.
Gartner defines ASPM as application security posture management; click here for a quick analysis of ASPM and key insights.

Application security (Appsec) is, as a similar analogy a diligent librarian, meticulously organising and protecting each book (application). In contrast, product security is the architect of the entire library, ensuring the safety and integrity of the structure, the books, and the readers.
With a similar chess analogy, I’ve explained why looking at the broader picture is important.
Contents
ToggleA broader vision for ASPM
ASPM, a concept that Cipollone expertly navigates, is not just about scrutinizing individual vulnerabilities; it’s about comprehending the entire digital ecosystem – akin to a grandmaster surveying the chessboard. Here are the key takeaways from Cipollone’s insightful discourse:
1. Broadening the Horizon Beyond Traditional AppSec
Traditionally, application security has been about focusing on isolated vulnerabilities. However, as Cipollone highlights, this approach is akin to studying a single chess piece in isolation. ASPM calls for a broader view, where the entire digital environment, much like a chessboard with its myriad pieces, is considered.
2. The Shift to a Portfolio Product View:
It is important to focus and emphasize the transition from a narrow focus to a portfolio product view, which allows for a more comprehensive understanding of the digital landscape. This shift is crucial for better threat modelling and identifying issues that truly matter.
3. Contextualizing Vulnerabilities:
ASPM involves analyzing vulnerabilities in context. It’s not just about identifying a security flaw but also understanding its relevance within the broader application environment. As Cipollone points out, the impact of a vulnerability can vary significantly depending on where and how an application is deployed.
4. Understanding the Digital Supply Chain:
Modern enterprises are part of a complex digital supply chain. ASPM enables organizations to view their role within this supply chain, assessing risks and vulnerabilities in isolation and as part of a larger, interconnected system.
5. Prioritizing Security Efforts:
By providing a holistic view of the digital landscape, ASPM aids in prioritizing security efforts more effectively. It helps identify which areas are most vulnerable or critical, enabling a more strategic allocation of resources.
Francesco Cipollone’s talk is a clarion call for organizations to adopt ASPM. It’s no longer sufficient to play a defensive game, focusing on individual vulnerabilities. The need of the hour is to adopt a grandmaster’s perspective, viewing the entire digital chessboard to strategize effectively against potential security threats.
In conclusion, ASPM is not just a component of cybersecurity; it is a fundamental strategy for any organization looking to secure its digital assets. The insights provided by Cipollone are invaluable for anyone looking to deepen their understanding of modern cybersecurity challenges.
The Role of ASPM in Product Security
Application Security Posture Management (ASPM) has become more relevant as the complexity of applications has grown. ASPM provides a full-stack view of the product’s security posture, identifying vulnerabilities in the application and across its entire ecosystem. It’s like having a security guard equipped with a high-tech surveillance system that monitors every nook and cranny of a building rather than just the front door.
When considering a product security approach, the security team considers all the elements that could affect a product.
- The location where the application runs, exposure of the system
- Which system is the application deployed into
- The health of the containers/ cloud environments
- The code, libraries, API, and web endpoint that form an application
- The teams that maintain the application and attribution of the vulnerabilities to the right team
To summarise, it is important to look at HOW an application is being built (appsec) and where it is deployed.
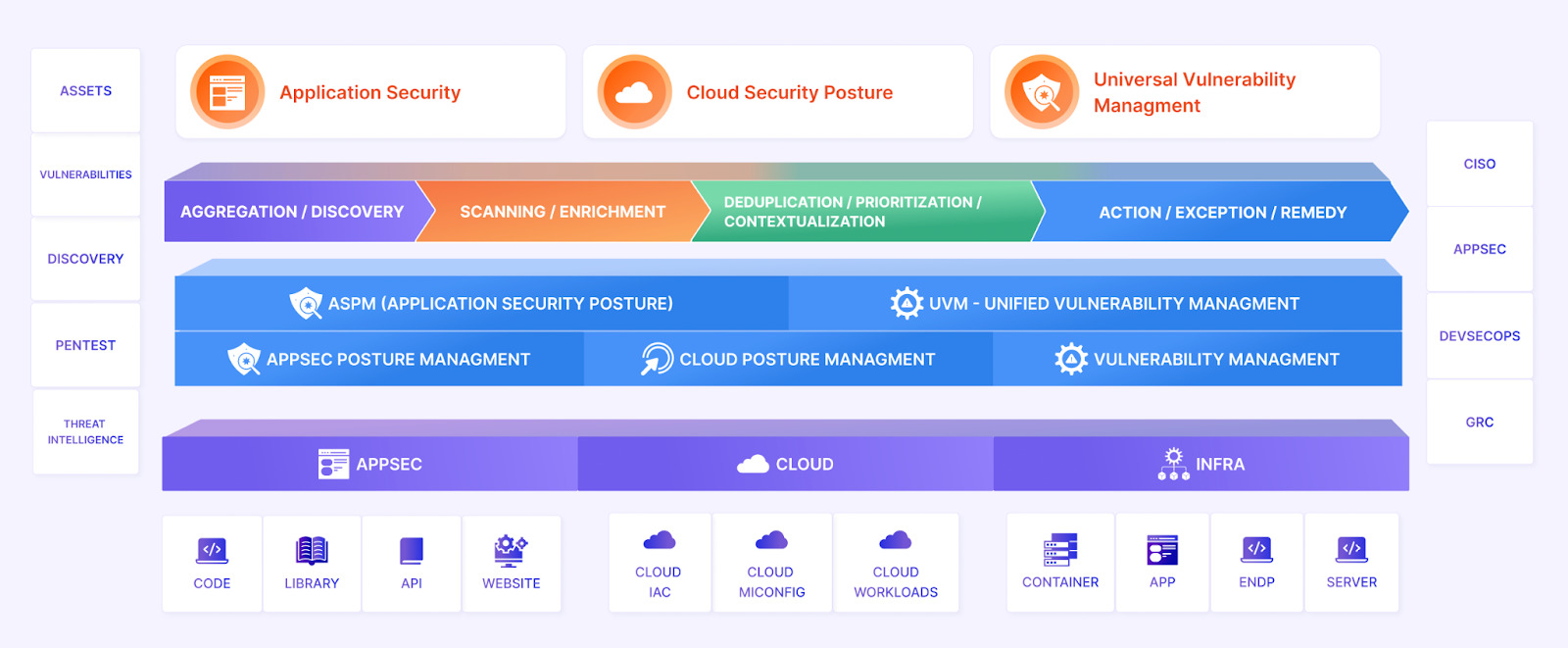
ASPM, Product Security, and the rest of the cybersecurity program

In the intricate web of cybersecurity, an application and environment security program comprises several key elements, each playing a distinct yet interconnected role. Dynamic Application Security Testing (DAST) serves as a vigilant scout, dynamically analyzing running applications for vulnerabilities, simulating an attacker’s perspective to identify real-time security flaws. On the other hand, Cloud Security Posture Management (CSPM) acts as the guardian of cloud infrastructure, continually monitoring and securing cloud configurations to prevent misconfigurations and compliance violations that could lead to security breaches.
Amidst these specialized components, Application Security Posture Management (ASPM) emerges as the strategic orchestrator, harmonizing various security practices into a cohesive whole. ASPM extends its purview beyond the boundaries of individual security measures, integrating insights from DAST, CSPM, and other security frameworks to provide a holistic view of the application security landscape. This comprehensive approach enables organizations to not only identify and remediate specific vulnerabilities but also to understand their broader security posture, anticipate potential threats, and allocate resources more strategically. By aggregating and contextualizing information from diverse security elements, ASPM empowers organizations to navigate the complex digital ecosystem with greater confidence and foresight, much like a master chess player adeptly managing every piece on the board.
The role of ASPM and why it makes product security life easier

Before ASPM: The cybersecurity landscape was akin to navigating through a dense fog, where each organization grappled with its security challenges in a somewhat siloed manner. Security teams focused predominantly on individual vulnerabilities, often employing tools like Static Application Security Testing (SAST) or Dynamic Application Security Testing (DAST) in isolation. This approach, while effective in addressing specific issues, often led to a fragmented view of security, with limited visibility into the broader application environment. Challenges such as understanding the interdependencies between applications, continuously evolving threats, and the rapid scale of cloud adoption often left security teams reactive rather than proactive, struggling to piece together a comprehensive security strategy.
After ASPM: The introduction of ASPM marked a paradigm shift, illuminating the cybersecurity landscape with a holistic view. It integrated disparate security practices into a cohesive framework, allowing organizations to see not just the trees but the entire forest. ASPM provided a comprehensive overview of the application security posture by aggregating data from various sources, including SAST, DAST, and Cloud Security Posture Management (CSPM). This broader perspective enabled security teams to understand the full context of their digital ecosystem, identify systemic vulnerabilities, and prioritize remediation efforts based on real-world risk scenarios. The proactive and strategic approach of ASPM led to more informed decision-making, better resource allocation, and, ultimately, a stronger defence against the ever-evolving landscape of cyber threats.
Why embrace product security with an ASPM methodology?
The product and application security teams have a wider attack surface to protect nowadays. The shift to product security is about expanding their purview and adopting a new mindset. It’s like moving from playing chess, instead of focusing on individual pieces, to playing 3D chess, where the dynamics of the entire board matter.
Application security issues tend to be complex in nature, and relating that message to business is challenging. No one in a development environment wants to develop bad code, but teams are pressured to deliver faster, cutting corners, resulting in poor security methodologies.
This is because the business often does not have an opinion on the security level they have to achieve. As security, we deliver a picture of thousands and thousands of problems without any context and is hard to decide how to prioritise.
Offering a risk-based view of the product (application security) and where those products operate (environment) is often the best way to achieve prioritised application security.
Product security enables CISOs and Application Security Product Security professionals to:
- Adopt a Holistic View: Understand the interdependencies within the product ecosystem, including third-party libraries, cloud environments, and CI/CD pipelines.
- Foster Collaboration: Work closely with development, operations, and business teams to embed security into every product lifecycle stage.
- Advocate for Security Culture: Promote a security-first mindset across the organization, ensuring that every stakeholder understands their role in maintaining the product’s security.
The Future of Product Security and the Role of ASPM
As we look ahead, product security is set to become the norm, with ASPM at its core and a transition into runtime analysis for a full-stack approach. This approach will not only enhance the security of products but also streamline compliance, improve customer trust, and ultimately contribute to the bottom line.
For organisations, the message is clear: the time to shift from application security to product security is now. And for CISOs, this shift represents an opportunity to redefine their role and impact within the organisation.
In conclusion, as we navigate this transition, let’s remember that product security is not just about protecting a product; it’s about safeguarding the trust in the software product.
How Phoenix Security Can Help

Phoenix Security helps organizations identify and trace which systems have vulnerabilities, understanding the relation between code and cloud. One of the significant challenges in securing applications is knowing where and how frameworks like Struts are used. ASPM tools can scan the application portfolio to identify instances of Struts, mapping out where it is deployed across the organization. This information is crucial for targeted security measures and efficient patch management. Phoenix Security’s robust Application Security Posture Management (ASPM) system is adept at not just managing, but preempting the exploitation of vulnerabilities through its automated identification system. This system prioritises critical vulnerabilities, ensuring that teams can address the most pressing threats first, optimising resource allocation and remediation efforts.
The Role of Application Security Posture Management (ASPM):
ASPM plays a vital role in managing and securing applications like those built with Apache Struts. It involves continuous assessment, monitoring, and improvement of the security posture of applications. ASPM tools can:
- Identify and Track Struts Components: Locate where Struts is implemented within the application infrastructure.
- Vulnerability Management: Detect known vulnerabilities in Struts and prioritize them for remediation.
- Configuration Monitoring: Ensure Struts configurations adhere to best security practices.
- Compliance: Check if the usage of Struts aligns with relevant cybersecurity regulations and standards.
By leveraging Phoenix Security, you not only unravel the potential threats but also take a significant stride in vulnerability management, ensuring your application security remains up to date and focuses on the key vulnerabilities.








![Phoenix Security infographic: Claude Code Critical Vulnerability — CI/CD Nightmare, 3 Command Injection Flaws. Dark navy and orange background with circuit-board pattern. Center: terminal window showing attack chain [config] | [shell] | [exfil] with three red arrows pointing to attack targets — CI/CD Pipeline Compromise (top right), Cloud Key Exfiltration via AWS (middle right), and Developer Workstation Compromise leading to Server-to-Server lateral movement (bottom right). Phoenix Security logo at top. Bottom text: "CLAUDE CODE / CRITICAL VULNERABILITY / CI/CD NIGHTMARE / 3 COMMAND INJECTION FLAWS / Credential Exfiltration · CWE-78 · Confirmed / Shell Injection in CLI, Editor, and Auth Helpers."](https://phoenix.security/media/Gemini_Generated_Image_abcn46abcn46abcn.jpeg)








